Iplogger.org (Virus Removal Guide) - Free Instructions
Iplogger.org Removal Guide
What is Iplogger.org?
Iplogger.org is a misleading URL that may be misused by malware for tracking users' IP addresses
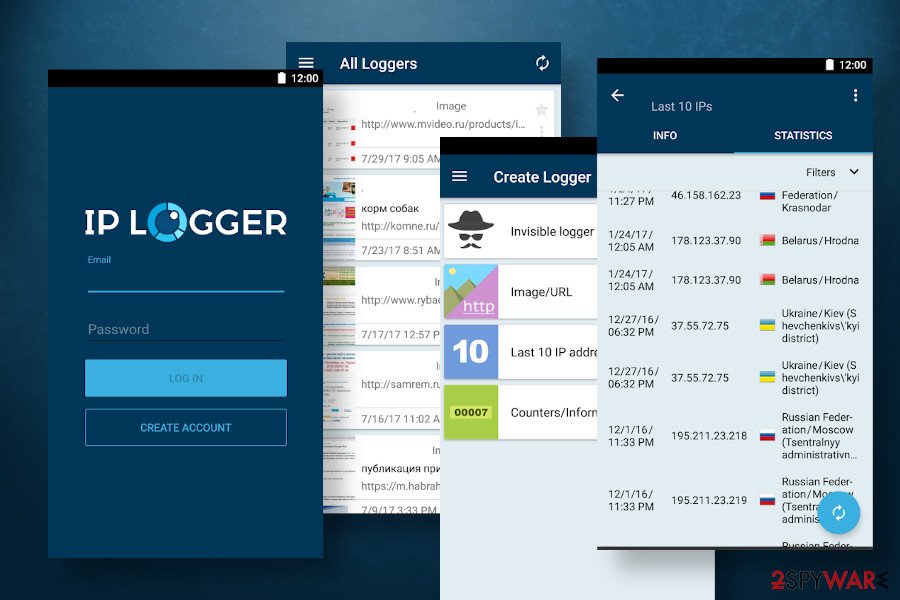
Iplogger.org or Iplogger.com is a website that allows users to track people's IP addresses by sharing shortened links with them. In addition, people can download an app IP LOGGER for free on Google Play Store and other sources for shortening the URLs and quick access to full logs and statistics for the clicks on those links. While the service is handy for webmasters and bloggers, cybersecurity experts warn that unexpected web browser's redirects to Iplogger.org domain are not a good sign and can mean a trojan infection.
Based on research results, the Iplogger.org site can be automatically launched by Trojan:Win32/Hynamer.C!ml, Trojan.Agent.Wacatac, and Logger.exe trojans aiming to track users' web browsing activities and harvest device IDs, Internet Service Provider (ISP), IP address, location, date, and time of website visits, and similar. Thus, suspicious browser's redirects or other signs of unusual behavior should not be ignored, especially by those people who are not using the IP LOGGER app.
| Name | Iplogger.org |
| Also known as | Iplogger.com or IP LOGGER app |
| Classification | Redirect virus / Trojan |
| Symptoms | The main symptom – random Iplogger.org redirects Slow web browser's performance Intrusive ads on legitimate sites |
| Main dangers | The direct access to this URL does not pose a risk of exposing personally identifiable data. However, experts warn that the domain may be involved in data tracking activities by unreliable third parties who seek to collect users' browsing activities |
| Removal | The URL address can be blocked by the AV engine adding it to the sites' blacklist. However, if it is managed by a trojan virus, it's important to remove the mother application by running a scan with a robust anti-malware. |
| Fixing the damage | Malware can attack the system by injecting entries into the Registry, Temp, or User folders. Therefore, a full scan with FortectIntego is recommended to ensure proper optimization |
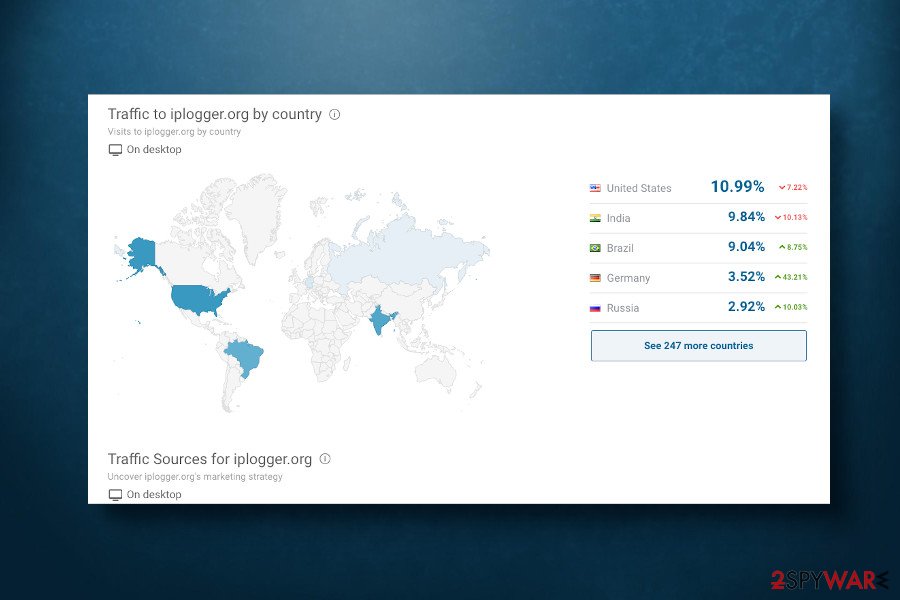
Iplogger.org URL shortener site is regularly accessed by thousands of users. The app for Windows and Androids is also popular, especially in the USA, India, Brazil, Germany, and Russia[1]. It's important to stress the fact that the service this site provides and the app that it promotes are legitimate and useful for admins that want to monitor detailed visitors' logs and statistics.
However, there are many dissatisfied users who report[2] the Iplogger.com virus for generating wrong IP addresses, false locations, showing the same result, or displaying an error saying “Check your internet connection.” The majority of users believe this app to be fake.
While its performance is in question, calling the URL as an Iplogger.org virus has a clear ground. Cybersecurity experts have noticed that this domain is quite frequently misused by criminals who seek to harvest IP addresses, locations, and other browser-based data without users' permission. The main signal indicating that the IP LOGGER related trojan has infected the machine – random redirects to this site or other related domains, including:
- sslupdate1.top
- iplogger.org
- iplogger.com/1kfvV6
- apps.identrust.com
- isrg.trustid.ocsp.identrust.com
- ocsp.int-x3.letsencrypt.org
- sslupdate2.top
In addition, this site may be involved in an active IP tracking, storing, and using itself. During the Coronavirus pandemic, many coronavirus-related websites have been found including suspicious scripts that belong to the iplogger.org domain. According to the researchers from Unit 42[3], the obfuscated script on sites like coronavirus-game.ru were used for dropping the invisible iframe that automatically sends visitor's IP addresses to the host iplogger service.
Iplogger.org accomplice in a ransomware attack
In the middle of March 2020, Trend Micro[4] team reported a new strain of Paradise ransomware that has been actively spreading via Internet Query Files. Although the payload of the ransomware has been dispersed in malicious spam email attachments, upon the launch it misuses the IQY files to make queries on the Internet to download Excel formulas allowing to misuse Windows PowerShell and CMD.
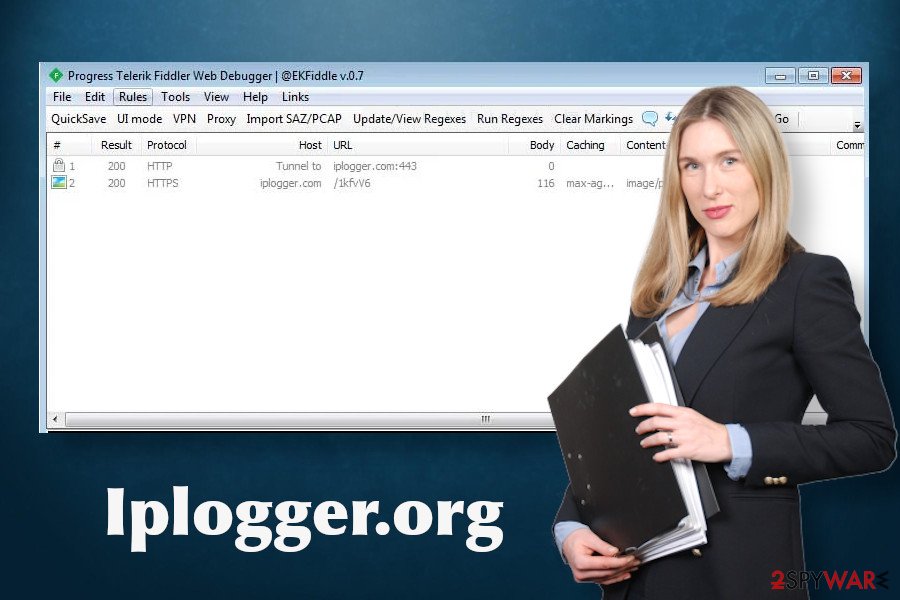
So how the Iplogger.org is related to this cyber attack? A close analysis of the Paradise ransomware launch has shown that this domain is an active accomplice. It's one of the URLs (hxxps://iplogger[.]org/1AsWy7) that the ransomware opens to establish a connection with the C2C server. That's yet another worrying fact proving that the site is often used by criminals.
AnyRun[5] analysis also detects the Iplogger.org redirects as malicious as the site is capable of initiating certain activities behind users' backs. It is capable of:
- launched itself
- change internet zones settings
- change settings of System certificates
- read internet explorer settings
- adds/modifies Windows certificates
- create files in the user directory (FlashUtil32_26_0_0_131_ActiveX.exe)
- reads Internet Cache Settings
- reads settings of System Certificates, and more
In general, if the web browser keeps redirecting your web browser to this URL, you should start worrying about the Iplogger.org virus removal. If you are using the IP LOGGER app, then it may be the culprit of the unwanted redirects. If nevertheless, the app is not installed, we recommend scanning the machine with a powerful anti-virus to delete trojan or other related malware.
You may not be permitted to remove Iplogger.org from your web browser easily since trojans may be blocking the processes of security software. To disable infringing processes, reboot Windows into Safe Mode with Networking. Once the machine is virus-free, optimize its performance with FortectIntego tool.
Malware prefers unpatched system and reckless PC users
Outdated and unprotected software and OS is a target for malware developers. Keep in mind that dangerous programs will never ask for permission to get a place on the system. Criminals are using various tricksters to make people download trojans, ransomware, and other malicious programs.
For this purpose, people should mind the three steps rule – update the system, use professional security software, and be careful on the Internet. Windows users can take advantage of the automatic update feature, which ensures a regular updating of software, OS components, and security systems, thus increasing the system's resistance to malware infections. However, we strongly recommend checking the update history regularly to ensure that all updates have successfully been installed.
Nevertheless, NoVirus.uk[6] researchers claim that even the well-patched and updated system can be attacked by viruses if the user behaves recklessly on the Internet. Downloading pirated software, cracks, keygens, visits to adult sites, or other untrustworthy domains always pose a risk of being exposed to dangerous content. Email messages should also be treated with carefulness since spam is the main mediator between malicious programs and PCs. Thus, it's important to think twice before clicking on any online content.
Learn how to remove Iplogger.org related malware from the system
Iplogger.org can be used interchangeably with Iplogger.com domain. The two are identical. If your machine exhibits the symptoms of potential infection because of redirects via the mentioned domain servers, we recommend scanning it with SpyHunter 5Combo Cleaner, Malwarebytes or another professional security tool immediately. As we have pointed out, these sites are not only related to the IP LOGGER application. They can be misused by trojans or ransomware viruses, so try to forestall future problems by deleting the virus as soon as it starts running.
In case you cannot remove Iplogger.org virus because such a virus is not detected by your anti-virus tool, there might be that the URL is being launched by other potentially unwanted applications or altered web browser settings. In this case, check the machine for PUPs, delete all of them if detected, and then blacklist the domain within AV settings, so that redirects to it would automatically be blocked.
Getting rid of Iplogger.org. Follow these steps
Manual removal using Safe Mode
If your machine is infected by Iplogger.org trojan. but you can't uninstall it because the AV scanner is blocked, we recommend you to restart the machine into Safe Mode to bypass restrictions.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Iplogger.org using System Restore
In case Safe Mode failed to help, try to uninstall Iplogger.org related apps by restoring the system to the state it was before the attack.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Iplogger.org. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Iplogger.org and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ iplogger.org domain. SimilarWeb. Global multi-device market intelligence.
- ^ IPLOGGER URL Shortener. Google Play Store. Official app distributor.
- ^ Janos Szurdi, Zhanhao Chen, Oleksii Starov, Adrian McCabe and Ruian Duan. Studying How Cybercriminals Prey on the COVID-19 Pandemic. Unit 42. Global threat intelligence team.
- ^ New Variant of Paradise Ransomware Spreads Through IQY Files. Trend Micro. Cyber security experts.
- ^ General Info on iplogger.org. AnyRun. Interactive malware hunting service.
- ^ SECURITY AND SPYWARE NEWS. NoVirus. Virus and spyware news.







