Kkll ransomware (Virus Removal Instructions) - Decryption Steps Included
Kkll virus Removal Guide
What is Kkll ransomware?
Kkll ransomware is an intricate piece of software that restrict people from accessing their personal files and demands them to pay for a decryption key
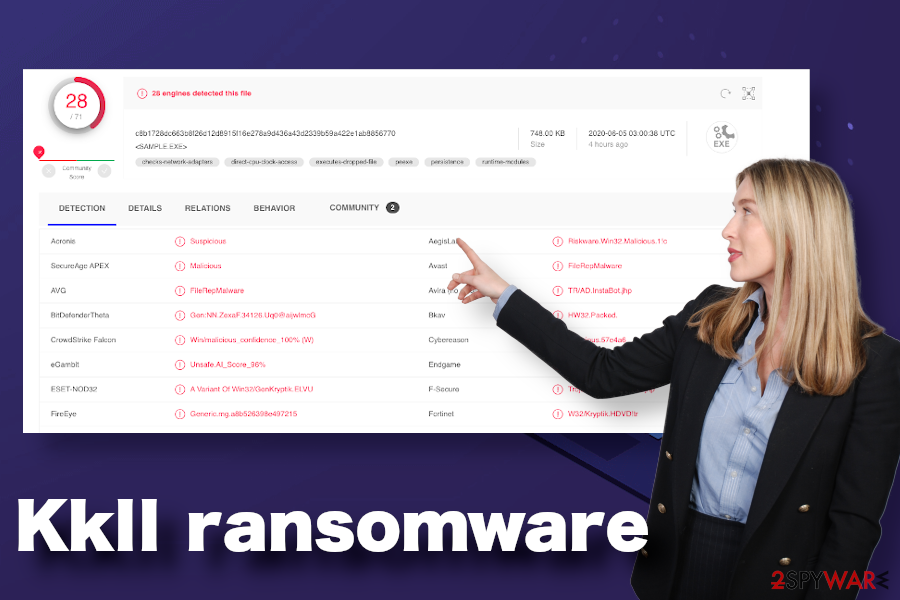
Kkll ransomware is a malicious piece of software that has been developed by the managers of the STOP/Djvu ransomware. It has been discovered in the first half of June 2020 and attributed to the group of the biggest ransomware family Djvu alongside Zipe, Nlah, Pezi, and many others.
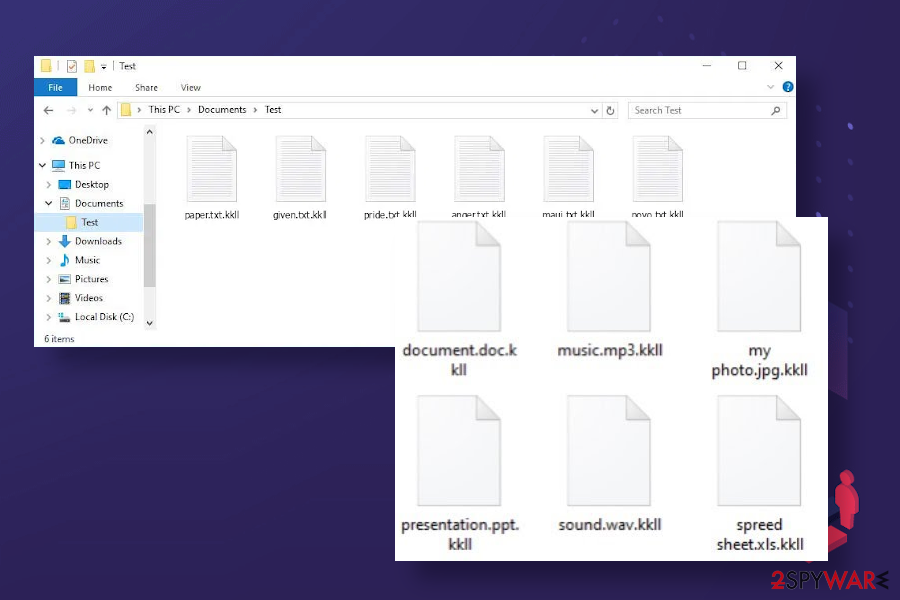
It targets all non-system files using a sophisticated RSA encryption[1] algorithm and appends .kkll file extension to pictures, videos, photos, images, documents, databases, and other data. This file-locking virus demands its victims to pay nearly $1000 ransom in Bitcoins and, since people's access to personal files is completely restricted, many falls for paying.
However, paying the ransom is not recommended. Although Kkll ransomware and other Djvu versions launched after August 2019 since they are encrypted using unique online keys stored on the C$C server. Nevertheless, even so, there's a high probability that cybersecurity researchers will find a flaw in the encryption and release a method to recover .kkll files.
| Name | Kkll |
| Classification | Ransomware virus |
| Geneology | 230th variant of the DJVU family |
| Cipher | The old Djvu used the AES cipher to lock files. The versions launched after August 2019 switched to RAS encryption model |
| File extension | .kkll extension is used to differentiate locked files |
| Ransom note | The virus generates a typical _readme.txt note. It appears on every folder where encrypted data is stored, as well as the desktop |
| Contacts | helpmanager@mail.ch and restoremanager@airmail.cc |
| Size of the redemption | $490/$980 in BTC depending on the time the victim responds |
| File recovery | It the virus is using online keys, removal of .kkll extension from files without paying the ransom or using backups of files is not possible. However, there's a chance to retrieve at least some pieces of locked files using alternative methods (listed at the end of the post). In case attackers rely on offline ID, the Emsisoft's decryptor might help. |
| Virus removal | The only way to remove the ransomware is to run a thorough system scan with a professional anti-virus program |
| Windows recovery | Ransomware negatively affects Windows OS performance as it compromises core files, and injects additional components that can trigger reboots, lags, crashes, and similar programs. Such performance issues can be fixed with a repair tool FortectIntego |
Kkll ransomware virus belongs to the category of cyber infections that cause the biggest losses and system problems. If it manages to infiltrate the machine, it initiates aggressive Windows setting changes and encrypts all personal files stored on all non-system locations.
Users are left with no choice except to pay the ransom or say goodbye to the files infected with .kkll file extension virus. This, 230th variant of the Djvu takes advantage of the sophisticated RSA encryption mechanism, which generates unique IDs for each victim, making a previously fully functional STOPDecrypter tool useless. This software has been launched by Emsisoft to help Djvu ransomware victims recover files that were locked by old Djvu versions launched prior to August 2019.
The authors of the Kkll ransomware virus are distributing this malicious software as an obfuscated payload of the pirated programs and software cracks/keygens[2]. Millions of people are not fond of paying the money for software licenses, so they risk downloading illegal software (Adobe Photoshop CS6 Extended, GTA 3, Adobe Acrobat XI Pro, Camtasia 9 + Serial Keys, etc.) on P2P sharing sites or shardy third-party download websites. When installing hacked software on the system, the ransomware drops the payload and the encryption procedure.
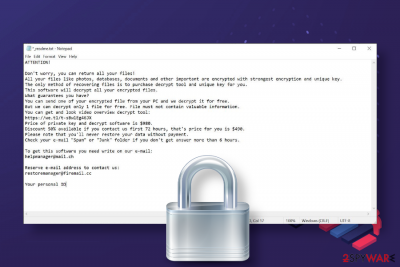
Upon successful establishment process, Kkll ransomware virus locks all files and drops a redemption note _readme.txt on the desktop and other folders that contain encrypted files. This note soothes the victims in the first place stating the fact that files can be returned. However, there's one important condition – the payment for criminals is required. The sequence of actions that criminals expect victims to do are the following:
- Upon reading the email, the victim writes an email message and sends it to helpmanager@mail.ch or restoremanager@airmail.cc email address.
- When ransomware managers respond, the victim sends the unique ID number to them and one encrypted file for test decryption.
- After that, criminals indicate the final price for the Kkll ransomware virus decryptor ($490 or $980).
- The victim purchases Bitcoins and transfers the payment via the Bitcoin wallet.
ATTENTION!
Don't worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.You can get and look video overview decrypt tool:
https://we.tl/t-WJa63R98Ku
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hours.
To get this software you need write on our e-mail:
helpmanager@mail.ch
Reserve e-mail address to contact us:
restoremanager@firemail.cc
Your personal ID:
XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
If you got a notification provided above, the first thing we recommend you do is remove Kkll ransomware virus completely. This malicious software initiates many changes on a target system leaving it more vulnerable and unstable. Therefore, it's important to restore Windows stability and ensure protection without a delay.
Kkll ransomware removal can be initiated with a professional anti-virus program. In many cases, Djvu ransomware variants download AzoRULT and other trojans that steadily harvest personal data and transmits it to remote servers. Thus, a scan with programs like SpyHunter 5Combo Cleaner or Malwarebytes in Safe Mode is needed.
.kkll file extension removal is possible with specific decryption software only
It's important to differentiate the removal process of the ransomware and the recovery of the .kkll extension files. The scan with AV engine and complete elimination of malicious ransomware files won't help you to restore the pictures, documents, and other files.
The data locked by .kkll file extension virus can be decrypted by paying the criminals the ransom demand (up to $980). However, there's no guarantee that criminals will provide you with a fully working decryption key, though Djvu victims claim that criminals behind this infamous virus were quite polite and provided a decryptor immediately.
Unfortunately, the Kkll ransomware is the newer variant of the STOP/Djvu, so expecting that its victims will have online IDs is very low. The new strains of this virus family are using offline keys, meaning that the virus is not establishing contact with C$C servers and cybersecurity experts are unable to crack them.
Anyway, we do not recommend paying the criminals for .kkll files. Instead of that, make the backups of the encrypted data using an external hard drive or USB flash drive and then give third-party recovery programs a try. Our technicians have tested several methods that may successfully decipher locked files.
At the end of this article, you can find all methods for removing .kkll extension from personal files. First of all, try Data Recovery Pro, Shadow Explorer, or System Restore options. Step-by-step recovery methods are listed at the end of this post.
Pirated software downloads are not only illegal but can also cause the loss of personal files
While dissemination methods of some Djvu versions have been disclosed by cybersecurity experts, the techniques used to distribute members of this family are unknown. In some rare cases, victims share their experience and suspicions when they might have got the infection. According to reports on Reddit, it turns out that the biggest chance of getting ransomware infection is to download pirated software, cracks, and keygens.
Although most people know that cracking the license of paid software, as well as downloading pirated software is an illegal activity, they disregard this fact. However, at the same time, they risk getting malicious file-encrypting viruses or trojans that may lead to bigger expenses than paying the penalty for breaking the law.
However, statistically, over 50% of ransomware viruses are installed on machines via malicious spam email attachments. People are represented with .PDF, .ZIP and other attachments within fake email messages that mimic various organizations, forwarding companies, couriers, business, or governmental institutions. Therefore, careful inspection of the inbox can also help people stay away from file encryption.
Remove Kkll ransomware virus to restore the system's performance and security
Kkll virus targets computers that run Windows OS and can attack both 32-bit and 64-bit versions. Upon infiltration, it places malicious files in %AppData% or %Temp% folder and then starts implementing encryption procedures. Additionally, it runs a command via an Elevated PowerShell to delete Shadow Volume Copies.
At this point, this threat makes the .kkll file extension removal impossible. Therefore, the solution in this situation – a quick elimination of the ransomware to protect the machine from backdoor access of trojans and crashes due to malicious ransomware processes controlling the machine.
To remove Kkll ransomware from the machine, restart it to Safe Mode with Networking and open the AV tool. You can try to launch the security software, for example, SpyHunter 5Combo Cleaner in a regular Windows mode, though it's very likely that the ransomware will be actively blocking security processes.
NOTE: before Kkll ransomware removal, novirus.uk[3] experts recommend preparing a USB flash drive or hard drive to back up the .kkll files on it. This way, you'll prevent a permanent file loss during the elimination procedure. Then initiate a full ransomware elimination and follow the recovery guidance submitted below. Besides, make sure to perform Windows recovery with the FortectIntego repair software.
Getting rid of Kkll virus. Follow these steps
Manual removal using Safe Mode
Those who've been hit by Kkll virus should remove the ransomware without a delay. For this purpose, you have to restart the machine into Safe Mode with Networking as explained below.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Kkll using System Restore
System Restore is the feature that may help to bring the machine back to the state before the ransomware attack
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Kkll. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Kkll from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.The elimination of the ransomware does not mean the recovery of .kkll files. Nevertheless, there are several alternative data recovery methods that can retrieve the most valuable entries.
If your files are encrypted by Kkll, you can use several methods to restore them:
Use the Data Recovery Pro to remove .kkll file extension virus from personal files
Give third-party programs a try in the recovery of ransomware encrypted files
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Kkll ransomware;
- Restore them.
Windows Previous Versions feature is an option that can work
This method may work for those who have the System Restore function activated.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
The Shadow Explorer software may help
Experts claim that the Kkll ransomware virus removes Shadow Volume Copies of locked data. However, you can only check that by trying to recover at least one file.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
There is no Kkll ransomware decryptor
The Kkll virus is the newer Djvu variant, meaning that each victim has to get a unique ID, which is generated online. Therefore, the STOPdecrypted provided by Emsisoft won't work in this case,
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Kkll and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Josh Lake. What is RSA encryption and how does it work?. Comparitech. IT news site.
- ^ Bradley Barth. Downloads of cracked software distribute ransomware via adware bundles. SC Media. Information security news.
- ^ Security and Spyware News. NoVirus. Virus and spyware news.





















