Fullpcchain.com ads (scam) - Free Guide
Fullpcchain.com ads Removal Guide
What is Fullpcchain.com ads?
Fullpcchain.com shows fake virus infection pop-ups to mislead users
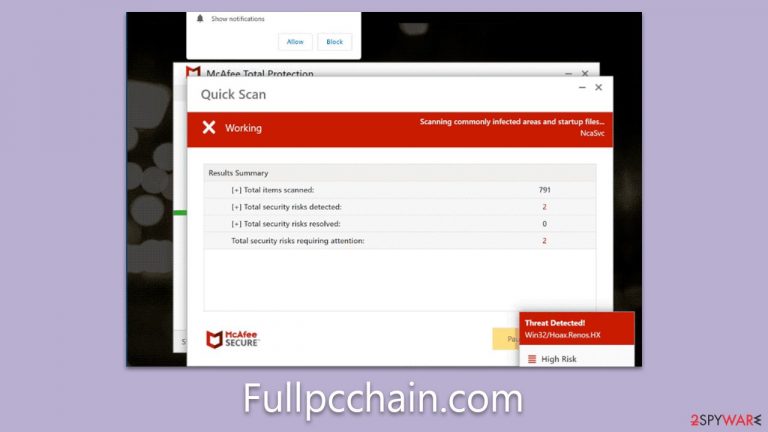
Fullpcchain.com is a notorious scam website that uses fraudulent tactics to mislead users into believing their systems are infected with malware. Upon visiting the site, users are presented with an imitation message, ostensibly from the renowned cybersecurity software vendor McAfee. This misleading message falsely alerts users that their systems are compromised by viruses and malicious websites, creating a sense of urgency and concern.
However, this message is entirely fraudulent and has no connection with authentic McAfee products or its vendor. Fake notifications are a ploy employed by scammers to profit from ads and affiliate marketing through unethical means.
Notably, the website even prompts users to enable push notifications, which could result in the display of these counterfeit malware infection prompts at any given time. It is advisable to avoid interacting with Fullpcchain.com entirely, and it may be worth checking your system for adware. Staying vigilant and discerning can help protect your system from such malicious attempts.
| Name | Fullpcchain.com |
| Type | Scam, fraud, phishing, redirect |
| Infiltration | Adware, redirects from other websites, malicious links |
| Operation | Shows fake messages about virus infections, allegedly coming from legitimate security software, and claims that the license of anti-malware has expired and needs to be renewed in order to fix the issue |
| Dangers | Installation of PUPs or malware, sensitive information disclosure, financial losses |
| Removal | You should not interact with any links or ads shown on the scam page and shut it down immediately. Then, perform a full scan with SpyHunter 5Combo Cleaner security software as a precautionary measure |
| Other tips | Third parties can employ cookies to continue tracking your online activities, so we recommended clearing browser caches and other leftover PUP files with FortectIntego |
How you end up on malicious websites
There are many ways that users might find themselves on malicious websites. Often, it can occur when users click on links or otherwise interact with unscrupulous websites, which could be disguised in various forms.
Some of these deceptive platforms could be websites offering illegal software downloads or cracks, sites providing counterfeit copies of popular apps or games, or even fake streaming platforms. These websites might look appealing and legitimate to the untrained eye, offering free or discounted services, but in reality, they serve as a conduit for harmful activities.
One common trap is the offering of “cracked” versions of popular software, where users are lured by the prospect of bypassing payment. However, these often come packaged with malware or lead to scam sites like Fullpcchain.com. Similarly, fake streaming platforms may promise free access to popular movies or TV shows, but the reality is they often redirect users to malicious websites or prompt them to download harmful files or programs.
Another significant way users might end up accessing scam websites is through an adware infection. Adware, short for advertising-supported software, is a type of malicious software that automatically displays or downloads advertising material, such as banners or pop-ups, when a user is online. This often happens without the user's consent and can significantly disrupt the user's experience.
Adware infections can occur in several ways. It could be downloaded alongside free software, where the adware is bundled into the installation package, or it might be installed via a malicious email attachment. Once installed, the adware can hijack your web browser, redirecting you to unwanted sites like Fullpcchain.com or displaying annoying and potentially harmful pop-up ads.
Adware is not only intrusive but also poses a significant security risk. It can monitor your browsing habits, collect personal information, and even make system changes without your knowledge or consent. This is why it's essential to stay vigilant online, avoid suspicious websites, and regularly check for adware infections. Regular use of reliable antivirus software, such as SpyHunter 5Combo Cleaner or Malwarebytes, can help protect your system from such threats. Remember, if an offer seems too good to be true, it likely is.
How crooks use social engineering to trick users
Upon visiting the deceptive site, users are confronted with a simulated system scan. A misleading alert subsequently appears, falsely claiming that their computer is riddled with numerous viruses. This strategic misdirection cultivates a false sense of urgency and anxiety, insinuating that these fictitious viruses can compromise the safety of the user's system and potentially expose their sensitive information, such as personal credentials or financial details.
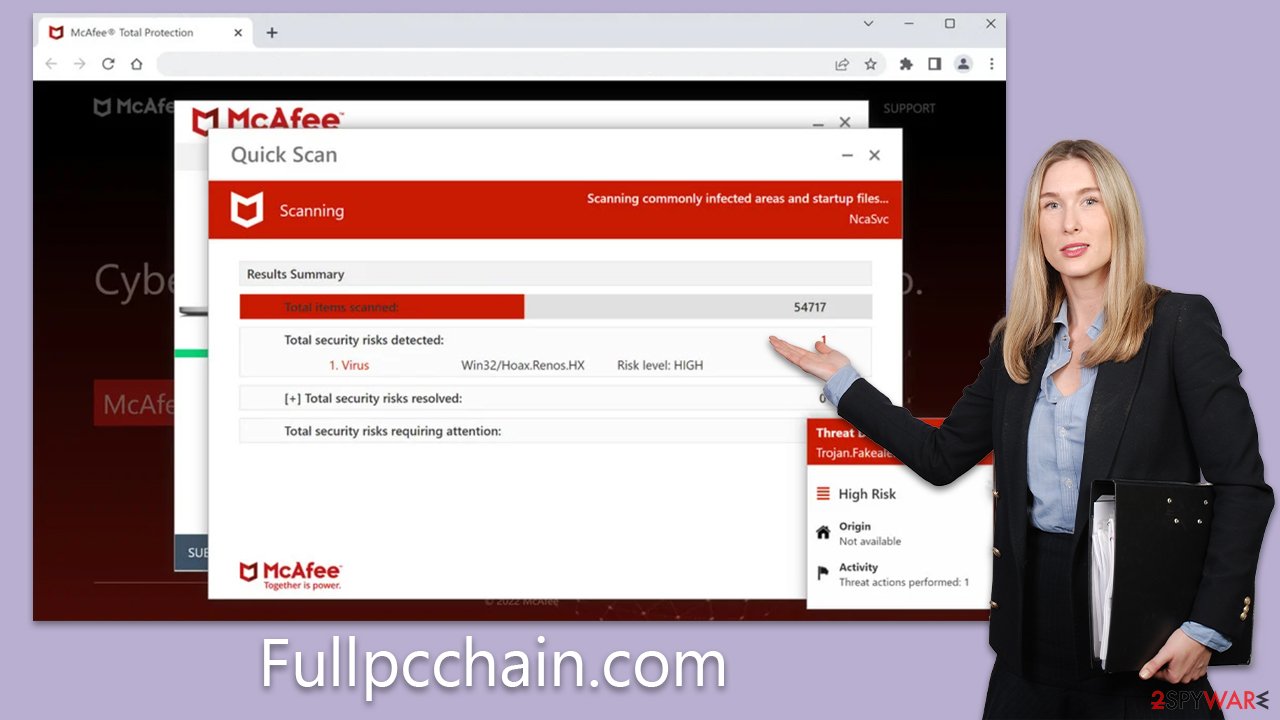
The site then persuades visitors to run a scan using McAfee Antivirus to eliminate the supposed threats. However, it's important to clarify that this site has no affiliation with the actual company. Instead, it's a creation of affiliates seeking to earn commissions from promoting and selling McAfee antivirus subscriptions via their unique links.
Scams like this, often dubbed “fake virus alert scams,” are masterful manipulators of human psychology. They exploit the fear and concern over personal cybersecurity to lure their victims. The scammers implement a variety of tactics, from fear-mongering to urgency creation, to ensure the victim feels compelled to act immediately.
Fear-mongering, as seen in the false virus detection alert, attempts to incite panic in users, making them more likely to follow through with the scammer's requests. In this case, users are led to believe their system security is at risk and that their sensitive information might be exposed. Here's an example of what you may see:
Your PC is infected with 5 viruses!
IMMEDIATE ACTION REQUIRED!
Your McAfee subscription has expired!
Renew now to keep your PC protected.
Viruses found on this PC most likely track internet activity to collect banking details and login credentials. Unprotected PCs are 93% more vulnerable to suffer from malware.
The creation of urgency is another common tactic. Users are misled into thinking that immediate action is necessary to prevent further damage or data loss. This sense of urgency prevents users from taking the time to verify the alert's authenticity, thereby falling into the trap set by the scammers.
Remediation steps to take
In order to recover from an encounter with a deceptive website like the fake virus alert, it is paramount to commence an adware scan as an immediate response. By leveraging reliable security software such as SpyHunter 5Combo Cleaner or Malwarebytes, you can conduct a comprehensive system assessment. These tools are designed to detect and eradicate any undesirable elements swiftly, thus restoring your system to an adware-free state.
Attempting to remove unwanted applications manually could become a tedious task, and it poses the risk of accidentally erasing beneficial programs. In contrast, automated removal offers an expedited and uncomplicated solution. As soon as you are confident that your device is purged of malware and adware, it becomes necessary to cleanse your browser's cookies and other trackers without delay.
You can either enlist the assistance of FortectIntego for this task, or you can choose to undertake it yourself by adhering to the guidelines we'll provide subsequently. This two-step process not only safeguards your device but also ensures your online browsing experience remains free from invasive tracking.
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Likewise, if you have intentionally or by accident enabled push notifications from Fullpcchain.com, you can follow the instructions below to get rid of them. Please do not interact with them in any way, as these pop-ups operate in a similar manner as the scam site itself.
Getting rid of Fullpcchain.com ads. Follow these steps
Stop browser notifications
Remove unwanted notifications from Google Chrome (desktop):
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate Privacy and security section and pick Site Settings > Notifications.

- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Remove unwanted notifications from Google Chrome (Android):
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).

Remove unwanted notifications from Mozilla Firefox:
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.

- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

Remove unwanted notifications from Safari:
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

Remove unwanted notifications from MS Edge:
- Open Microsoft Edge, and click the Settings and more button (three horizontal dots) at the top-right of the window.
- Select Settings and then go to Advanced.
- Under Website permissions, pick Manage permissions and select the URL in question.

- Toggle the switch to the left to turn notifications off on Microsoft Edge.

Remove unwanted notifications from MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Remove unwanted notifications from Internet Explorer:
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
- Locate web address in question under Allowed sites and pick Remove.

How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
