Ranion ransomware / virus (Removal Guide) - updated Mar 2018
Ranion virus Removal Guide
What is Ranion ransomware virus?
Ranion is a file-encrypting virus that uses a sophisticated encryption algorithm
Ranion is a HiddenTear-based ransomware virus that also operates as a Ransomware-as-a-Service. The virus was updated two times already. On September 2017, developers of malware introduced 1.06 version of the malware. One month later, v.1.07 variant was released. The newest version 1.08 shown up in February 2018.
Ranion malware uses a strong encryption algorithm and appends .ransom file extension to the targeted files. Following the successful data encryption, malware delivers a ransom note where criminals demand to pay the ransom in order to get back access to the locked files.
The significant feature of the Ranion ransomware is that it also works as ransomware-as-a-service (RaaS). Though the ransom message of the original virus warns users not to use the malware other than educational purposes[1], now it is clear that it is only a lie. The virus is promoted as the “Better & Cheapest FUD Ransomware.”
The news broke out about the Ranion virus when a security specialist Daniel Smith found the malware in a dark web. At the beginning of its emergence, the yearly access to the malware source code costs 0,95 BTC (approximately $1000). Additionally, buyers get the decrypter, anonymous C&C dashboard that can be accessed via Onion. What is more, hackers offer free customizations as well.
Update February 2018. The latest version of Ranion was detected at the February 2018. Malware is executed on the system from the custom-2017.exe file and immediately starts encryption procedure. It appends the same .ransom extension to the files. Following the encryption, Ranion 1.08 ransomware delivers a ransom note which is available in 8 languages, such as Spanish, Persian, Russian, Italian, Dutch and German.
In the ransom note, crooks ask to pay 999 USD in Bitcoins in 7 days. After making the payment, victims have to send their unique ID number, which is provided in the note, to 0dayservices0@gmail.com email address. Authors of Ranion malware promises to respond with the decryption key. However, following these guidelines is not recommended due to the possible money loss.
Update November 2017. Security experts discovered a new version of the Ranion ransomware. Malware is executed on the system from the ransom-cleaned.exe file. Just like the previous version, it also appends .ransom extension to each of the targeted files. Malware uses AES-256 encryption to lock the files. As a result, users are unable to open and use them.
However, cybercriminals offer a shady way to restore data. Following data encryption, the Ranion v1.07 ransomware creates the README_TO_DECRYPT_FILES.html file where crooks demand to pay 0.3 Bitcoins in 7 days. After the deadline, the decryption key is said to be deleted. Additionally, victims are also asked to send their ID number via theaccountant@Safe-mail.net email as soon as they transfer the money.
Paying the ransom is not recommended because it may lead to money loss. Crooks might ask for more money and never decrypt your files. Therefore, after the attack, its’ advised to obtain a security software and remove Ranion immediately.
Update September 12th, 2017. It seems that the break since its appearance on the web was not wasted. The developers have struck again with a new Ranion 1.06 ransomware version, which leaves .ransom extension at the end of the encoded data. It seems that it may come with a counterfeited Minecraft game as it executes via MineCraft Hack + Setup TuT.exe[2] file.
It may come as Trojan.RansomKD.DBAD6A3, Win32.Trojan.WisdomEyes.16070401.9500.9979, or Backdoor.Ratenjay. Considering the latter, it is necessary to eradicate the infection as soon as possible since it manifests capabilities to function as backdoor, i.e. grant remote access to the device.
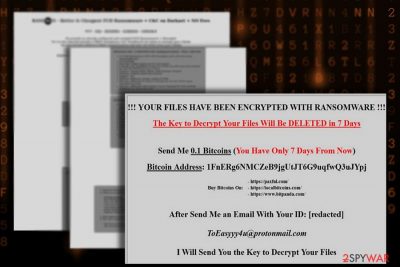
The current version displays README_TO_DECRYPT_FILES.html file on a Desktop with further instructions of data recovery. the latest version demands 0.1 BTC, i.e. approximately $431 in exchange for the files.[3] The perpetrator urges a victim to remit the payment within 7 days and contact them via ToEasyyy4u@protonmail.com. Despite the claims to retrieve the files, it is not recommended to pay the ransom but instead ,remove Ranion 1.06 malware.
Modus operandi of the Ranion ransomware virus
The malware, which contains the allusion to the characters Sprites from the animated film “Spirited Away,” claims to be the cheapest ransomware-as-a-service. Any user, who is willing to take the risk and enter the business, is granted the payload file. Afterward, he will receive the instructions how to access his Command and Control server. Now the malware targets a relatively small number of file formats.
.txt, .rtf, .doc, .docx, .xls, .xlsx, .ppt, .pptx, .odt, .ods, .jpg, .jpeg, .png, .bmp, .csv, .sql, .mdb, .db, .accdb, .sln, .php, .jsp, .asp, .aspx, .html, .htm, .xml, .psd, .cs, .java, .cpp, .cc, .cxx, .zip, .pst, .ost, .pab, .oab, .msg
Nonetheless, the cyber villains are planning to expand the list. Interestingly, that the penetrators also offer the utility of encrypting .exe files. Ranion ransomware is able to encode files on all disks. It is promoted as the virus which is not detectable by the majority of anti-virus applications[4].
However, since the virus has been published on the dark market and now security companies may forward the emergency updates to prevent the damage.
Furthermore, the infection does not differ much from other threats: it employs AES-256 algorithm[5]. Previous cases revealed that the cipher creates great obstacles for decryptors. The dashboard of Ranion malware disclosed information about users identification codes, usernames, and each unique AES decryption software. However, getting infected with ransomware is not a deadly verdict.
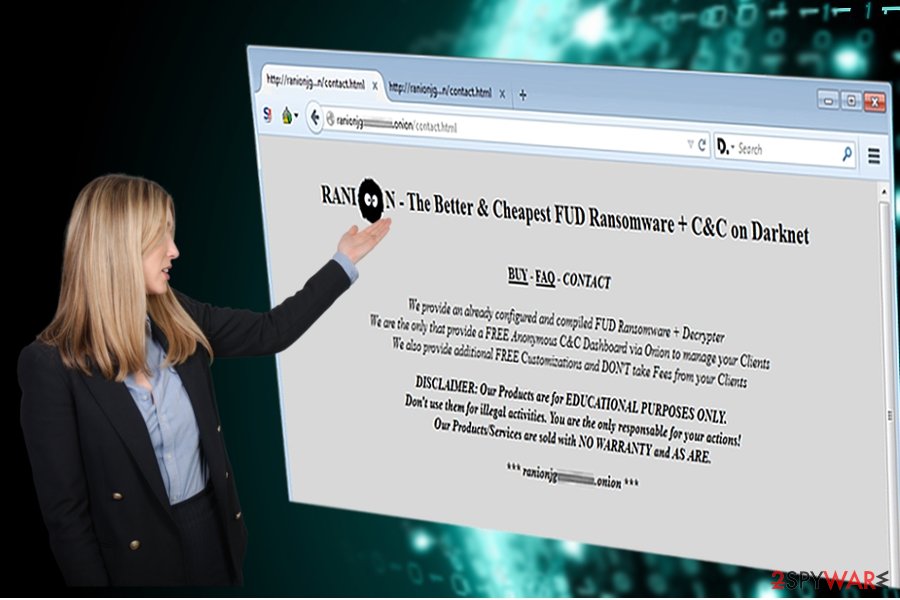
Interestingly, the bidders do not need to share their profits with the authors of this Ranion RaaS in contrast to previous cases when the developers demand ¼ of the profits. It is likely that some of the cyber hackers have already purchased the rights to the malware and spread the infection. If you happen to be infected, remove Ranion right away. You can do it with malware removal utility or look up alternative methods below the article.
Ransomware payload spreads in obfuscated email attachments
Such category of threats is transmitted via spam emails[6]. Despite continuous alerts, the virtual community still falls for the trap opening counterfeited invoice, custom declaration forms, delivery emails. However, it is not difficult to prevent ransomware spreading in such case. Usually, such emails contain evident grammar and style mistakes.
Full credentials are missing, or the copied logos have altered elements. Additionally, Ranion hijack may occur due to visiting an infected domain which possesses exploit kits. Recently, EITest scripts have been gaining popularity in delivering exploit kits.
When a user visits a web page infected with them, the hijack by the ransomware becomes a matter of time. The exploit kits function on behalf of system vulnerabilities, so it is of utmost importance to update software regularly.
Delete Ranion virus from the Windows computer
Luckily, this cyber menace has not yet spread throughout the entire cyber space, but there are chances that it might have reached some users. If you happen to be one of the unlucky ones, start the automatic Ranion removal. For that purpose, FortectIntego or Malwarebytes serves as a proper elimination tool.
Since the penetrators may customize the threat according to their own liking, it is likely that the modified version might paralyze a computer. If you cannot control it, follow below-indicated instructions. Only when you successfully remove Ranion virus[7], you may consider initiating data decryption procedure.
Getting rid of Ranion virus. Follow these steps
Manual removal using Safe Mode
If the PC screen is locked or other vital functions stopped working, enter Safe Mode and follow the instructions.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Ranion using System Restore
If the above-suggested method does not help, perform System Recovery.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Ranion. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Ranion from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Ranion, you can use several methods to restore them:
Data Recovery Pro
This program is specifically designed for locating damaged or lost files. It may also help you recover some of the encoded files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Ranion ransomware;
- Restore them.
Opting for Shadow Explorer
The key advantage of the program is that it recreates the files according to the patterns called shadow volume copies. They are created by the operating system. Luckily, few viruses are known to delete them. In short, you might stand a chance.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
The official Ranion decryptor is not available yet
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Ranion and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Karsten Hahn and Tilman Frosch. It's Educational - On the No 1 Argument for Open Source Ransomware. G Data Security Blog.
- ^ MineCraft Hack + Setup TuT.exe. VirusTotal. Free malevolent URL analysis service.
- ^ MalwareHunterTeam. So, it is Hidden Tear based. Note name (main): README_TO_DECRYPT_FILES.html Others: 2nd screenshot shows all names. Extension: .ransom. Twitter. Online source for communication and news.
- ^ Paul Rubens. How to Stop Ransomware. eSecurity Planet. Inteente Security for IT Professionals.
- ^ How does the encryption algorithm Rijndael (also called AES) work?. Password Depot. All about encryption.
- ^ JP Buntinx. New Spam Campaign Distributes Locky Ransomware and Kovter Trojan Simultaneously. The Merkle. IT News and Reviews.
- ^ Cat Ellis. How to block or remove ransomware. TechRadar. The source for tech buying advice .





















