Erbi90s.click ads (fake) - Free Instructions
Erbi90s.click ads Removal Guide
What is Erbi90s.click ads?
Erbi90s.click attempts to impersonate a virus scan of a reputable vendor to profit from software purchases

Erbi90s.click is a deceptive site that you might be redirected to after clicking on a suspicious link or being rerouted by an automatic script while using Google Chrome, MS Edge, or another web browser. In some cases, adware infections could also cause these redirects. The main goal of the page is to scam users into believing that their systems are infested with multiple viruses so that they would purchase software licenses for security apps.
We do not recommend clicking on buttons or links hosted by Erbi90s.click scam, as you may end up losing money on services or software you don't need. Likewise, you might be redirected to a malicious website where you could be tricked into installing malware and infecting your system instead.
Upon entering the site, you may also be asked to enable push notifications, which would later deliver you ads and fake messages. We explain how to get rid of these pop-ups, as well as how to remove potentially unwanted applications[1] that could be lurking on your system without you knowing.
| Name | Erbi90s.click |
| Type | Scam, phishing, redirect |
| Scam content | Claims that the antivirus software license has expired and that the computer is exposed to various malware |
| Distribution | Compromised websites, pop-up ads, potentially unwanted applications |
| Risks | Loss of finances due to fake subscriptions redirects to other malware-laden, scam websites, installation of potentially unwanted or malicious software |
| Removal | Do not interact with links or other content of a scam site. Instead, check your system with SpyHunter 5Combo Cleaner security software |
| Other tips | Third parties can use cookies to continue tracking your online activities, so you should browser caches and other leftover files with FortectIntego to secure your privacy |
Many criminals engage in online fraud because it is anonymous and easy to do. With the help of the internet, some people decide to play dirty and create phishing content in order to make more money. Phishing content is more effective than other forms of advertising in some cases, which makes it an attractive option for criminals.
There are various forms of scams out there, and technical support or fake virus infection scams remain among those most used. Erbi90s.click is not a unique site; in fact, we have already covered multiple others claiming that the system is infected (or is in danger) and security software needs to be purchased – Control-scanning.com, Alltimesecuritysystem.live, or Protectwatcher.xyz, are just a few examples.
Scammers imitate fake virus scanners
If you land on the website, you'll likely see several windows that resemble a system scan from McAfee. In just a few moments, you'll receive what appears to be harsh truth – your system is infected with multiple viruses. The full message reads as follows:
Your PC is infected with 5 viruses!
ACTION REQUIRED!Your McAfee Subscription Has Expired!
Renew now to keep your pc protected.
If your PC is unprotected, it is at risk for viruses and other malware.
Also, you may be shown another pop-up on top, which closely resembles a Blue Screen of Death screen – something often done in social engineering[2] attacks. All these elements, including the name of McAfee, are used in order to make the scheme more believable to users, so they would give in and proceed with the steps provided.
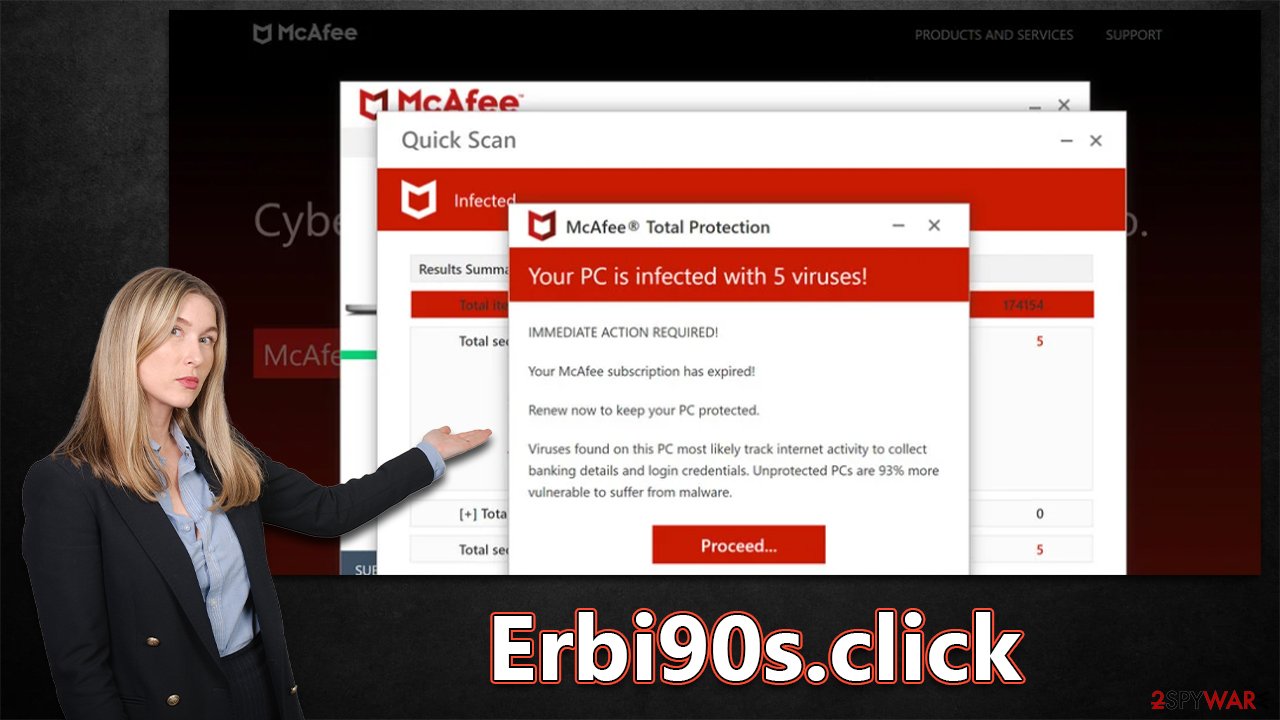
Soon after receiving this message, users are shown the “Renew subscription” or “Proceed” buttons (depending on the pop-up window people are viewing). Those who use them are then redirected to a software purchase page – allegedly to remove the found viruses.
This way, crooks can monetize the clicks and software downloads made by users via the affiliate links. Even if the promoted software might be legitimate, the people behind the scheme are scammers and shouldn't be rewarded for this activity.
To avoid being tricked, ensure you never listen to any notifications claiming that your system has been infected with viruses – no website can tell that, as legitimate security software needs to be installed on the system to diagnose it correctly. It is also not difficult to see how the URL of the page showing the face scan Erbi90s.click has nothing to do with McAfee or any other legitimate companies.
Adware removal
After you've landed on the Erbi90s.click scam website, the first step in repairing your computer is to check for adware. While everything displayed on the virus scan result page is fake, the possibility of adware infection remains, as these potentially unwanted apps are commonly used to expose users to phishing[3] content and ads when browsing.
The most foolproof way to know if you have adware is by scanning your entire system with SpyHunter 5Combo Cleaner or Malwarebytes security software – this will delete all harmful components at once. Although you can try to get rid of useless programs manually, it is much faster and simpler to do so automatically.
Moreover, uninstalling some helpful programs could unintentionally end up doing more damage than good. That being said, once you're confident that your device doesn't have any malware or adware on it, the next step is clearing out your browser's cookies and other tracking data. You can use FortectIntego for this task or follow the directions below:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

How to stop the push notification spam
If you hit the “Allow” button for push notifications when you first enter Erbi90s.click, you'll be spammed with pop-ups later. These pop-ups can happen anytime, even if you're not actively using your browser.
While the majority of users would ignore the request, some might accidentally click the “Allow” button, which would cause intrusive pop-ups to appear on users' desktops and show inappropriate, deceptive content, and possibly even contain malicious links. It is not advised to respond to these notifications because doing so could endanger your security and safety. Instead, adhere to the advice below to stop the intrusive ads:
Google Chrome
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the URL's drop-down menu.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.

- Click on More actions and select Block.
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ What is a potentially unwanted application?. Blockbit. Cybersecurity solutions.
- ^ Social Engineering. Imperva. Application and data security.
- ^ Phishing attacks. Imperva. Application and data security.
