News-gazifo.cc ads (fake) - Free Guide
News-gazifo.cc ads Removal Guide
What is News-gazifo.cc ads?
News-gazifo.cc is a malicious website showing messages you shouldn't trust
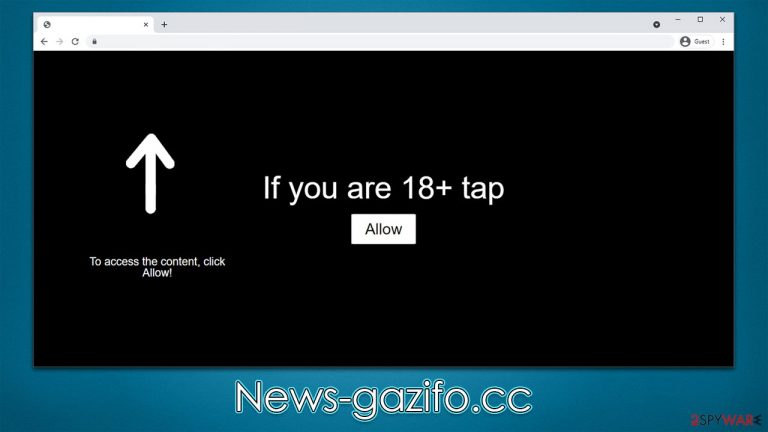
News-gazifo.cc is a phony website that sets out to mislead Internet users into thinking it is what it appears to be, only to take advantage of advertising revenue later. It simply attempts to present a request to enable push notifications as something entirely different so that users would click the “Allow” button within the prompt.
Scammers constantly create phony websites, and notification scams are quite common, especially when visiting high-risk places such as illegal video streaming platforms or pirated software distribution websites. Redirects to News-gazifo.cc may also occur if the device is infected with adware or other potentially dangerous software, thus needs to be checked out.
Possibly the worst outcome of the whole ordeal is that users are stuck with potentially dangerous ads that are shown directly on their screens, sometimes even covering other apps or browser windows. The content of these pop-ups is also misleading or even malicious, as links may lead them to websites where they could infect their systems with malware or be tricked into subscribing to more spam, etc.
| Name | News-gazifo.cc |
| Type | Push notifications, ads, scam, pop-ups |
| Distribution | After the “Allow” button in the notification prompt is clicked on the site |
| Symptoms | Notifications show up at the bottom-right corner of the screen – these include fraudulent content and links to potentially dangerous websites |
| Risks | The ads shown within push notifications might include misleading messages and links to malicious websites. If clicked, you might end up infecting your system with malware, disclosing your personal information, or losing money |
| Removal | To stop getting intrusive push notifications from a specific website, access your browser's settings. Afterward, scan your system for adware or malware to ensure that it is not infected |
| Other tips | It is vital to clean web browser caches to prevent further data tracking and other issues related to web data corruption – use FortectIntego to do this quicker |
Social engineering helps crooks to manipulate people online
Users don't come to the News-gazifo.cc site on purpose, which isn't surprising, considering it is a scam. An unanticipated redirect from another questionable source, such as a torrent site (and many other similar nefarious locations), might nevertheless lead to it. That's why it's important to stay away from high-risk sites as much as possible, and it includes those that spread software cracks and illegal installers of various software. Ransomware[1] and other malware are also lurking in these places, so be aware that one click may end up badly.
Once users are rerouted to the page, they see a request that appears normal – verify that they aren't robots or confirm they are 18 and over. These requests have been in plain sight of many internet users for some time now, so it's not hard to understand how someone might fall for it, except that these prompts are fabricated.
It is indeed true that users previously encountered requests to confirm their age or fill in captcha[2] symbols presented to them, and the way they should allegedly do this is by clicking the “Allow” button within the notification prompt, which is not what it is actually designed for.

It is also noteworthy that people might be told that there's some underlying content behind this request, such as a video that can be played or that there is a prize to be claimed just by simply clicking the button. In reality, News-gazifo.cc, as well as other similar sites like Cousonelly.com, Nonspewpa.com, or Cirlaing.com, have no content to explore and are entirely fake – their purpose is to convince users to subscribe to push notifications so that ads could be shown to them later.
Stop push notifications from malicious websites
Intrusive push notifications that originate from a scam scheme often confuse users about the source of the activity and what is causing it. Many assume their systems are infected with a virus because suspicious pop-ups typically indicate an infection is present. When looking for these infections, they attempt to scan their devices with security software but are unsuccessful. This is because push notifications can only be stopped manually via browser settings.
Nonetheless, the scan of the device when dealing with suspicious activity is extremely important, as there could be an adware or other unwanted software running in the background without your knowledge. Malware may sneak in when downloading repacked installers or when being exposed to malicious ads. The whole operation is rather sneaky, so you may not even know your system is infected.
Before proceeding with the News-gazifo.cc ads removal, we recommend scanning the system with potent security software, such as SpyHunter 5Combo Cleaner or Malwarebytes. After that, using FortectIntego can help you with clearing browser caches, including cookies,[3] and ensuring that no data tracking is taking place.
Google Chrome (desktop)
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).

Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.

- Locate the web address in question under Allowed sites and pick Remove.
How to prevent from getting adware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Ransomware. Wikipedia. The free encyclopedia.
- ^ CAPTCHA. Imperva. Data and application protection.
- ^ What are cookies? | Cookies definition. Cloudflare. The Web Performance & Security Company.
