Domainxnewma.com ads (Chrome, Firefox, IE, Edge)
Domainxnewma.com ads Removal Guide
What is Domainxnewma.com ads?
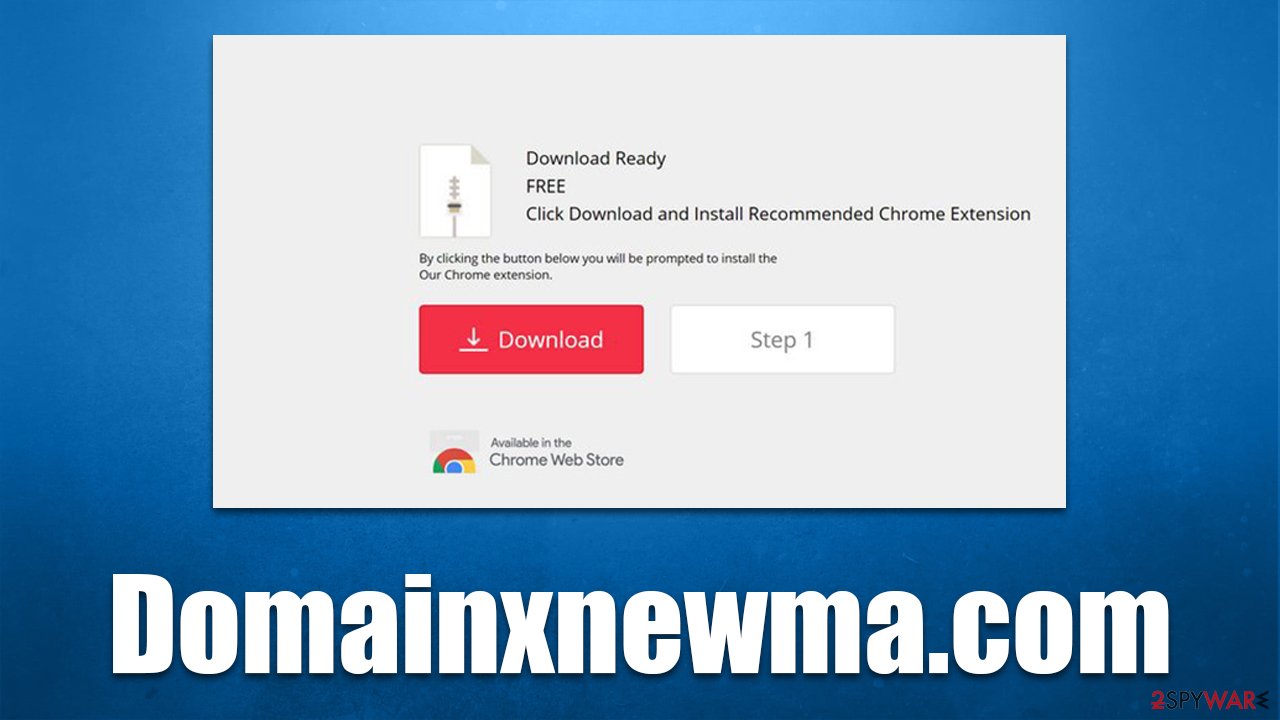
Domainxnewma.com is a misleading website that spreads potentially unwanted programs
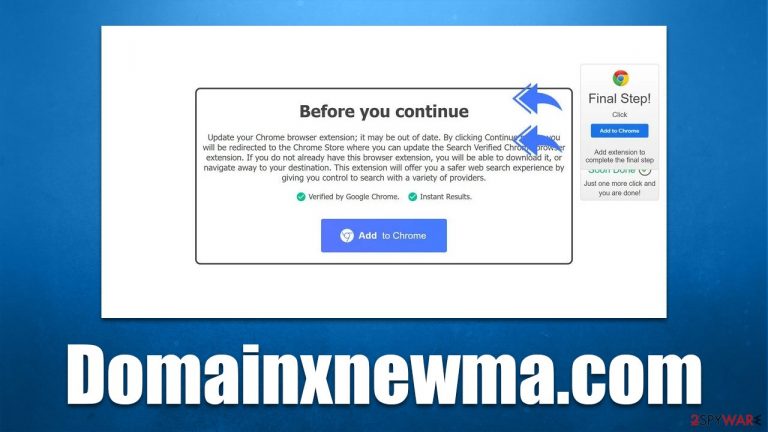
Domainxnewma.com is a deceptive website you can encounter under various circumstances, but not certainly willingly. Typically, you are likely to be redirected there when visiting high-risk websites such as peer-to-peer networks, illegal video streaming, X-rated, or similar places. Alternatively, adware could also be causing these redirects, especially if they are persistent and you see more ads everywhere you go.
The website is used by various crooks to advertise potentially unwanted programs; usually, browser hijackers are offered for users to be installed. Domainxnewma.com might also claim that an extension is outdated and needs to be updated, or push notifications should be enabled. Regardless of what you see on the page, we recommend not interacting with the promoted links or downloading software.
If you do, you are likely to install a browser-hijacking app on your system, which would take over your browser, show sponsored links, track your data, and reduce your online security. In this article, we will explain how to find and remove all potentially unwanted or malicious programs from your system.
| Name | Domainxnewma.com |
| Type | Redirect, scam, phishing, adware |
| Distribution | Software bundling, redirects, misleading ads |
| Symptoms | Shows fake ads and promotes potentially unwanted applications |
| Risks | Installation of potentially unwanted software, such as browser hijackers; redirects can also lead to other malicious websites, resulting in monetary loss or personal data disclosure to unknown parties |
| Removal | Perform a full system scan with SpyHunter 5Combo Cleaner or use manual guidelines below |
| Other steps | After PUP elimination, make sure you clean your browsers to prevent data tracking. FortectIntego can significantly quicken this process |
Potentially unwanted programs and redirects
Potentially unwanted software has always been a mixed bag, as it is usually not recognized as malicious by security applications, although it can have plenty of unwanted or even malicious traits. Adware, in particular, is one of the most annoying and useless applications that most users have to deal with.
There are a few ways people get infected, although they almost always install adware or other potentially unwanted programs themselves, even if they are tricked into doing so. Users sometimes install adware whenever they believe the app is not being such and trust in the advertised features.
In reality, adware puts monetization via advertising above everything else, hence the affected users can be intrusive ads showing up at random times. Some of these ads can even be malicious and should not be interacted with. It is also not a secret that potentially unwanted applications are actively spying on users in order to profit from targeted advertisements, which can put one's privacy at risk.
Some adware apps straight out fail to provide the functions they advertise (for example, file conversion), and remain on the system to earn revenue from ads. In the more extreme cases, PUPs may even use malicious persistence mechanisms and be difficult to uninstall manually.
Thus, if you have noticed suspicious redirects to Domainxnewma.com, Samplelocation3.xyz, Yexcelltoolse.xyz, Alcovenin.xyz, or similar deceptive websites, we recommend you check your system for adware immediately.
How to deal with scams
Online fraud is extremely prevalent – it varies in threat levels, although all of it is always disadvantageous for the affected users. Crooks usually go for money that comes from advertising or ads that are inserted into users' browsers illegally (thanks to adware). Alternatively, they might try to extort money from unsuspecting victims after promoting fake tech support services online.
Therefore, it is extremely important not to get tricked by websites such as Domainxnewma.com, regardless of how you ended up on them. If the claim is made that your system is infected and the reputable anti-malware software is allegedly providing these results, you should completely disregard them, as only an application installed on your system is capable of doing that.
You should also not get carried away with free gift cards and lottery winnings online. While the tech support scams focus on fear, fake winnings are often used to mislead users into believing that they are lucky winners and that they can get expensive items or money for free. All the scammers want is your information that can later be used for further phishing[1] attempts or other malicious purposes.
Adware removal
You are likely to see pop-ups and all sorts of other ads while browsing the web due to adware infection. Therefore, we recommend taking your time to remove them accordingly. Even if your system is not infected, you can rest assured that your personal safety and computer security are not in danger.
The first thing we recommend is scanning the system with powerful anti-malware software, such as SpyHunter 5Combo Cleaner or Malwarebytes. This will eliminate all the malicious programs on your system automatically and ensure all the processes, files, and other components are removed at once.
However, some PUPs might not be detected, so we recommend combining both manual and automatic removal. First, you should check your browsers for unwanted extensions:
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the window's top-right).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.

MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Some intentionally unwanted applications might be installed on the system level. However, if they are aggressive enough to cause browser redirects and show pop-up ads, most security programs would remove them at once. Thus, if this step seems confusing to you, you can skip it.
- Enter Control Panel into the Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till the uninstallation process is complete and click OK.

With Macs, application removal might seem straightforward, as most of them can be uninstalled by moving them to Trash. However, adware[2] might insert additional files, settings, and other components in order to increase persistence. Therefore, we recommend performing additional steps on a Mac:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
Finally, we recommend cleaning web browser caches to prevent data tracking by third parties. It is also recommended to regularly remove cookies and other web data to avoid corrupted caches and reduce the probability of session hijacking[3] attacks. For this, you could employ FortectIntego PC maintenance utility, or you can follow the manual guide below:
Google Chrome
- Click the Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies, and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Phishing attacks. Imperva. Application and data security.
- ^ Adware. Wikipedia. The free encyclopedia.
- ^ Allie Johnson. Session hijacking: What is a session hijacking and how does it work?. Norton. Security research blog.
