Hacking ransomware / virus (Removal Guide) - Nov 2017 update
Hacking virus Removal Guide
What is Hacking ransomware virus?
Hacking ransomware: another version of HiddenTear targets French computer users
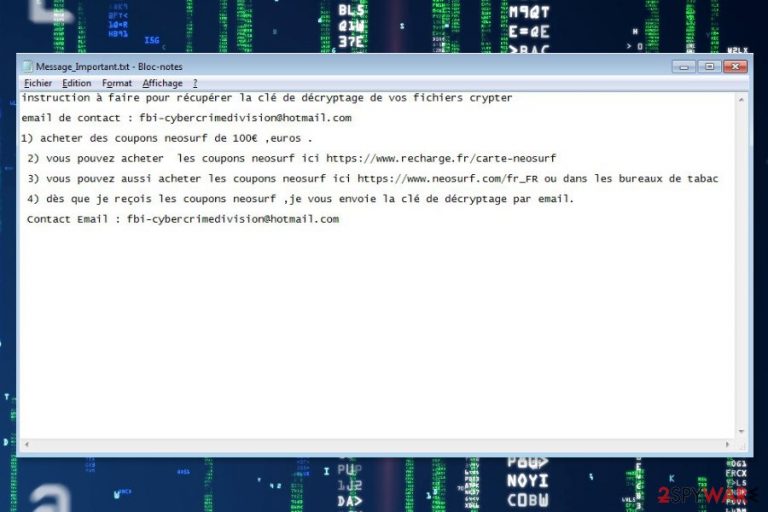
Hacking ransomware possesses similar features as any other crypto-malware — encrypts valuable information on the victimized computer and demands to pay a ransom in return to recover the data. In fact, this virus is classified as an offspring of the infamous HiddenTear since its source code is used to develop the latter infection[1]. IT experts have analyzed a sample of the file-encrypting virus and detected that it adds .hacking file extension to the corrupted data and drops a Message_Important.txt ransom note.
According to the latest reports, Hacking virus spreads as a .zip file which supposedly contains 6 pictures with an adult content. Typically, victims are offered to download pornographic images on various suspicious adult-only websites and the executable file of the malware is named as video.exe to trick gullible people into opening it.
Once they double-click on the .exe file, the Hacking ransomware infiltrates on the system and starts data encryption. Furthermore, it provides instructions on how to recover the compromised data in French[2]. Victims are asked to send Neosurf coupons for 100 euros and contact cybercriminals via fbi-cybercrimedivision@hotmail.com. Hackers promise to respond with the decryption key soon.
The translated text from the ransom note:
To recover encrypted files, you have to obtain the decryption key and send an email to: fbi-cybercrimedivision@hotmail.com
1) Buy Neosurf coupons of 100 €, euros.
2) You can buy Neosurf coupons here https://www.recharge.fr/neosurf-card
3) You can also buy Neosurf coupons here https://www.neosurf.com/en_US or at tobacconists
4) As soon as I receive the Neosurf coupons, I send you the decryption key by email.
Contact Email: fbi-cybercrimedivision@hotmail.com
Security experts do not recommend paying the ransom. Criminals may not have the working decryption key, or they might blackmail you into transferring more money. Besides, the Hacking malware is based on HiddenTear which is a decryptable virus. Thus, files encrypted by this virus might be recovered too. You can check the official decryptor which is attached at the end of this article.
After ransomware attack, you should focus on Hacking removal. The cyber threat is capable of modifying Windows Registry, installing malicious components and affecting legit processes. For this reason, your computer is no longer safe to use. In addition, you might suffer from system slowdowns and other computer-related problems.
To remove Hacking ransomware virus entirely, you have to reboot the computer to the Safe Mode with Networking and run a full system scan with malware removal software. We recommend using FortectIntego. However, you can choose any other preferred tool as well.
Distribution methods employed to spread the file-encrypting virus
As mentioned above, the latest research found out that the ransomware spreads as a deceptive .zip with pornographic images. However, note that the hackers employ many techniques to distribute the infection. Thus, cybersecurity experts warn about other possible ways to get infected with ransomware:
- malicious ads placed on legit and high-risk websites;
- Remote Desktop Protocol (RDP) brute force attacks;
- exploitation of software or system vulnerabilities;
- bogus software downloads;
- fake update downloads;
- illegal downloads.
Additionally, you should stay away from malicious spam emails, since many criminals choose is as the primary ransomware distribution strategy[3]. Also, users are reminded to be careful and avoid clicking, opening or downloading questionable content. Installing reputable antivirus also helps to reduce chances to catch a cyber infection. However, you should be prepared for the worst and backup your files as well as to update them regularly!
Learn how to terminate Hacking ransomware
Be aware that ransomware is the most harmful type of the virus. It can not only corrupt your data, but infiltrate additional high-risk computer infections to increase the damage as well. In this case, Hacking removal can be performed either by certified IT technicians or by a professional security software.
We recommend you to save your time and choose to use FortectIntego, SpyHunter 5Combo Cleaner or SpyHunter 5Combo Cleaner. These anti-malware programs are designed to safely remove Hacking virus from the system and protect your computer from the future threats. It is a wise decision to opt for automatic elimination since it is not a one-time investment — security software will serve you for years.
Note that manual ransomware removal is not an option, because it may have injected malicious components to legit system processes. To terminate them manually is a hard and complicated task that might end up bad for the inexperienced computer users. Thus, it’s highly recommended to invest in legit antivirus tool and clean the device with it.
Getting rid of Hacking virus. Follow these steps
Manual removal using Safe Mode
You can disable Hacking ransomware and successfully install a security software by carefully following the guide below:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Hacking using System Restore
In some cases, the ransomware might still block the installation of the antivirus system. Thus, you can use the additional method to reboot your PC to Safe Mode with Command Prompt function.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Hacking. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Hacking from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.While paying the ransom to the criminals is not the smartest and safest option to retrieve your data, you can check whether the automatic function to store backups was enabled on your computer before ransomware attack. If you are lucky, you can try to recover your files using them.
However, for those who do not have backup copies, our team has prepared useful instructions on how to employ alternative recovery tools to restore the corrupted data.
If your files are encrypted by Hacking, you can use several methods to restore them:
Try Data Recovery Pro
This is a professional tool designed to help ransomware victims. If you aim to recover files with .hacking extension, follow the instructions below:
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Hacking ransomware;
- Restore them.
Windows Previous Versions feature might help to retrieve the most important files
Before proceeding to the guide below, check whether the System Restore function was enabled before Hacking entered your PC. If it was disabled, then head to the next alternative recovery method. Otherwise, follow the steps below:
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
You can benefit from ShadowExplorer tool
Luckily, there is no reliable information that Hacking ransomware deletes Shadow Volume Copies from the victimized systems. Thus, you are free to use the instructions below:
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
HiddenTear official decryptor can be helpful
While the Hacking ransomware uses HiddenTear source code, it might be also decryptable:
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Hacking and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Dan Turkel. Cyber security researcher created a dangerous virus for experiment — and then chaos broke loose. Business Insider. Business site with deep financial, media, tech, and other industry verticals.
- ^ Les Virus. Les Virus. Cyber security news and malware database.
- ^ Maria Korolov. 93% of phishing emails are now ransomware. CSO Online. Security news.







