Helathy adware (virus) - Free Guide
Helathy adware Removal Guide
What is Helathy adware?
Helathy is an adware-type program that shows intrusive advertisements regularly
Helathy adware is not usually installed by users intentionally, as they are tricked into doing so with the help of software bundling – a deceptive practice, extremely common for potentially unwanted program distribution. Alternatively, some users may also install the virus after being tricked by a misleading advertisement that claims that the system is infected or that there are other unverified reasons to install it.
Once on the system, Helathy adware would immediately begin advertisement campaigns via Google Chrome or another compatible web browser. Unfortunately, adware is known for being associated with insecure advertising networks, which results in users being exposed to scams and phishing content. Redirects to malicious sites are likely as well.
The software can only run on Windows operating systems, so Mac users can be confident that they are safe from this infection. In this article, we will provide more information on the Helathy virus and teach you how to remove it from your system effectively, stopping the annoying pop-ups, banners, auto-play, and similar annoying ads.
| Name | Helathy |
| Type | Adware, potentially unwanted application |
| Distribution | Software bundling, third-party websites, misleading ads |
| Symptoms | Shows intrusive advertisements, phishing material, and promotes other potentially unwanted applications |
| Risks | Ads might include links to potentially dangerous or even malicious websites, resulting in malware infection, personal information disclosure, or financial losses |
| Related | Words, Drinker, Energy |
| Removal | The easiest way to remove malicious software from Windows is by employing SpyHunter 5Combo Cleaner security software and then cleaning web browsers |
| Other steps | Malware or adware infections can diminish the performance of your computer or cause serious stability issues. Use FortectIntego to remediate your device and ensure that the virus damage is fixed |
How adware spreads on Windows platforms
Most users claim that they themselves did not install Helathy virus. This may be surprising, but users actually install adware themselves, as the distribution techniques used by these potentially unwanted programs do not allow automatic installation. Only more sophisticated malware, such as rootkits,[1] can be installed with the help of exploits or other advanced methods. It is worth noting that some adware may be included along with malware payload as a tool to generate revenue for the cybercriminals.
Typically, adware is installed with the help of one of the following methods:
- Software bundling;
- Fake ads/phishing messages.
In order to avoid being tricked by bundled software, you should always pay very close attention to the installation of shareware/freeware,[2] especially if it is downloaded from third-party websites. During the installation process, users can be shown misleading information to make them install programs they aren't even aware of – this is done thanks to misplaced “Accept offer” buttons, pre-ticked checkboxes, and promotion of “Recommended” settings, and similar.
Overall, if there's a possibility to download software from its developer or other official sources (Microsoft Store, Google Web Store, etc.), always choose the latter option, so you can know that the installer is genuine and not compromised.
When it comes to suspicious and misleading advertisements, you should always watch out for messages or pop-ups which claim that something is missing from your system and needs to be installed. For example, you could be told that you need to install a particular font to view the page or that your Flash Player is out of date. Fake virus infection notices can also spread adware or malware.
Helathy adware removal steps
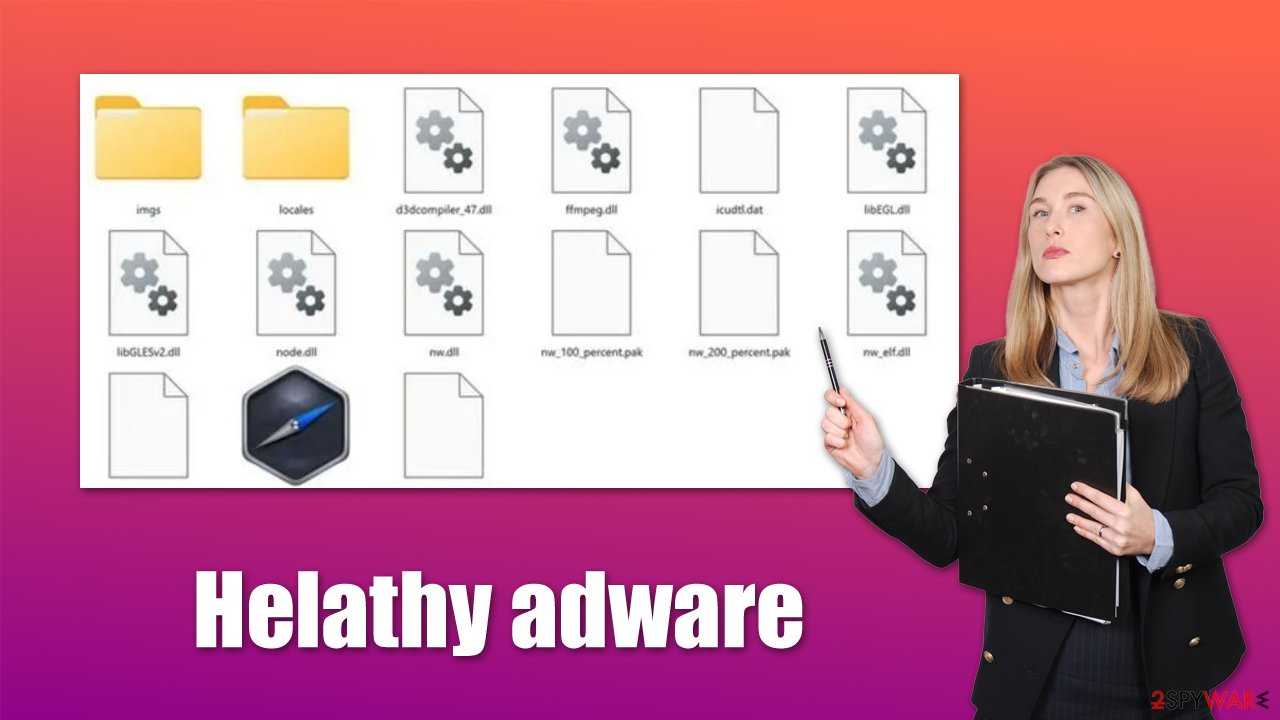
When it comes to adware removal, it depends on the severity and capabilities of a particular example. Most adware nowadays comes as browser extensions, as it is their main operation surface. However, some PUPs are still installed on the system level, which can also change Windows registry settings or create new scheduled tasks to remain on the system for as long as possible.
This is why we strongly recommend you remove Helathy virus with SpyHunter 5Combo Cleaner, Malwarebytes, or another powerful security software instead of following through with the manual steps below. This would ensure that all the malware-related files are removed effectively. If you rather do it yourself, follow these steps:
Windows 11/10/8
- Enter Control Panel into the Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Windows 7/XP
- Click on Windows Start > Control Panel located on the right pane (if you are a Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.
![Uninstall from Windows 7/XP Uninstall from Windows 7/XP]()
- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Once the program is deleted, you need to remove the leftover files as follows:
- Press Win + E to open File Explorer
- At the top, go to the View tab
- Mark the Hidden items checkbox
- Next, go to your main drive (usually drive C) and enter the following path:
C:\Users\YOURUSERNAME\AppData\Roaming - Locate the Helathy folder and delete it.
Clean your browsers from cookies to prevent tracking
After removing adware and other potentially unwanted or malicious programs from your system, we recommend not to forget the browsers, as adware is known to operate using this application. This means that advertisements are often initiated during the operation of the web browser, although in some rare cases, the pop-ups may show up independently of which other programs are currently running in the background.
Cookies[3] are one of the most common elements used by adware, and Helathy is no exception. Upon infiltration, it places and stores cookies locally on the victims' machines, which allows constant surveillance of various user actions online, including their browsing history, search queries, ads clicked, technical device data, unique identifiers, and more.
To remove leftover files effectively and quickly, we recommend using the FortectIntego repair and maintenance tool. In case adware or malware manages to break the integrity of Windows system files, it can easily fix them automatically without you having to reinstall the operating system. Alternatively, you can always proceed with manual instructions:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies, and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
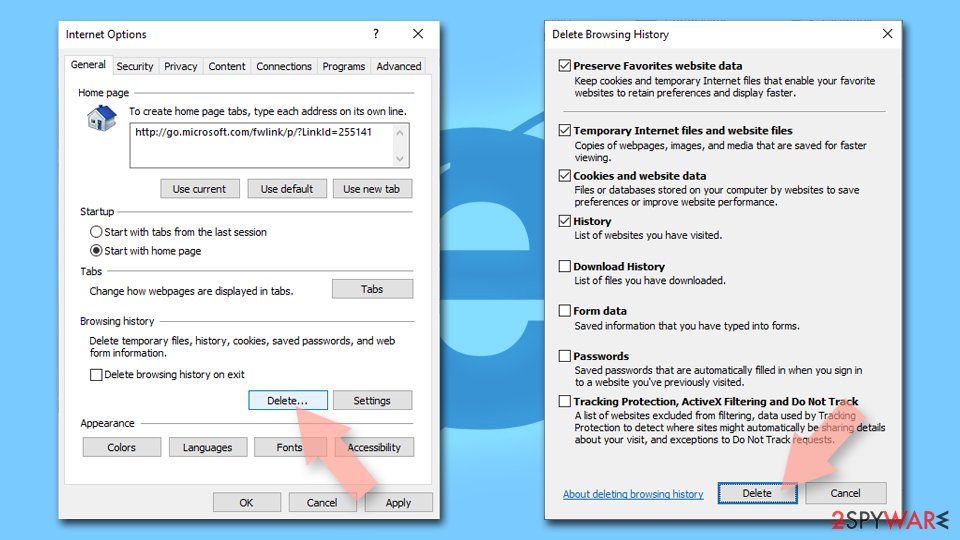
Internet Explorer
- Press on the Gear icon and select Internet Options.
- Under Browsing history, click Delete…
- Select relevant fields and press Delete.
![Clear temporary files from Internet Explorer Clear temporary files from Internet Explorer]()
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Rootkit. Wikipedia. The free encyclopedia.
- ^ Freeware v/s Shareware. GeeksforGeeks. A computer science portal for geeks.
- ^ What are cookies? | Cookies definition. Cloudflare. The Web Performance & Security Company.