Files-null.com ads (scam) - Free Guide
Files-null.com ads Removal Guide
What is Files-null.com ads?
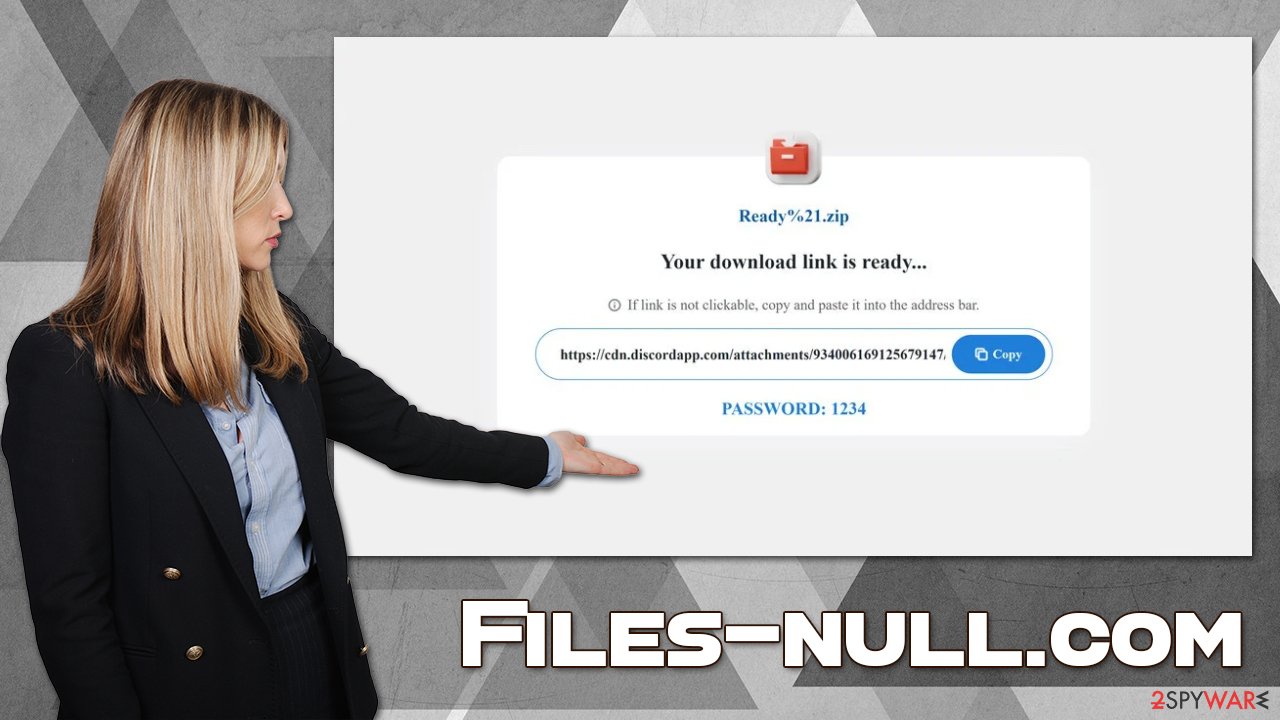
Files-null.com shows misleading ads to make visitors download potentially unwanted software

Files-null.com is a malicious website that most users encounter inadvertently during their web browsing sessions. It does not matter whether Google Chrome, MS Edge, Mozilla Firefox, or another web browser is used. The contents of the site are always misleading in one way or another; in most cases, visitors are asked to download and install potentially unwanted or dangerous programs on their systems.
While in most cases, users might venture to Files-null.com after clicking a link on another website, it is also possible that a potentially unwanted program, namely, adware, is present on the device. Thus, even if you have not installed any promoted software, we advise checking the system thoroughly with the help of the instructions we provide below.
How do scams work?
Phishing[1] websites are created by unfair individuals who are seeking some type of benefit by misleading and fooling people into doing something they otherwise wouldn't, and there's plenty to gain. For example, technical support scam authors commonly provide fake support numbers and then attempt to remotely connect to users' devices. They then compromise them by installing malware, presenting regular operating system elements as malicious, or demanding high payments for the fake removal of malware.
The scheme of Files-null.com is rather simple, though – the main goal of it is to make users download software and earn money through the pay-per-install scheme that is commonly used in various affiliate programs. Unfortunately, insecure ad networks might advertise software that is relatively useless and sometimes might even be unwanted or even dangerous.
Adware in the form of browser extensions that are supposed to fulfill some type of role (block ads, convert files, etc.) is one of the most common scam goals. Those who install promoted software might run it for days or even weeks before they realize that pop-ups, deals, offers, banners, coupons, and other intrusive content are generated by a particular app downloaded from Files-null.com.
If you have downloaded anything from this or another similar website, you should immediately uninstall it and follow our check lists in order to ensure that your system is secure and malware-free.
| Name | Files-null.com |
|---|---|
| Type | Scam, phishing, redirect, adware |
| Operation | Uses deceptive, misleading messages to make people install potentially unwanted or even malicious apps/extensions |
| Symptoms | If infected with adware, the web browser might start redirecting to misleading and even malicious websites; users might be infected with additional PUPs or malware, disclose their personal data to insecure parties, or suffer financial losses |
| risks | Ads and links to sites displayed by the website might be dangerous: users might suffer from monetary losses, install malware or potentially unwanted programs on their systems, or disclose their sensitive data to cybercrooks |
| Removal | Do not interact with the contents shown by a scam website and instead, check your system for adware or malware infections with SpyHunter 5Combo Cleaner security software |
| Other steps | Employ FortectIntego to clean your system from PUP leftover files and fix any damage done by the virus |
How do you end up on malicious websites?
There are two primary reasons why users end up on malicious websites: they are either being redirected by an aggressive adware program installed on their systems or they have fallen victims to a complex redirect/hyperlink dynamic while browsing potentially dangerous websites. Either way, the result of this is that those affected may end up being victims of an elaborate scam or, even worse – have their personal data compromised or dangerous malware installed.
Let's talk about the high-risk websites first. While most people are aware that there are certain groups of websites they should avoid and never visit them on purpose, others are doing so intentionally in order to receive some type of benefit for themselves, all while believing that the dangers are not that great in comparison to the reward.
However, this is a very dangerous stance to have, as it has been proved time and again that torrents, warez, and software crack websites host tons of malicious content – from the executable files themselves to malicious ads that were inserted by cybercriminals to exploit vulnerabilities present on some users' devices.
Of course, such places are known for including fake links – fake “Download” buttons or clicks on empty spaces are extremely prevalent. As a result of these, users are typically rerouted to other malicious websites, where they could be fooled into subscribing to useless services, accepting push notifications from malicious parties, exposing their personal details, or installing even more malware. Files-null.com is one of the websites that users might be redirected to this way.
Another reason for redirects is adware that could secretly run in the background. Most aggressive adware can start displaying pop-up windows and insert a virtual layer of ads when users visit completely unrelated websites. Therefore, we strongly recommend following the instructions below and checking the system thoroughly.
Adware removal
Adware is a type of potentially unwanted software that can take up different forms – from programs installed on the system level to browser extensions. Most aggressive adware might be absent from the list of the installed application, making it more difficult for users to eliminate. Another obfuscation technique used by adware and malware is not running any active windows or disguising active processes under legitimate Windows process names like csrss.exe or winrmsrv.exe.
Therefore, we recommend starting with a system scan with SpyHunter 5Combo Cleaner or Malwarebytes security software, as this would immediately eliminate all the dangerous malware and malicious files from the system at once. Since some potentially unwanted applications might not always be detected, we recommend checking the installed app section as well:
Windows
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

Mac
While moving apps into Trash is how you delete most normal applications, adware tends to create additional files for persistence. Thus, you should look for .plist and other files that could be related to the virus. If you are not sure, skip this step entirely.
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
Adware often takes a form of an extension – it is easy to produce and has enough functions to fulfill its purpose – deliver advertisements to users. Therefore, you should check if your browser does not have apps installed you never installed yourself. Note that some extensions might be installed for a while until they start showing unwanted symptoms.
Thus, if you are not sure which extension is showing you ads, you can simply remove them all then reinstate them one by one. After you do so, make sure you clean your browsers from cookies and other web data files to ensure no data tracking continuously takes place. If you want a quicker solution, we recommend using FortectIntego instead.
Google Chrome
- Click the Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Other tips
There are all sorts of scams on the world wide web and the scale of damage and other unwanted consequences may differ drastically, depending on what type of fraud it is, what's the goal of the cybercriminals is, and what the actions of those who encounter it. There are different levels of damages and consequences that could be suffered due to phishing attacks, thus it is important to make sure not to get tricked by them.
First of all, you should ensure that you encounter as little fraudulent content as possible. To achieve that, you should start from your own actions:
- Employ powerful anti-malware, such as SpyHunter 5Combo Cleaner or Malwarebytes, to protect yourself from malware attacks;
- Update all software and the operating system to avoid dangers of software vulnerabilities;[2]
- Do not ignore warnings from your security software and dismiss them as false positives;
- When installing freeware,[3] always be aware that you might be offered optional applications in a deceptive manner, so watch out of pre-ticked boxes, fine print, misplaced buttons, and similar tricks;
- Always choose Advanced or Custom settings instead of Recommended/Quick one to stay in control of what is being installed on your system;
- Protect all your accounts with comprehensive passwords and never reuse them;
- Employ additional security tools such as ad-blockers to prevent the execution of malicious scripts.
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Phishing attacks. Imperva. Application and data security.
- ^ Thomas Holt. What Are Software Vulnerabilities, and Why Are There So Many of Them?. Scientific American. Science magazine.
- ^ Freeware. Wikipedia. The free encyclopedia.
