I sent you an email from your account scam (Free Guide) - Virus Removal Instructions
I sent you an email from your account scam Removal Guide
What is I sent you an email from your account scam?
I sent you an email from your account scam – a phishing email that is sent to random users by using the email-spoofing technique
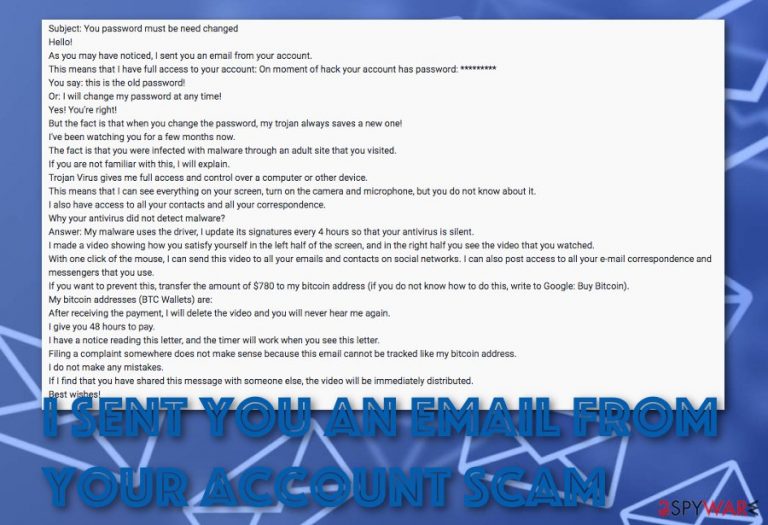
I sent you an email from your account scam is a fake and threatening email message that provides false information to collect $780 in BTC as ransom. Hackers who distribute such questionable email use the email-spoofing technique[1] when it looks like the user has sent the scam message to himself. The email's title line appears to be “You password must be need changed” that encourages users to open and view the content inside. I sent you an email from your account scam virus will try to trick you about gaining full access to your email account and computer and infecting you with malware during your visit to an adult-related source. Nevertheless, the scam will even state that you have been spied on while performing private activities in front of the computer screen and everything will be posted on the Internet if the Bitcoin payment is not made in 48 hours.
| Name | I sent you an email from your account scam |
|---|---|
| Type | Spam tool/scam message |
| Goal | Hackers who distribute this type of email seek to collect as much income as possible by providing people with false information and threats |
| Email title | If you ever received this email scam, note that it will supposedly come with this title: “You password must be need changed” |
| Ransom | Crooks who push this scam message urge for a quite big sum. The price is $780 which needs to be transferred in Bitcoin cryptocurrency |
| Conditions | Criminals urge for the money to be transferred via a 48 hours period in order for them “not to post a private video of you” |
| Potential danger | The suspicious scam message might include infectious hyperlinks or attachments that might carry some malware-laden payload |
| Receiving email addresses | Hackers might steal private data if it was exposed during data leaks on specific forums and similar. Also, you might end up with a leaked email address if you type it in while filling some bogus online surveys |
| Removal | Get rid of the scamming message from your email box as soon as you discover it. There is no need to believe in what it says as all is written just to threaten and swindle a big amount of money form you |
| Safety tip | After you get rid of the bogus email message, it is about time to scan your computer system and check if it is fully protected. Due to the slight risk that some type of malicious strain might have entered your machine after opening a bogus attachment or clicking somewhere on the message, you should perform a thorough system scan with FortectIntego software that might indicate affected files and help you fix them |
I sent you an email from your account scam is a completely fake message that does not provide any reliable information. You should not fall for believing in the claims that are written in this email as you will waste a big amount of money for nothing. These types of scams are very common and have been taking control of numerous users' minds lately. Rather than agreeing with the hackers' demands, you should remove I sent you an email from your account scam from your email box.
Hackers that promote I sent you an email from your account scam also falsely claims that the malware that has been used for recording visual data and attacking the victim cannot be detected by AV engines as the malware itself prevents being spotted by antivirus software while running on a driver that gets updated every 4 hours:
Subject: You password must be need changed
Hello!
As you may have noticed, I sent you an email from your account.
This means that I have full access to your account: On moment of hack your account has password: *********You say: this is the old password!
Or: I will change my password at any time!Yes! You're right!
But the fact is that when you change the password, my trojan always saves a new one!I've been watching you for a few months now.
The fact is that you were infected with malware through an adult site that you visited.If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.I also have access to all your contacts and all your correspondence.
Why your antivirus did not detect malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts on social networks. I can also post access to all your e-mail correspondence and messengers that you use.If you want to prevent this, transfer the amount of $780 to my bitcoin address (if you do not know how to do this, write to Google: Buy Bitcoin ).
My bitcoin addresses (BTC Wallets) are: 19Q3HZtnznuB5cuWng8cacwqZV13gNpZaN, 1HPhZrmyevkNXKo1MYnZG1A65p2PtyEpqc, 18kXxMp9NuTMUFVAfXR4TFT4CrrHWVzwm4, 1PNpAXTo6jh4V9dhXRvimNYqPYjvZEnQiu, 16LBDius3vg6ufFvnc7PGXfiTZgphuZgr5, 18eBGkYam1wjz1S77jz3VmADuYYFzhA3vB, 1BPUUNghhuwQjDDvFd3TnJz2ato5dyDLr8, 1DrCbXWfTqJbaiak2wjGUQiEo1WBzCBnof, 1GEhuEajkFXVe7vhtZqy1hRLdCaguhWBC2, 19rvCcYfSwPUSvJJKNyTyRFi5vxt6zaqJC, 1KeCBKUgQDyyMpaXhfpRi2qUvyrjcsT44o, 1Jh1miFmhTmGQvn6Zejaqg85viD4k1vVjG, 142e8SgyTLnkvwkDkNNon9jMtKY4UDvQqr, 1GoWy5yMzh3XXBiYxLU9tKCBMgibpznGio, 1GdSHQ4aE7zUD8HDqVJDEwU9dxn3LfJLMK, 1N5PXJHzJFyFfyqd32Gn9FZsVzNz8hqjqs, 1JBFFHR8tGiMgYLpnZCVG8n4cSpm591urc, 14tfS3yWL2cABhXVJZ97XRhuDXC69aWH6Y, 1N6dubqFmnyQ2qDWvi32ppVbc3kKMTYcGW
After receiving the payment, I will delete the video and you will never hear me again.
I give you 48 hours to pay.
I have a notice reading this letter, and the timer will work when you see this letter.Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.If I find that you have shared this message with someone else, the video will be immediately distributed.
Best wishes!
Furthermore, the scammers demand a payment of $780 in Bitcoin and promise not to post the video after receiving the money. However, this part in I sent you an email from your account scam is also a misleading one and you should not follow these instructions. By transferring the money to the crooks, you will lose a very big sum for nothing.
In some cases, bogus email messages such as I sent you an email from your account scam might carry additional payload attached to the message. If you find a bogus attachment, for example, a Word document, executable, JavaScript file, or any similar component clipped to the email, be aware not to open it as malicious payload might be inserted there.
Besides, if you find any links within I sent you an email from your account scam, do not take risks by opening them too. Even though receiving malware is not the main goal here but it still might happen as producing notorious various and damaging the victim's computer system might also bring great benefit to the cybercriminals and allow them to receive even more income when offering a fake money-regarding fixing solution.
I sent you an email from your account scam removal is the best option here as there is no reason for keeping the rogue email notification in your inbox or even spam section or trash. Once you clean your email box, make sure to scan your entire computer system with an anti-malware tool. System programs like FortectIntego can also give the advantage, in case some type of malware affected files or damaged system data.
Hackers manage to drop bogus emails to random users by harvesting their personal information
For a suspicious scam message to appear on your computer system, the sender needs to receive your email address somehow. Collecting information such as the user's email is possible if you have landed on a specific domain that aims to gather personally-identifiable through questionnaires or fake prize offers.
According to experts from Virusai.lt,[2] hackers can get in hold of some user-related details if the person's data has been exposed widely during some type of data leak. You might have been using some online services provided by a particular company and the company might have gotten their online page breached which might have resulted to exposure of some of your personal data, including your email address.
We urge all users to stay careful while filling in various online surveys or claiming specific rewards as most of them appear to be fake. Always be aware of what kind of people you provide personal information too and if you ever get involved in a breach, change passwords of your online accounts, emails immediately. If you are interested in checking if your email has ever been breached, go to haveibeenpwned.com and check it out there.[3]
Do not fall for I sent you an email from your account scam and eliminate it quickly

I sent you an email from your account scam virus can approach any type of user and every person needs to know how to deal with such bogus messages. Of course, you should not believe in any claims that are stated in such bogus emails as they are provided for money-collecting purposes only.
If you ever receive such a suspicious email message in your inbox or spam sections, be aware that you need to remove I sent you an email from your account scam right away as there is a risk that the bogus scam message might carry additional malware-laden payload.
If you did not succeed with the I sent you an email from your account scam removal process and some type of malicious payload has managed to invade your computer system, you should use reliable anti-malware programs. Also, employ FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes for repairing the virus damage.
Getting rid of I sent you an email from your account scam. Follow these steps
Manual removal using Safe Mode
If any type of malicious product managed to reach your computer system from the background, you can reverse bogus changes on the machine by rebooting it to Safe Mode with Networking:/GI]
[GI=method-2]Activate the System Restore feature in order to disable all suspicious processes that might be running on the background of your computer. Turn this function one with the help of these lines:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from I sent you an email from your account scam and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting spam tools
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Margaret Rouse. Email spoofing. Search Security. Tech Target.
- ^ Virusai.lt. Virusai. Spyware and security news.
- ^ Check if you have an account that has been compromised in a data breach. Have I Been Pwned.
