Hese ransomware (Removal Instructions) - updated Sep 2019
Hese virus Removal Guide
What is Hese ransomware?
Hese is crypto-malware the is using a comprehensive asymmetrical encryption method to lock all files on the host machine
Hese is a ransomware infection that started infecting users in India, Spain, Argentina, Uruguay, and other countries. As it is typical to Djvu/STOP variant, the victims are selected randomly and all their personal files are locked with the help of an asymmetric cipher – data can no longer be accessed and marked with .hese file extension.
To retrieve files encrypted by Hese virus, victims are asked in the _readme.txt ransom note to contact ransomware developers via gorentos@bitmessage.ch or gorentos2@firemail.cc emails and pay up the ransom of $980 (crooks also offer a 50% discount if the contact is made within 72 hours of the infection). Besides encrypting all personal data, Hese ransomware also changes “hosts” file located on every Windows system in order to prevent users from visiting security-related websites, including 2-spyware.com.
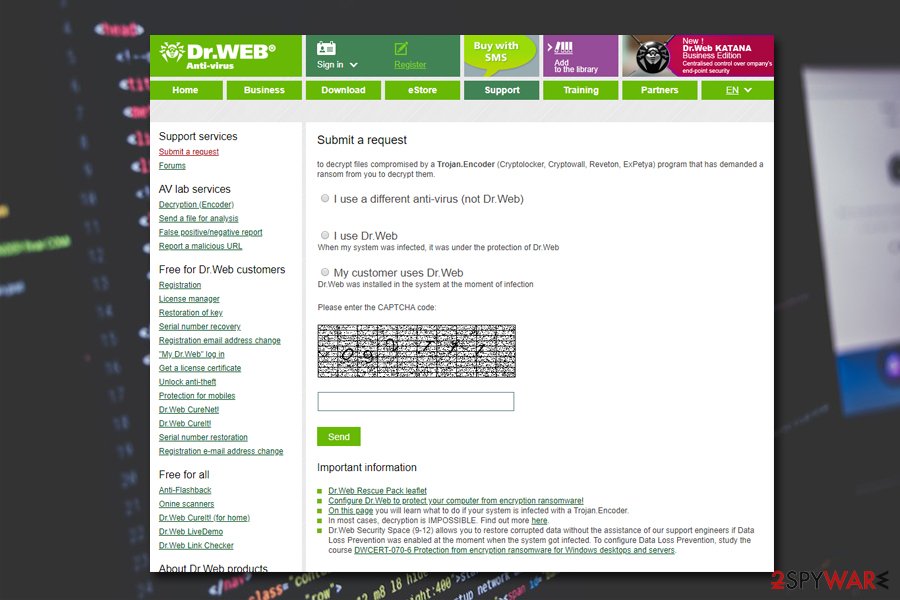
Unfortunately, but Hese belongs to the new wave of the infections, which are no longer decryptable with tools like STOPDecrypter. The only hope to recover at least some files is to contact Dr.Web and use its paid service or try out third-party recovery tools. Regardless of file recovery, Hese ransomware removal should be performed before that. Additionally, infected users should delete the hosts file located in C:\Windows\System32\drivers\etc folder to be able to enter cybersecurity websites again.
| Name | Hese ransomware |
|---|---|
| Type | Cryptovirus – type of malware that focuses on money extortion |
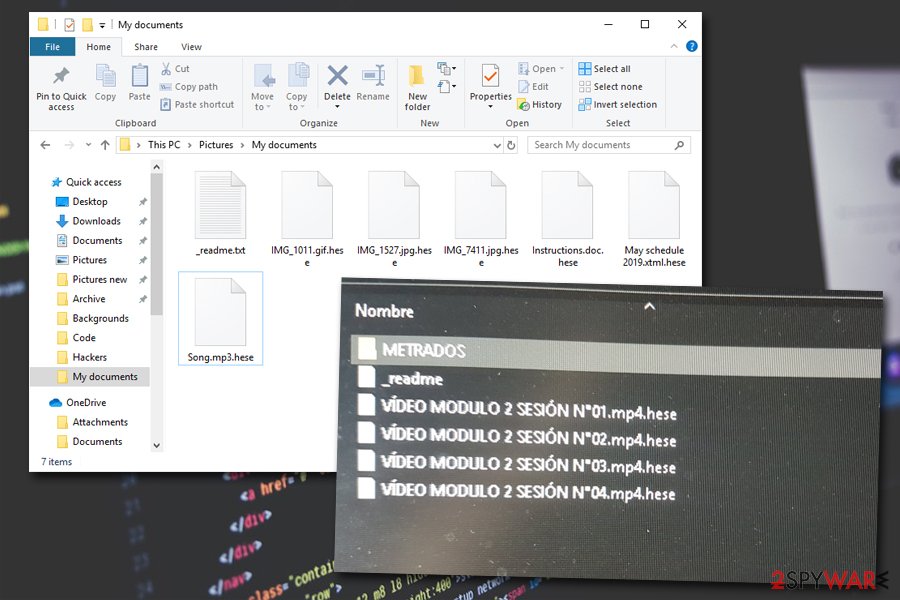
| File marker | As soon as the malware infects the computer, pictures, videos, documents and other personal files are appended with .hese file extension |
| Family | Hese ransomware belongs to Djvu/STOP malware, which is one of the most notorious ransomware families that was first introduced to the world in December 2017 and released over 150 variants since |
| Ransom demanding note | Ransom note _readme.txt is dropped into each of the affected folders – it informs users about the file hijacking |
| Ransom amount | Hackers ask for $980 for the decryptor, although users are also offered a 50% discount if the contact with criminals is made within 72 hours of the infection |
| Distribution | Bundled adware installers, exploits, web injects, software cracks (such as “NBA (Game) Serial Key,” for example), unprotected RDP, etc. |
| Main functions | Encrypts files, alters hosts file, installs privacy-threatening malware |
| Additional payload | It is known that AZORult malware can be delivered with the help of this ransomware virus |
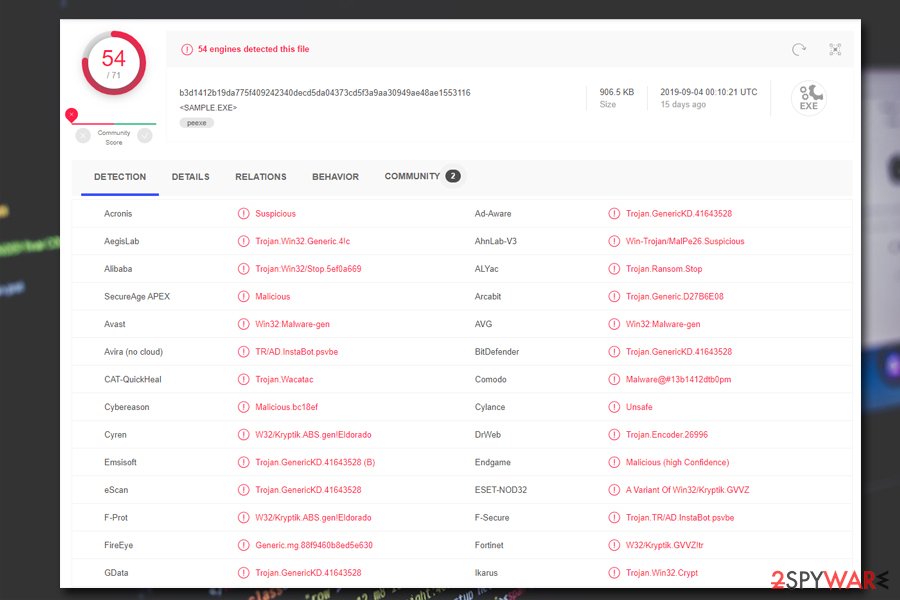
| Recognized by av vendors as[1] |
|
| Elimination | Install anti-malware software and remove Hese ransomware completely from the system. To fight virus damage, we recommend using FortectIntego |
| File decryption | There is a chance of restoring particular file types (.pdf and MS Office files) with the help of a paid service from Dr.Web. Alternatively, you could try third-party tools and Windows Previous Versions feature to retrieve at least some of the locked files |
| Additional actions | You need to delete Windows hosts file in the following folder: C:\Windows\System32\drivers\etc |
Hese ransomware distribution methods
Distributing Hese with the help of various methods is worth for criminals, as it increased chances of more victims getting infected, which consequently results in more ransom payments. Throughout the time of STOP virus operation, hackers used exploit kits, spam emails, unprotected RDP, fake updates, and other common malware distribution methods.
Most recently, however, users reported being infected with Hese ransomware (and other variants) after extraction of cracks for software and video games (for example, “NBA (Game) Serial Key”). These unsafe tools can be downloaded from various unsafe sites, such as torrent or dodgy websites specifically crafted by criminals in order to impersonate a distributor of keygens or cracks.
Therefore, you are highly advised staying away from illegal software and cracks, as downloading these tools might give you a nasty surprise instead of a working cracked program. In the worst case, you should at least scan the executable with tools like Virus Total or comprehensive anti-malware software to prevent Hese virus from infiltration.
Characteristics of Hese ransomware operation
Ransomware is a serious computer threat and, thanks to its ability to keep files locked after its elimination, has become one of the most lucrative business models for hackers. It is not surprising that this malware alters Windows system profoundly in order to perform what it was designed to do – encrypt all files with .hese extension and then ask ransom for their release.
Upon installation on Windows OS, Hese ransomware creates a randomly-named executable that is placed into the %AppData% folder – it is then used to launch the file scanning process. Before that, however, the malware also performs the following changes:
- Modifies Windows “hosts” file to prevent users from visiting security sites;
- Launches Shell Commands;
- Creates new processes to be run in the background (for example, C:\Users\username\AppData\Local\Temp\TeBF7MXfgNte0R.exe
- Creates mutexes;
- Loads new modules;
- Deletes Shadow Volume Copies;
- Modifies Windows registry, etc.
Additionally, Hese ransomware might install additional payloads, such as AZORult malware[2] or install modules that would harvest sensitive banking information from Google Chrome, Safari, Mozilla Firefox, or another installed browser. That is another reason why infected users should remove Hese ransomware from their systems as soon as possible with the help of anti-malware software. Besides, using tools like FortectIntego can ensure that all the affected system files get repaired and there is no need to reinstall Windows, if the damage is severe enough.
Hese ransomware encryption process and possible decryption methods
Hese ransomware is the malware that targets Windows computer and makes users' files useless once it gets on the machine. The virus immediately stars the encryption process and interferes with other parts of the system, programs, and files.
The initial versions of STOP/Djvu virus used AES and other symmetrical encryption algorithms to encrypt files, which means that the secret key that is used to lock data is the same as the one that is used to unlock it. However, the key is only known to cybercriminals behind the malware, as it is held on a remote server.
Hese now uses asymmetric encryption method, which means that the key to encrypt data is public (available to everybody to see), while the decryption key is different – unlike in the symmetric encryption method. The encrypted file formats include, but not limited to, the following:
.mp4, .7z, .rar, .m4a, .wma, .avi, .wmv, .csv, .d3dbsp, .zip, .sie, .sum, .ibank, .t12, .qdf, .gdb, .tax, .pkpass, .bc7, .bkp, .qic, .bkf, .sidn, .sidd, .mddata, .itl, .itdb, .icxs, .hvpl, .hplg, .hkdb, .mdbackup, .syncdb, .gho, .itm, .sb, .fos, .mov, .esm, .vcf, .vtf, .dazip, .fpk, .mlx, .kf, .iwd, .vpk, .tor, .psk, .rim, .kdb, .pak, .big, wallet, .wotreplay, .xxx, .desc, .py, .m3u, .flv, .js, .css, .rb, .png, .jpeg, .txt, .pfx, .pem, .crt, .cer, .der, .x3f, .srw, .pef, .ptx, .r3d, .rwl, .raw, .raf, .orf, .nrw, .mrwref, .mef, .erf, .kdc, .dcr, .crw, .bay, .sr2, .srf, .arw, .3fr, .dng, .jpe, .jpg, .pdf, .pdd, .psd, .dbf, .mdf, .wb2, .rtf, .wpd, .dxg, .xf, .dwg, .pst, .accdb, .mdb, .pptm, .pptx, .ppt, .xlk, .xlsb, .xlsm, .xlsx, .xls, .wps, .docm, .docx, .doc, .ods, .odt.
At the end of each file, the infected users will notice a .hese marking; for example, a file named “picture.jpg” will be turned into “picture.jpg.hese.” While it may seem like data is corrupted, it is only partially true, as encryption should be imagined as a lock that can be only opened with a particular key that hackers possess. Unfortunately, threat actors are happy to use this situation for their advantage – they ask for ransom in Bitcoin for the decryption tool.
Previously a specific tool – STOPDecrypter – could have been used to retrieve data which was locked with a hardcoded key (i.e., the locking process was performed offline). However, due to significant improvements that hackers implemented in Hese virus, this method is no longer valid.
However, if your files are encrypted with .hese, you should not lose hope yet. If you are willing to pay a much lesser sum of money than the ransom for partial decryption, you can contact Dr.Web. As of now, the the Rescue pack costs €150, and can decrypt .PDF and MS Office files.
Why you should avoid paying ransom to Hese virus authors
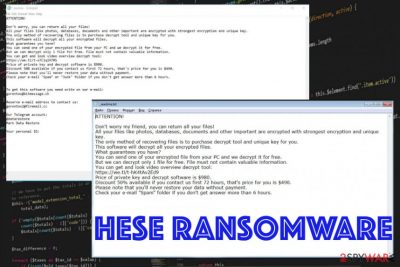
Hese file virus is demanding a ransom in _readme.txt file that shows up in every folder with encrypted data and on the desktop. Here's the statement by hackers behind the malware:
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-o7ClqIH7RS
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.To get this software you need write on our e-mail:
gorentos@bitmessage.chReserve e-mail address to contact us:
gorentos2@firemail.ccOur Telegram account:
@datarestore
Mark Data RestoreYour personal ID:
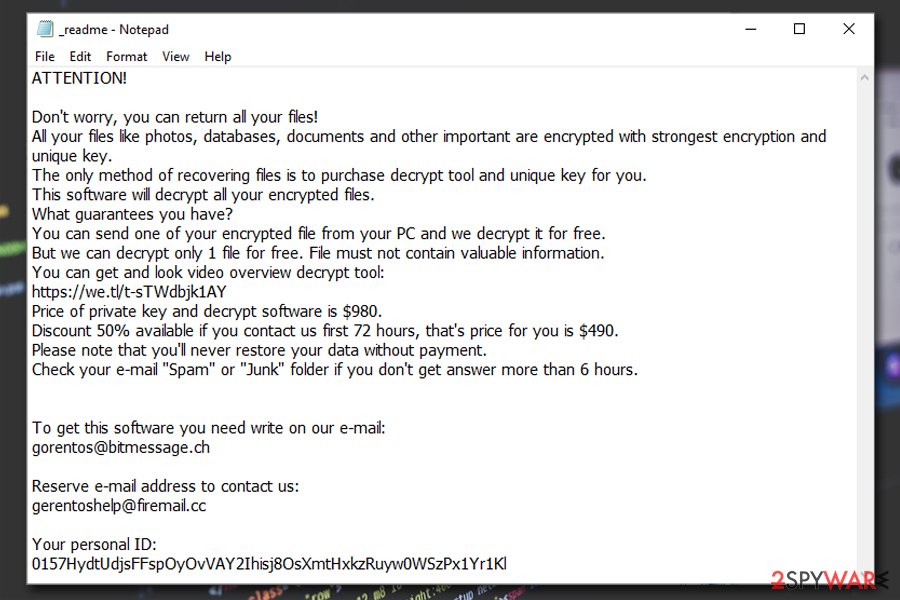
Although the ransom message states about the “only ” solution for file decryption, Hese developers are cybercriminals, and they care about their gains, and not the well-being of their victims. Even when the ransom amount has a discount, you shouldn't believe the criminals and stay away from paying the demanded amount in Bitcoin.[3]
Besides, paying Hese ransomware authors would only prove that their illegal business works, and will only encourage them to infect more victims. Additionally, there is no guarantee that the tool threat actors will send you will work in the first place. However, if you are willing to risk your money, you can contact criminals and explain the situation – in some cases they might show remorse and decrease the value of the decryptor.[4]
We provide alternative ways to decrypt Hese encrypted files below – you might be lucky and recover your files without spending money. Additionally, security experts are always working on decryption tools that would allow victims to retrieve ransomware-locked files for free – you can check these sites for any updates on decryptors:
- https://www.nomoreransom.org/en/index.html
- https://id-ransomware.malwarehunterteam.com/
- https://www.avast.com/ransomware-decryption-tools
- https://www.emsisoft.com/ransomware-decryption-tools/
Get rid of Hese ransomware virus and wait for the new decrypter from ransomware researchers
Although the previous decryption tool is not working towards this variant, you need to remove Hese ransomware as soon as possible with other methods. You can still collect files affected by the virus and wait for the proper decryption tool, but system cleaning is crucial if you want to use the device normally again.
Hese virus removal is not that difficult if you trust expert[5] recommendations and get professional anti-malware software for the job. Install it and run a full system check with the application. If the procedure fails, you should access Safe Mode with networking in order to delete the malicious payload without disruptions.
Getting rid of Hese virus. Follow these steps
Manual removal using Safe Mode
Reboot the machine in Safe Mode with networking before you scan the system using anti-malware tools and remove Hese ransomware
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Hese using System Restore
System Restore is the feature that can be enabled and help to get rid of the virus this way
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Hese. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Hese from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Hese, you can use several methods to restore them:
Data Recovery Pro – a program for file restoring
Hese ransomware encrypted files are possible to restore with data backups from external device or software like Data Recovery Pro
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Hese ransomware;
- Restore them.
Windows Previous Versions feature recovers your files after Hese ransomware attack
If you need an alternate option for file backups, rely on Windows Previous Versions. The method works when System Restore gets enabled in the first place
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer – a feature for file recovery
When Shadow Volume Copies are left untouched, you can use Shadowexplorer and restore any data
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Try Dr.Web's decryption service
If you are willing to pay for partial file decryption by Hese file virus, you can contact Dr.Web for .pdf and MS Office file decryption service.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Hese and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ b3d1412b19da775f409242340decd5da04373cd5f3a9aa30949ae48ae1553116. Virus Total. File and URL analyzer.
- ^ By Pierluigi Paganini. STOP ransomware encrypts files and steals victim’s data. Security Affairs. Security website.
- ^ John E Dunn. US city balks at paying $5.3 million ransomware demand. Sophos. Naked security news.
- ^ Ondrej Kubovič . ESET releases new decryptor for Syrian victims of GandCrab ransomware. WeLiveSecurity. ESET security blog.
- ^ Uirusu. Uirusu. Spyware related news and virus removal guides.





















