Hacktool:win32/keygen (Virus Removal Guide) - updated Oct 2020
Hacktool:win32/keygen Removal Guide
What is Hacktool:win32/keygen?
Hacktool:win32/keygen is a generic detection name that points to the pirated software for cracking software licenses
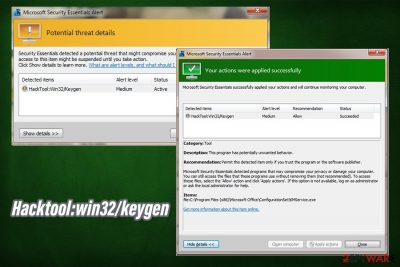
Hacktool:win32/keygen is a representation of a cracking tool, which is often detected by anti-malware applications. While not all the cracks are malicious, they are often boobytrapped or distributed with a variety of malware, such as Remote Access Trojans, ransomware, crypto miners, backdoors, worms, etc. In most cases, users download this Hacktool intentionally when trying to bypass restrictions of application trials, or simply use an otherwise paid program for free.
In case Hacktool win32 keygen is programmed to infect the machine with malware, it can result in serious consequences, although these depend on the infection type. For example, ransomware could result in permanent personal file loss, while a stealthy backdoor can proliferate more malware and gather sensitive information (such as banking credentials, log in details, etc.) in the background, without emitting any symptoms. If you have recently download the tool, you should hurry up and remove Hacktool:win32/keygen as soon as possible – we explain how in this article below.
| Name | Hacktool:win32/keygen |
| Type | Malware, Trojan |
| Distribution | Hack tools and keygens are acquired from insecure third-party websites that host pirated software (torrents, warez) |
| Related | KMSpico, AutoKMS |
| Symptoms | Symptoms vary greatly, as malware behind crack tools can be different; symptoms range from total lockdown of personal files, high CPU usage, system crashes, to no visible signs of intrusion |
| Dangers | Further infection of malware, loss of personal files, sensitive information disclosure to cybercriminals, high electricity bills, etc. |
| Removal | To get rid of malware behind Hacktool:win32/keygen, users should immediately scan their machines with reputable anti-virus, such as SpyHunter 5Combo Cleaner or Malwarebytes. In case the virus is tampering with security software, Safe Mode with Networking can be used – check the bottom section for more details |
| System fix | In some cases, malware can permanently damage Windows systems and render them useless. To fix all the damage done by the virus an remediate the system, use repair tools like FortectIntego |
It is a very rare occasion when users spot a Hacktool:win32/keygen pop-up of their anti-malware tool while being unaware of its presence. In other words, users download keygens deliberately to avoid licensing fees or other restrictions. Thus, users typically get infected with keygen virus after they visit insecure sites that host pirated programs and software cracks, such as torrent websites.
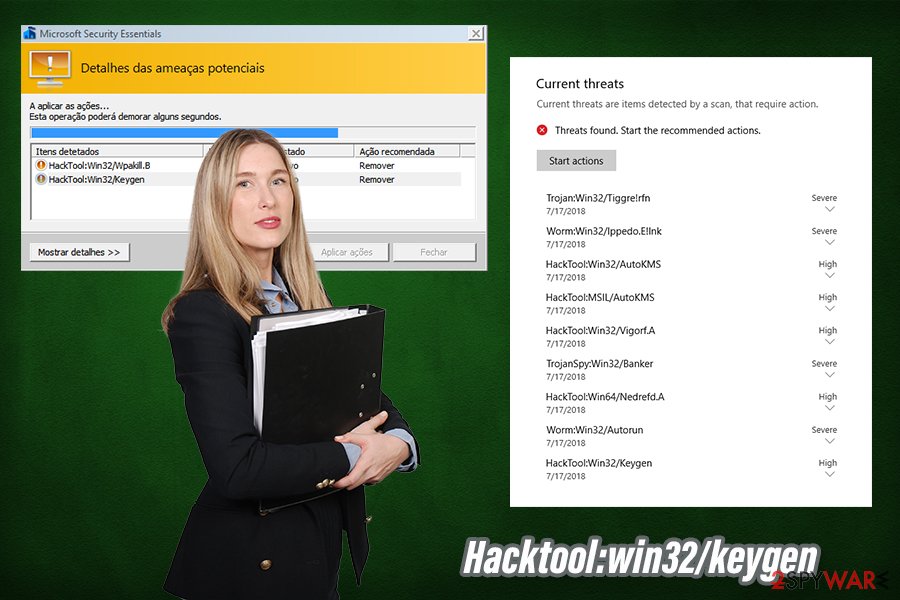
Possibly the most used cracks are AutoKMS (hacktool:win32/autokms) and KMSpico (used to bypass the licensing process of MS Office suite, as well as Windows OS) – these can most commonly be detected as Hacktool:win32/keygen.
Since Hacktool:win32/keygen is a heuristic detection name, it can represent a variety of different files, each having different functionality. For example, some hack tools are simply applied as executable files, while others generate keys that can be inserted directly into an application or a video game. Besides the tool's functionality, malware that can be related to win32/keygen can vary greatly, and so will the symptoms of the infection.
While Hacktool:win32/keygen malware can be classified as a Trojan (users believe they install a hack tool, but instead they infect computers), the functionality of each particular infection and ramifications of such can vary greatly. Here are a few examples of possible keygen virus executed on your PC:
- Ransomware. Possibly the most devastating malware – it encrypts all personal files on the system, and only the attackers can return the access to it. Typically, hackers ask for ransoms raging anything between $100 to $1,000 in Bitcoin per PC, with payments rising to thousands of dollars for corporations. One of the best examples that are being distributed via cracks is Djvu ransomware – one of the most widely-spread crypto-malware in the wild.
- RATs (Remote Access Trojans). These parasites can allow malicious actors to control the machine remotely, execute malicious commands, and even lockout users from their computers.
- Rootkits gain one of the highest levels of permissions on the system, and typically are very difficult to eliminate (if not impossible, in some cases).
- Cryptominers use around 90% or more CPU (sometimes GPU as well) to mine digital currency to cybercriminals' wallets, while users suffer from errors, crashes, and increased electricity bills.
- Banking trojans enable the attacks to perform web injects and other tactics to steal financial and other sensitive information from users' machines.
- Keyloggers can log all the information typed on a keyboard and utilize it for malicious purposes.
As evident, threats that could be installed via Hacktool:win32/keygen can be extremely devastating to every user, and can also result in further computer compromise. To make matters worse, most of the info-stealing malware is programmed to remain on the system unnoticed for long periods of time[1] – this is another reason to ensure that a powerful anti-malware is employed at all times.
As for Hacktool win32 keygen removal, you should always employ reputable anti-malware software for the job. While manual termination is possible, it is a complete opposite for regular computer users, and an automatic option should always be chosen. Thus, download powerful anti-malware and perform a full system scan. In case this process fails, you can access Safe Mode with Networking and perform a scan from there, although most modern AVs should be able to remove Hacktool:win32/keygen virus easily.
Additionally, once malware infects your machine, it might not run at its full capacity anymore, even after it is terminated. Therefore, if you are experiencing any issues post-termination of Hacktool win32 keygen, you can employ FortectIntego to repair virus damage with ease.
Here is why you should not be downloading software cracks and hack tools
First of all, we should talk about intellectual property. Application and video game developers all put a lot of effort to deliver results, and each need to be paid a salary. By downloading software cracks, users simply strip creators of their earned money, which can be devastating to some companies or entities.
If morality is not an issue, you should keep in mind that pirating software is illegal and punishable by law. Copyright laws were not immediately implemented, although even now, torrent and other illegal software distribution sites still manage to bypass restrictions implemented to protect the intellectual property of others.
In the meantime, crack sites also became a hub for malware distribution,[2] as there are by far less regulated, even though site owners not necessarily want to infect users with malware. Ad space can be bought by hackers, which allows the deployment of malicious ads. As a result, some users can get infected as soon as they access such a website – and this is another reason to stay away from pirated software and its distribution sources.
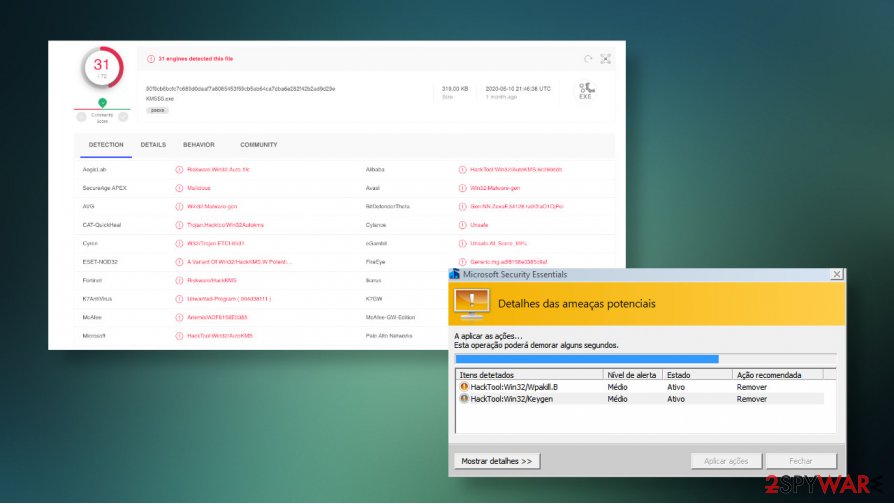
Finally, most of the anti-malware tools will flag cracks as malicious, regardless if they actually are. This is because hack tools are designed to break the code of an application, which is essentially malicious activity. Therefore, even if the installer is not boobytrapped with malware, there is no way to check, even by uploading it to analysis tools like Virus Total. Next time you click on a crack, remember that it can result in severe computer infection, such as ransomware.
Remove Hacktool:win32/keygen malware without a delay
Keep in mind that, while some malware installers might be named as software crack (for example, KMSSS.exe),[3] others can function as a crack, providing the promised functionality, all while executing code in the background and downloading malicious payload. As a result, you might not know that malware is running in the background and also might not realize that you need to remove Hacktool virus to protect your personal safety and privacy.
Since the malware embedded in cracks can vary greatly, Hacktool:win32/keygen removal can sometimes also be complicated. For example, the rootkit can be difficult to eliminate and need specific tools, while other malware might disable anti-virus tools altogether. If any difficulties arise, you can always access Safe Mode with Networking and perform a full system scan from there – instructions on how to reach it are listed below.
Getting rid of Hacktool:win32/keygen. Follow these steps
Manual removal using Safe Mode
In case you are having issues with Hacktool:win32/keygen removal, you should access Safe Mode with Networking and perform a full system scan with anti-malware from there:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Hacktool:win32/keygen and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Elizabeth Montalbano. Stealthy Malware Flies Under AV Radar with Advanced Obfuscation. Threat Post. The first stop for security news.
- ^ Filip Truta. Beware of New Wiper Malware Distributed through Free Software / Crack Sites. Hot for Security. Bitdefender's security blog.
- ^ KMSSS.exe. Virus Total. File and URL analysis.














