Feg ransomware (virus) - Free Guide
Feg virus Removal Guide
What is Feg ransomware?
Feg ransomware is a type of malware designed for file locking, resulting in easy money extortion by cybercriminals
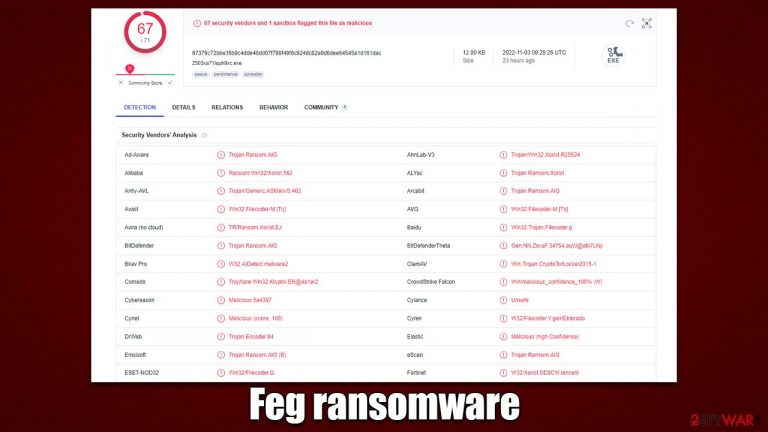
Feg ransomware is a malicious program designed to encrypt[1] all personal files on the system and then demand ransom from the victim. Belonging to the broad family of Xorist ransomware, it began spreading in early November 2022. Upon entering a Windows system, it may spread laterally via the network if such is available and protected poorly.
After the infection, malware would encrypt all files located on the network and every affected machine. This would result in pictures, videos, documents, databases, and other personal files receiving a .feg extension. Because a sophisticated encryption algorithm is used, modifying or even opening these files becomes impossible, although they are not corrupted but rather locked.
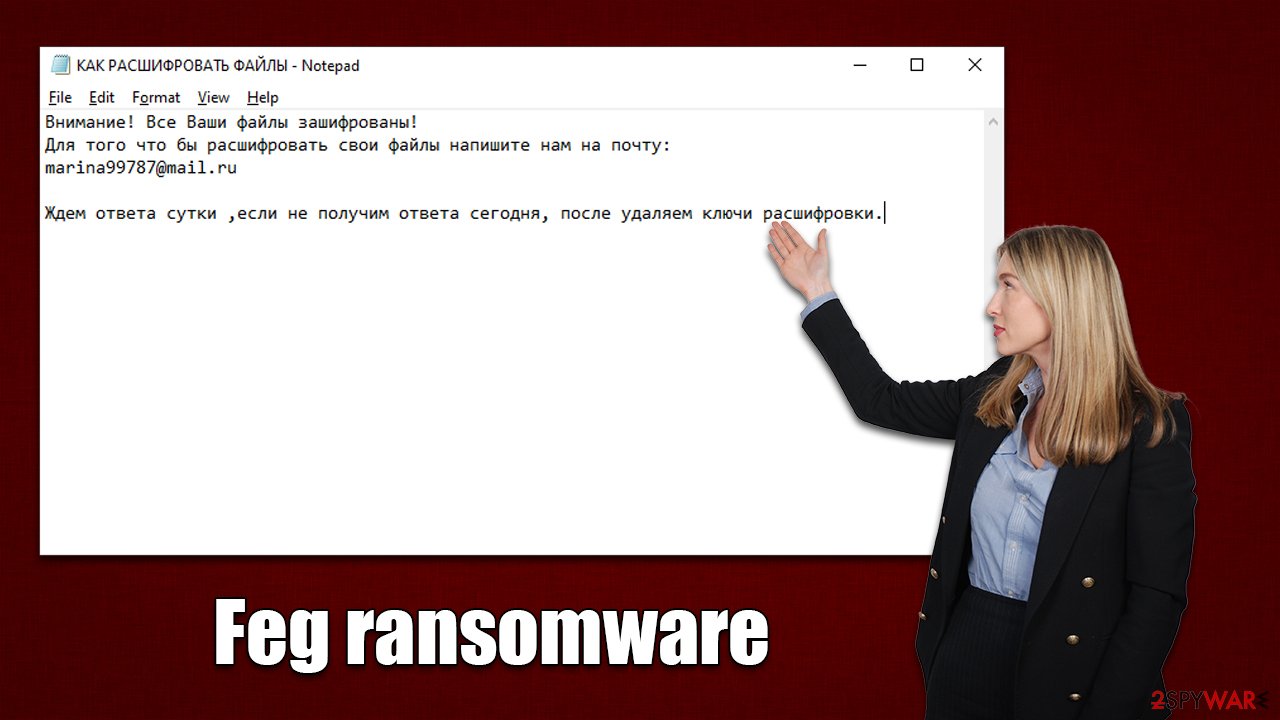
In the note КАК РАСШИФРОВАТЬ ФАЙЛЫ.txt, which is dropped right after the Feg virus encrypts the data, ransomware authors explain to victims that their files are encrypted and that the only way to restore them is by paying a ransom in bitcoin. Cybercriminals also leave a contact email marina99787@mail.ru, which is meant to be used for communication purposes between crooks and victims to negotiate the price and other details. We do not recommend contacting them and instead employ alternative methods to restoring files after malware is eliminated.
| Name | Feg virus |
|---|---|
| Type | Ransomware, file-locking virus |
| malwre family | Xorist |
| File extension | .feg, appended to each of the personal files |
| Ransom note | КАК РАСШИФРОВАТЬ ФАЙЛЫ.txt |
| Contact | marina99787@mail.ru |
| File Recovery | If no backups are available, recovering data is almost impossible. However, we suggest you try the alternative methods that could help you in some cases – we provide them below |
| Malware removal | Perform a full system scan with powerful security software, such as SpyHunter 5Combo Cleaner |
| System fix | Malware can seriously tamper with Windows systems, causing errors, crashes, lag, and other stability issues after it is terminated. To remediate the OS and avoid its reinstallation, we recommend scanning it with the FortectIntego repair tool |
Ransom note delivered in Russian
We have previously discussed ransomware like Tuow, Adlg, or Venolock, and many others, all of which employ a ransom note. In fact, ransomware developers are almost always making sure that these messages are delivered to users, as they would not be able to contact crooks, preventing them from receiving any type of payment.
The absence of a ransom note after infection may mean one of two things: either it was not delivered, or it was of a destructive type. The latter can happen for a variety of reasons, such as bugs in malicious programs. Therefore, Feg ransomware ensures that the ransom note is delivered, although, unlike many other viruses of this type, it delivers the body text written in Russian – it reads:
Внимание! Все Ваши файлы зашифрованы!
Для того что бы расшифровать свои файлы напишите нам на почту:
marina99787@mail.ruЖдем ответа сутки ,если не получим ответа сегодня, после удаляем ключи расшифровки.
Even if victims can't read Russian, all they essentially need is the contact email. However, looking at the translation, cybercriminals claim that if no contact is made within a day after infection, decryption keys meant for file restoration would be deleted. This is done in order to frighten users and make them pay sooner rather than later. In addition, the virus delivers a pop-up message which shows an identical text.
We recommend performing Feg ransomware removal and then employing alternative methods for file recovery – we provide detailed instructions for both of these procedures below.
Disconnect the affected computer from the network and internet
Malware can communicate with remote Command & Control[2] servers through the Internet connection, which in some circumstances, could give attackers remote access.
Therefore, you should disconnect your PC from the network and the internet before moving further with anything else. To do this, all you have to do is unplug the computer's ethernet connection or turn off the WiFi. You can also disconnect from your network in the following manner if you have one that you use:
- Type in Control Panel in Windows search and press Enter
- Go to Network and Internet

- Click Network and Sharing Center

- On the left, pick Change adapter settings

- Right-click on your connection (for example, Ethernet), and select Disable

- Confirm with Yes.
After encrypting all files, the majority of ransomware programs self-destruct, while others may leave behind different dangerous components. Additionally, because ransomware frequently spreads along with other viruses, subsequent strains may carry on stealthily encrypting all incoming files.
The only method to determine whether this is true is to run a system scan with SpyHunter 5Combo Cleaner, Malwarebytes, or another trustworthy anti-malware program. If the infection is not well confined, security software may quickly and easily identify all the dangerous files and delete them right away, preventing any damage that might later emerge. If malware is interfering with this process, you can always enter Safe Mode and perform elimination steps from there:
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on the Start button and select Settings.
- Scroll down to pick Update & Security.
- On the left side of the window, pick Recovery.
- Now scroll down to find the Advanced Startup section.
- Click Restart now.
- Select Troubleshoot.
- Go to Advanced options.
- Select Startup Settings.

- Click Restart.
- Press 5 or click 5) Enable Safe Mode with Networking.
Recover your files in alternative ways
Although some users assume that after malware removal is completed, their files will be automatically restored, this is not the case at all. Because ransomware undertakes the encryption process on its own, once it is finished, the data cannot be restored to its original state by removing the infection.
The scenario gets more difficult because the encryption locks files with a complicated alphanumeric string. The attackers are the only ones with access to the key. But for the reasons already mentioned, we advise attempting alternate approaches first, starting with data recovery software. Before proceeding, make sure you make copies of encrypted files to make sure they don't get corrupted in the process.
- Download Data Recovery Pro.
- Double-click the installer to launch it.

- Follow on-screen instructions to install the software.
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders which you want the files to be recovered from.

- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.

- Press Scan and wait till it is complete.

- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
Decryption tools might also be created for certain ransomware strains thanks to the efforts of security researchers. In some cases, law authorities seize the servers of malicious actors,[3] which allows the keys to be released to the public, which is usually done by security vendors. Here are a few links you might find helpful:
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

Fix damaged system files
After malware infection, Windows is no longer the same, as some system files might get damaged or even destroyed. This can result in system instability – crashes, failure to launch programs, BSODs,[3] etc. If you suffer from these problems after eliminating the infection, use data recovery software, as explained below.
- Download FortectIntego
- Click on the ReimageRepair.exe

- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process

- The analysis of your machine will begin immediately

- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.

How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Encryption. Investopedia. Sharper insight, better investing.
- ^ Command and Control [C&C] Server. Trend Micro. Security blog.
- ^ Ryan Gallagher. Police arrest five people tied to ransomware group REvil. Fortune. Official website.
