Micro Antivirus 2009 (Removal Guide)
Micro Antivirus 2009 Removal Guide
What is Micro Antivirus 2009?
Micro Antivirus 2009 –
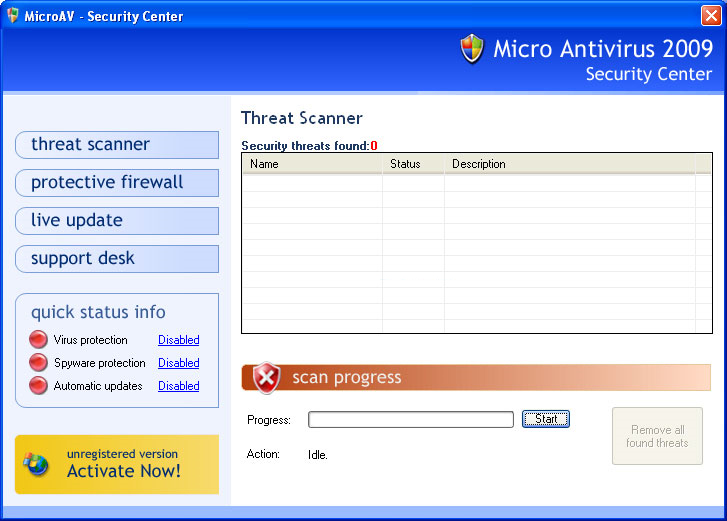
Micro Antivirus 2009 is distributed by trojans. This fact alone should raise suspicions about the reliability of this application. This program is not an anti-virus; it’s a computer parasite. However, it acts very convincingly: it mimics computer scans and fabricates security reports similar to those loaded by reputable tools.
MicroAntivirus can even imitate system alerts of the Windows operating system. It displays the falsified threat alerts in order to push people into buying a licensed version. Convincing people to pay money for a non-existent full version is the main goal of this corrupt anti-virus. Avoid it and remove it without hesitation.
| name | Micro Antivirus 2009 |
|---|---|
| Type | Fake anti-malware software, rogue antispyware |
| Purpose | Gain sales by making users believe their devices are infected with tons of various computer viruses |
| Risks | Malware infections, money loss |
| Elimination | Remove this program with the help of proper anti-malware software |
| System health | Take care of your device's systems wellbeing by using the FortectIntego system diagnostics software |
MicroAntivirus2009.com is the main website that sells the licensed version of the bogus security tool. Avoid this website, or better yet, block it using your HOSTS file. Although other shady websites could also spread and offer to pay for this rogue antispyware.
Other notable distribution methods include software bundling and fake Flash Player updates. Be watchful of what you install on your device to avoid not only the article's culprit but also other dangerous malware, such as trojans, ransomware, keyloggers, etc.
Also, please don't believe any virus scans or notifications that Micro Antivirus 2009 displays to you, as all of them are fabricated. It's a scam meant to scare you into thinking that your computer is infected when in reality, the only infection is the bogus software itself.
Remove it by scanning your device with reliable anti-malware software. If the rogue antispyware prevents you from launching your AV tool, please do it in Safe Mode with Networking. You could also try to remove it manually with our guide below. Afterward, to ensure that your PC runs smoothly, perform system diagnostics.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Micro Antivirus 2009. Follow these steps
Uninstall from Windows
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Micro Antivirus 2009 registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting rogue antispyware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
