Happy Locker ransomware / virus (Tutorial)
Happy Locker virus Removal Guide
What is Happy Locker ransomware virus?
Happy Locker virus does not bring happiness
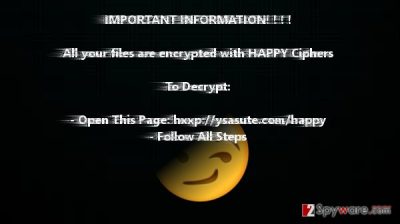
If you see the black screen with the message that your data was encrypted with “happy,” it means that you became the victim of Happy Locker. This is another virus belonging to ransomware category. Despite it using AES encryption technique, the virus remains a difficult task for virus researchers. However, if you encountered this ransomware, it does not mean that it is time for distress. You can remove Happy Locker effectively with the help of FortectIntego. This tool deals with a variety of trojans, ransomware, and similar threats. After completing Happy Locker removal, you might be also interested in the alternative ways of decrypting the affected files.
“Locker“-named viruses have become a new wave. The virtual community has already seen similar threats: Wicked Locker HT, Wildfire Locker, etc. They all seem to be entitled in the fashion of original CryptoLocker virus – which still leaves a menacing awe for many hacker-wannabees. Obviously, some crooks clearly mock their victims and create supposedly amusing ransomware veneers and ransom notes. However, dealing with a file-encrypting malware is surely an unpleasant experience. The new virus – Happy Locker ransomware – is supposed to be another alternative of Hidden Tear 2.0 virus. It seems that its authors decided to revive the ransomware and generated its several new versions.
The current virus has gained such notoriously ordinary title as it appends .happy extension to all affected files. Unfortunately, the virus targets a broad range of files so the majority of your image, audio, video and .doc files might be already encrypted and bearing the mentioned extension. After the process is finished, the virus opens READDDDDDD.txt containing scarce instructions how to decrypt the files. certainly, they demand money in exchange for the decryption software. However, we would like to remind you once again that hackers have an awful peculiarity not to keep their word. In short, you may waste your money and the last drop of patience.
We would like you to warn not to purchase Happy Decryptor, the program which is supposed to decode your files. Do not forget that this program may only worsen the situation. There are no guarantees that after paying the money, the decryptor will decode the data. What is more, this application may leave malicious elements on the system which later facilitate the future Happy Locker hijack or another cyber infiltration.
Happy Decryptor™
We present a special software – Happy Decryptor™ –
which allows to decrypt and return control to all your encrypted files.
How to buy Happy Decryptor™?
You can make a payment with BitCoins, there are many methods to get them.
You should register BitCoin wallet:
Simplest online wallet or Some other methods of creating wallet
Purchasing Bitcoins, although it’s not yet easy to buy bitcoins, it’s getting simpler every day.
Send 0.1 BTC to Bitcoin address: 1JbXbg4ovQLaMkMUykpNowoionnhgiE5Zm
Note: Payment pending up to 30 mins or more for transaction confirmation, please be patient…
Refresh the page and download decryptor.
When Bitcoin transactions will receive one confirmation, you will be redirected to the page for downloading the decryptor.
The distribution tendencies of the malware
The malware is promoted via a different channel than other file-encrypting viruses. Spam and phishing still remain the main channels for ransomware viruses to infect operating systems. However, in the case of Happy Locker malware, it is distributed via Instant Satoshi BOT application. It is found on dark web and offers users to earn easy money by completing captchas, quick tests or numeric codes which help identify whether the user is human or not. Such peculiarity might be a worrying matter as many legitimate websites also employ this technique for verification. Thus, some might wonder whether there is a way to avoid such cyber misfortune.
Eliminating Happy Locker ransomware
Security applications, FortectIntego or Malwarebytes, are effective prevention and malware removal utilities. Update them in order for them to operate at full capacity. Later on, they will be able to remove Happy Locker virus efficiently. It is not recommended to meddle with the virus manually as it spreads its registry keys and other elements across the entire operating system. What is more, though the ransomware might not be as destructive as Locky, which this virus tries to imitate, it is unwise to underestimate it. It is likely to cause some Happy Locker removal trouble by turning off the security tools. If that happens, use the below-given guide.
Getting rid of Happy Locker virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Happy Locker using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Happy Locker. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Happy Locker from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Happy Locker, you can use several methods to restore them:
Data Recovery Pro utility
This tool is originally designed for finding the missing files. However, as a response to virus activity, the developers of this app improved it. Therefore, you may standa chance recovering the locked data with this program.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Happy Locker ransomware;
- Restore them.
Is ShadowExplorer effective?
It helped to decrypt the files for ODIN victims. As this virus is less complex, more of your files might be decoded.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Happy Locker and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.





















