Mbed ransomware (Removal Guide) - updated Nov 2019
Mbed virus Removal Guide
What is Mbed ransomware?
Mbed ransomware is a ransom-demanding threat that spreads via infected files from pirated software packages
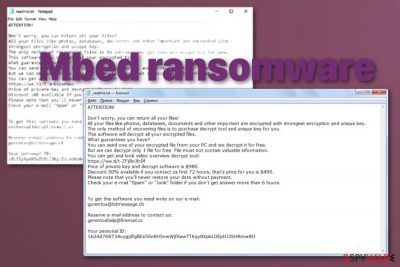
Mbed ransomware ads the ransom note to each folder that holds encrypted data and also places one copy of the message on the computer's desktop. This way the crooks are ensured that the users will definitely find and access the ransom note. Furthermore, hackers provide two email addresses: restorealldata@firemail.cc and gorentos@bitmessage.ch as contact information where the victims can send one small file for free decryption.
| Name | Mbed ransomware |
|---|---|
| File extension | .mbed |
| Family | Djvu/STOP virus |
| Ransom note | _readme.txt is the file that provides all the needed instructions for the ransom paying. Developers also offer to test decrypt one file in this message, but these people are criminals and you shouldn't trust them with your files or money |
| Ransom price and payment conditions | Victims who are infected with Mbed virus and get their files locked with the .mbed appendix are provided with ransom demands that vary from $490 to $980. The users can pay the smaller price if they manage to contact the crooks via a three-day time duration |
| Contact emails | The criminals provide gorentos@bitmessage.ch and gerentoshelp@firemail.cc email addresses as a way to communicate. Here users are also offered to send one small file for decryption as evidence of the tool's existence |
| Distribution | Files with malicious script get prepacked with pirated software, serial numbers of licensed tools or video games. Once the person gets a torrent file with cracks and cheat codes, installs the application the payload dropper gets triggered and ransomware loads on the machine. Encryption starts immediately after infiltration[1] |
| Elimination | The best option for Mbed ransomware removal is anti-malware programs that are designed to fight various malware and can detect the malicious activity |
| Damage | The threat also gets on the system to alter certain system parts, add files, disable programs, and install applications. Various changes get made, so the virus keeps its persistence up and decryption, the termination process gets interfered with |
| System repair | When it comes to issues with your system files and functions, you should rely on a particular PC repair application, so the virus damage might get fixed. FortectIntego is the tool that should indicate corrupted, damaged or altered parts of the system, so the performance of the device can be improved |
Those variants in the Djvu family that got in distribution until the end of August 2019 were the ones that supported offline IDs for the most part. STOPDecrypter tool was based on this functionality and helped many victims throughout the year. Unfortunately, the updated version of the Emsisoft decryption tool is not providing such functionality for versions released after August.
This option for file recovery includes 148 variants in the same Djvu family, but all the recent versions cannot be decrypted. If you got affected by Mbed ransomware virus variant or any previous version and the victims' ID ends in t1, you may get your files recovered with this tool, but that is only a possibility since developers haven't used offline keys for a while.
Mbed ransomware is one of the most recent Djvu ransomware versions that came out in November 2019, alongside Peet, Lokf, and Grod variants. Being released by rapid speed, all of these variants are not decryptable due to the advanced encryption method and online IDs in use. However, we have browsed the Internet sphere and discovered multiple user reports about the appearance of Mbed ransomware. Some people have been desperate for help and panicking that this malware hit their computer systems unknowingly and might be residing on a wide range of machines.[2]
Researchers speculate that decryption tools for this family in general, and for Mbed ransomware, in particular, can't be developed unless law enforcements discover the creators and obtain their database of decryption keys.[3] Otherwise, people will have to say goodbye to their data encrypted by this notorious malware.
Since Mbed ransomware virus is not easily decryptable, you should avoid giving the threat opportunity to ruin your machine and remove the malware completely using anti-malware programs. Then the best file recovery option is to rely on your data backups. Experts[4] always note that this is the best option to have the advantage in such instances – backup your file occasionally. Third-party software and other system features that can be useful for you are all listed below the article in the virus termination guide.
As for the proper tools that allow you to remove Mbed ransomware, you should go for anti-malware tools that can detect malicious activities and delete the virus completely from the machine. Since this cryptovirus runs on the system and affects more important parts that your personal files and cannot be terminated manually, you would need to find all associated files and programs to do so. However, professional anti-malware can do that for you during a full system check. 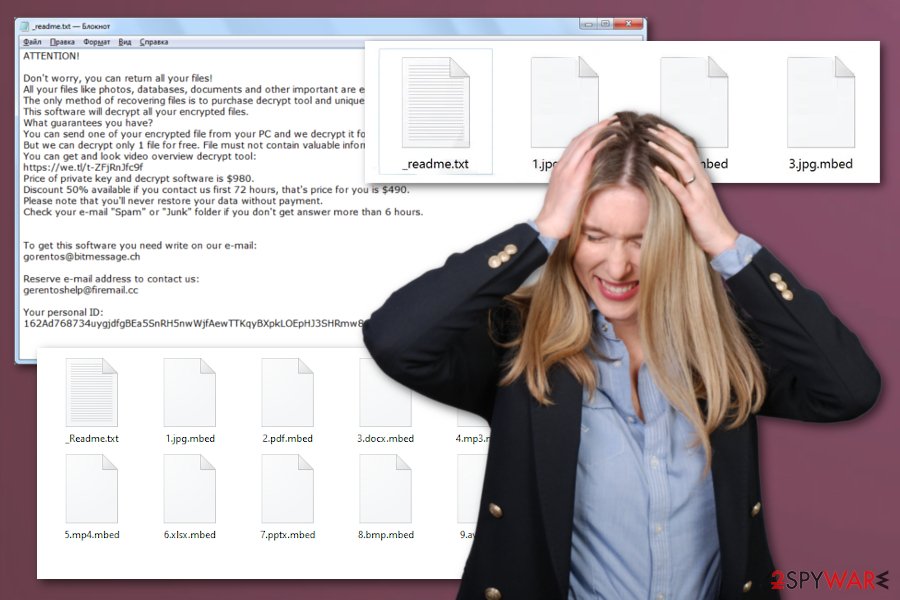
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-IbdGyCKhdr
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.
Offline IDs used by some of the versions in this family, generally, can be identified easily. This also means that ransomware can't connect to C&C servers while encrypting files, so built-in encryption keys and IDs get used. People that get affected by the same Djvu ransomware variant have the same ID, so files can be decrypted using one key. Unfortunately, this is not working for Mbed ransomware since the updated encryption method.
When it comes to online IDs that Mbed ransomware and more recent versions rely on, the C&C server connection allows the virus to generate random keys. Since each victim gets unique IDs, the person needs to get that particular decryption key to recover files completely. Mbed ransomware removal and decryption become merely impossible because of this fact.
You should get a proper system tool like FortectIntego and try to find, indicate and repair the damage that the virus has left behind, so your machine can be used normally again. If you try to do that manually, you may affect more crucial parts and make things worse, so try to scan the machine and restore system files this way since Mbed ransomware also can:
- alter files or add new ones in folders like %AppData% or %LocalAppData%;
- install trojans, info-stealing malware and run additional processes in the background;
- make the system running significantly slower;
- alter directories, registry entries and disable some system functions;
- compromise the Windows hosts file to prevent victims from accessing security-related forums.
Regarding information provided by VirusTotal,[5] Mbed ransomware has been flagged as a malicious program by 54 engines out of the total 69 AV tools. Some detection names include Win32:DropperX-gen [Drp], Trojan.GenericKD.32728174, Trojan.Encoder.858, Gen:NN.ZexaF.32515.Uy0@aWWfuRk, Trojan.MalPack.GS, Trojan:Win32/GandCrypt.GB!MTB, etc.
Pirating and using torrent services can lead to malware infections besides being illegal
Files delivered during the installation of a cracked program or download of the licensed keys for a professional tool can have more to them than you think. Even when the site shows verification badges for senders and pirated product providers, you cannot be sure that everything is safe to download and doesn't include any malicious script. No one can guarantee you that.
Cracks, cheats and other content like this are the main vectors used by this malware creator. The file only needs to get installed and launched alongside the program you initially download. Unfortunately, encryption is launched immediately and your files get locked in a matter of minutes.
Another method used by ransomware developers includes infected files placed on emails as file attachments. Microsoft documents filled with macros get planted in various email boxes attached to Financial information notifications from common companies, so people fall for the trick and can trigger the payload dropper by Enabling the Content. Clean your email box more often and stay away from illegal online services if you want to avoid cyber infections.
Last but not least, ransomware infections can be sneaked into your computer system via vulnerable RDPs such as the TCP port 3389. This happens when the RDP holds vulnerable security and protection. For example, when the generated password holds only simple words, letters, and numbers, or when there is no password at all. So, do not forget to think of strong and reliable passwords that include a mixture of letters, numbers, and symbols altogether.
Protect valuable data files by forming backups
There are plenty of places where you can store your files and documents, however, it is the most important to pick a safe location. Keeping all of your valuable information just on your primary computer is not a good idea as if a ransomware infection occurs, it might easily lock all of the data and make sure that it is permanently gone.
We recommend keeping copies of all valuable files and documents at least on multiple computer systems. However, it would be best if you have purchased a USB flash drive and stored copies of important data on this device. Just remember to keep it unplugged from your machine when you are not using it, otherwise, the infection might be capable of reaching your connected device too.
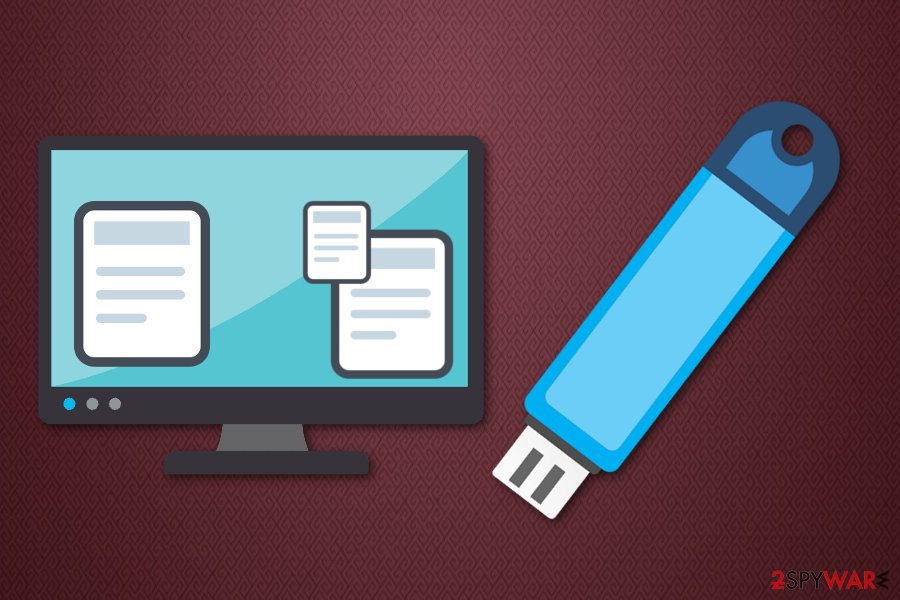
Continuously, there are other ways of keeping your information safe, for example, portable CDs, DVDs if you do not want to use a USB although it is the most comfortable way. Also, you can transfer copies of important data to remote servers such as iCloud if you are using a Mac machine or to Dropbox if you obtain a Windows computer.
Get rid of Mbed ransomware virus and clean the machine before its too late
When you can indicate that Mbed ransomware virus was the malware that encrypted your files, you can learn about the particular family and other versions, decryption options and try to find more details about the best removal methods. Unfortunately, you don't have much time for the research, so you can upload the sample of the threat for researchers' analysis.
Talking about Mbed ransomware removal as a general process, you should rely on anti-malware tools that can find malicious activities and eliminate the program with all the associated applications. Anti-malware programs can scan the machine and find, remove and terminate malware of all sorts. However, you shouldn't think that AV tools will recover your files.
The best method to restore encrypted files is to use your own file backups, but that cannot be done when your system is still affected. You need to remove Mbed ransomware and fix virus damage, to have a clean and safe device. For the possible system repair try FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes and check the machine for additional issues. Then you can rely on methods below dor file recovery.
Getting rid of Mbed virus. Follow these steps
Manual removal using Safe Mode
Reboot the machine in Safe Mode with Networking and then run the AV tool to remove Mbed ransomware completely from your machine
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Mbed using System Restore
System Restore is the feature that can help with malware removal since it repairs the machine in a previous state when the virus was not running
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Mbed. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Mbed from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Mbed, you can use several methods to restore them:
Data Recovery Pro is the third-party program for file restoring
You can use Data Recovery Pro for accidentally deleted files or encrypted data
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Mbed ransomware;
- Restore them.
Windows Previous Versions is the feature for file restoring purposes
However, when you use System Restore to remove Mbed ransomware, you can rely on Windows Previous Versions for file recovery
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer is the feature that can restore encoded data
You should check Shadow Volume Copies and when those are not damaged you can use ShadowExplorer
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Decryption tool is not developed for this version, but you can check options
You should check here for updates on decryption
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Mbed and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Encryption. Wikipedia. The free encyclopedia.
- ^ Riadg. attacked with an MBED. Eset forum. Topic.
- ^ Luke Irwin. List of data breaches and cyber attacks in September 2019 – 531 million records leaked. ITgovernance. IT protection blog.
- ^ Lesvirus. Lesvirus. Spyware related news.
- ^ 54 engines detected this file. VirusTotal. File detection information.





















