Defenderfocus.xyz ads (Free Guide)
Defenderfocus.xyz ads Removal Guide
What is Defenderfocus.xyz ads?
Defenderfocus.xyz is a scam website that impersonates legitimate security software
Defenderfocus.xyz is one of the thousands of fake websites you may encounter online out of the blue. To be more precise, this usually happens whenever high-risk places, such as torrent hosts, illegal video streaming services, and similar. In rarer cases, the reason for redirects could be adware[1] – a potentially unwanted program specializing in displaying intrusive ads and tracking user data.
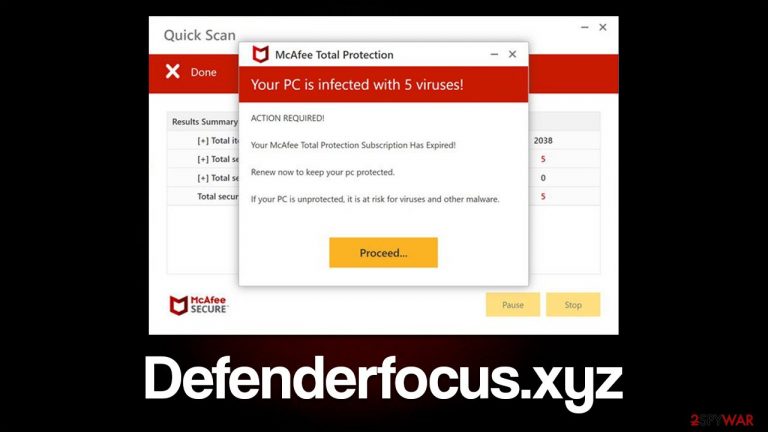
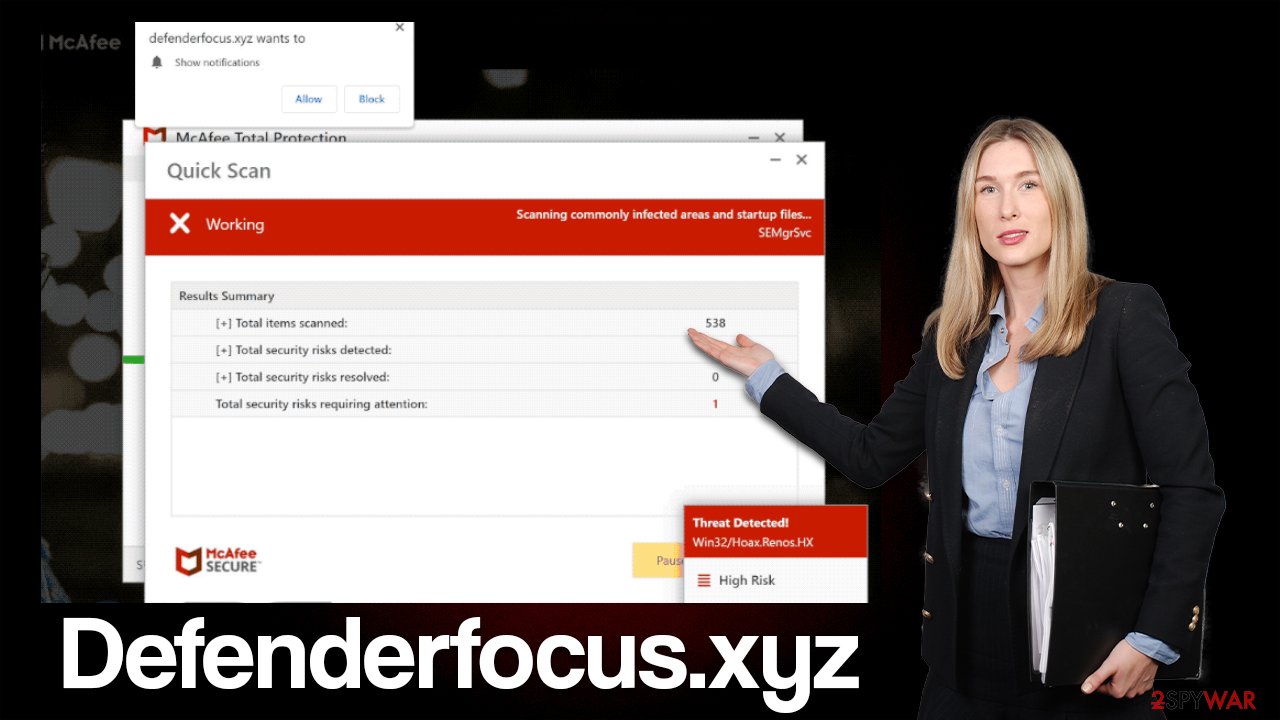
Once on Defenderfocus.xyz, users are immediately presented with what looks like a system scan with several pop-up windows. In mere few seconds, several pop-ups show up, with each showing allegedly found threats. Soon after, people are shown the following result, which seems very alarming:
Your PC is infected with 5 viruses!
ACTION REQUIRED
Your McAfee Subscription Has Expired!
Renew now to keep your PC protected.
If your PC is unprotected, it is at risk for viruses and other malware.
People who aren't familiar with scams of this nature can mistakenly assume that trustworthy security providers have detected infections on their computers and that swift action is required. Users who are not very aware of these aspects are exactly who scammers are going for.
Please do not trust messages which claim that your system has been infected with malware, as they are all fake. Reputable security vendor names such as McAfee or Norton have been increasingly used in various scam schemes. In fact, other fake sites like Protectyour-device.com, Suldo.click, Stayundercontrol.online are using the exact same messaging pattern. Keep in mind that legitimate security software needs to be installed on your system for it to yield results. Everything portrayed on Defenderfocus.xyz is generated via the browser and is fake.
| Name | Defenderfocus.xyz |
| Type | Scam, fraud, phishing, redirect |
| Distribution | Redirects, misleading ads, software bundling |
| Operation | Shows fake virus infection messages to promote software for profit. Also asks to enable push notifications |
| Dangers | Loss of finances due to fake subscriptions; redirects to other malware-laden, scam websites; installation of potentially unwanted or malicious software |
| Removal | You should not interact with the contents shown by a scam website and check your device with legitimate security software to check for adware |
| Other tips | Third parties can employ cookies to continue tracking your online activities, so we recommended clearing browser caches and other leftover PUP files with FortectIntego |
Deal with adware
If you frequently visit websites like Defenderfocus.zyx and your browser is overwhelmed with ads, it's likely that adware has infiltrated your system without your knowledge. Without a doubt, you should not keep this software installed on your system, as not only does it produce various phishing[2] messages and shows intrusive ads, but it also tracks your online activities. Therefore, we would recommend taking care of the infection automatically.
To effectively remove all unwanted and malicious programs from your device, use SpyHunter 5Combo Cleaner or Malwarebytes security software that can locate and remove all the malicious components. While the manual steps below can help you deal with most potentially unwanted apps, a security scan will ensure that invisible malware like Trojans or backdoors is eliminated too. After that, use FortectIntego to remove trackers from the web browser caches[3] and fix virus damage if such has occurred.
If you would like to go the manual route, we suggest you start by checking your browser extensions, as it is one of the most common forms of adware.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the window's top-right).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.

MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Adware can also be installed on the system level. In this case, you would have to access the list of installed applications and get rid of suspicious media players, system optimizers, file converters, and similar software. If you just recently installed an app and noticed suspicious activity, uninstall it at once. On the other hand, if you aren't completely sure, we recommend leaving this step for security software instead.
Windows
- Enter Control Panel into the Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

Mac
While moving apps into Trash is how you delete most normal applications, adware tends to create additional files for persistence. Thus, you should look for .plist and other files that could be related to the virus. If you are not sure, skip this step entirely.
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
Disable unwanted push notifications
The Defenderfocus.xyz website will prompt you to enable push notifications immediately upon entering the site. Clicking the “Allow” button within the notification prompt would allow the site to deliver you ads at any time. If you enable these notifications, you may start receiving suspicious pop-ups at random times that could show further scam content or lead you to other malicious sites. It is recommended that you ignore these pop-ups and use the following instructions to get rid of them instead:
Google Chrome
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Safari:
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

How to prevent from getting adware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Adware. Investopedia. Source of financial content on the web.
- ^ Phishing attacks. Imperva. Application and data security.
- ^ Browser cache. PCMag. The Latest Technology Product Reviews, News, Tips.
