ICE virus (Removal Instructions) - updated Apr 2020
ICE virus Removal Guide
What is ICE virus?
ICE virus – a type of malware that prevents users from accessing their computers or phones
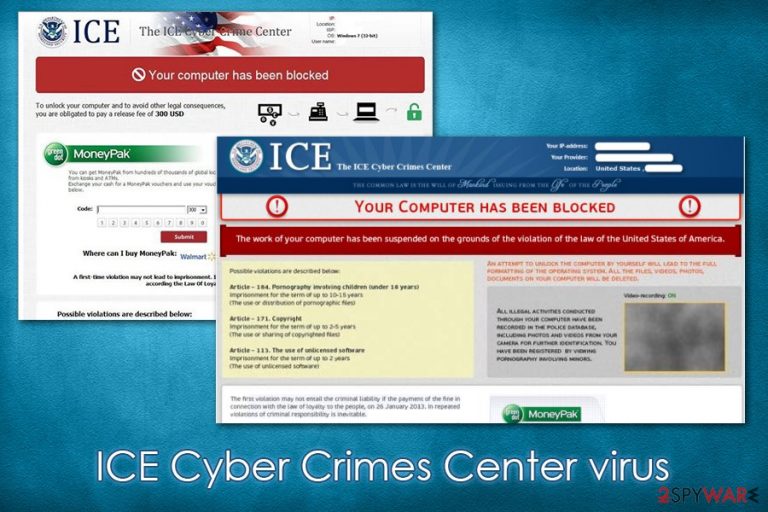
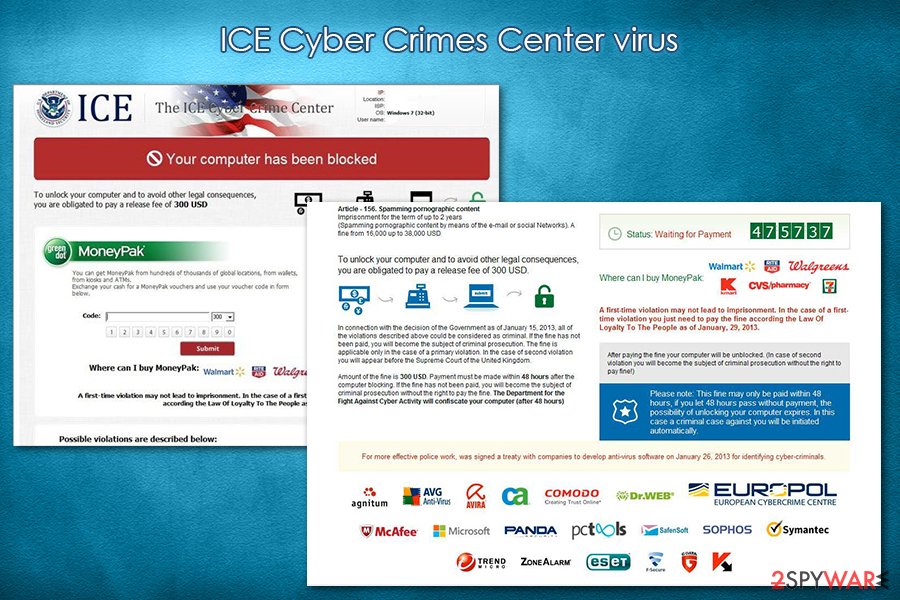
ICE virus, otherwise known as the ICE Cyber Crimes Center virus, is a computer infection that uses scare tactics in order to make victims pay the demanded sum of money to cybercriminals. There are a few variations of the scam, but most of the time, users are accused of such heinous crimes as view pornography involving children or copyright infringement, both of which could result in jail time. Since the ICE virus locks the screen and pretends to come from a federal law enforcement agency, some users are sent into panic mode immediately.
Users are asked to pay a “fine” of up to $400 via MoneyPak or MoneyGram systems, which allow threat actors to remain anonymous. When dealing with ICE Cyber Crimes Center or a similar scam, users should remember that no law enforcement agencies would lock their PC screen, regardless if they actually are guilty of some type of crime (different procedures are followed in such case). ICE virus is specifically crafted to abuse human psychology and make significant sums of money in illegal ways.
| Name | ICE virus, ICE Cyber Crimes Center virus |
| Type | Trojan, malware, ransomware |
| Malware family | FBI virus |
| Infiltration | Screenlockers can be spread in various different ways, including spam email attachments/hyperlinks, fake updates, scam messages, repacked installers, software cracks, etc. |
| Symptoms | The screen is locked and a long message (allegedly coming from law enforcement agency) is displayed; no keyboard shortcuts are operational, i.e., it is impossible to call up Task Manager or other Windows components |
| Risks | Financial loss if the ransom is paid, other malware infiltration |
| Ransom size | $400, although the demands might vary from person to person |
| Removal | To get rid of the virus, victims should access Safe Mode with Networking as explained below and then perform a full system scan with anti-malware, such as SpyHunter 5Combo Cleaner or Malwarebytes |
| System fix | Malware can sometimes irreversibly damage Windows files, preventing it from working normally again. To fix virus damage and remediate the PC, scan it with repair software FortectIntego |
While the malware might be called ransomware, it is more likely to be its predecessor, as it does not lock personal files, and the lock screen feature is removed as soon as ICE virus removal is performed. However, many users might not know how to access their computers once their screen becomes locked, although Safe Mode always bypasses the feature.
The ICE Cyber Crime Center virus gains access to computers in various ways, including:
- spam email attachments;
- fake updates;
- exploits and vulnerabilities;[1]
- software cracks;
- web injects, etc.
Note that malware not only targets Windows systems but can often be encountered on Android phones and tablets – a very typical FBI virus behavior. In most cases, users infect their portable devices when they decide to download apps from shady third-party sources.
Once inside the system, the Cyber Crime Center virus will change the way Windows operates, making it load the scam message each time the OS is booted. For that, malware alters the registry, boot sequence, and other vital files. In some cases, it might also prevent users from users System Restore function.
When it comes to the ICE Cyber Crime Center scam itself, users are hit with a lengthy text, which tries to accuse them of various crimes, such as the use of unlicensed software, illegal pornography, terrorism, cybercrimes, and much more. Threat actors also bothered to write down article numbers and punishments related to each of the alleged crimes and claim that the message is written by the Department of Homeland Security ICE Cyber Crime Center Unit.
During the infection routine, the ICE virus also hijacks a video camera if such is available – this is another trick to make users believe that the law authority is filming them. In other words, cybercriminals use all types of scare tactics to make victims deliver the alleged “fine” via shady ways. Please do not give in to ICE Cyber Crime Center scam, as you will lose your money and feed criminals' illegal business.
Unfortunately, the scare tactics sometimes work, and victims decide to pay criminals the sum of money they are asking for. However, this will not unlock their computers, as Ice virus removal tool is needed for that. There are several anti-malware solutions available that would recognize and remove Cyber Crimes Center virus from the system with no problems.
However, since the Task Manager or any other functions cannot be used due to malware functionality, the affected users should access Safe Mode with Networking as explained below and then perform a full system scan from there. In case your Windows does not operate appropriately even after malware termination, remove virus damage with the help of FortectIntego and fix your computer.
Malware can be distributed in various ways – learn to protect your computer from it
While some threat actors pick a single way to distribute malware, other groups rely on multiple attack vectors to achieve maximum profits – the latter is more common for malware-as-a-service[2] scheme-operating criminals. However, this does not make any difference for regular users, as their computers get in trouble if they do not apply the correct measures to protect them from malware in the first place.
Security experts from novirus.uk[3] have listed the most common screen-locking malware distribution methods. Here they are, and also tips on how to avoid the infection:
- Never open spam email attachments that ask you to run macro function (“Allow Content”);
- Scan the attachment with anti-malware software/ upload to Virus Total if you are not sure;
- Hover the mouse over a suspicious hyperlink on a suspicious website or an email – this will allow you to view the real URL you will be redirected to in the corner of the screen;
- Employ reputable anti-malware software and keep it updated;
- Update Windows and all other installed programs as soon as security patches come out; set the updates to be applied automatically within application settings;
- Never download high-risk applications, such as software cracks or pirated program installers;
- Use third-party tools like ad-blockers for safe web browsing.
Remove ICE virus from your machine
Even those who instantly detect deception might be baffled when it comes to ICE virus removal due to screen locking functionality. Therefore, the only way to bypass this feature is to access Safe Mode with Networking as explained below – Windows is loaded with an only a minimum number of drivers and other resources that are necessary for the boot to be successful. This temporarily disables malware functionality and removes the locks screen, although victims need to remove ICE Cyber Crimes Center virus in order to regain access to normal Windows functions once in normal mode again.
To remove ICE virus, you should use a reputable anti-malware tool such as SpyHunter 5Combo Cleaner or Malwarebytes – download it and place it into a bootable USB drive. Then, access Safe Mode as explained below, boot from the USB, and perform a full system scan. Note that users infected with ransomware viruses are allowed to access other accounts on their Windows systems. If one such account has administrator rights, you should be capable of launching the anti-malware program.
Getting rid of ICE virus. Follow these steps
Manual removal using Safe Mode
To bypass ICE virus functionality and remove the lock screen, access Safe Mode with Networking as explained below:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove ICE using System Restore
You can also attempt to use System Restore to get rid of the malware:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of ICE. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from ICE and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Vulnerabilities and Exploits. ENISA. European Union Agency for Cybersecurity.
- ^ Marcus Moreno. Malware as a Service: As Easy As It Gets. Webroot. Security blog.
- ^ Novirus. Novirus. Cybersecurity advice and malware insights.







