Hored.live ads (scam) - Free Guide
Hored.live ads Removal Guide
What is Hored.live ads?
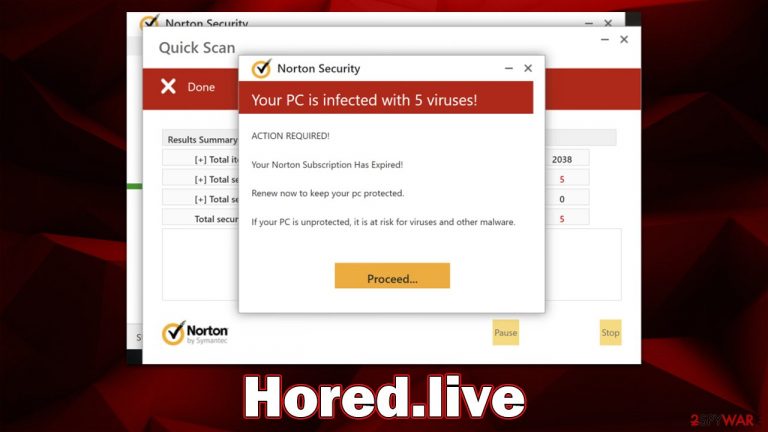
Hored.live promotes fake pop-ups that imitate security software scan results
Hored.live is a malicious website that displays false virus infection messages for the purpose of earning affiliate sales from software. Most people end up on this site after clicking a dangerous link on torrent or similar high-risk websites, but it's not always the case – adware could be the reason for unexpected redirects, too.
As soon as you enter the site, you're greeted with a fake security scan that claims your system is infected with viruses. The only way to remove these supposed threats is to renew your subscription to Norton Anti-Malware software. Of course, this is all just a ploy to get your money, and there's nothing legitimate about these claims. The security vendor has nothing to do with this scam as well and links shown there may lead to malicious websites and fake anti-malware download pages.
Hored.live also offers to enable push notifications to visitors – something that could provide additional income to scammers. Refrain from interacting with anything shown to you via the push notification pop-up window – we explain how to get rid of these as well. Likewise, we will show how to remove everything suspicious from your system effectively and easily.
| Name | Hored.live |
| Type | Scam, phishing, adware, redirect virus |
| Distribution | Compromised websites, pop-up ads, potentially unwanted applications |
| Scam content | Shows fake messages about virus infections, allegedly coming from Norton security software, and claims that the license of anti-malware has expired and needs to be renewed in order to fix the issue |
| Dangers | Financial losses due to fake subscriptions; redirects to other malware-laden, scam websites; installation of potentially unwanted or malicious software |
| Removal | Do not interact with links or other content of a scam site. Instead, check your system with SpyHunter 5Combo Cleaner security software |
| Other tips | Once you have removed all of the unwanted software, it is important to clean your web browsers and fix any corrupted system files. You can do that automatically by following the instructions here FortectIntego or referring to our manual guide. |
Scam operation techniques dissected
Users are frequently taken aback by what they see once they have logged on to the website: several windows with names such as “Quick Scam” flash up, which perfectly imitates a legitimate way of scanning of a device. In a matter of seconds, they are given the impression that their computer is infected with various threats, and the notorious “Your PC is infected with 5 viruses!” message comes up straight after that.
Along with the declaration of the alleged viruses found, it is also claimed that users' security software has expired, and there's no way to get rid of the found infections without a working tool. This is a typical social engineering scheme component – to make people question their computer security state and purchase the offered software or other services.
After frightening users, Hored.live shows the “Proceed” button, which redirects people to the purchasing page of the security software. While most commonly, it reroutes people to the official website of the vendor, it might not always be the case, and you may end up on malware-laden sites. Besides, by purchasing software in such a way, you would only be supporting scammers, so refrain from doing so.

Is your system infected?
As soon as users enter Hored.live scam site, they either believe what is happening or not. Since scammers use legitimately-looking pop-ups that imitate security scans so well, some users might be convinced that message about an infected computer actually comes from Norton.
However, it is important to note that the user interface of the scan has nothing to do with the official one, as these pop-up windows are mere imitations. There is no way that malware could be detected on your computer just by you accessing some website unless your PC has already been compromised.
There are some users that aren't completely sure of what happened and are afraid that accessing the scam site might have compromised their computer security. In reality, it is unlikely for anything like that to happen by just visiting a scam website alone – not clicking any links and downloading software is what's the most important.
Check your device for infections
Just because everything that's claimed on Hored.live is bogus, it does not mean that your system is clear from infections. For example, adware is known for its ability to redirect users to phishing[1] websites and expose them to intrusive ads, so you should definitely check your device.
Adware is a sort of program that spreads via software bundles[2] or other suspicious means, allowing it to enter unnoticed. It may execute processes and display advertising, redirects, and various other activities in the background.
Instead of relying on fake scan results or downloading unreliable software from these ads, we recommend employing the SpyHunter 5Combo Cleaner or Malwarebytes security tool that can immediately expose all the malicious components on the system and effectively remove them. Also, with FortectIntego, you could quickly get rid of leftover files such as cookies used for tracking and cleaning your system to ensure the best performance.
Get rid of push notifications from malicious websites
A push notification prompt is shown to users entering the Hored.live site immediately. While people usually decline this offer, some might accidentally click the “Allow” button. Only later would users notice that their screens are being spammed with intrusive pop-ups which show more misleading information, such as fake virus infections or get-rick-quick[3] scams.
Just like with the website itself, we do not recommend interacting with these notifications or visiting websites they link to. If you have encountered this issue, you should follow the steps below to address it:
Google Chrome
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Phishing attacks. Imperva. Application and data security.
- ^ Bundled software. Computer Hope. Free computer help.
- ^ Get rich quick scams. SRA. Solicitors Regulation Authority.
