MacBooster (Removal Instructions) - Improved Guide
MacBooster Removal Guide
What is MacBooster?
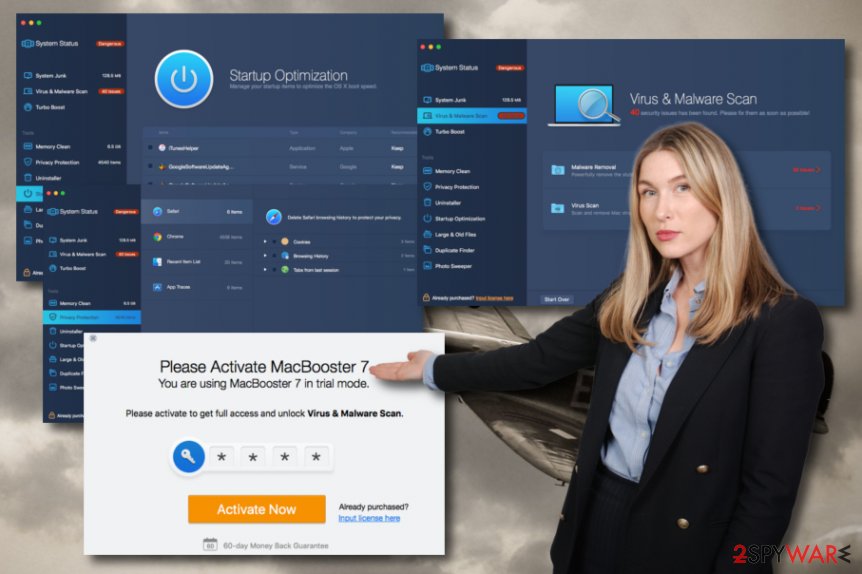
MacBooster – a bogus computer tool that provides harmless components as serious threats

MacBooster, developed by IObit, is described as a doubtful tool for Mac system optimization by many users. Even though the official website of this software provides a nice description of the product and encourages people to “enjoy a faster and more secure Mac”, our research shows the opposite. MacBooster is not the program you can leave your computer security for as all it does is providing false check-up results and urging users to buy the activation key for the licensed version in order to be able to “fix” all issues detected. Mostly, these “detected issues” are just outdated files, cache,[1] and other useless objects that do not possess any harm to our machines.
| Name | MacBooster |
|---|---|
| Type | Rogue system tool |
| Creator | IObit |
| Target | Mac OS-based computers |
| Aim | To push the licensed version of the program |
| Spread by | Official website, packages of freeware/shareware |
| Removal | Get rid of the suspicious tool automatically/manually. In addition, scan the entire system with FortectIntego to stop all additional PUP-related content |
MacBooster aims to provide a big variety of beneficial-looking features. Some of them are checking the system status, scanning the machine for potential malware, cleaning space, protecting your computing and online privacy, optimizing the entire machine, uninstalling bogus or harmful programs, speeding up processes, and so on.
However, keep in mind that MacBooster might look very attractive from the first view but all of these provided features are not truly existing. The best that this tool can do is eliminate some junk files. Of course, this is not a reason to keep it on your system as any reputable software can do the same and ten times better.
Besides, we believe that you want to receive true system check-up results to be notified about the real condition of your machine. Well, we cannot say that such a thing will happen if you continue using MacBooster. Better try installing and launching a trustworthy program and taking a look at the scan results that it provides you. We bet that you will see nothing similar to the “malware” provided by the bogus tool.
We do not recommend visiting macbooster.net, the official website of MacBooster either. We have read the Privacy Policy there and discovered that the developers are allowing third-party advertising[2] on their website. Once you start receiving a “great deal” of pop-ups and pop-unders, do not be surprised if some type of adware has got into your computer system:
The majority of the online banner advertisements you see on IObit web pages are displayed by IObit. However, we allow other companies, called third-party ad servers or ad networks, to display advertisements on IObit web pages.
What is more, it seems that MacBooster developers allow third-parties to provide tracking cookies through their ad networks. Such components are usually placed on one's web browser to capture all activities and habits of the user. The more you get involved in all this advertising activity by clicking on the provided ads, the more the information third-parties will be capable to gather about you:
Some of these ad networks may place a persistent cookie on your computer or device in order to recognize your computer or device each time they send you an online advertisement. In this way, ad networks may compile information about where you are, or who are using your computer or device, saw their advertisements and determine which ads are clicked on. This information allows an ad network to deliver targeted advertisements that they believe will be of most interest to you.
Regarding all the mentioned reasons, MacBooster virus is another name given to this bogus security tool. Many people are not happy about the side effects that are brought together with this program. Besides, its reputation and ability to carry out promised functions are questionable which forces people to think about the elimination of this software.
If you are also a user who has been struggling with this questionable computer tool, you should get rid of it without any hesitation as it is not a necessary component and you will absolutely survive without it. Use FortectIntego for scanning the system and locating all additional files that have been brought by the PUP.[3] Afterward, continue with MacBooster removal.
Once you remove MacBooster from your Mac machine, you should consider getting a reliable antivirus tool for guarding your computer system and your personal data during computing/browsing sessions. Make sure that you identify the reputation of the software and experts' reviews in order not to be caught on another bogus piece of security software.

Prevention of bogus tools is necessary for an excellent system optimization
ZonderVirus.nl specialists[4] have made a research and found out that only the minority of third-party security tools are downloaded from their official website and the biggest number of downloads is made from secondary sources after all. However, these types of secret installations usually happen unknowingly when users lack attention.
In order not to fall for such tricks you have to opt for the right configuration in your browser settings. Do not let any suspicious software slip through your eye and you will have your system optimized 24/7. Do this by selecting the Custom or Advanced downloading/installing mode and by un-marking the Quick or Recommended options.
In addition, you should always have your own antivirus security. If you are wondering how to choose a reliable system optimization tool and not get caught on developers' tricks, we have some tips for you:
- Check for users' reviews about the tool.
- Check for experts' reviews about the tool.
- Do full research on the software that you are wanting to download.
Elimination purposes for MacBooster bogus software
Looking for a way to get rid of this suspicious software? Then you have come to the right place. We have provided you with two possible options on the MacBooster removal topic and which technique you are going to choose is completely up to you.
However, some recommendations would be to measure your capabilities on eliminating MacBooster by yourself and the time that you have for completing the process. If you have any doubts in your skills or you have been running into a lack of time, you should use the automatical removal option.
If you are not in a rush with some computing work or any other tasks and believe that you have good skills and some experience in the threat elimination field, you can try to remove MacBooster manually. Some helping guidelines have been provided at the end of this article.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of MacBooster. Follow these steps
Delete from macOS
Clean your Mac OS X computer system from bogus software and PUPs. You can do that by completing the following instructions:
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of MacBooster registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting system tools
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Cache. Techopedia. Tech terms and definitions.
- ^ Neil Kokemuller. What Is Third-Party Advertising?. Chron.com. Small Business.
- ^ Potentially unwanted program. Wikipedia. The free encyclopedia.
- ^ ZonderVirus. ZonderVirus. IT news and virus discovery.
