Cryptor2.0 ransomware (Virus Removal Guide) - Decryption Methods Included
Cryptor2.0 virus Removal Guide
What is Cryptor2.0 ransomware?
Cryptor2.0 ransomware is the newest version of Ryuk virus that originally targeted high-profile organizations
Cryptor2.0 ransomware is a file locking virus that was spotted at the end of January 2019. Malware stems from the infamous Ryuk ransomware, which is speculated to be connected to the North-Korean Lazarus hacking group. This variant uses Microsoft Enhanced RSA and AES encryption algorithms to lock up data and then adds .RYK file extension to pictures, videos, databases, documents, etc. Next, Cryptor2.0 ransomware contacts a remote server that is controlled by hackers and drops a ransom note ReadMe.txt into each of the folders. Victims are informed that their personal files have been encoded and only a unique key can unlock them. They are asked to contact crooks via DejackomeAjna@protonmail.com or ElmersVictoria@tutanota.com for Bitcoin wallet information that the ransom should be transferred to, as well as the ransom size.
| Name | Cryptor2.0 |
| Type | Ransomware |
| Family | Ryuk |
| Ciphers | RSA and AES |
| File extension | .RYK |
| Ransom note | ReadMe.txt |
| Contact | DejackomeAjna@protonmail.com or ElmersVictoria@tutanota.com |
| Decryptable? | No |
| Elimination | Use security software like FortectIntego that can detect[1] the virus |
Ryuk ransomware created real chaos among users and organizations when it started to infiltrate systems all over the world back in summer 2018. It later devastated various newspapers in the US, preventing Tribune Publishing and Los Angeles Times delivering new issues on time.[2] It asked between 15 to 20 BTC for the decryptor, and managed to earn a fortune during its reign. As evident, malware authors are not backing away and continuing their campaign with the release of Cryptor2.0 ransomware.
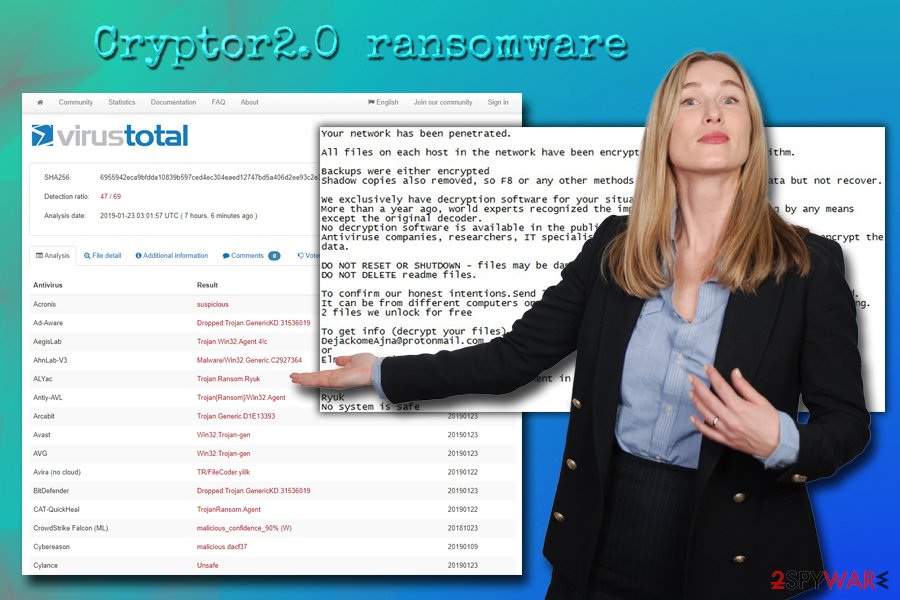
For Cryptor2.0 ransomware removal, users need to choose software that can recognize the threat. Currently, 47 AV engines detect the malicious dropper file as:[1]
- Dropped:Trojan.GenericKD.31536019
- TR/FileCoder.yiilk
- TrojanRansom.Agent
- a variant of Win32/Filecoder.NTB
- Ransom:Win32/Ryuk.S!MTB
- W32.Ransom.Gen, etc.
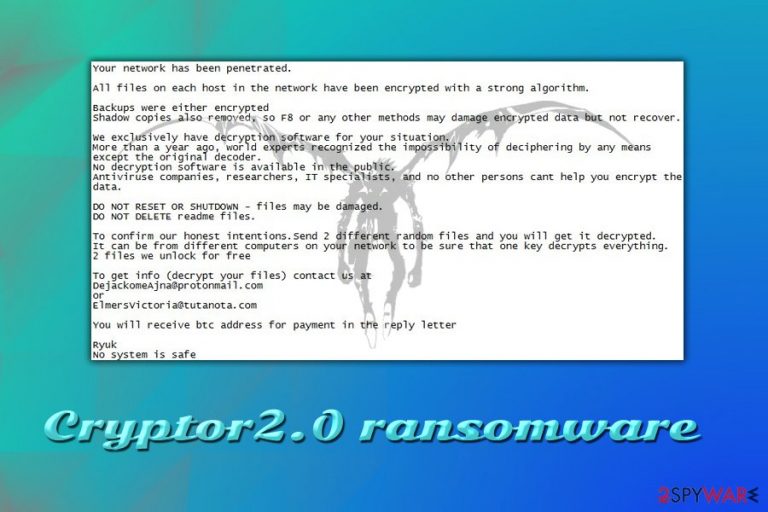
As soon as Cryptor2.0 virus modifies the system files and encrypts data, it drops the ransom note which reads as follows:
Your network has been penetrated.
All files on each host in the network have been encrypted with a strong algorithm.
Backups were either encrypted
Shadow copies also removed, so F8 or any other methods may damage encrypted data but not recover.
We exclusively have decryption software for your situation.
<…>
To get info (decrypt your files) contact us at
DejackomeAjna@protonmail.com or ElmersVictoria@tutanota.com
You will receive btc address for payment in the reply letterRyuk
No system is safe
Cryptor2.0 ransomware authors also offer to send two files for test decryption. This action is done to raise a false feeling of trust in victims, which would make them more likely to pay the ransom. However, even with test decryption being successful, there is no guarantee that users will receive full decryptor for .RYK encoded files.
Security researchers also vote against paying the ransom, as such action would simple encourage cybercriminals to improve the code and produce more sophisticated viruses. Thus, victims should remove Cryptor2.0 ransomware with the help of reputable security software like FortectIntego – it can detect all the malicious elements of malware and eliminate them.
Common ransomware distribution methods
Ransomware is a dangerous cyber infection, as it leaves files locked even after its removal. Therefore, it is vital to use maximum protection measures when it comes to computer security.
Ransomware authors usually employ a variety of distribution techniques, most prominent of them being the spam emails. Phishing emails are often sent to thousands of victims and include attachments or malicious links. As soon as users click on those – malware is executed on the system and files encrypted.
Another technique which recently grew in popularity due to “on the spot response” functionality[3] is the brute-forcing. This allows hackers to scan the internet for vulnerable RDP connections and use a preset list of most commonly used passwords. Consequently, bad actors can manually install ransomware into the computer. This is extremely common in targeted attacks against various businesses and organizations.
Additionally, malware authors use exploit kits, fake updates, malicious JavaScripts, and other techniques to infect as many users as possible. To protect yourself from ransomware attacks, use comprehensive security software, patch your system, prepare backups of your files, do not open spam emails casually, use strong passwords, and generally be more careful when browsing the web.
Cryptor2.0 ransomware removal instructions
To remove Cryptor2.0 virus, you should choose appropriate anti-malware software. There are plenty available on the market, so choose the one that suits you best, although we recommend using FortectIntego. In case Cryptor2.0 ransomware prevents security software from working normally, enter Safe Mode with Networking as explained below.
Unfortunately, but the malware is not currently decryptable. Therefore, regaining access to files without paying crooks might be quite tricky. Nevertheless, users can wait till cybersecurity researchers create an official decryptor or can try third-party recovery software as an immediate remedy. Remember, you should only try to recover your files after Cryptor2.0 ransomware removal, as your data would be encrypted again.
Getting rid of Cryptor2.0 virus. Follow these steps
Manual removal using Safe Mode
In case Cryptor2.0 ransomware prevents security software from working correctly, use these steps to enter Safe Mode with Networking:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Cryptor2.0 using System Restore
System Restore is another method that can be used to disable malware's functionality:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Cryptor2.0. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Cryptor2.0 from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Cryptor2.0, you can use several methods to restore them:
Data Recovery Pro can be used to attempt file recovery
This tool is professional software that can recover corrupted or accidentally deleted files. Also, it might help you recover .RYK files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Cryptor2.0 ransomware;
- Restore them.
Make use of Windows Previous Versions feature
This option is only available for those who set up the System Restore point before the virus attacked.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer might be able to help
ShadowExplorer is a program that can recover all your data if Cryptor2.0 virus failed to delete Shadow Volume Copies.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryptor is available yet
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Cryptor2.0 and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ 6955942eca9bfdda10839b597ced4ec304eaed12747bd5a406d2ee93c2e3f356. Virus Total. URL and file analyzer.
- ^ Jake Doevan. Ryuk ransomware attack delays the distribution of major US newspapers. 2-spyware. Cybersecurity news and articles.
- ^ Benjamin Hosack. Stronger and more frequent Brute Force Attacks are now the norm. Foregenix. Global Cybersecurity Experts.







