ExemplaryDatabase Mac virus (Free Guide)
ExemplaryDatabase Mac virus Removal Guide
What is ExemplaryDatabase Mac virus?
ExemplaryDatabase is a Mac virus that can breach your privacy and install additional payloads
ExemplaryDatabase Mac virus, a member of the notorious Adload malware family, presents a significant risk to Mac users. This harmful virus is engineered to seize control of web browsers, funneling users toward harmful websites and clandestinely extracting their personal data for nefarious activities, such as unauthorized sales on the dark web.
The task of eliminating ExemplaryDatabase Mac virus is notably complex. It integrates an array of components and employs diverse methods to stay hidden and resist removal attempts. Failure to thoroughly remove this virus can lead to its resurgence, perpetuating its damaging impact on the infected system.
For the safety of your computer and the protection of your personal information, it's crucial to act swiftly to remove the ExemplaryDatabase. Recognizing the challenges involved in this process, detailed guidance is provided to assist in effectively tackling this cybersecurity threat.
| Name | ExemplaryDatabase |
| Type | Mac virus, adware, browser hijacker |
| Malware family | Adload |
| Distribution | Fake Flash Player installers or bundled software from malicious sources |
| Symptoms | A new extension is downloaded to the browser, along with a matching app; search and browsing preferences are changed to use a different search engine; new user profiles and login items are created on the account; intrusive advertising and redirects |
| Removal | You can remove Mac malware effectively with the help of a powerful security tool, such as SpyHunter 5Combo Cleaner. If you want to attempt to get rid of the threat yourself, check the manual guide below |
| Optimization | By cleaning web browser caches and web data, you would ensure that third parties can no longer track you – use FortectIntego for this task |
How malware is distributed and how to avoid infections
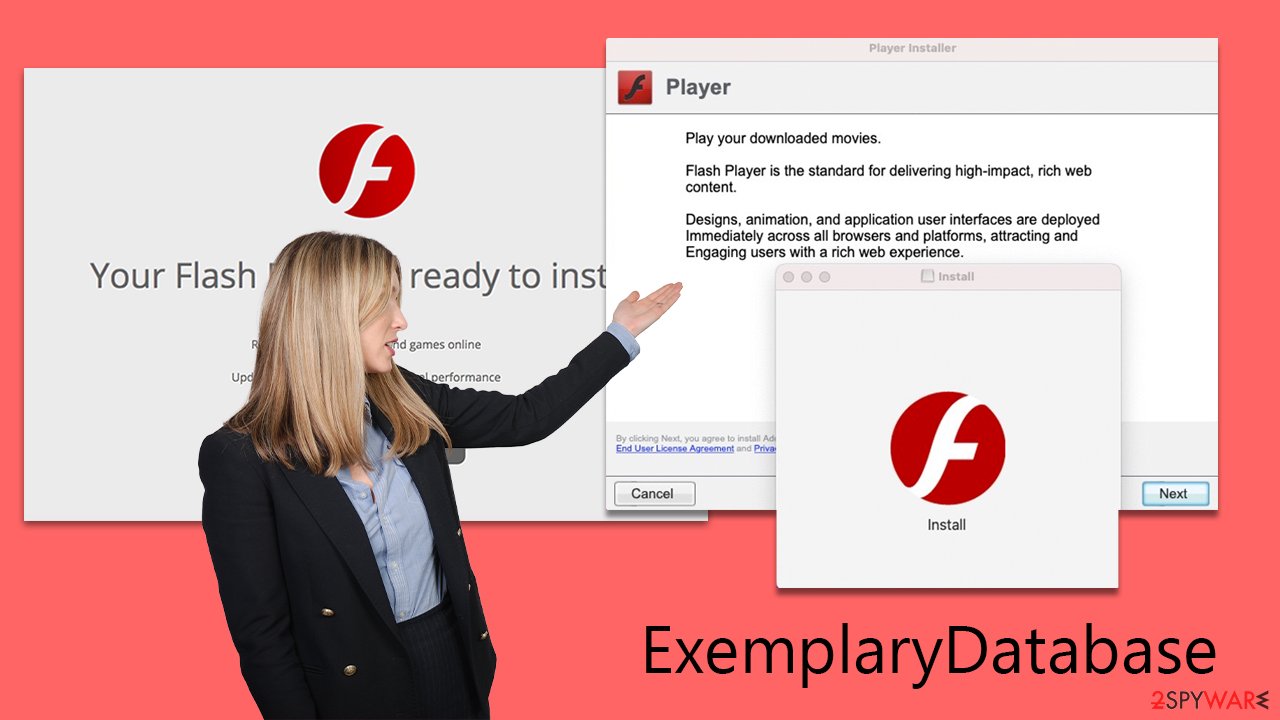
Adload variants, including ExemplaryDatabase, are predominantly disseminated via two principal channels: deceptive Flash Player updates and illicit software cracks or unauthorized software installers.
A prevalent tactic for spreading this malware involves counterfeit Flash Player updates. Long known for its multimedia functionalities, Flash Player was ultimately phased out by Adobe due to its instability and the multitude of security flaws that required frequent patching.
Users are often duped into downloading these bogus Flash Player versions from untrustworthy sites featuring phishing tactics. For instance, users might be misled by prompts urging them to update Flash Player to access specific content. These prompts are misleading and should be disregarded. Additionally, this malware can be masked as “Installer.app,” a guise also employed for distributing other malicious software like the Shlayer Trojan.
ExemplaryDatabase is also spread through illegal software cracks and pirated software installers. These unauthorized avenues often used to access otherwise paid software, can serve as conduits for the virus, embedding the malware within pirated applications unbeknownst to the user.
To safeguard Macs against Adload strain and other malware, it's crucial for users to only download software from trusted sources. They should also refrain from engaging with dubious links or downloading attachments from unknown origins. Keeping anti-virus software updated and adhering to safe browsing practices are also key measures in maintaining cybersecurity.
How malware functions
ExemplaryDatabase poses serious threats to macOS users. Its design incorporates a wide array of capabilities specifically aimed at compromising the security of the user's system.
Key features of the virus include:
- Intrusive advertising campaign. The virus can inject unwanted ads into websites, disrupting the user's browsing experience. It also manipulates search results, leading to inaccurate and misleading information.
- Proxy server setup. It establishes a proxy server, enabling cybercriminals to redirect and control internet traffic. This function is exploited to monetize user traffic through unsolicited ads, generating illegal profits.
- Data theft. The malware has the potential to harvest personal information, such as passwords and financial details, from compromised systems. This poses a significant risk of identity theft and financial fraud.
In addition to these features, ExemplaryDatabase demonstrates a disturbing capability to install other Adload variants, escalating the severity of the threat. This multiplicity of threats undermines the digital security of affected users.
Further complicating its removal, it can bypass macOS's native security features like Gatekeeper and XProtect. This results in stubborn infections that continually expose users to risks.
Finally, the malware's ability to implant itself deeply within the Mac's system layer allows it to conduct harmful activities covertly. This deep integration makes its complete eradication a formidable task. Fortunately, despite these challenges, there are effective methods available for removing this threat, as outlined in the following instructions.
Effective malware removal steps
The removal of ExemplaryDatabase, given its deep integration and high-level system access, is a complex endeavor. Unlike standard applications, this virus scatters multiple malicious files across the system, establishes new user profiles, and creates login items, all of which complicate manual removal. It's important to note that even attempting to manually remove it might not fully eliminate the malware from your system.
Therefore, we recommend the use of trusted anti-malware software, such as SpyHunter 5Combo Cleaner or Malwarebytes for an automated removal process. Employing these specialized tools is a more effective and reliable approach to removing the virus. These programs are adept at identifying and eliminating a broad spectrum of malicious software, increasing the likelihood of thoroughly purging the virus.
Regardless of the chosen removal method, a thorough clean-up of your web browser caches is highly advisable. This step is crucial for maintaining a healthy system and reducing the risk of future issues.
Key steps for ExemplaryDatabase removal include:
- Shutting down active processes: Before proceeding with removal, ensure that all active processes related to ExemplaryDatabase are terminated. This can be done through the Activity Monitor.
- Using anti-malware software: Leverage reliable security software to automatically detect and remove the malware.
- Cleaning web browser caches: Post-removal, clear your web browser caches to enhance system health and security.
Remember, while manual removal is technically possible, it's often incomplete and risky. Relying on professional anti-malware tools provides a safer and more comprehensive solution for dealing with such sophisticated threats.
- Open Applications folder.
- Select Utilities.
- Double-click Activity Monitor.
- Here, look for suspicious processes and use the Force Quit command to shut them down.
- Go back to the Applications folder.
- Find the malicious entry and place it in Trash.
![Uninstall from Mac 1 Uninstall from Mac 1]()
Login items are responsible for booting the malicious app as soon as the computer starts up, while Profiles tackle different account settings. These malware-related components should be deleted as follows:
- Go to Preferences and pick Accounts.
- Click Login items and delete everything suspicious.
- Next, pick System Preferences > Users & Groups.
- Find Profiles and remove unwanted profiles from the list.
Finally, you should get rid of Launch Daemons and other configuration data left by malware. Proceed with the following:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and delete all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
Removing trackers from the drivers
Removing malware components from web browsers, such as harmful extensions and tracking elements like cookies, is a vital step in the process of eliminating the virus. If not properly addressed, these remnants can continue to pose risks to your privacy and security.
For efficient and thorough removal of these browser trackers, we recommend using a specialized tool FortectIntego designed for this purpose. Such software automatically identifies and clears any residual or malicious trackers left by the virus.
For those who prefer a manual approach, detailed instructions are provided below to assist in purging your browsers of these persistent components. While manual clearance can be effective, it tends to be more time-consuming and demands meticulous attention to detail to ensure the complete removal of all malicious elements. Opting for a maintenance application offers a more straightforward and dependable solution, but manual removal remains an option for those who choose it.
To begin, focus on removing any malicious extensions associated with ExemplaryDatabase:
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Clear cookies and other web data from your browsers:
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
In some cases, resetting the browser is the best choice once all adware is deleted from your Mac:
Safari
- Click Safari > Preferences…
- Go to the Advanced tab.
- Tick the Show Develop menu in the menu bar.
- From the menu bar, click Develop, and then select Empty Caches.
![Reset Safari Reset Safari]()
Google Chrome
- Click on Menu and select Settings.
- In Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.
![Reset Chrome 2 Reset Chrome 2]()
How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.








