Nlah ransomware (Virus Removal Instructions) - Jun 2020 update
Nlah virus Removal Guide
What is Nlah ransomware?
Nlah ransomware is a sophisticated file encrypting malware that asks for up to $980 for data redemption
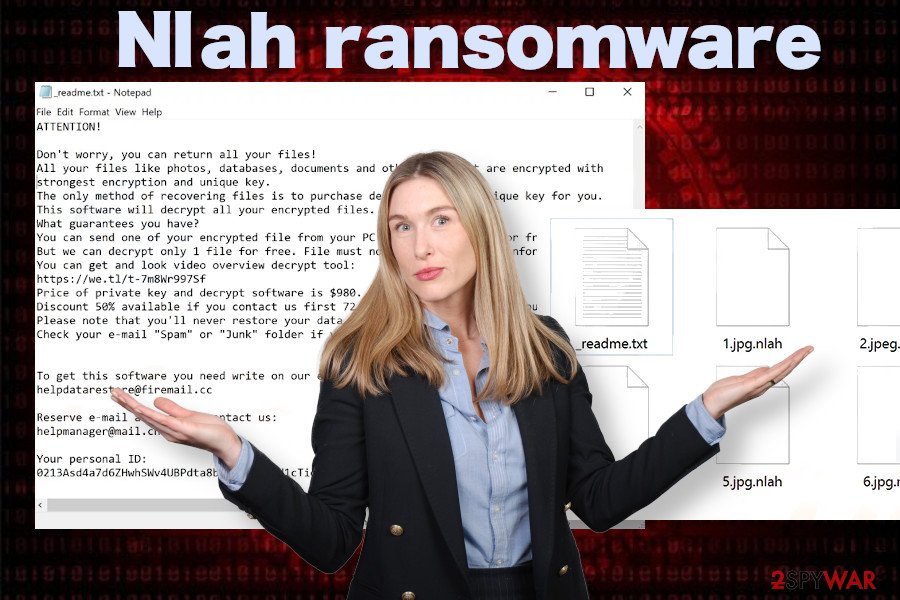
Nlah ransomware, first discovered by Michael Gillespie[1], is the latest family member of the Djvu ransomware family, which is positioned 229th in the list. Just like its forerunner, it uses a unique RSA algorithm to lock data on the host PC, although it uses a different extension – .nlah – to manifest the encryption. Although Emsisoft security research team developed a fully-functional Djvu decryption software, it can only decrypt files encrypted by Djvu variants launched before August 2019. Nonetheless, in case Nlah ransomware encrypted files with an offline ID, there is a chance that a different decryptor might work for you.
Nlah ransomware virus payload is usually launched after unsuspecting PC users open boobytrapped email attachments or download pirated software on P2P networks or similar sites. If the infection process is successfully initiated, it alters Windows Registry/Task Manager/Boot sequence to gain control over the system and launch the encryption algorithm smoothly. Upon that, photos, documents, and other personal property stored on the machine are locked, and the specific appending is added. This ransomware is also dubbed as .nlah file extension virus based on the suffix of encrypted files. The ransom demand varies from $490 to $980, which is disclosed in _readme.txt file or lock screen.
| Name | Nlah |
|---|---|
| Type | Ransomware / encryption-based malware |
| GENEALOGY | Djvu ransomware family |
| List number | 229th in the list |
| File extension | .nlah file extension |
| Ransom note | _readme.txt |
| Contact email | helpdatarestore@firemail.cc or helpmanager@mail.ch |
| Danger level | High. Permanent file loss possible. Serious Windows system compromises can cause system crashes. |
| Symptoms | Inaccessible files on the machine. Ransom file created on the desktop and non-system files. Sluggish PC's performance, high CPU usage, unresponsive AV engine |
| Elimination | Nlah removal depends on the powerful anti-virus program |
| Damage fix | Use FortectIntego to restore the settings that have been set before the ransomware attack |
During the installation, Nlah ransomware virus payload is extracted and multiple malicious entries are scattered through multiple system's locations. Some of the components are responsible for compromising Windows OS performance, the others for launching the cipher for data lock, and the last part initiates modifications to gain persistence, and prevent removal.
Typically, Nlah ransomware virus drops a malicious executable file in the %LocalAppData% or %AppData% and disguises it under legitimate Windows OS file names. Alternatively, it runs a Windows PowerShell command under administrative privileges, which deletes Volume Shadow Copies[2].
In many other traits, Nlah ransomware is identical to Zipe, Koti, Mzlq, Nesa, Gero, and the rest of 228 variants. However, not all of the Djvu versions are equally active. The activity of the ransomware depends mostly on its distribution technique and it seems that this latest version is likely to be persistent. Just a few hours after its release, people started reporting on Reddit[3] that their files have been encoded by this malicious crypto-ransomware.
According to the reports, the .nlah file virus is capable of locking most of the non-system files. Upon that, it automatically creates a text file _readme.txt, which informs the victim about the following requirements:
- He or she has to pay the ransom that varies from $490 to $980;
- The only currency accepted – Bitcoin;
- The contacts of the Nlah ransomware managers – helpdatarestore@firemail.cc and helpmanager@mail.ch;
- If the victim contacts criminals less than 72 hours after the attack, they apply the lowest price for the decryption software;
- This version of ransomware uses an online key protected by RSA encryption cipher. Therefore, the decrypted files cannot be recovered for free.
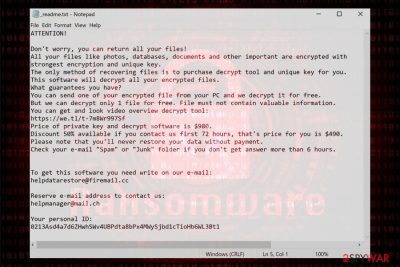
The original file of the ransom demand text file contains the following information:
ATTENTION!
Don't worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://we.tl/t-7m8Wr997Sf
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
helpdatarestore@firemail.ccReserve e-mail address to contact us:
helpmanager@mail.chYour personal ID:
–
If you have fallen victim to this cyber infection, please do not fall for paying the ransom. Experts from semvirus.pt[4] claim that paying the ransom is a big mistake because of future insecurities that emerge because the victim may disclose some pieces of personal information to criminals during the transfer of the payment. Besides, giving away money to criminals can't fix your machine. Therefore, full Nlah ransomware removal is a better solution.
In terms of decryption of the personal files locked by this ransomware, it's advisable to get an HDD or a high capacity USB flash drive for cold storage backups. Copy all encrypted data on the alternative storage and then run a thorough system scan with SpyHunter 5Combo Cleaner security tool to remove Nlah ransomware completely.
If you cannot remove Nlah virus because it actively blocks your anti-virus software, the only way to decontaminate malicious processes is to restart Windows OS into Safe Mode. The guide on how to do that is provided at the end of this post. Nevertheless, don't try to look for malicious entries manually because you will only waste your time for nothing.
.nlah file recovery methods are quite limited
Please note that ransomware termination and data encryption are two separate procedures, so you will not be able to recover your files just because you deleted the malware from your computer. If you wonder how you can open .nlah files, there is no way to do that until the decryption is performed, although some alternative methods (such as Emsisoft's decryption tool or third-party recovery software) might be able to restore your data.
However, the success of the provided methods highly depends on various factors, including:
- For Emsisoft's decryptor to work, your files must be encrypted with an offline ID, which means that malware should not have contacted a remote server to extract a unique key; additionally, somebody infected with Nlah ransomware must have paid the ransom to cybercriminals and provided the decryption key to security researchers;
- Built-in methods, such as System Restore or Previous Version Feature would only work if malware failed to remove Shadow Volume Copies and other Windows backup mechanisms;
- Third-party recovery software can be successful in retrieving working copies of some of the files that are still present on the HDD and has not yet been overwritten by other data.
Despite these difficulties, you should still try to recover them in alternative methods and avoid contacting cybercriminals.
Keep in mind that .Nlah files do not pose any threat to your computer, as they do not hold any malicious code, while malicious processes on your computer should be stopped by a robust anti-malware software.
The vulnerable system is a perfect target for criminals
The amount and time you invest in the system's stability and security pay off not in the cache, but the possibility to use the system efficiently and safely. Those who do not invest in professional AV software package, use illicit Windows version, fails to update software, and leave vulnerabilities unpatched risk exposing PCs to hacks and virus attacks.
Security experts claim that people should patch vulnerabilities by installing the latest software updates. Microsoft regularly releases patches to fix security vulnerabilities, especially the ones that are easily exploitable by hackers.
If you are using RDP services, make sure to password protect the service and use a strong password, not 123321 because it can easily be revealed. Besides, do not underestimate the protection capabilities of the professional AV programs. A full pack of security tools can help to protect the system in real-time attacks, as well as quarantine cyber threats that have already installed on the machine.
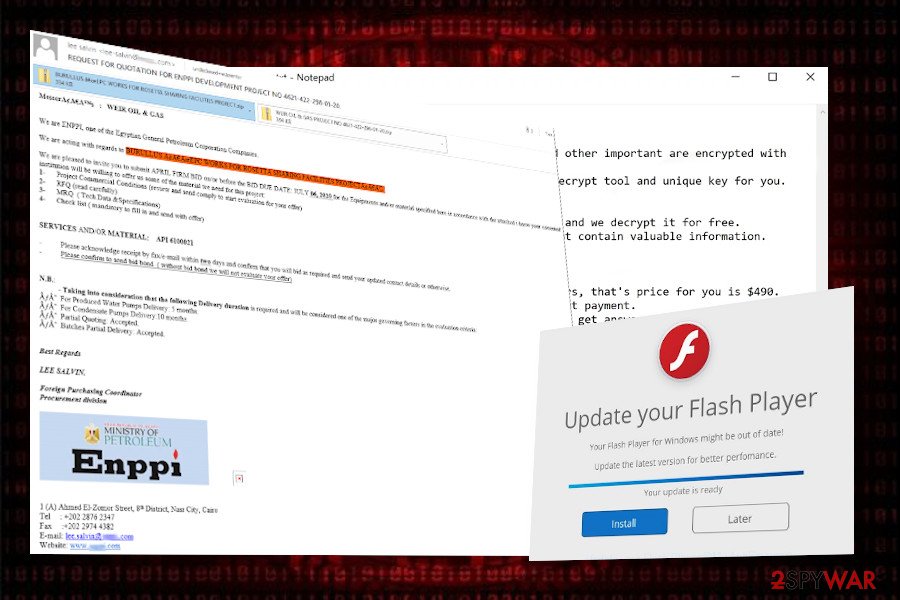
Apart from brute force attacks and exploits, criminals prefer spamming campaigns for spreading ransomware payloads. Criminals create professional-looking emails pretending to be from courier companies (Fedex, DHL, etc.), banking firms, governmental institutions, or various worldwide-known organizations. Such emails contain an attachment, which carries obfuscated ransomware payload.
Therefore, we strongly encourage people to not open email messages that contain grammar, spelling mistakes, or unknown sender. Such attachment supplemented emails are a perfect medium for spreading not only ransomware but other malware as well, so it's better to send them to spam immediately than opening just to satisfy curiosity.
Only a robust anti-virus tool can fully remove Nlah virus ransomware
Nlah ransomware removal is not the procedure that can be initiated in an easy way. People who are not tech-savvy enough can hardly find any malicious entries by themselves as they are usually disguised under legitimate files in the following locations:
- %AppData%
- %Local%
- %LocalLow%
- %Roaming%
- %Temp%
To remove Nlah virus once and for all, try downloading these tops: SpyHunter 5Combo Cleaner or Malwarebytes. This piece of software will check the system for all malicious files and processes that belong to the suite of the ransomware and you won't have to search for any dangerous entries by yourself.
If, however, you doubt about the removal of this ransomware because you are afraid of losing files encrypted by .nlah file extension virus, then we can assure that keeping the virus on the system will not help with file recovery. As soon as the virus is removed, we recommend making backups of encrypted files and keep them in the external storage until cybersecurity experts find the flaw in the encryption algorithm and update the existing Emsisoft's decryption tool.
Alternatively, you can find tips on how to recover files locked by Nlah ransomware virus at the end of this article. We strongly recommend trying each of the methods because they can help you to restore at least a part of corrupted documents.
Besides, the post-ransomware for of the Windows OS requires deep maintenance. Compromised registry keys and executables can end up with incompatibilities, errors, BSODs, and similar malfunctions. Thus, we recommend scanning the system with FortectIntego to fix Nlah ransomware virus damage.
Getting rid of Nlah virus. Follow these steps
Manual removal using Safe Mode
Safe Mode environment is required to delete the ransomware completely. A scan in a regular environment can end up with AV unresponsiveness and failure of the removal process.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Nlah using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Nlah. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Nlah from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.Nlah ransomware locks files just like any other Djvu variant. However, the versions that were encrypted using the offline keys can be recovered using Emsisoft's STOP/Djvu decrypter. This 229th version has no decryption software, at least for now, so you can try alternative data recovery methods listed below:
If your files are encrypted by Nlah, you can use several methods to restore them:
Employ Data Recovery Pro for file recovery
Data Recovery Pro is a tool that can be used for file decryption. However, before launching it, make sure that you have completely removed the Nlah ransomware.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Nlah ransomware;
- Restore them.
Unlock files locked by .nlah extension with Windows Previous Versions feature
Unfortunately, users who did not have the Windows Previous Versions feature enabled, won't be able to retrieve any of the locked files.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Run Shadow Explorer software
Djvu developers are known for programming their software to delete Volume Shadow Copies. However, try to look for flaws in ransomware programming with the help of this tutorial.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Nlah decryptor is in a development stage. No free key is currently available.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Nlah and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Michael Gillespie. Twitter. Social network.
- ^ Volume Shadow Copy. Science Direct. Online journals and books.
- ^ ".nlah" Ransomware infected some files, any news or decryptors for these?. Reddit. The biggest collection of forums.
- ^ NOVIDADES DE SEGURANÇA E SPYWARE. Semvirus. Virus and spyware news.





















