Lulz ransomware (Virus Removal Guide) - Decryption Steps Included
Lulz virus Removal Guide
What is Lulz ransomware?
Lulz ransomware is crypto-malware that belongs to Project Root RaaS scheme
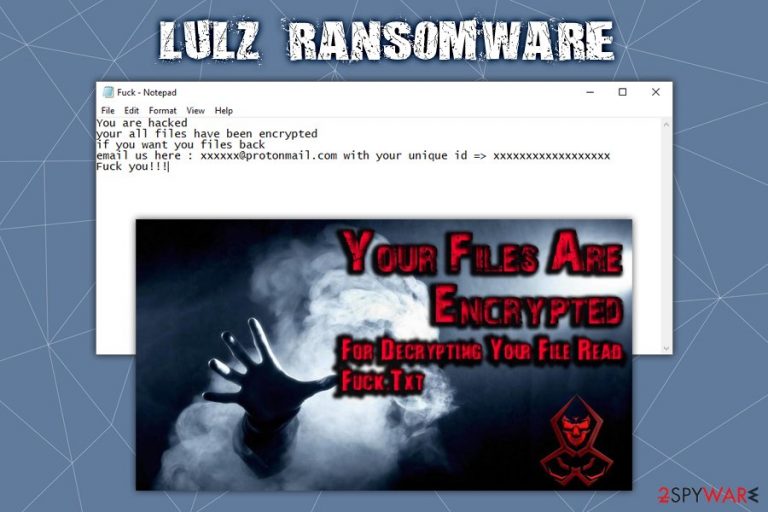
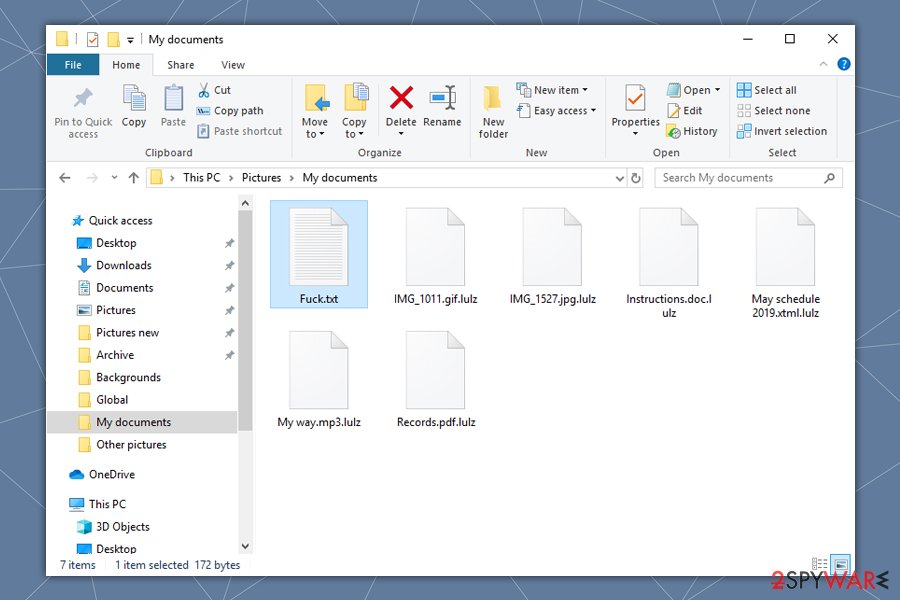
Lulz ransomware is a new file locking malware strain that was first analyzed by security experts from SentinelOne.[1] Once inside the system, it encrypts 195 file types located on the local and connected drives with the help of the AES-256 encryption algorithm and appends .lulz marker to each of them (for example, a picture.jpg is turned into picture.jpg.lulz). After that, the data becomes inaccessible, and victims are asked to pay a ransom in order to regain access to it – a brief message from hackers appears in the “F*ck.txt” file, as well as a desktop wallpaper which is altered from a preset one.
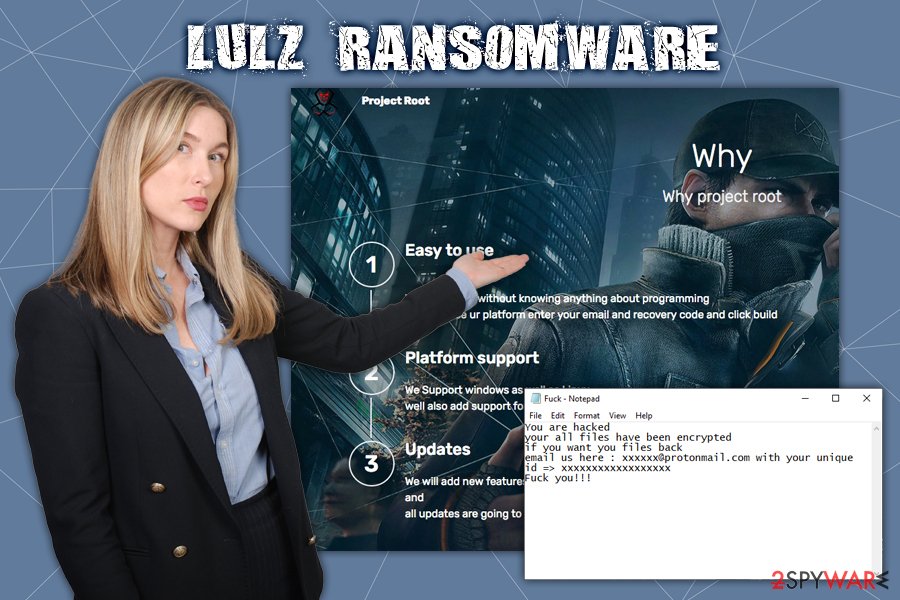
Lulz ransomware is one of the first releases based on Project Root – a Ransomware-as-a-service[2] scheme. Crooks, even without much of a programming proficiency, can buy the malicious payload via the Dark Web and use it for a cut from the profits made by collecting ransom payments from victims.
| Name | Lulz ransomware |
| Type | Crypto-malware |
| Originates from | The malware comes from a ransomware-as-a-service Project Root |
| Operating platforms | The malware is developed for Windows and Linux operating systems and supports 32-bit and 64-bit architectures |
| File extension | Each of the affected files is appended with .lulz, although the extension can vary and be anything, as set by the attacker |
| Encryption method | Lulz ransomware uses symmetric encryption AES-256, which uses one key to lock and unlock the data on the host machine |
| Ransom note | Users' desktop wallpaper is altered that tells them to open a “Fu*k.txt” file that is placed into each of the affected files folder |
| File recovery | File decryption is only possible via backups, using third-party recovery software (low chance) or by paying cybercriminals (not recommended) |
| Ransomware removal | To get rid of Lulz ransomware, a scan with a robust anti-malware software is advised. If malware prevents security software from operating properly, enter Safe Mode with Networking as explained below |
| Recovery | Ransomware is known to alter multiple system files, and some of them cannot be recovered by anti-malware software. In such a case, we advise scanning the machine with FortectIntego, which could remove damage done by the infection |
Lulz ransomware, while not extraordinary, has multiple tricks up its sleeve. Similarly to LockerGoga, the malware is written in Golang, which allows the payload to avoid both machine-learning and signature-based detection techniques by anti-virus engines. Nevertheless, most of the security solutions are equipped with advanced engines and might be able to stop the infection before file encryption is performed. Thus, for Lulz ransomware removal and protection, use reliable protection measures.
Lulz virus is programmed to exit the machine upon detecting a sandbox environment,[3] such as VMware and Oracle VirtualBox (these are usually used by security researchers to analyze malware samples). Before proceeding with the infection, it will also attempt to establish the connection to one of amazonaws.com addresses, to ensure that internet connection is available on the targeted machine. Lulz ransomware will then try to disable the installed anti-virus applications.
Once the preparations of Windows or Linux operating systems are done, Lulz ransomware will look for the following file types and encrypt them with a secure symmetric encryption AES-256:
001, 3fr, 7z,asset ,d3dbsp, ,mdbackup ,pkpass, ,psk ,rar accdb, ai, apk, arch00, avi, bar, bay, bc6 bc7 big, bik bin, bkf bkp blob bsa c, cab, cas, cdr, cer, cfr, con, cpp, cr2, crt, crw, css, csv, das DayZProfile, dazip, db0, dbf, dcr, der, desc, dmp, dng, doc, docm, docx, dwg, dxg, epk eps, erf, esm ff flv, forge fos, fpk fsh, gdb, gho,iso gif, hkdb hkx, hplg, htm, html, hvpl, ibank, icxs, indd, itdb, itl, itm itm, iwd, jpe, jpeg, jpg, js, kdc, kf, lbf, litemod, lng lrf ltx lvl m2, m3u, m4a, map, mcgame, mcmeta mdb, mdf, mef, menu, mlx, mp3, mp4, mpq, mpqge, mrwref, ncf, nrw, ntl, odb, odc, odm, odp, ods, odt, orf, p7b, p7c, p12, pak, pdd, pdf, pef, pem, pfx, png, ppt, pptm, pptx, psd, pst, ptx, py, qdf, qic, r3d, raf, raw, re4, rgss3a, rim rofl, rtf, rw2, rwl, sav sb, sc2save sid, sidd, sidn, sie, sis, slm snx, sql, sr2, srf, srw, sum, svg, t12,t13, tax, tor, torrent ttarch2 txt, unity3d upk, vdf, vfs0 vpk vpp_pc vtf, w3x, wb2, wma, wmo wmo, wmv, wotreplay, wpd, wps, x3f, xf, xlk, xls, xlsb, xlsm, xlsx, ztmp
The changed wallpaper will refer users to the ransom note Fu*k.txt which states the following:
You are hacked
your all files have been encrypted
if you want you files back
email us here : xxxxxx@protonmail.com with your unique id => xxxxxxxxxxxxxxxxxx
F*ck you!!!
Please do not contact cybercriminals behind the ransomware, as, looking at the way they communicate with victims, it is highly likely that they might not send back the Lulz ransomware decryptor, even after payment is transferred. Instead, you could attempt to recover data with the help of third-party recovery software such as Data Recovery Pro or Shadow Explorer. Under certain circumstances, alternative methods may help you retrieve the locked data, although the chances are very low.
However, before that, you should remove Lulz ransomware from your computer, which might prove to be a challenge for some, unfortunately. Due to the sophisticated functionality of malware, we highly recommend you access Safe Mode with Networking for the process. After you are sure that all Lulz virus components are eliminated, you could also use FortectIntego to recover from system errors caused by malware infection.
Ransomware authors can use multiple different distribution methods
The ransomware-as-a-service scheme allows multiple different threat actors to buy the service and customize it before deploying it to the victims. Therefore, even the same malware might have different features or be delivered in different methods, depending on its distributors' preferences. If you want to protect your machine from ransomware, you should be ready for everything – check out these security tips from industry researchers:[4]
- Employ reputable anti-malware software that uses advanced detection methods and provides real-time protection;
- Enable Firewall and protect your WiFi connection with a secure password;
- When using Remote Desktop, change the default TCP port, use a strong password and always disconnect from the service once complete;
- Beware of spam email attachments that ask you to enable macros – these phishing emails might seem legitimate from the first sight;
- Never download pirated software installers or cracks/keygens – these tools are often infused with malware;
- Patch your system with the latest security patches;
- Set all the installed software to be updated automatically.
Finally, you should backup your files – this will save a great deal of frustration when dealing with ransomware infection.
Lulz ransomware elimination might get tricky – here's what to do
As we previously mentioned, the Lulz virus is capable of using evasion techniques and might also be able to disable your anti-virus software. Luckily, the Safe Mode environment usually tackles these problems and prevents ransomware from reaching its goals. Therefore, if you fail to remove Lulz ransomware normally, you should access the Safe Mode, as explained below. If your security software does not start or got corrupted by malware, you should download the installer from an unaffected computer, transfer it via the USB or DVD, install it, and only then run a full system scan.
Once you complete Lulz ransomware removal, you should first backup all your data. Paying criminals is one of the possibilities of recovering your files but be aware that:
- the provided tool might not work or be contaminated with other malware;
- crooks may simply ignore you after they get your money.
Therefore, rather attempt to recover your data with third-party solutions first. Likely these will not be effective for all files, although some parts may be recovered successfully. If no luck, you should wait for security experts to find vulnerabilities within ransomware code and release a working Lulz ransomware decryptor in the future.
Getting rid of Lulz virus. Follow these steps
Manual removal using Safe Mode
Lulz ransomware might be difficult to remove. If you are struggling, you should access Safe Mode with Networking and attempt the process from there:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Lulz using System Restore
System Restore function can also serve as an effective method when trying to get rid of malware:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Lulz. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Lulz from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Lulz, you can use several methods to restore them:
Data Recovery Pro might be used to recover ransomware-locked files
Data Recovery Pro is one of the leading recovery tools on the market. However, it is not designed to recover data that has been locked by ransomware, to the results might not always be positive.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Lulz ransomware;
- Restore them.
Windows Previous Versions feature might be a solution
In some cases, Windows Previous Versions feature can be used to retrieve files one-by-one. However, this method only works if the System Restore function was enabled prior to the Lulz ransomware attack.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Make use of ShadowExplorer
Ransomware is programmed to perform certain changes in the system. However, just like any other software, it might fail to execute certain functions because of bugs within the programming code. If that is the case and the Lulz virus failed to delete Shadow Volume Copies, you have a high chance of retrieving all your files with ShadowExplorer.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryption tool is currently available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Lulz and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Jim Walter. Behind Enemy Lines | Looking into Ransomware as a Service. SentinelOne. Cybersecurity research blog.
- ^ Ransomware-as-a-Service (RaaS): How It Works. Tripwire. Cybersecurity and Compliance Solutions.
- ^ What Is a Sandbox Environment?. Cloudshare. Virtual IT Labs.
- ^ Avirus. Avirus. Cybersecurity insights and malware reports.







