ODIN ransomware / virus (Removal Guide) - updated Nov 2016
ODIN virus Removal Guide
What is ODIN ransomware virus?
What is ODIN ransomware virus?
ODIN ransomware hails from an infamous family of Locky virus. This cyber threat was released as the addition to the notorious campaign that has already affected thousands of computer users who found their files useless. According to experts, this ransomware is named after its exceptional feature – it can encrypt your files and append .odin file extension to each of them. Next, it drops HOWDO_text.html and similar files on your computer’s desktop that let you know about a special ransom that you need to pay in exchange for the decryption key. As the original virus is continuously developing and keeping the virtual community under its shadow of terror, you should be extremely careful with this malware. Though it is not difficult to remove ODIN virus itself, the decryption of files is a complicated matter. Fortunately, 2-spyware researchers have already found several methods that can be used for recovering files. If you are already infected and misfortune enough not to have backups of your encrypted files, collect yourself. First of all, it is necessary to complete proper and full ODIN virus removal in order to proceed to file recovery.
It seems that the main reason why we have to deal with Odin is the success of Locky virus which exceeded its developers’ expectations. Most probably, they decided to retain the title of most dangerous ransomware threat for a longer while and presented ODIN. Since the emergence of its original version in February, the world has seen already several versions ,e.g., Zepto, Bart, Thor, etc. Now the hackers could not resist the current trend to name the ransomware after movie or fictional characters and gave their virus a grand name as well. As well as the original bearer of this name – Odin – the oldest and main deity in Norse mythology, the virus also tries to invoke similar overwhelming impression. It employs common RSA-2048 and AES-128 encryption algorithms to encode personal files. Since these strategies are based on a mathematical equity, it is a difficult task to find an alternative private key for the unique public key.
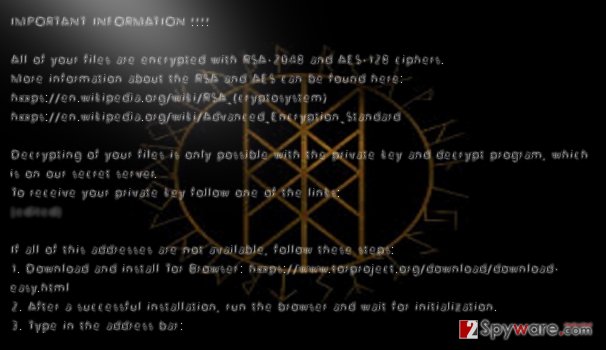
Moreover, in order to inflict more damage, .ODIN file extension malware developers set a broad range of extensions for the virus to encrypt. It may take a while for the virus to locate your possibly valuable files and append .odin file extension to them. However, when it is finally done with the process, the ransomware presents three files: _[2_digit_number]_HOWDO_text.html, HOWDO_text.bmp, and HOWDO_text.html in which the victims are disclosed their current situation. An example of the latter ransom note variant can be seen below:
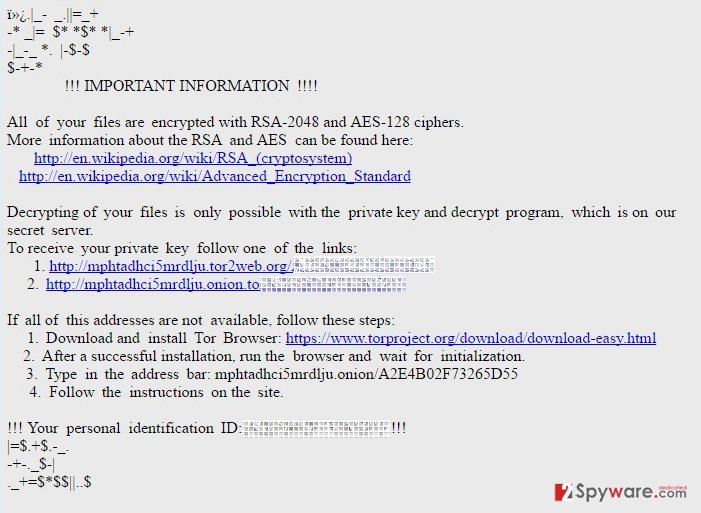
As its predecessor, ODIN ransomware also asks to employ anonymity-assuring Tor browser. Within it, the victims are expected to remit the payment and supposedly receive the private key to unlock the files. Brush aside any considerations to waste money and concentrate on the elimination of the malware. Let FortectIntego to speed up the procedure. After that, you may still have a chance to recover your data. You can do that using one of our suggested data recovery techniques at the end of the article.
The latest techniques used to spread ODIN
Odin is still in its active distribution stage. The most of its examples are detected spreading with the help of spam (a full explanation of this distribution technique and initial methods used to promote this ransomware can be found in “virus detection” section). However, we should exclude the latest spam campaign noticed in the middle of November which relies on law-related theme. The misleading email message that reports: PLEASE READ YOUR FAX T6931. The attachment added to this malicious email message is named as “Criminal Case against_You-O00_Canon_DR-C240IUP-4VF.rar”. Seems quite tricky, right? However, no matter how interesting the criminal case you are possibly dealing with seems, you should know that the attachment is infected with the Trojan Downloader which is set to download Odin virus to the system.
Update October 2016: ransomware spotted on Honolulu Fire Department’s computers
The end of September marked the biggest cyber attack ODIN ransomware has committed so far. Around 20 computers located in Honolulu’s Fire Department were hacked after one of the administration employees opened a personal email containing the infection. Soon after the news had reached the authorities, the Fire Department workers were ordered to shut down their computers to curb the spread of the virus. Luckily, the emergency response system was not affected and could continue to operate while the IT sector worked on eliminating ODIN virus from the network of administrative computers. Nevertheless, the attack did not pass that easily: Fire Department’s email exchange, internal administrative duties and communication have been paralized for a whole day until all ODIN files were decontaminated. The virus was successfully removed and the whole data was restored from backups, so the authorities did not have to empty their wallets to get their institution’s files back. You can only imagine, though, what disastrous consequences would fall on the companies which haven’t backuped their data.
It seems that the virus is becoming more advanced as it continues to spread around the world. Though Europe is still its main target, although the computers in Asian countries, USA and African continent are becoming increasingly infected as well. Thus, major company breaches are more likely to happen. As the program improves, the method it uses to infect computers also changes. Some time ago, the virus used WSF or JS files to download the virus executable on the computer. Now, instead of the executable, DLL file is used to deploy the malicious ODIN script. It seems like a small change, but it is a whole another challenge for the antivirus developers. The virus will only keep expanding and improving, so institutions, companies and private users simply have to start taking about the preventative measures.
Odin virus detection
Most likely, .odin file extension virus might have used the chance to take control of your device via an infected spam message. It is a common strategy for the majority of ransomware threats as this tendency, unfortunately, proves to be successful. After receiving a fake invoice or simply a video with an intriguing headline, few suspect that there might lie a greater danger behind such veneer. The recent reports claim that currently, the virus is delivered as a fake receipt file, with a subject title “Receipt [random numbers]” or similar. Thus, the users who regularly shop online can easily give into the curiosity and click on the infected attachment. Then, it is only a matter of time when the virus sets out to perform its mischief. In addition, some versions of ODIN malware might also be distributed via exploit kits. In order to ward off such insidious files, it is crucial to improving your security with a proper anti-spyware application.
ODIN ransomware elimination steps
Since you are dealing with a complex file-encrypting malware, we do not recommend meddling with it manually. In relation to this, it would be better to entrust ODIN ransomware virus removal to a security application. There are multiple of them, which get rid of the virus: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes. After the completion of the termination, you can think about data recovery. Therefore, we present several suggestions below this article. However, note that you need to remove ODIN virus first and only then try to decode the files. Otherwise, the data recovery might turn out into failure.
Getting rid of ODIN virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove ODIN using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of ODIN. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove ODIN from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.Unfortunately, there is currently no ODIN decryption tool that could help lift the encryption. The only option the criminals suggest is purchasing the Locky Decrypter. We strongly recommend abstaining from doing that, because this decryption tool is a malicious program and may damage your system instead of fixing it. That is why we present a couple of methods that could be used to recover the encrypted files without having to pay the extortionists.
If your files are encrypted by ODIN, you can use several methods to restore them:
Recover your files encrypted by Odin with the help of Data Recovery Pro
This application is specifically designed for locating missing files and folders in your computer. Though it was initially designed for system wreckage cases, when your files get lost or damaged, you might as well give it a chance and try to retrieve your files using this application.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by ODIN ransomware;
- Restore them.
Use Windows Previous Version feature to decrypt your files encrypted by Odin
In abstract terms, this functionality turns back time. In other words, it reverts the operating system to the previous build. Likewise, you gain time to copy the files which are not affected by the ransomware yet. There is one “but” to this useful feature. It only works if the System Restore function was enabled before the Odin virus was deployed on the system. Besides, this technique will not unlock all of your files. So choose wisely what important documents you want to have recovered.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Using ShadowExplorer method for data recovery
ShadowExplorer is a software created for recovering files using the Volume Shadow Copies — a type of backup information that is stored on the system. There is a risk, though, that Odin ransomware, like its predecessor Locky, deletes Shadow Copies of files as soon as it enters the system. In such a case, this method will not be effective. Nevertheless, it is still worth giving it a try. Learn how to recover your data using ShadowExplorer here:
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from ODIN and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.







