Desync ransomware (Virus Removal Guide) - Recovery Instructions Included
Desync virus Removal Guide
What is Desync ransomware?
Desync ransomware is a cryptovirus that mostly targets corporate devices and encrypts data with AES + RSA algorithms
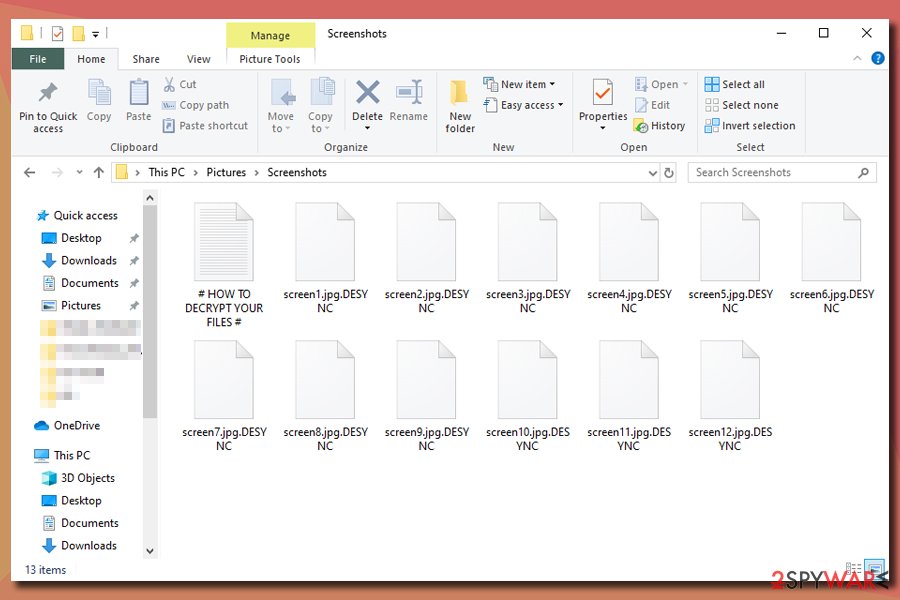
Desync ransomware is a file locking virus that was first spotted in January 2019, although the attackers updated malware – a new version was released in November of the same year. Upon infecting the targeted machine, the virus applies sophisticated encryption algorithms – AES and RSA and encrypts all documents, databases, pictures, spreadsheets, and other files, also appending .DESYNC marker.
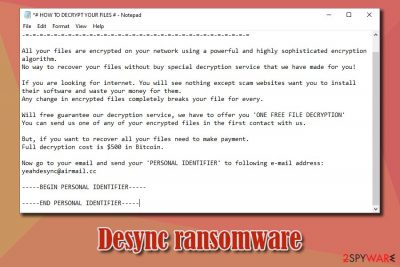
Such modified files can no longer be accessed by Desync virus victims, and, for them to be aware of what happened to their computers/networks, a ransom note # HOW TO DECRYPT YOUR FILES #.txt is dropped on desktops. The text file serves as the first mean of communication between hackers and users, which states that only “a special decryption service” could unlock all files. What Desync ransomware developers mean is payment in Bitcoin or another cryptocurrency – to be made after contacting hackers via desync@airmail.cc or yeahdesync@airmail.cc email.
While there is no Desync ransomware decryptor developed yet, paying ransom to crooks is dangerous, as receiving a tool that does not work or not receiving one at all is one of the outcomes that victims can face. Instead of paying the ransom, users can first remove Desync ransomware and then apply alternative file recovery methods provided below.
| Name | Desync ransomware |
| Type | Cryptovirus, file-locking malware |
| Malware relations | Researchers found that Desync has several similarities with Indrik ransomware |
| Cipher | Virus applies a combination of AES and RSA encryption algorithms to lock data |
| File extension | Each of the encrypted files receive .DESYNC extension and can no longer be accessed by victims |
| Ransom note | Ransom note # HOW TO DECRYPT YOUR FILES #.txt is dropped into each of the affected folders and the desktop |
| Contact | Hackers ask to contact them via desync@airmail or yeahdesync@airmail.cc for the negotiations |
| Ransom cost | $500 in Bitcoin, although ransom demands may vary depending on the company/individual affected |
| Malware removal | While some ransomware viruses might self-delete after infection, there might be various components and secondary payloads present on the system. Thus, the affected users should access Safe Mode and perform a full system scan with anti-malware software like SpyHunter 5Combo Cleaner or Malwarebytes |
| File decryption | The only secure way to retrieve encrypted data is by recovering it from backups. Without them, it might also be possible to retrieve at least some of files by using third-party recovery software – check for more details below |
| System recovery | The ransomware changes the way the system operates and affects multiple important files. To restore Windows OS to its pristine condition and remove all malware damage, we suggest using FortectIntego |
It is yet unknown how Desync ransomware is distributed, as there were very few incidents in the wild. However, because malicious actors mainly target organizations, it is highly likely that they use of the following delivery methods:
As soon as Desync ransomware gains access to the targeted machine, drops files like Desync.exe, final.exe, [random].exe into the system's %Temp% folder and implements various changes to it. For example, it modifies the Windows registry to establish persistence, deletes Shadow Volume Copies to prevent quick recovery, etc.
It is also important to note that one of the mutexes created by Desync ransomware is named “Global/Indrik,” and security researchers managed to find other similarities with Indrik ransomware – there is a chance that same threat actors started distributing new malware for monetary gain.
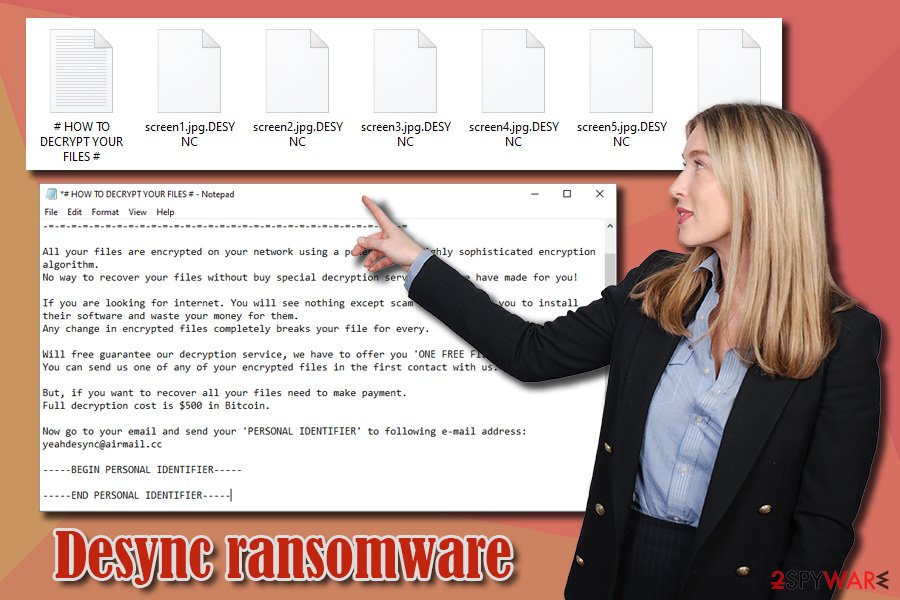
Once the necessary changes are completed, Desync ransomware encrypts all the files on the device/network and drops a ransom note # HOW TO DECRYPT YOUR FILES #.txt. Malware-affected files are easy to spot, as they are all appended with .DESYNC extension (for example, a picture.jpg is turned into picture.jpg.DESYNC). One of the most recent notes that victims received reads the following:
-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
*** PLEASE READ THIS FILE IF YOU WANT TO GET BACK YOUR FILES ***
-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=All your files are encrypted on your network using a powerful and highly sophisticated encryption algorithm.
No way to recover your files without buy special decryption service that we have made for you!If you are looking for internet. You will see nothing except scam websites want you to install their software and waste your money for them.
Any change in encrypted files completely breaks your file for every.Will free guarantee our decryption service, we have to offer you 'ONE FREE FILE DECRYPTION'
You can send us one of any of your encrypted files in the first contact with us.But, if you want to recover all your files need to make payment.
Full decryption cost is $500 in Bitcoin.Now go to your email and send your 'PERSONAL IDENTIFIER' to following e-mail address:
yeahdesync@airmail.cc—–BEGIN PERSONAL IDENTIFIER—–
[redacted]
—–END PERSONAL IDENTIFIER—–
Considering that the “Big Game Hunting” ransomware examples like Sodinokibi, SamSam, Ryuk, LockerGoga, etc., demand ransom sums of tens of thousands of dollars, $500 payment might seem like nothing much. However, be aware that Desync ransomware authors may never send the required decryption tool, or it might not work. Instead, examine alternative file recovery options we provide below – beware that Desync ransomware removal should be performed prior to that.
For that, use anti-malware software that could detect and delete Desync ransomware.[3] Finally, security experts[4] also recommend scanning the affected devices with a PC repair tool FortectIntego to avoid system failures after the infection is terminated.
Protect your computer from ransomware attacks
File locking malware that targets organisations can be a deadly blow to its operations and cost thousands of dollars in recovery costs. Therefore, it is best to make sure that no ransomware enters the corporate computers in the first place.
As mentioned above, companies and businesses usually get infected via targeted attacks – malicious emails, brute-forcing or software vulnerabilities. To prevent malware attacks, it is vital to keep the healthy approach when it comes to cybersecurity and also rely on powerful anti-malware solutions. Here's what to do:
- To prevent targeted email campaigns, users should be aware about their existence and treat most of the emails with suspicious, especially “when they don't feel right.” Hackers can use email spoofing technique, so just looking at the sender address is no longer enough. It is vital to not enable macro feature on malware-infused MS Office documents or click on embedded links within PDF files;
- RDP connections are often used inside organisations due to its convenience. However, these remote connections are sometimes poorly protected and are great finds for cybercriminals – they scan the internet for connections using the default TCP port, apply a predetermined list of easily-guessable passwords and then install malware manually. To avoid that, RDP needs to be properly configured and protected by secure passwords;
- Finally, all the company-wide software and the operated system should be patched with the most recent security updates to avoid hackers from exploiting common vulnerabilities.
- Backup all server data at all times!
Desync ransomware removal steps
Many ransomware viruses are programmed to self-delete after the infection. Nevertheless, some malware might keep running its operations post-infection in order to encrypt all the incoming files. Additionally, many ransomware payloads come combined with other threats, such as banking trojans or backdoors. Thus, Desync ransomware removal is important and should be performed as soon as possible. It is also important to note that the action may break the encrypted files completely, so it is vital to make backups of the locked data before proceeding.
To remove Desync ransomware safely, victims should access Safe Mode with Networking as explained below and perform a full system scan with anti-malware software – it should find all the malicious components and terminate them. However, anti-malware software does not really fix corrupted Windows OS files, so for that job, we recommend using FortectIntego.
Getting rid of Desync virus. Follow these steps
Manual removal using Safe Mode
Ransomware might interfere with security software operation. Thus, access Safe Mode with networking to stop the malware from operating:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Desync using System Restore
System Restore is also an option when trying to remove Desync ransomware:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Desync. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Desync from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Desync, you can use several methods to restore them:
Data Recovery Pro might recover working copies of files
Data Recovery Pro might retrieve files from the hard drive, although the more the infected machine is used, the less there are chances of success.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Desync ransomware;
- Restore them.
Windows Previous Versions feature might help
This method might be functional if System Restore was enabled before ransomware encrypted files.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer might be useful in some cases
If the virus failed to delete Shadow Volume Copies, using ShadowExplorer might help you recover all your data.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Desync ransomware is currently not decryptable
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Desync and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Jakub Křoustek. Ransomware attacks via RDP choke SMBs. Avast. Security blog.
- ^ Vulnerability (computing). Wikipedia. The free encyclopedia.
- ^ Desync.exe. Virus Total. File and URL analyzer.
- ^ Novirus. Novirus. Cybersecurity advice from the UK.





















