GVU virus - 2021 update
GVU virus Removal Guide
What is GVU virus?
GVU virus is a screenlocker virus that asks for payments from German-speaking victims mainly
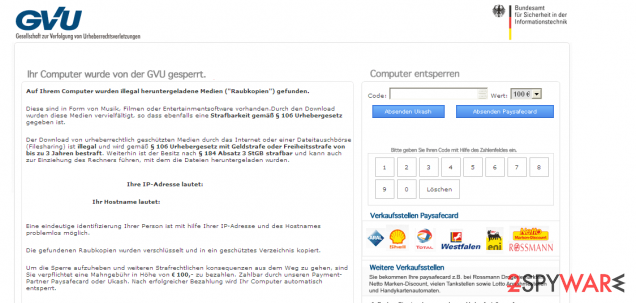
GVU virus also called Gesellschaft zur Verfolgung von Urheberrechtsverletzungen virus is a malicious ransomware infection that seeks to get 100 euros from each of its victims. For that, it firstly blames the user for the copyright law violations and locks his computer's system down.
You should have already heard about other Ukash viruses that are designed to mislead Germain-speaking PC users – such programs as Bundesamt für Polizei virus, Der Computer ist für die Verletzung der Gesetze der Republik Österreich blockiert worden or Polizei österreich virus are well-known threats in the industry of malicious ransomware infections.
Typically, GVU virus claims that the user has been visiting websites filled with violence or pornographic content:
Die Funktion ihres Computers wurde aufgrund unerlaubter Internethandlungen außer Kraft gesetzt. im Folgenden werden mögliche Verstöße aufgelistet, die von ihnen begangen werden konnten: Artikel 274- Urheberrechte Eine Ge dstrafe oder Freiheitsstrafe von bis zu 4 Jahren. (Die Benutzung oder Verbreitung von Daten, die urheberrechtich geschützt sind – Ei me, Software( Artikel 263- Pornografie Eine Ge dstrafe oder Freiheitsstrafe von bis zu 2 Jahren. (Die Benutzung oder Verbreitung von pornografischen Daten) Artikel 184 – Kinderpornografie (bis 28 Jahre) Eine Fre-heitsstrafe von b-s zu 15 Jahren (Die Benutzung oder Verbreitung von pornografischen Daten' Artikel 104- Terrorismusförderung Eine Fre-heitsstrafe von b-s zu 25 Jahren (Sie haben Seiten von Terrororganisationen besucht: Artikel 297- Fahrlässige Computernutzung mit schwerwiegenden Konsequenzen Eine Geldstrafe oder Freiheitsstrafe von bis zu 2 Jahren (ihr Computer ist von e-nem Virus infiziert welcher bereits andere Computer infiziert hat) Artikel 108 – Glücksspiel Eine Geldstrafe oder Freiheitsstrafe von bis zu 2 Jahren. (Sie nahmen am Glücksspiel teil, jedoch ist dies entsprechend der Gesetzgebung ihres Landes verboten) in Bezug auf den Regierungsentscheid vom 22 August können alle verstöße bei einer Geldbuße als bedingt angesehen werden. Die Summe der Geldbuße beträgt ic0 Euro. Die Bezahlung muss innerhalb von 48 Stunden nach Kundgabe des verstoßes entrichtet werden. wenn die strafe nicht entrichtet wird, wird automatisch ein Strafverfahren gegen Sie eingeleitet.
Then the screen locking scares victims even more. However, you should never believe this alert or any other claims of cybercriminals and remove Gesellschaft zur Verfolgung von Urheberrechtsverletzungen virus. Follow this post to get all the details on how you can do that.
These threats that fall into the ransomware category all pretend to belong to governmental organizations and use the translated notifications that look like legitimate ones. Be sure that Gesellschaft zur Verfolgung von Urheberrechtsverletzungen virus is nothing else but a malicious application that needs to be eliminated.
However, in order to remove Gesellschaft zur Verfolgung von Urheberrechtsverletzungen virus or GVU virus, you will have to unlock your PC first. This is not the easiest thing, but there are tools and security programs or PC repair apps like FortectIntego that can help you with some of the removal steps.

Spreading methods of such money-demanding threats
The most obvious sign you are infected with GVU virus is a disabled computer's screen, which gets locked by a misleading message written in Germain. Typically, Ukash viruses are spread by trojan horse, which comes inside the system through its backdoors after the user forgets to update his security software.
Note that you can easily download this threat when downloading infected downloads, such as freeware, opening infected email attachments, or using P2P networks. As soon as it gets inside the PC, the machine becomes locked, and it seems that there’s nothing you can do except paying 100 euros to unlock your PC screen.
Gesellschaft zur Verfolgung von Urheberrechtsverletzungen virus claims that country's local police has detected your computer via its IP address and now you are locked because of illegal activities on your computer.
Ways to remove GVU ransomware virus
When trying to remove GVU virus, you may find that you are blocked from getting on the Internet. As you know, this is the only way to download the anti-malware program, so you will have to unlock your PC first if you are blocked by this virus. However, if you can get online, we recommend downloading SpyHunter 5Combo Cleaner and running a full system scan with it. If you can't, follow these tips:
1. Take another machine and use it to download Malwarebytes or another reputable anti-malware program.
2. Update the program and put into the USB drive or simple CD.
3. In the meanwhile, reboot your infected machine to Safe Mode with a command prompt and stick a USB drive in it.
4. Reboot computer infected with Ukash virus once more and run a full system scan.
Users infected with Ukash viruses are allowed to access other accounts on their Windows systems. If one of such accounts has administrator rights, you should be capable to launch an anti-malware program. You should also try to reboot the machine and run a full system scan with updated FortectIntego to remove remaining virus files or corrupted data, virus damage, altered data in system folders that GVU virus might have left installed. You can find in-depth instructions below.
Getting rid of GVU virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove GVU using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of GVU. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove GVU from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by GVU, you can use several methods to restore them:
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from GVU and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.







