Zipe ransomware (Virus Removal Instructions) - Decryption Steps Included
Zipe virus Removal Guide
What is Zipe ransomware?
Zipe ransomware is an encryption-based cyber infection that belongs to Djvu family
Zipe ransomware is a file-encrypting virus that was first exposed publicly at the beginning of June 2020 by cybersecurity experts who were quick to analyze its core components and accredited it to the Djvu ransomware family. Looking to its core components, payload, ransom note, and encryption model, it because clear that the crypto-malware derived from this old ransomware family, which uses RSA Salsa20[1] encryption algorithm to restrict user's access to personal files.
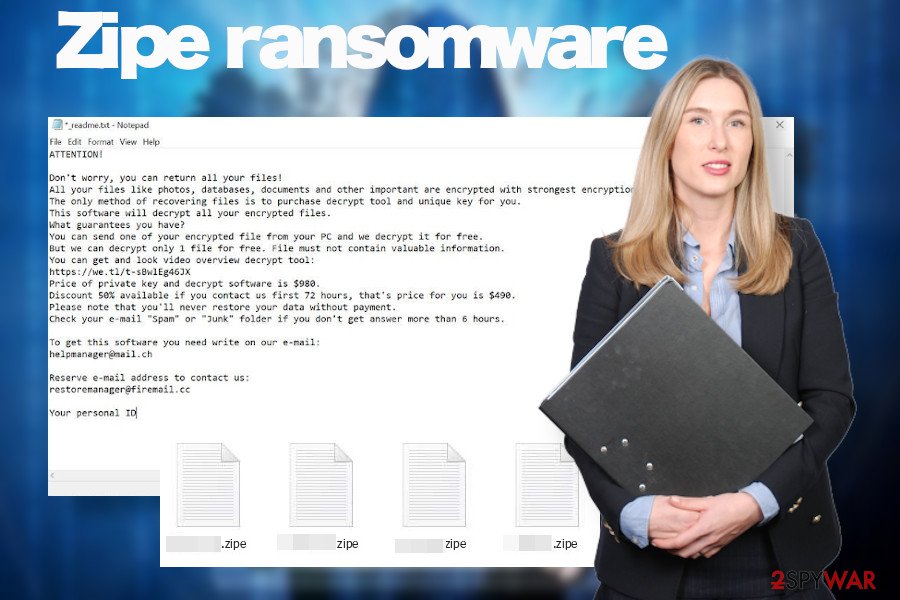
When the payload of this ransomware is downloaded, it unravels itself in phases – infiltration to gain prevalence, the launch of the cipher, manifestation. Just like any of the Djvu variants, it targets over 200 file types to lock, which subsequently get the .zipe file extension. Besides, a ransom note that the Zipe ransomware virus (_readme.txt) is yet another distinctive feature of the Djvu.
The danger level of the Zipe crypto-ransomware is highly dangerous as it may cause permanent loss of personal files. The encryption model that it uses cannot be brute-forced, meaning that it cannot be decrypted using the official Emsisoft's STOP/Djvu decrypter[2]. At the moment of writing, the only way to recover files is to pay the criminals $490 or $980 in Bitcoins (the price depends on how fast the victim responds).
| Summary of the virus | |
| Name | Zipe |
| Categorization | Ransomware |
| Genealogy | Djvu ransomware family |
| File marker | .zipe |
| Note | _readme.txt |
| Contacts | Hackers provide the helpmanager@mail.ch or restoremanager@firemail.cc emails for contacting them |
| Ransom size | The size of the ransom varies from $480 to $980 depending on the time span when the victim contacts the ransomware owners. The sum double drops if the victim contacts within 72 hours. The only currency accepted – Bitcoin. |
| Distribution | Hackers behind this ransomware are actively exploiting security vulnerabilities, initiating brute-force attacks via unprotected RDPs, spreading the payload via malicious emails, pirated software, etc. |
| Danger | High. It locks personal files that cannot be decrypted without paying the criminals. Moreover, it corrupts the system to weaken its security and may attempt to download payloads of Trojans. |
| Elimination | Perform Zipe ransomware removal with a professional antivirus program. Manual removal is possible. |
| Decryption | Although some of the Djvu versions can be decrypted, the latter variants are impossible to decrypt without a unique private key, which is owned by criminals. |
| Tips for fixing virus damage | Ransomware compromises the system significantly. Not only it locks personal data but attacks Windows OS, which may start malfunctioning in various ways. upon elimination of the file-encrypting virus, run a scan with FortectIntego tool to recover Windows performance |
The malware may skip some of the personal files that it is not compatible with. Unfortunately, it's most likely that the following file extension will get the .zipe file virus extension:
.aif, .cda, .mid, .midi, .mp3, .mpa, .ogg, .wav, .wma, .wpl, .7z, .arj, .deb, .pkg, .rar, .rpm, .zip, .bin, .dmg, .iso, .toast, .vcd, .csv, .dat, .dbf, .log, .sav, .tar, .xml, .ai, .bmp, .gif, .ico, .jpeg, .jpg, .png, .svg, .asp, .css, .part, .rss, .xhtml., .docs, .docx, etc.
Each locked file gets a .zipe extension and the design of the file (regardless of its type) is changed to a simple white design without logos. The owner of the PC is restricted from opening, renaming, or moving any of the locked files. Unfortunately, the owner will not be allowed to do anything before he or she pays a redemption.
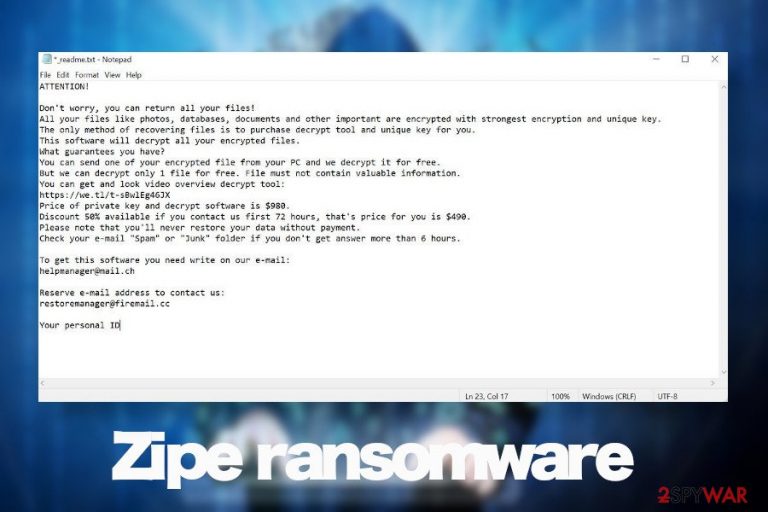
The size of the ransomware is stable with all Djvu variants. Just like Sqpc, Mzlq, or Koti, Zipe ransomware virus managers urge victims to pay the ransom in Bitcoins within 72 hours. If the victim does not fall for negotiations and resists paying the size doubles and reaches $980. All details about the payment are provided in the _readme.txt file, which is dropped by default in every folder that contains locked files. The ransom note says:
ATTENTION!
Don't worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-gSEEREZ5tS
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
*** Email address is removed for privacy ***Reserve e-mail address to contact us:
*** Email address is removed for privacy ***Your personal ID:
The ransomware targets the most popular file types with an intention to cause the highest losses and, thus, push the victim into paying the ransom. That's what Zipe ransomware virus does. Several minutes upon infiltration it adds a suffix to photos, documents, videos, file archives, etc. and leaves the victim helpless. Nevertheless, it's not advisable to pay the ransom due to a high risk of PII (Personally Identifiable Information) leakage.
Do not pay the ransom to protect your privacy. Instead, remove Zipe ransomware from the system asap. Before that, copy and paste the encrypted files into the USB flash drive to prevent its permanent loss. After that, launch the scanner of SpyHunter 5Combo Cleaner, Malwarebytes, or another professional AV tool while the system is in Safe Mode.
Experts from losvirus.es[3] recommend people to scan the system with FortectIntego utility upon Ziper removal to recover the performance of the system. Such malicious software places rogue files into the %Temp% folder alters Windows registries at directories like \SOFTWARE\Microsoft\Windows\CurrentVersion\Run, changes the boot sequence, and etc. Eventually, Windows runs slower, software gets unresponsive and vulnerable.
Malware authors keep exploiting vulnerabilities and flaws to inject malicious payloads
The best part of ransomware viruses is spread via obfuscated email attachments (.zip, .pdf, or Microsoft Office documents). Such attachments mimic order confirmations, invoices, tax-refunds, shipment tracking details, etc. Such emails contain malicious scripts that once activated drops the payloads and the ransomware engines start.
Alternatively, ransomware viruses travel via software cracks and keygens that, despite being widely used, are pirated and spread on peer-to-peer networks by unknown actors. Thus, downloading cracks[4] like Synapse, Deepfake, Outbyte, Adobe Acrobat, Adobe Photoshop, etc. pose a high-risk of a ransomware attack.
Last, but not least, these viruses can infiltrate PCs via infected pop-ups, hyperlinks, and other online content if the system is outdated, especially if it lacks updates for patching security loopholes or flaws. Thus, we strongly recommend people to update Windows OS regularly. This can be done automatically by accessing Windows settings and Checking for updates automatically.
Nevertheless, it does not mean that bad parties cannot use alternative distribution techniques. Thus, individual users and business administrators should take precautionary measures and render the most powerful anti-virus solution pack to protect their servers and machines from losses. It's advisable to enable Firefall protection, render a professional ad-blocker, and act carefully with downloadable content.
Remove Zipe ransomware from the machine and protect your PC with the powerful antivirus suite
Ransomware victims usually get a shock once they understand that each .zipe file extension virus-infected document can no longer be opened. It's not surprising having in mind that people are required to pay nearly $1000 to regain their property. However, experts stress the fact that paying the ransom is not the best solution.
Even if you pay the ransom and the criminals send you the offline Zipe decryption key, the virus itself remains on the system along with its pack of malicious entries. The ransomware has to be eliminated separately using professional security software that is up-to-date with the latest virus definitions.
Our technicians recommend people to use SpyHunter 5Combo Cleaner and Malwarebytes tools to remove Zipe ransomware. However, you can use any tool that you prefer the most. However, do not forget to update it before the scan and restart Windows into Safe Mode.
Getting rid of Zipe virus. Follow these steps
Manual removal using Safe Mode
If you have never dealt with a ransomware-type virus, then please note that all actions against it should be performed when Windows is in Safe Mode with Networking. Thus, remove Zipe why following these steps:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Zipe using System Restore
System Restore is yet another option that can help to handle with file-encrypting malware
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Zipe. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Zipe from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Zipe, you can use several methods to restore them:
Data Recovery Pro option might help to retrieve some files
Data Recovery Pro is a utility that is practically used for retrieval of files after system's crash. However, it is useful for encrypting some files after the ransomware attacks.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Zipe ransomware;
- Restore them.
You have Windows Previous Versions feature to try
If you have had Windows Previous Version feature enabled on your machine, try to enable the version that has been created before Zipe virus attack.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Enable Volume Shadow Copies
Usually, Djvu ransomware variants run malicious scripts to delete Volume Shadow Copies right after infiltration. However, that's not a rule, so checking for copies is recommended.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Zipe decryption software is not available.
STOP/Djvu virus has the official decryption software developed by Emsisoft. However, it is only available with variants that have been launched before August 2019.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Zipe and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ RSA and AES combination in offline situation. Information security. Stack exchnage blog.
- ^ Free Ransomware Decryption Tools. Emsisoft. Official website of the cybersecurity software developers.
- ^ NOTICIAS SOBRE SEGURIDAD Y VIRUS. Losvirus. Virus and spyware news.
- ^ oftware Cracks: A Great Way to Infect Your PC. Krebs On Security. Covering computer security.







