Luckynationalsuperworldwide.cyou ads (scam) - Free Guide
Luckynationalsuperworldwide.cyou ads Removal Guide
What is Luckynationalsuperworldwide.cyou ads?
Luckynationalsuperworldwide.cyou promotes scams that seek your personal information or other benefits
Internet is incredibly vast – it hosts almost two billion websites at any time. While most of the sites are created to be useful and informative, others are there for malicious purposes. Luckynationalsuperworldwide.cyou is a prime example of a phishing[1] website that shows users fake information and should be avoided at all costs.
Most of the time, people end up on this page by accident – they either click a malicious link somewhere else or are taken by an automatic script. This activity is prevalent mostly on torrent and similar illegal websites since they are usually very poorly regulated, and even cybercriminals have access to them.
Alternatively, users might land on Luckynationalsuperworldwide.cyou website due to adware[2] installed on their systems. Many people aren't even aware of adware's presence on their computers due to their deceptive distribution or operation methods. Sometimes, even a seemingly trustworthy app can be the reason behind intrusive ads and redirects. Thus, this aspect should be thoroughly investigated.
Upon accessing the website, users are commonly presented with a fake message – they are promised an expensive gift or a gift card. In return, they are asked to provide their personal details or download insecure software. There could be many nuances of what could be asked of visitors here, but they are never positive.
Once users provide personal details or download software, they would never receive the promised item and only then realize they have been scammed. This commonly results in users logging money or suffering from privacy issues due to personal data disclosure to cybercriminals. In some extreme cases, even identity theft is a possibility.
Thus, if you have encountered Luckynationalsuperworldwide.cyou while browsing the web on Google Chrome, Mozilla Firefox, MS Edge, or another browser, you should ignore whatever messages are shown and leave the page immediately. We provide more details on how to remediate the situation under different circumstances below.
| Name | Luckynationalsuperworldwide.cyou |
|---|---|
| Type | Scam, adware, ads |
| Operation | Claims that the memory is full and suggests to free it by offering insecure software |
| Distribution | Redirects, software bundles |
| Symptoms | Redirects to suspicious websites that hold plenty of commercial or scam content; fake messages offer to download malicious software; ads plague every visited website; unknown extension or program installed on the system |
| risks | Those who have malicious software installed on their systems are more likely to encounter malicious websites, resulting in financial losses, malware infections, and more |
| elimination | To stop the redirects, you'll have to remove adware from your device – you can either follow manual instructions or employ powerful SpyHunter 5Combo Cleaner anti-malware, which could do the job for you automatically |
| Further steps | Malware or adware infections can diminish the performance of your computer or cause serious stability issues. Use FortectIntego to remediate your device and ensure that the virus damage is fixed |
We have talked about scams many times before, and while they are evolving and new techniques are being used, their fundamentals remain the same. There are many different forms of fraud online – technical support scams, survey scams, get-rich-quick scams, and much more. The number of those does not subside because there are plenty of users who fall for them, providing some type of benefits for crooks in the process.
Tech support scams impersonating Microsoft, Apple, or Google are possibly the most common, and the main principle is to make visitors scared. They are often threatened with some type of consequence after a false statement is made. For example, “Your computer is infected with viruses. You should call the provided number to remove the infection,” or “Your anti-virus is out of date – click here to update immediately.”
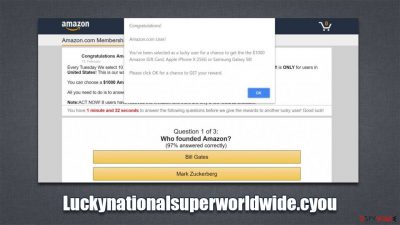
Alternatively, crooks also go the opposite route and try to sound friendly and welcoming, all while pretending to be somebody they are not, and this is the precise type of scams you are likely to encounter on Luckynationalsuperworldwide.cyou website. Here is an example of the “You've made the 9.68-billionth search” scam:
You've made the 9.68-billionth search!
Congratulations! You are the lucky winner!
Every 10 millionth search is reached worldwide, we will proclaim a winner to send out a thank-you gift.
Please select your lucky prize below and claim it by following the instruction.
In these scams, cybercriminals try to make users believe that they are some type of lucky winners, as they were chosen (usually to participate in a survey or raffle). They are promised a gift card, iPhone, PlayStation, or another pricy item in exchange for participation.
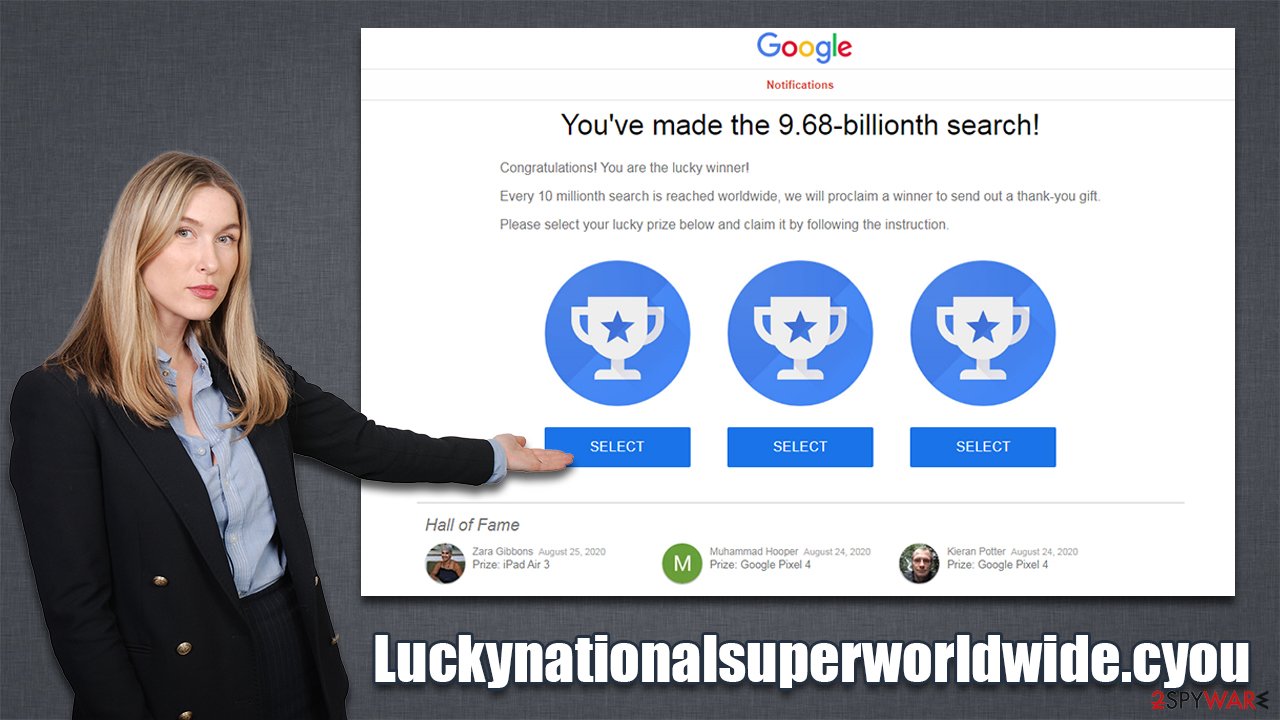
At the end of the quiz, people are then asked to provide their name, home address, email, and similar personal details. In some cases, users might be asked to give their credit card information, which is extremely dangerous and should never be done. This might allow crooks to break into your bank account and steal your money, so be careful!
The best way to go about this is to leave the page immediately without interacting with it. Keep in mind that tech giants don't randomly choose people to give them expensive presents for no reason – it is all a scam. Always check the URL of the website that promises anything similar, and you will quickly see it's a fake.
What to do after being exposed to Luckynationalsuperworldwide.cyou ads?
First of all, there is a major difference between whether or not you interacted with the malicious website. If you are simply wondering why you see suspicious websites and ads while browsing the web – follow the instructions below to clean your system from adware
If you have interacted with the scam in any way, you should do the following:
- If you provided your password, change it immediately on all accounts you are using (do not reuse your passwords in the future!);
- If you spent money on fake services such as alleged tech support, call your bank and explain the situation, the transaction might be reversed in some cases;
- If you downloaded and installed unknown apps, perform a full system scan with SpyHunter 5Combo Cleaner, Malwarebytes, or another reputable security software.
1. Check for suspicious extensions
Potentially unwanted applications that cause the annoying redirects are commonly installed as browser extensions. In some cases, they might not engage in bad activity for a very long time until they do. Thus, we recommend removing all the apps and enabling them one by one to see whether suspicious activity continues. Keep in mind that malicious apps, regardless if installed on the browser or system levels, will always be detected by security software.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
MS Edge (legacy)
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.
![Remove extensions from Edge Remove extensions from Edge]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
2. Remove the installed programs
As already mentioned, adware might be installed on the system level. Most apps can be manually removed via Control Panel (Windows) or Applications (Mac) locations. If you struggle to eliminate unwanted programs this way, simply skip this step.
Windows
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Mac
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
3. Scan with anti-malware
This step is particularly important for those who downloaded and installed something from Luckynationalsuperworldwide.cyou or another similar website. Crooks often create fake scenarios where users are convinced that installation of some type of application is beneficial or even necessary.
Likewise, the most aggressive adware and some other potentially unwanted software can be detected and removed by SpyHunter 5Combo Cleaner, Malwarebytes. or another powerful anti-malware. Security software is also your first line of defense from ransomware, rootkits,[3] Trojans, and other dangerous threats that could be encountered online.
4. Remove browser caches
The last step that should seal the deal and get rid of all the unwanted activity is your browser cleaning. Cookies, for example, might in some cases be hijacked by cybercriminals, which would allow them to access your sessions, meaning they could get access to your personal accounts – social media, banking, etc. Thus, as a precautionary measure, security experts urge users to clean browser caches from time to time.
Likewise, web data might contain cookies that are used for data tracking. Even though the collected information is anonymous, it does not improve your privacy in any way. If you want to stop being tracked, employ FortectIntego maintenance tool to clean your browsers and other junk from your PC. Alternatively, proceed with the following steps:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
MS Edge (legacy)
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.
![Clear Edge browsing data Clear Edge browsing data]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Phishing Attacks: Statistics and Examples. Check Point. Security solutions.
- ^ Adware. Wikipedia. The free encyclopedia.
- ^ What are Rootkits and Why are They Bad News for Your PC?. Sophos. Security research blog.














