JS.Nemucod (Virus Removal Guide) - updated Oct 2020
JS.Nemucod Removal Guide
What is JS.Nemucod?
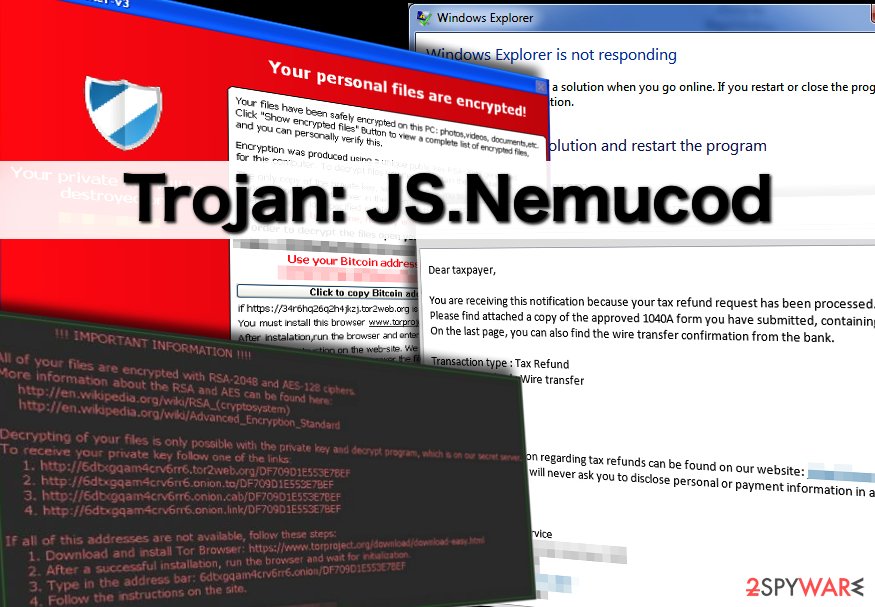
JS.Nemucod – a trojan that can install Crowti, Tescrypt, Locky, Fareit, and Ursnif viruses
JS.Nemucod, also known as Nemucod Trojan or TrojanDownloader:JS/Nemucod, is a very dangerous parasite that can relate in the installation of well-known ransomware and other malware. The trojan camouflages as a JavaScript component that is provided in the format of a ZIP file and comes clipped to email spam. According to Microsoft's report,[1] these files have been found to be related to JS.Nemucod virus and its variants: Invoice_ref-.zip, foto.zip, Gilberto_Bond.zip, 8221261_notice_to_appear_000986189.zip. A very interesting but harmful part of this Trojan virus is that it brings ransomware such as Tescrypt, Locky, Crowti, and Fareit, Ursnif parasites to the infected computer.
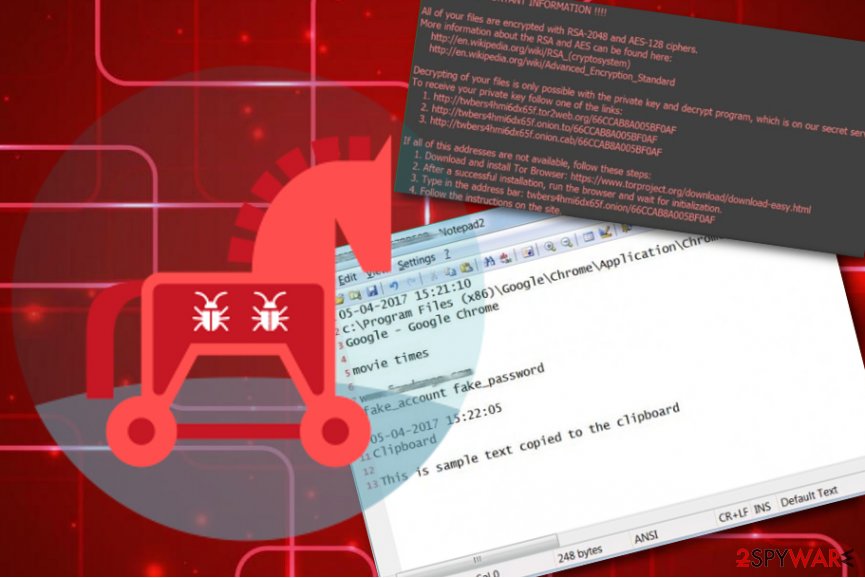
The ransomware viruses that are brought by JS.Nemucod aim to encrypt data that is stored on the targeted PC and demand ransoms in exchange for the decryption tool. Continuously, Fareit malware acts as a password recorder and might also access your personally-identifiable information where Ursnif is a Trojan horse that can also steal sensitive data that is saved on your machine and view technical details about your used computer.
| Name | JS.Nemucod |
|---|---|
| Alternative names | Nemucod Trojan, TrojanDownloader:JS/Nemucod |
| Category/type | Malware/Trojan horse |
| Related files | Once the malware infiltrates the system, it can show up in the format of these files: Invoice_ref-.zip, foto.zip, Gilberto_Bond.zip, 8221261_notice_to_appear_000986189.zip |
| Remote hosts | The Trojan virus also is capable of connecting to remote hosts such as ohelloweuqq.com, hpalsowantsff.com, sahasafe.com using port 80, thisisitsqq.com |
| Related malware | This virus does not come alone. It can also download Tescrypt, Locky, Crowti ransomware, and Fareit, Ursnif malware |
| Distribution | Trojan viruses are often spread via malicious email attachments that come in the format of a .zip or .exe file. However, they can also be distributed via p2p networks and other unsecured locations |
| Elimination | You should delete the malware by using automatical software only. Do not try to eliminate the parasite manually as this is a very complex process for such threat |
| Repair tip | If you have spotted any damaged objects on your Windows computer system, try repairing them with software such as FortectIntego |
According to Symantec researchers,[2] once JS.Nemucod is installed and starts running on the Windows computer system, it connects to a hacked WordPress[3] page and installs one of these files: %Temp%\67057318.dll, %Temp%\27172347.exe. Afterward, the malware might launch the downloaded components by using WShell or Rundll32.exe processes.
Since its release in 2015, JS.Nemucod seems to hold multiple versions and complex functionality. Besides all the mentioned processes, the Trojan virus also connects to a remote host in order to succeed in its activities:
- ohelloweuqq.com;
- hpalsowantsff.com;
- sahasafe.com using port 80;
- thisisitsqq.com.
JS.Nemucod might be set to perform multiple activities. Trojan viruses are capable of stealing personal information about the user. This might result in identity theft and you might find your important data put up for sale on some dark web markets. Continuously, the malware might access the technical data of your computer to remotely connect to it.
Remote connection gives JS.Nemucod the possibility to monitor various activities and alter system settings. The Trojan virus can run secret processes in the background, start damaging your programs and services, disabling your antimalware software, and assuring that it launches newly every time the user turns on the computer system.
This trojan is a very dangerous threat and holds the harm level of very high. Be careful while dealing with this parasite and remove JS.Nemucod as soon as possible. Also, check your system for additional malware that the trojan might have installed and be aware that alterings might have been made to multiple directories of your Windows computer.
Signs that indicate the computer is infected with JS.Nemucod virus
JS.Nemucod, just like other Trojan viruses might not show any accurate signs at first and antimalware alerts might be the only way to recognize the malware. However, if you are a more accurate computer user, you might spot some symptoms that indicate the infection. These signs can be the following:
- The computer runs incredibly slow because of high CPU usage;
- Programs cannot be opened or crash soon after the user launches them;
- Minimizing and maximizing windows has become an annoying process due to constant freezes;
- Intrusive and aggressive pop-ups show up on the screen, even if the user does not browse the Internet; typically, they announce that the computer is severely infected and suggest to install rogue anti-malware program to “fix” all problems;
- Web browsers act suspicious; the user experiences multiple unexpected redirects to questionable web pages;
- You discover unnoticed or doubled processes running in the Task Manager section;
- The Windows Registry is filled with unknown entries.
Unfortunately, it is very hard to detect and remove JS.Nemucod virus manually, because this threat tends to mask itself under unsuspicious and safe-looking names. What is more, this Trojan can disable computer security programs and pass through Windows Firewall and antivirus programs. To remove this threat, we strongly advise you to scan your computer with a powerful malware removal tool that is capable of detecting this virus.
Continuously, JS.Nemucod might scatter malicious objects all over the system. If you want to get rid of the Trojan virus permanently, you have to eliminate not only the malware itself but all the additional content that has been added by the virus. Also, try detecting all compromised objects as they might require fixing. If you spot any damaged components, you can try repairing them with system repair software such as FortectIntego.
Trojan delivery techniques
Trojans, unlike viruses, do not spread by themselves. They can only be installed manually. Usually, cybercriminals spread Trojan horses via email or messages on social media websites, peer-to-peer file-sharing programs, or simply place its download link in insecure websites.
However, the most popular and efficient way to spread this virus is to send it directly to the victim via email. Cybercriminals send deceptive messages that usually urge the victim to open the email attachment, often disguised as an official document, for instance, court notice, invoice, resume, or a bill. Also, note that trojans are mostly distributed via files that include the .zip and .exe appendix.
Email service providers usually automatically filtrate such messages as Junk/Spam, however, some deceptive emails might successfully pass through Spam filters. Before you open any email letter, check if you recognize the sender of it. If you don’t, you should not open such emails or files that come with them.
Continuously, always have reputable antimalware working on your Windows computer and keep the program regularly updated. Experts from Virusai.lt[4] state that every user has to make sure that the antivirus software that he/she employs includes as many protective features as possible, e.g. safe browsing, threat detection, malware removal, pushing warnings when something bad occurs, etc.
Removing JS.Nemucod virus
Unfortunately, it is nearly impossible to remove JS.Nemucod manually. It is a complex computer virus, which uses advanced techniques and manages to conceal its components in the computer system ably so that the victim would not find them. So if you have noticed that your computer acts suspiciously, or that some files or programs are missing, and the overall system’s performance has decreased, you should install a reputable anti-malware program.
Use the tool for complete JS.Nemucod removal and get rid of all of the additional content and other parasites that the malware might have brought to the computer system during the infection process. Afterward, scan the entire system for compromised objects by using SpyHunter 5Combo Cleaner or Malwarebytes. When the program detects all of the components, try repairing the damaged products by employing a program such as FortectIntego.
If you find JS.Nemucod virus hard to eliminate because of the malicious processes that it has been initiating or if the parasite has been blocking your antivirus, you can diminish all malicious alterings by completing the following steps:
Getting rid of JS.Nemucod. Follow these steps
Manual removal using Safe Mode
Boot your Windows computer to Safe Mode with Networking and get rid of all malicious changes.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove JS.Nemucod using System Restore
Get rid of suspicious alterings and disable the virus by activating System Restore.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of JS.Nemucod. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from JS.Nemucod and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ JS/Nemucod. Microsoft Security Intelligence.
- ^ JS.Nemucod. Symantec. Security Center.
- ^ WordPress. Wikipedia. The free encyclopedia.
- ^ Virusai.lt. Virusai. Security and spyware news.







