Shield-fordesktop.com ads (scam) - Free Guide
Shield-fordesktop.com ads Removal Guide
What is Shield-fordesktop.com ads?
Shield-fordesktop.com is a malicious website that hosts various scams
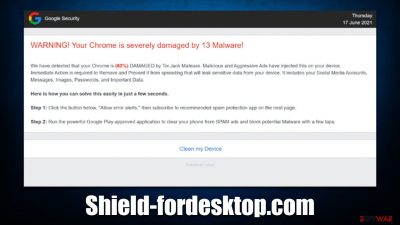
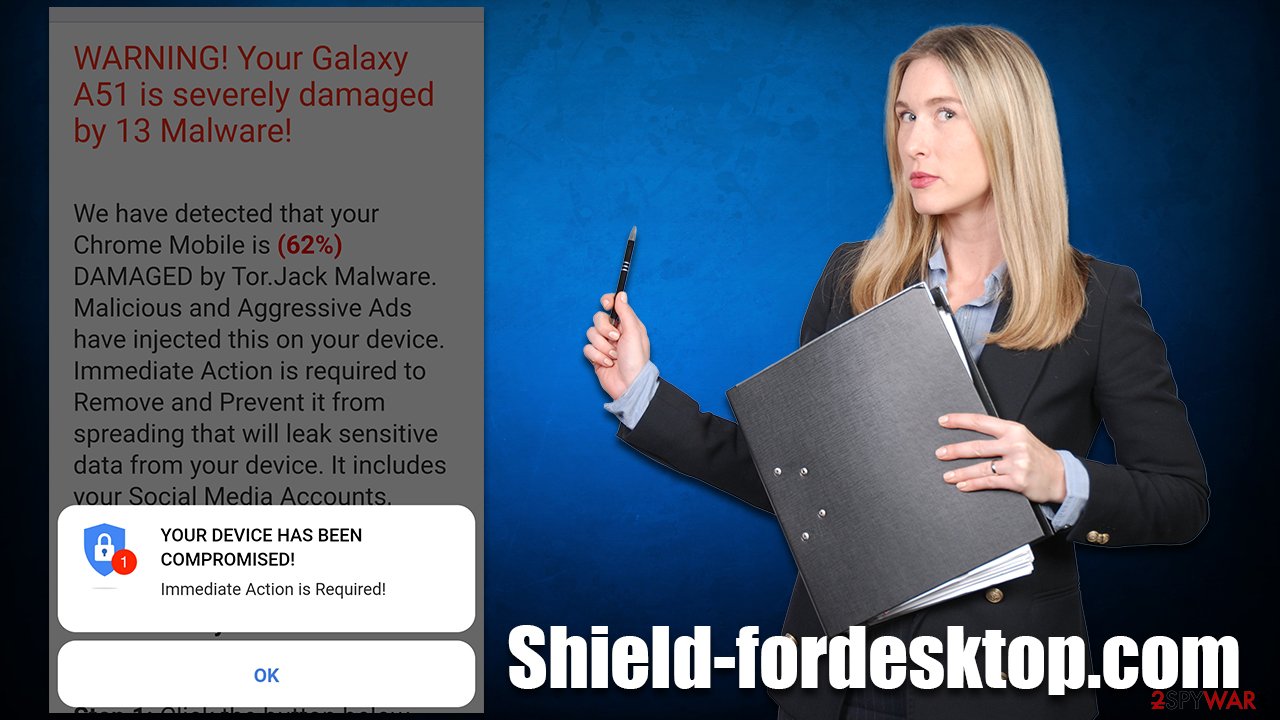
Shield-fordesktop.com is just another website created by scammers. It promotes a widely prevalent scam campaign known as “Your Chrome is severely damaged by 13 malware,” where crooks show fake Tor.Jack malware infection messages are meant to frighten users and completely mislead them about their machine's state of security.
The main goal of crooks is to use the Shield-fordesktop.com website to benefit from the affiliate program.[1] Scam schemes can also sometimes lead to malware downloads, where specially crafted spoofing websites are presented as legitimate ones. Regardless of the download content, you should never interact with any components of the scam.
In addition to the scam content, Shield-fordesktop.com would also ask users to enable push notifications. Those who intentionally or accidentally click the “Allow” button within the notification prompt would permit notifications to be shown directly on the desktops at any time, as long as the browser is running. We explain how to deal with Shield-fordesktop.com ads as well – you have to access the browser settings section and block its access to you.
| Name | Shield-fordesktop.com |
| Type | Scam, phishing, fraud, fake alert |
| Operation | Claims that Chrome browser has been damaged by malware. It then asks users to download a fake security tool to remove it |
| Risks | Fake messages usually aim for users to download potentially unwanted or malicious programs, steal their personal information or trick them into subscribing to useless services |
| Removal | To get rid of unwanted apps manually, you can follow our removal guide below. If the unwanted ads and other disruptive behavior do not stop, you should scan your computer with SpyHunter 5Combo Cleaner security software and delete all threats automatically |
| Other tips | After removal of adware and other PUPs, you should take your time to clean your browser from cookies, and other trackers – FortectIntego can help you with that |
The fake message
Malware infection messages are not new when it comes to online fraud. Fear is a very powerful emotion and, in conjunction with a lack of IT knowledge, vulnerable groups become easily manipulated by these scams. This is why it is important not to jump to conclusions immediately and research the website or a message shown somewhere on the web.
In the case of Shield-fordesktop.com, the scam attempts to mimic Google – a well-known entity for everybody who ever used the internet. By imitating and presenting itself as a popular brand, the site tries to disguise its nature. Here's the message you might expect to see upon entry:
WARNING! Your Chrome is severely damaged by 13 Malware!
We have detected that your Chrome is (62%) DAMAGED by Tor.Jack Malware. Malicious and Aggressive Ads have injected this on your device.
Immediate Action is required to Remove and Prevent it from spreading that will leak sensitive data from your device. It includes your Social Media Accounts, Messages, Images, Passwords, and Important Data.Here is how you can solve this easily in just a few seconds.
Step 1: Click the button below, “Allow error alerts,” then subscribe to recommended spam protection app on the next page.
Step 2: Run the powerful Google Play-approved application to clear your phone from SPAM ads and block potential Malware with a few taps.
In reality, this phishing[2] message was not written by Google. Also, no website is capable of detecting whether or not malware is installed on your system – only a dedicated anti-malware software installed on the system can do that. When in doubt, always scan the system with a reputable security tool instead of trusting messages on random sites online.
How to remove Shield-fordesktop.com redirects?
The first and most important step to take when dealing with a scam website is not to interact with it – there could be malicious links that would redirect to other dangerous sites. Scams are designed for a few different purposes, including personal information theft that can be later converted to monetary benefits, malware installation that profits the crooks behind it, or direct financial losses due to fake services or goods.
If you have disclosed your personal information, be aware that crooks might contact you via email, phone, or other means and convince you to give them money in one way or another. If you have installed software from suspicious sources, you should immediately perform a full system scan with SpyHunter 5Combo Cleaner, Malwarebytes, or another powerful anti-malware software.
The below instructions should help you to remove adware that could cause Shield-fordesktop.com redirects in the first place. Keep in mind that the message on the scam site is fake, and has nothing to do with adware that might be lurking on your system.
Uninstall programs installed on the system
As a first step, you should check the list of the installed programs on your system. It is important to note that adware is rarely installed in such a way nowadays (potentially unwanted applications are usually spread as browser extensions), although some media players, PDF converters, system optimizers, and similar apps are known to also show intrusive ads.
Windows
- Enter Control Panel into the Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till the uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Mac
Besides moving the unwanted app into Trash, removing adware might require a few more steps. Adware is known for inserting additional files that might cause the infection to resurface, so we recommend removing them too.
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- Look for any dubious entries in the Application Support folder and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
Uninstall suspicious extensions and clear caches
The next step that should finish the process and stop all the unwanted activity is to clean your browsers thoroughly. Cookies, for example, might in some cases be hijacked[3] by cybercriminals, which would allow them to steal your sessions, meaning they could get access to your personal accounts. Therefore, as a precautionary measure, we recommend cleaning browser caches from time to time.
Cookies are also used by third parties, including adware authors to track your information, including visited websites, clicked links, ISP, and other data. You can remove these caches with the help of the FortectIntego tool or refer to the instructions below. Don't forget to remove unwanted extensions first:
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Clean web data on Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
Clean web data on Firefox:
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Clean web data on MS Edge:
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Clean Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
Stop intrusive push notifications
As mentioned at the start of the article, users who access the Shield-fordesktop.com site are asked to enable push notifications. Those who accept them would later be exposed to intrusive pop-ups, showing up directly on their screens. Luckily, it is very easy to get rid of them via browser settings.
Getting rid of Shield-fordesktop.com ads. Follow these steps
Stop browser notifications
Remove unwanted notifications from Google Chrome (desktop):
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate Privacy and security section and pick Site Settings > Notifications.

- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Remove unwanted notifications from Google Chrome (Android):
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).

Remove unwanted notifications from Mozilla Firefox:
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.

- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

Remove unwanted notifications from Safari:
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

Remove unwanted notifications from MS Edge:
- Open Microsoft Edge, and click the Settings and more button (three horizontal dots) at the top-right of the window.
- Select Settings and then go to Advanced.
- Under Website permissions, pick Manage permissions and select the URL in question.

- Toggle the switch to the left to turn notifications off on Microsoft Edge.

Remove unwanted notifications from MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Remove unwanted notifications from Internet Explorer:
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
- Locate web address in question under Allowed sites and pick Remove.

How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Jake Frankenfield. Affiliate Marketing. Investopedia. Source of financial content on the web.
- ^ Phishing attacks. Imperva. Application and data security.
- ^ Allie Johnson. Session hijacking: What is a session hijacking and how does it work?. Norton. Security research blog.




















