Noblis ransomware (Virus Removal Instructions) - updated Nov 2019
Noblis virus Removal Guide
What is Noblis ransomware?
Noblis ransomware – a Phyton-written cryptomalware that demands 1 BTC for file redemption
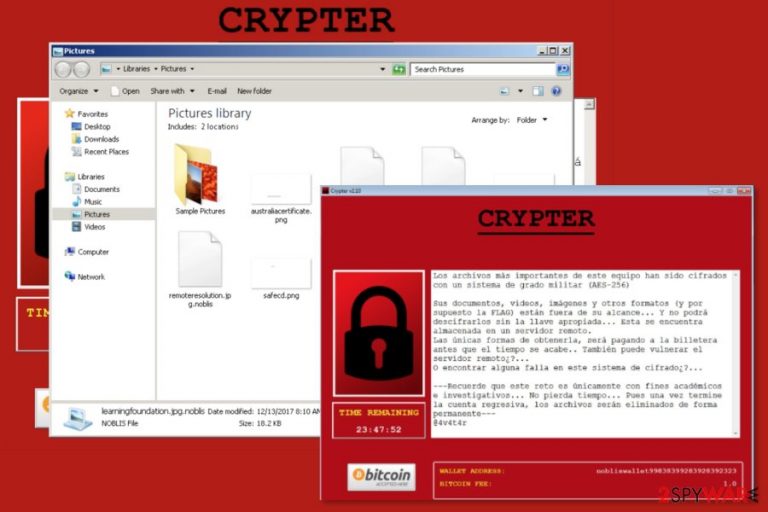
Noblis is crypto-malware that aims at Spanish[1] computer users and is written in Phyton. The file-encrypting virus uses AES-256 cipher[2] to encode files and make them inaccessible by adding .noblis, .anyrun, or, most recently, .sorryforthis, file extension. Following the encryption, it opens program Window Crypter v2.10 with data recovery instructions.
Some ransomware viruses are not designed by cybercriminals, and Noblis ransomware is one of them. Instead, the virus was written for educational purposes only, but most likely leaked by malicious actors – a similar situation happened to HiddenTear malware. Thus, the Noblis virus is created with the help of ransomware generator software.
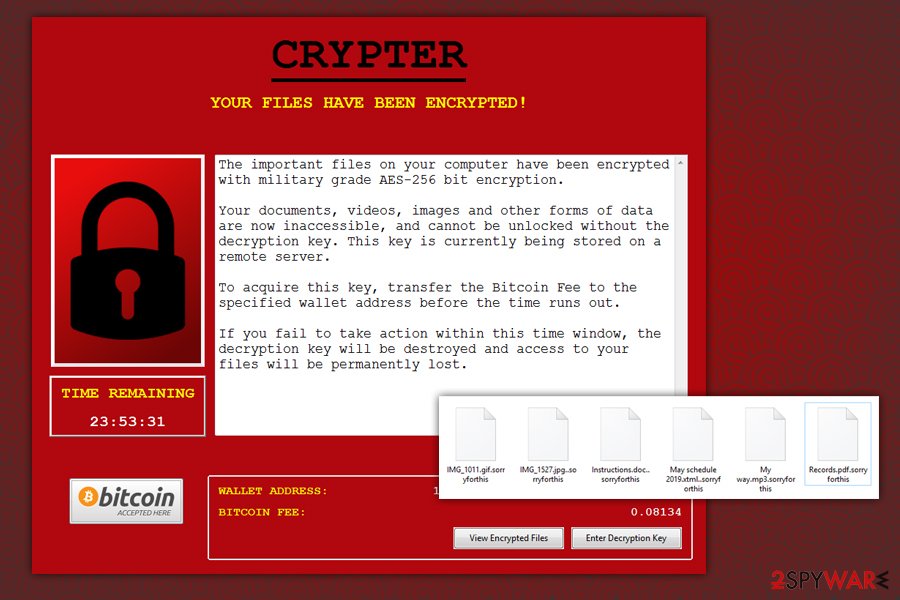
After Noblis ransomware initial release in December 2017, it went doormat and did not show much activity. Later, Cyclone ransomware was developed based on this malware. Most recently, in late October 2019, the newest variant of the virus was released – the ransom note is written in English, and attackers now ask for 0.08134 BTC payment for the decryptor.
| Name | Noblis |
| Type | Ransomware, cryptovirus |
| Initial release | December 2017 |
| Written in | Phyton programming language |
| Cipher | Malware uses AES-256 to encrypt data on the host system |
| Distribution means | Ransomware is known to be spread with the help of obfuscated spam email attachments, although other means might be used as well |
| Targets | Initially, malware targeted Spanish users but the most recent variant drops ransom note in English, meaning that the attackers chanced the distribution scope and aim to infect users worldwide |
| Versions | .noblis, .anyrun and .sorryforthis |
| Newest variant | .sorryforthis variant of malware was spotted in the wild at the end of October 2019 and asks users for 0.08134 BTC for file decryption software |
| Related | Cyclone ransomware derived from this malware |
| Termination | Use anti-malware software to locate the payload and remove all the components |
| File decryption | Only possible via backups. In some cases, third-party recovery software might be effective – check the methods described below |
| Recovery | After malware is deleted from Windows, it might start misbehave due to system file damage. To fix crashes, slowdowns, and similar aftereffects of ransomware, use FortectIntego |
According to the latest research data, malware is in in-dev mode. However, obfuscated payload called noblis.exe might be soon spread via malicious spam emails or using other ransomware distribution methods.
Once inside, Noblis ransomware makes necessary system changes before starting the encryption:
- Executes the dropper from Temp folder and unpacks associated files
- Establishes connection with a remote server
- Deletes Shadow Volume Copies to prevent file recovery
- Alters the registry and other vital Windows components to gain persistence, etc.
Noblis ransomware then starts file encryption with a strong cipher and uses encrypted_files.txt during the process – the file is placed into the %AppData% folder. When the virus finishes its destructive task, it opens a program Window with timer and Spanish recovery instructions:
Crypter
YOUR FILES HAVE to the BEEN The ENCRYPTED!
Archivos más importantes los de este equipo han edition sido cifrados con un sistema de Grado militar (the AES-256)
Sus Documentos, the videos, imágenes y otros formatos (y por supuesto la the FLAG) están fuera de alcance the su … the Y the no podrá descifrarlos sin llave apropiada … la Esta se Encuentra almacenada en un Servidor remoto.
Únicas Formas de las obtenerla, será la pagando a billetera antes que of el tiempo se .. acabe También puede vulnerar of el Servidor remoto¿? …
About encontrar alguna falla en este sistema de cifrado¿? …
— Recuerde que este reto es únicamente con fines an e … investigativos académicos No pierda tiempo … Pues una vez termine la cuenta regresiva, the los archivos serán eliminados de forma permanente —
@ 4v4t4r
WALLET the ADDRESS: nobliswallet99838399283928392323
Bitcoin of FEE: 1.0
The interesting fact is that the final sentences of ransom note tell that malware was created for academic and research purposes. However, it seems that someone wants to learn to program by harming others. According to the ransom note, Noblis virus is designed to delete files once the timer goes to zero (after 24 hours).
However, authors of Noblis ransomware offer not to waste time and obtain decryption software immediately. Victims have to transfer 1 Bitcoin to the provided wallet address. The research has shown that criminals provided a wrong address. Thus, even if you decide to sponsor criminals with such a huge amount of dollars, you won’t be able to do it.
Thus, after a ransomware attack, you should clean your computer and restore your files from backups or hope that third-party software will bring back at least some of the most important data. You have to remove Noblis automatically with reputable security software.
In some cases, Noblis ransomware removal might not succeed from the first time due to heavy system modifications made by malware. In such a case, you should access Safe Mode with Networking, as explained below. Once the virus is eliminated, you should take care of not only personal files but also system settings recovery. For that, use FortectIntego.
Prevention tips that help to minimize the risk of ransomware attack
Noblis is still in development. Thus, you have time to backup your files, obtain antivirus program and learn how to protect yourself from ransomware attack. Unfortunately, any security software cannot fully protect from crypto-malware. Thus, additional actions are needed:
- Be careful with emails. Do not rush to open email attachments or click on provided links without checking information about the sender and making sure that content is safe.
- Download only legitimate software and its updates. Trying to save the money by installing cracked programs is the straightest way to install malware. Additionally, you should not download free programs or updates from unknown file-sharing sites or network.
- Do not accept every offer provided in ads. Pop-ups that offer to download PC scanners, antivirus programs or other application most of the time include malicious content. Keep in mind that malware-laden ads might be displayed on popular websites as well.[3]
- Update software and operating system. Updating software or OS might seem bothersome task. However, it’s one of the most important ways to protect from cyber threats that might exploit outdated program’s vulnerabilities to hack your PC.[4]
Removal of the Noblis virus
Noblis removal has to be completed using reputable malware removal software. The malicious program might inject malicious code into various system processes, and terminating them manually is nearly impossible. Only professional malware removal tools can get rid of them safely.
Before downloading security software, you should reboot your computer to the Safe Mode with Networking. Then you should be able to remove Noblis without any obstacles. Scroll down for more information and detailed removal guidelines.
Finally, to ensure that your system's operation works just as well (or even better) as previously, you should use PC repair software FortectIntego. As for personal data recovery, use backups, as it is the only safe method to retrieve files without paying the criminals ransom. If none available, use alternative methods we provide below but keep in mind that chances of success are pretty low.
Getting rid of Noblis virus. Follow these steps
Manual removal using Safe Mode
To remove ransomware without any problems, you should reboot to Safe Mode with Networking first:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Noblis using System Restore
If a previous method did not help, try System Restore:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Noblis. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Noblis from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.The official decryptor is not available, but you can try alternative tools to restore your files if you do not have backups:
If your files are encrypted by Noblis, you can use several methods to restore them:
Try Data Recovery Pro
This program is designed to restore files after system wreckage or accidental deletion. However, it is also useful after the ransomware attack.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Noblis ransomware;
- Restore them.
Try Windows Previous Versions feature
If System Restore was enabled before the Noblis ransomware attack, follow this guide and restore individual files:
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Try ShadowExplorer
If Shadow Volume Copies were not deleted, Shadow Explorer might be useful in recovery procedure:
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Noblis decryptor is not released yet.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Noblis and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Los Virus. Los Virus. Spanish cyber security news.
- ^ Advanced Encryption Standard. Wikipedia. The free encyclopedia.
- ^ Dan Goodin. Big-name sites hit by rash of malicious ads spreading crypto ransomware [Updated]. Ars Technica. IT news, reviews, and analysis.
- ^ Russell Brandom. The global ransomware attack weaponized software updates. The Verge. Technology news and media network .







