First ransomware / virus (Tech Support Scam)
First virus Removal Guide
What is First ransomware virus?
First ransomware — a new version of Hidden Tear
First virus is a crypto-ransomware [1] infection derived from an open-source program known as Hidden Tear. This virus is not the only example of an educational-purpose program gone wrong. We have seen a similar situation with EDU2 [2] as well. After receiving some critique from the security community, Hidden Tear creator Utku Sen has taken this program down, but the hackers continue using its leaked code for their malicious inventions. In our previous articles, we have already talked about such malicious Hidden Tear spin-offs as FSociety and today, we would like to discuss FirstRansomware virus as one of the latest ransomware using this code. By analyzing the newest ransomware variants, we can have a better idea of how these programs develop and what can possibly be expected in the future. If you do not wish to wait a minute longer, you can skip the analysis and head straight to the First removal. Just remember, that you should only use automatic scanners for the removal. We recommend trusting FortectIntego for the task.
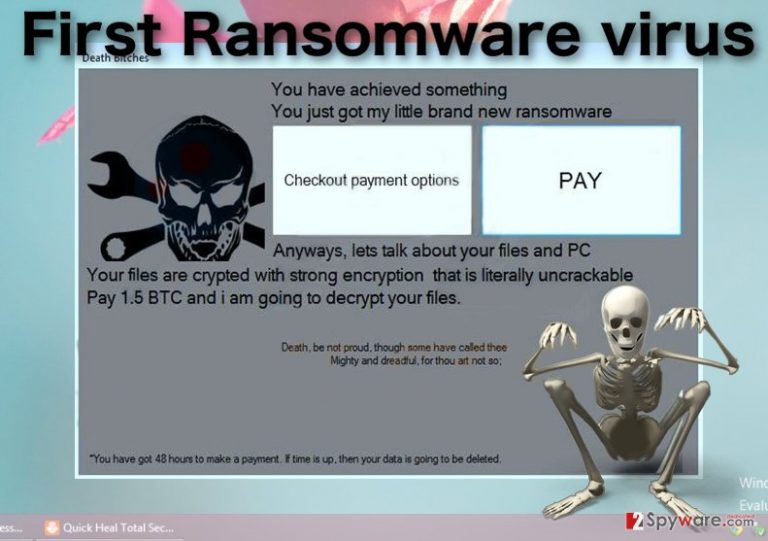
Technically, like most ransomware, the First virus encrypts files using an algorithm that replaces contents of the infected files with a sophisticated code [3] which can only be decoded with the help of a special decryption key. Such files become virtually unreadable and stand out from the non-infected ones with untypical extensions .krzysiok (or .locked) which are appended to the end of the filename. The encryption process itself may last from a couple of hours to several days, depending on how much data there is to encrypt and the time the computer in on standby. Finally, when the files are all encrypted, and the appended with specific extensions the virus drops a skeleton-themed ransom note:
Death B*tches
You have achieved something
You just got my little brand new ransomware
Anyways, lets talk about your files and PC
Your files are crypted with strong encryption that is literally uncrackable
Pay 1.5 BTC, and i am going to decrypt your files.
Death, be not proud, though some have called thee
Mighty and dreadful, for thou art not so;
*You have got 48 hours to make a payment. If time is up, then your data is going to be deleted.
The file of this pop-up note is deployed on every folder of the infected computer so that there is no way for the victim to bypass it without noticing. In the note, the extortionists explain what the victim has to do in order to fix the hijacked device and give 48 hours to meet the set terms. In particular, they try to persuade them into paying the 1.5 Bitcoin ransom which, looking at the current Bitcoin value, is a relatively large sum. Though such scare tactics [4] may be very convincing, we do not advise paying it. On the opposite, you should avoid any collaboration with the cyber criminals at all costs and remove First without second-thinking it.
How to protect your device against this ransomware?
Though there is no guaranteed way to secure your device against First ransomware attack, there is a way to protect your data. In other words, you have to make backup copies of your important files [5]. Today, there is a variety of backup software on the market. The storage of the backups is not a problem either since there are devices that can hold 1 TB or even more information in one spot. Copies of your files can be saved on thumb drives, external HDDs, etc. We do not recommend limiting yourself to a single storage option. Besides, data transfer to an external storage should only be carried on on a completely clean computer. Same goes for the data recovery. You can roll back your files from backup when you are entirely sure First ransomware is gone from your computer.
Remove First ransomware with professional antivirus tools:
First of all, we should say that we highly recommend you to remove First virus from the computer using automatic tools not only for the first-timers but also for the more advanced users as well. There are several reasons for this. Automatic First removal is less risky and ensures that all of the virus files are detected and eliminated from the device successfully. Besides, ransomware is often destructive and designed to mess up the computer system when the victim attempts their removal. But professional antivirus software does not fall into such traps and eliminates the virus without causing additional havoc on the computer.
Getting rid of First virus. Follow these steps
Manual removal using Safe Mode
First ransomware may interfere with your antivirus blocking it from scanning your device properly. To unblock your security scanners, follow the instructions below.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove First using System Restore
To unblock the antivirus scanner First ransomware virus may be preventing from cleaning up your system, check out these guidelines:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of First. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove First from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by First, you can use several methods to restore them:
Save your precious files with Data Recovery Pro
One of the first remedies that might help recover your system after the ransomware attack is Data Recovery Pro. You can learn how to use this tool in the instructions below:
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by First ransomware;
- Restore them.
Secure your computer with Windows Previous Versions feature
Even if the Windows Previous Versions feature does not help you recover your files in the case of this particular ransomware attack, you should known that you can use for emergency situations in the future. All you have to do it enable the System Restore function on your Windows. If you have already done that before First ransomware infection, the steps indicated below should help you recover your files.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Try data recovery with ShadowExplorer
ShadowExplorer technique is not always useful, especially if the virus deleted Volume Shadow Copies of the files. Nevertheless, it is always worth giving it a try. Either way, you have nothing else to lose.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from First and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Crypto Ransomware. U.S. Department of Homeland Security Seal. United States Computer Emergency Readiness Team US-CERT.
- ^ Hidden Tear Project: Forbidden Fruit Is the Sweetest. Tripwire. THE STATE OF SECURITY News. Trends. Insights..
- ^ Asymmetric cryptography (public key cryptography). Techtarget security news website.
- ^ Ransomware: 10 Years of Bullying, Fear-mongering and Extortion. Trend Micro antivirus blog.
- ^ Why do I need backup and what options do I have for that?. 2-spyware malware news site.







