D00mEd ransomware (Free Instructions) - Virus Removal Guide
D00mEd virus Removal Guide
What is D00mEd ransomware?
D00mEd ransomware – a file-encrypting malware strain that uses the combination of AES 128 and RSA 2048 to lock up victims' files

D00mEd ransomware is an AES and RSA[1] key-based file locker that has emerged at the start of October this year.[2] Aimed for ransom demands, the malware encrypts all files/documents on the infected Windows OS. Regarding the text written in READ_MEE.txt, D00mEd ransomware points its target towards English-speaking users. Criminals place ransom demands in this message and paste a copy of the note in each folder that contains encrypted data. These people urge some price in exchange for the decryption software. However, there is no particular information provided about the ransom demands for .D00mEd files but they usually vary between $100 and $1000 and need to be transferred via BTC services.
| Virus name | D00mEd ransomware |
|---|---|
| Malware type | Ransomware virus |
| Encryption used | This dangerous malware form uses the combination of two popular encryption algorithms – AES 128 and RSA 1048 |
| Appendix added | Once the files and documents get locked by D00mEd ransomware virus, all of them receive the .D00mEd appendix near to their filenames |
| Ransom note | Later on, the malware developers provide the READ_MEE.txt ransom message in order to bombard the victims with ransom demands |
| Ransom details | However, the crooks do not give any particular details about the ransom price that needs to be paid, hackers are most likely to urge for an amount between $100 and $1000 |
| Main target | Regarding the ransom note's written language, this malware strain appears to target English-speaking users |
| First spotted | According to cybersecurity researchers' reports, the ransomware virus was first spotted at the beginning of October 2019 |
| Investigate your PC | Use software such as FortectIntego to perform a thorough system check-up. Afterward, employ professional software to delete the malware safely and permanently |
D00mEd virus supposedly holds both encryption and decryption keys on remote servers which are accessible only for the cybercriminals themselves. This hardens the data recovery process for regular users but we offer to stay away from any ransom demands as there is a big risk of getting scammed and facing huge money swindles.
In addition, D00mEd ransomware might try to harder the file restoring process in two more ways. First, the malware might corrupt the hosts file and prevent users from accessing security-related websites. Continuously, the ransomware viruses might execute specific PowerShell commands to eliminate Shadow Copies[3] of locked data.
Once you are completing D00mEd ransomware removal, make sure to eliminate the Windows hosts file, otherwise, the access to security-based forums and pages might remain blocked. Do not get threatened by statements that your files are going to be lost forever and try finding other alternatives to reverse your data back to its previous state:
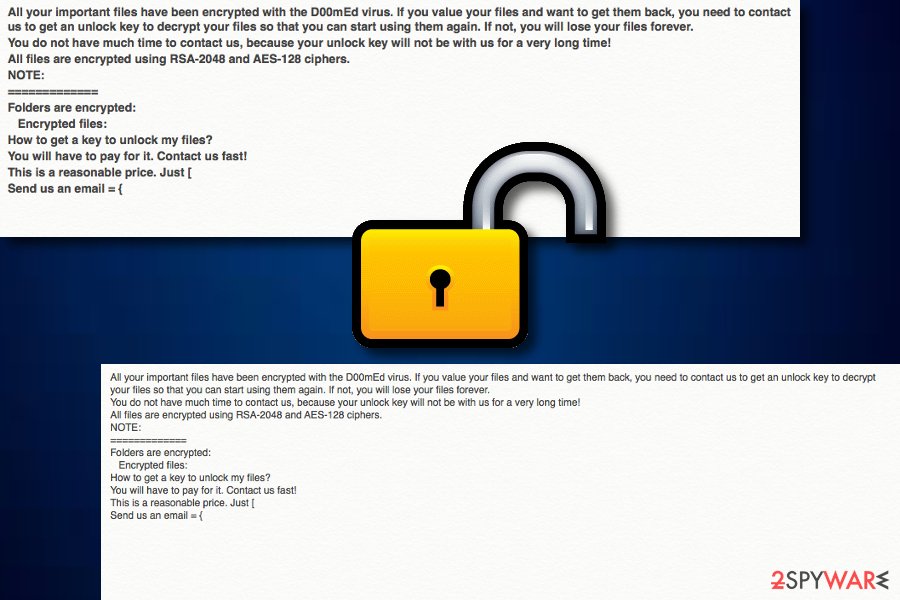
All your important files have been encrypted with the D00mEd virus. If you value your files and want to get them back, you need to contact us to get an unlock key to decrypt your files so that you can start using them again. If not, you will lose your files forever.
You do not have much time to contact us, because your unlock key will not be with us for a very long time!
All files are encrypted using RSA-2048 and AES-128 ciphers.
NOTE:
=============
Folders are encrypted:
Encrypted files:
How to get a key to unlock my files?
You will have to pay for it. Contact us fast!
This is a reasonable price. Just [
Send us an email = {
D00mEd ransomware might urge you to pay the ransom in Bitcoin or another type of cryptocurrency, for example, Ethereum or Litecoin.[4] Criminals require this type of currency as it allows the transferred and the receiver to stay completely anonymous. This way the hackers slightly decrease their chances of being exposed to the police.
There are also some things that can be up the sleeve of D00mEd ransomware developers. These people might distribute more than one malware in an entire package. Sometimes, ransomware can come together with a Trojan virus, worm, botnet, cryptocurrency miner, spyware, or other malicious programs that will benefit the crooks' needs.
Be aware that the ransomware virus might run malicious processes in the background and this is why it is important to boot your Windows system to Safe Mode with Networking and just then try to remove D00mEd ransomware from the system. Find a detailed guide on how to accomplish the boot process at the end of this article.
Once again, there is no need of paying D00mEd ransomware developers as these people might only seek to benefit from you. Rather than emptying your bank account for nothing, go to the bottom of this page and there you will find three data recovery options that might help you to restore some of your individual files.
Ransomware infections are still on the rise
D00mEd ransomware is just one of the thousands of other existing ransom-demanding threats. Reports about recent ransomware infections flood the Internet space daily. We guess that all of you have heard about the infamous WannaCry attack that has related to blackmailing huge companies worldwide.
However, this malware's time has already passed and newer ransomware strains are hitting the cybersphere each day. At the moment of writing, Djvu ransomware has been filling its family line very quickly. We have already counted over 170 versions of this malware that allows the developers to generate more success than they would by distributing only one are a few ransomware variants.
Continuously, other file lockers such as Sodinokibi have also been targetted companies worldwide. Sodinokibi has hit around 400 dental health offices during August. However, criminals often urge huge ransom demands from reputable companies that might even reach thousands of hundreds of millions of dollars. Some companies decide to pay the price to recover their files, some employ advanced experts to help them with data recovery.
Ransomware payload comes camouflaged
Malicious payload that includes the ransomware infection is often passed on to users through email spam and the malicious files attached. Crooks often pretend to be from reputable shipping organizations such as FedEx/DHL and ask users to “confirm an order” via a suspicious hyperlink or “view order information” by downloading a particular attachment.
Be aware of bogus email messages that fall into the Spam section of your email box as the service automatically sorts out all unpleasant letters and sends them to Spam. However, even if you receive a message to your Inbox section, verify its sender first and scan the attachments with AV protection before opening them just for ultimate security.
Other ransomware viruses are distributed via software cracks that are posted on The Pirate Bay, eMule, and similar torrenting networks. Our point of view would be to try downloading programs, files, and services only from reliable sources and choosing original developers only.
According to experts from Virusai.lt network,[5] ransom-demanding threats are able to spread through hacked RDPs such as the TCP port 3389. Ransomware developers abuse vulnerable RDP, hack it, and gains remote access to the computer system by forcibly entering the password into the machine.
Advanced removal possibilities for D00mEd ransomware
Remember that in order to get rid of D00mEd ransomware fully, you have to terminate all dangerous objects that the malware has planted on your computer system. Usually, some dangerous products will be spotted in the Windows Registry and Task Manager sections from where they also need to be deleted.
If you do not remove D00mEd ransomware fully, the file-locking malware might launch itself automatically within the next Windows OS boot as this type of feature usually comes included in the virus's module. Do not forget to employ reputable antimalware such as FortectIntego, SpyHunter 5Combo Cleaner, Malwarebytes to perform a full malware scan.
After the check-up process is completed, you can successfully continue with D00mEd ransomware removal. However, DO NOT try to eliminate the cyber threat on your own as you might make unrepairable mistakes. Use professional tools only and check out the data recovery possibilities at the end after you are finished with the elimination.
Getting rid of D00mEd virus. Follow these steps
Manual removal using Safe Mode
To get rid of malicious processes on your Windows OS, launch Safe Mode with Networking:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove D00mEd using System Restore
To prevent bogus activities, reboot the system via System Restore:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of D00mEd. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove D00mEd from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by D00mEd, you can use several methods to restore them:
Employ Data Recovery Pro and restore some individual files.
If D00mEd ransomware virus has locked your data, try restoring some components with the help of this software.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by D00mEd ransomware;
- Restore them.
Using Windows Previous Versions feature might allow you to recover some data.
Employ this product and try to bring some of your files back to their primary positions.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Shadow Explorer might help you with data recovery.
If the ransomware virus did not eliminate Shadow Volume Copies of the encrypted files, you can try this software.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Currently, cybersecurity experts are working on the official decryptor.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from D00mEd and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Josh Lake. What is RSA encryption and how does it work?. Comparitech. Relevant information.
- ^ Amigo-A. D00mEd ransomware. Twitter. Social platform.
- ^ Vangie Beal. Shadow Copy. Webopedia. IT definitions.
- ^ Litecoin. Wikipedia. The free encyclopedia.
- ^ Virusai.lt. Virusai. News source.







