Installsophisticatedsupertheproduct.vip ads (fake) - Free Guide
Installsophisticatedsupertheproduct.vip ads Removal Guide
What is Installsophisticatedsupertheproduct.vip ads?
Installsophisticatedsupertheproduct.vip ads can be dangerous: here's what they are

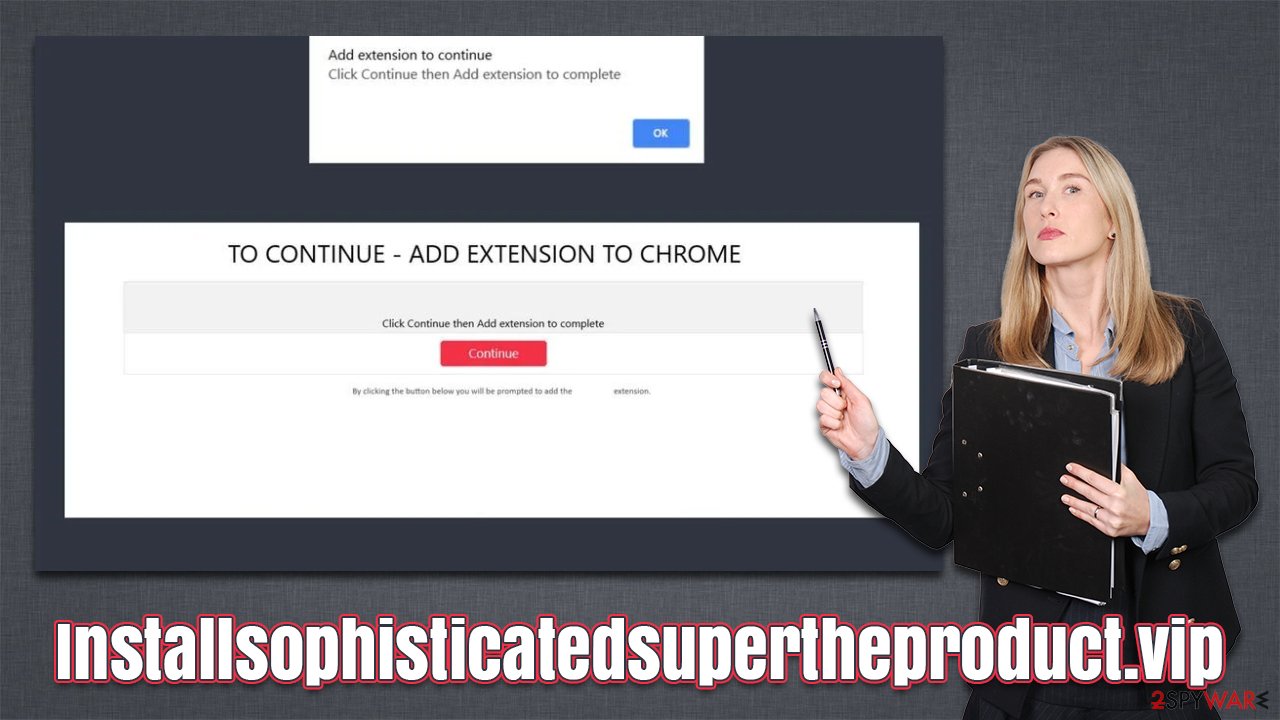
Installsophisticatedsupertheproduct.vip is a potentially dangerous website you may encounter by accident while browsing the web on Google Chrome, Mozilla Firefox, MS Edge, or another browser. The site's main goal is to convince people that they should install the promoted application (usually a browser extension) that would hijack the homepage, replace it with an alternative provider, and promote ads at the top of the search results.
If you are suffering from continuous Installsophisticatedsupertheproduct.vip redirects, there is a chance that adware is installed on your system. This type of software is usually installed accidentally, so many people are not even aware it is running in the background. Those affected may experience an excessive amount of ads such as pop-ups, banners, deals, offers, in-text links, etc. We explain how to get rid of the unwanted software thoroughly in this article below.
| Name | Installsophisticatedsupertheproduct.vip |
| Type | Redirect, scam, phishing, adware |
| Distribution | Software bundles, malicious websites |
| Symptoms | Shows fake ads and promotes potentially unwanted applications |
| Risks | Installation of potentially unwanted software, such as browser hijackers; redirects can also lead to other malicious websites, resulting in monetary loss or personal data disclosure to unknown parties |
| Removal | Do not interact with scam content; if you did, uninstall the unwanted browser extension and check your system for other infections with SpyHunter 5Combo Cleaner anti-malware |
| Other steps | Employ FortectIntego to clean your system from PUP leftover files and fix any damage done by the virus |
Online fraud is something that users came across at least once or twice while browsing the web on Google Chrome, Mozilla Firefox, MS Edge, or another web browser. There are different scam messages with different goals, although none of the phishing messages benefit the user – it's the scammers behind it that get some type of payoff, which is usually financial.
Installsophisticatedsupertheproduct.vip is yet another website that seeks to profit from less experienced users in the IT field – its main goal is to make people download potentially unwanted software. It is not the first or the last website which uses such techniques – we have previously discussed Highpotencysoftware.com, Victorysweepstakes.com, Shield-fordesktop.com, and many others.
How you end up on malicious websites
As mentioned, people do not intentionally wander off to scam websites, although some users still risk it and visit torrents, illegal video converters, video streaming, and similar dangerous sites. These places are the very first reason why they end up on deceptive websites such as Installsophisticatedsupertheproduct.vip – they are filled with booby-trapped links and even malicious scripts[1] that would take users away from their destination.
The unexpected redirect may add to the surprise of those who didn't expect it, consequently adding to one's confusion. In other cases, people may simply not think the message through: they are then more susceptible to being scammed, and that's precisely what crooks are trying to abuse.
Adware could also be one of the reasons why users get redirected to suspicious websites. This potentially unwanted software s usually installed with freeware or via deceptive links/fake messages, so many people don't know they have it installed on their systems. Below you will find the instructions on how to get rid of it effectively.
Adware removal and remediation tips
It is very important not to interact with any links, buttons, and other components of the scam page, as you could immediately be redirected to other malicious places, or a download of a malicious executable could be initiated automatically.
Under some circumstances, malware could also be installed automatically – this happens when software vulnerabilities[2] are present on the user's device. To mitigate this, always make sure your system and apps installed on it are fully patched with the latest security updates. Even if you did not download and install anything, we still recommend you check the system for adware or other infections as we explain in the next section.
Possibly the most important security measure is security software – it can not only prevent the installation of potentially unwanted programs and malware but also remove adware that causes Installsophisticatedsupertheproduct.vip redirects in the first place. Of course, you can always look for unwanted apps yourself, and we recommend starting from extensions.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the window's top-right).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Although this rarely happens, the adware can also be installed as a program that runs on the system level. For example, media players or driver updaters might fail to provide the functionality they advertise and instead start initiating intrusive ads and redirecting to suspicious websites. If you have noticed pop-ups, deals, banners, offers, browser redirects, and other infection symptoms after installation of one of these apps, you should check the installed program list:
Windows
- Enter Control Panel into the Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till the uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Mac
Moving the unwanted application to Trash is not enough, as adware and malware commonly use persistence mechanics. Therefore, you might have to clean the leftover files as follows:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any suspicious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
Adware uses cookies[3] and other trackers to harvest various data about users. IP addresses, search queries, clicked links, visited websites, and similar information can be collected passively via these trackers. The data collection may continue even if adware or other PUP is removed.
Therefore, we strongly recommend cleaning web browser caches after the elimination of adware and other malicious programs. FortectIntego is the quickest way to get rid of browser caches quickly and effectively. The app can also be used to repair any damage that could have been caused by a computer infection.
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Andra Zahara. JavaScript Malware – a Growing Trend Explained for Everyday Users. Heimdal. Security blog.
- ^ Thomas Holt. What Are Software Vulnerabilities, and Why Are There So Many of Them?. Scientific American. Science Magazine.
- ^ HTTP cookie. Wikipedia. The free encyclopedia.







