Ovo ransomware (Virus Removal Guide) - Free Instructions
Ovo virus Removal Guide
What is Ovo ransomware?
Ovo ransomware – a cryptocurrency demanding file-locking parasite

Ovo ransomware is a cryptovirus that locks all personal victim files and demands a ransom through generated notes, text files titled FILES ENCRYPTED.txt, and a pop-up window. All non-system files, such as pics, audios, videos, archives, etc., are also renamed by appending a unique user ID, one email of the criminals, and a .OVO extension. If you had a file named a.pdf, it would now appear as a.pdf.id-XXXXXXXX.[dable19@mail.fr].OVO. Renamed files are inaccessible, but their contents aren't changed.
Ovo file virus belongs to one of the biggest ransomware families that are threatening everyday computer users. That family is called Dharma, and it's been active since 2016. All file-lockers from this lineage bear many similarities, of them being the title of the ransom notes, but there are many differences too. For instance, each cryptovirus has different criminal contact details. In this case, it's dable19@mail.fr and airbusbtc@goat.si.
Usually, files can't be restored without the intervention of the assailants. But ransomware attack victims shouldn't succumb to their demands as there might be other data recovery options. The most important thing to do after such an attack is not to make rash decisions and remove the infection. This article provides a detailed summary of the culprit and the most effective ways to get rid of it and restore your device to a pre-contamination phase.
| name | Ovo ransomware |
|---|---|
| Type | Cryptovirus, File-locker |
| Family | Dharma |
| Ransom note | FILES ENCRYPTED.txt text files found in affected folders, and a pop-up window |
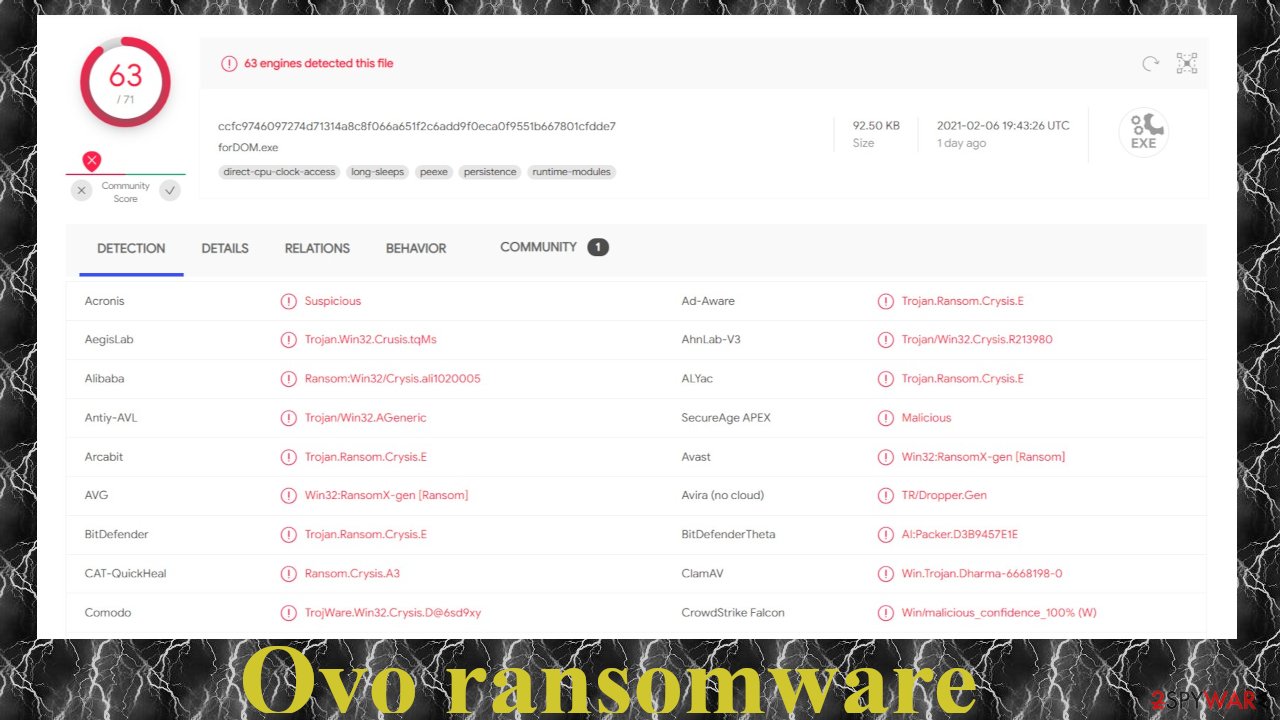
| Detection names | Win32:RansomX-gen [Ransom], TrojWare.Win32.Crysis.D@6sd9xy, Ransom.Crysis, Ransom:Win32/Wadhrama!hoa, Trojan.GenAsa!PU4zXkABPRE[1] |
| Appended file extension | All files are renamed by adding .id-XXXXXXXX.[dable19@mail.fr].OVO extension (X's stand for a unique user ID) to their default names |
| criminal contact details | dable19@mail.fr and airbusbtc@goat.si |
| Distribution | Malspam,[2] file-sharing platforms, deceptive ads, fake updates |
| Malware removal | The only safe way to get rid of any ransomware is to eliminate it with trustworthy anti-malware software |
| System health fix | Users should use powerful system repair tools like the FortectIntego or similar to restore altered system settings/files/values |
As mentioned before, Ovo ransomware virus stems from the Dharma family, which is one of the most active among all ransomware families. New file-locking parasites from this lineage are developed each week. Here are a few examples of the latest versions:
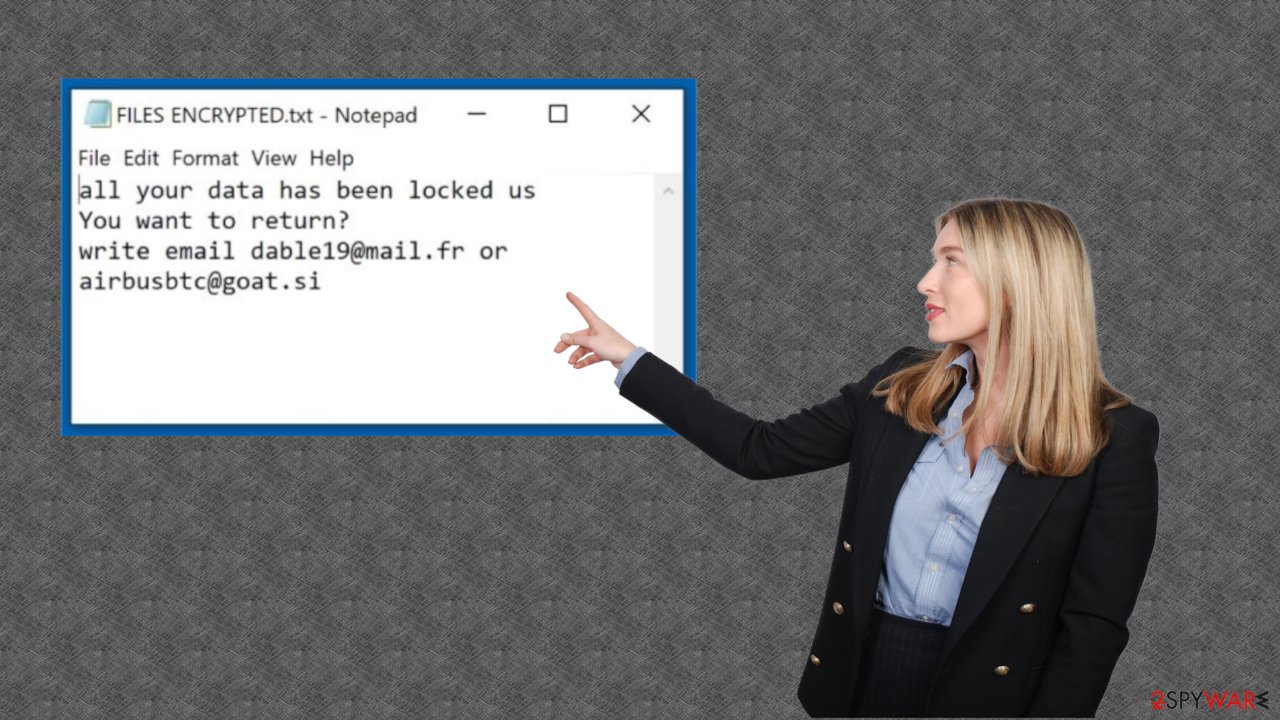
Ransom note in the text file is, as always, short and bears two emails to establish contact with the cybercriminals:
all your data has been locked us
You want to return?
write email dable19@mail.fr or airbusbtc@goat.si
Whereas the message in the pop-up window is a bit more enlightening. It contains the same two emails and some threats. Victims are told not to try any third-party decryption software to unlock the data and not to rename any files as that may lead to permanent data loss. The whole message states:
YOUR FILES ARE ENCRYPTED
Don't worry,you can return all your files!
If you want to restore them, follow this link:email dable19@mail.fr YOUR ID –
If you have not been answered via the link within 12 hours, write to us by e-mail:airbusbtc@goat.siAttention!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
Ransomware attacks are on the rise as researchers predict[3] that in 2021 ransomware damage will cost $20 billion globally. Therefore, you should have a trustworthy security tool watching your back. We recommend installing either SpyHunter 5Combo Cleaner or Malwarebytes to automatically remove Ovo ransomware and protect your devices from such malware in the future.
Eliminating the cyber threats from your devices is the only responsible thing to do, as the only way to stop ransomware attacks is by not paying the cybercriminals. If people would stop paying the ransom, the criminals would go broke and wouldn't have the money to orchestrate more attacks.
Cryptoviruses often modify various system settings and its files. So to finish Ovo ransomware removal, you'll have to do one more thing – perform a full system scan with powerful repair tools. Experts from ZonderVirus.nl[4] highly recommend using the FortectIntego app for this task.
Improve security to avoid becoming a victim
Until victims of ransomware attacks, whether regular people or companies won't stop paying cybercriminals for their decryption tools, the attacks won't stop. That's why you have to take care of your cybersecurity to avoid becoming a victim of a cybercrime.
We're here to help. Below are guidelines that will exponentially increase your cybersecurity level and, if followed, will safeguard your safety, your privacy, and your hard-earned money:
- Every device that's regularly connected to the internet must have a trustworthy anti-malware tool.
- All software, in particular the operating system, must be up-to-date.
- Backups of all sensitive, crucial data should be stored on two devices, one of which should be offline storage.
- System repair tools should be used regularly to keep system settings and files updated and fresh.
- People should learn how to identify malware and the most popular distribution methods (like spam emails, deceptive ads, file-sharing platforms, etc.) by reading our articles on Googling.
Remove Ovo ransomware virus automatically with reliable anti-malware tools
If your device got infected with Ovo file virus – that's not the end of the world. Your machine can be restored and you'll be able to use it again normally. Before beginning the file-locker elimination process you have to export all crucial encrypted files to an external offline storage device as there are no decryption tools available at the moment.
Only then you can begin Ovo ransomware removal. If you had a security tool by the cryptovirus slipped by its defenses, then you need an upgrade. We recommend using trustworthy anti-malware software such as SpyHunter 5Combo Cleaner or Malwarebytes. Keep its virus databases updated at all times so it could stop the latest malware from infecting your device.
Once you remove Ovo ransomware with a security tool, you must perform a system tune-up to restore any altered system settings. Malware does that to establish persistence and prolong its unwelcomed stay. The best system repair software for this task is the powerful FortectIntego app.
Getting rid of Ovo virus. Follow these steps
Important steps to take before you begin malware removal
File encryption and ransomware infection are two independent processes (although the latter would not be possible without the former). However, it is important to understand that malware performs various changes within a Windows operating system, fundamentally changing the way it works.
IMPORTANT for those without backups! →
If you attempt to use security or recovery software immediately, you might permanently damage your files, and even a working decryptor then would not be able to save them.
Before you proceed with the removal instructions below, you should copy the encrypted files onto a separate medium, such as USB flash drive or SSD, and then disconnect them from your computer. Encrypted data does not hold any malicious code, so it is safe to transfer to other devices.
The instructions below might initially seem overwhelming and complicated, but they are not difficult to understand as long as you follow each step in the appropriate order. This comprehensive free guide will help you to handle the malware removal and data recovery process correctly.
If you have any questions, comments, or are having troubles with following the instructions, please do not hesitate to contact us via the Ask Us section.
IMPORTANT! →
It is vital to eliminate malware infection from the computer fully before starting the data recovery process, otherwise ransomware might re-encrypt retrieved files from backups repeatedly.
Identify ransomware affecting your PC
Modern-day ransomware had its roots in the early 2010s when cybercriminals began to understand the potential it has for money extortion. Over the years, thousands of new ransomware strains have been developed and spread all over the world, infecting regular consumers, small businesses, and high-profile organizations.
Because of the lucrative nature of ransomware, cybercriminals are creating new ransomware versions in the hopes of establishing themselves in this illegal business. Ransomware often uses different extensions, ransom notes, and other attributes that it can be identified by. However, quite often, this information can overlap or simply not be available, so identifying the threat might be difficult.
In order to deal with ransomware infection effectively, you must first identify it. Here are a few examples of how to determine the precise ransomware you are dealing with:
File extension
Almost all modern ransomware viruses are using extensions that are appended at the end of the original filenames. However, this is not a rule, and in some cases, cybercriminals change the name by replacing it with randomly generated characters, add the marker before the file name, or do not visually change the name of the file at all.
Here you can see an example of a unique extension .hhmgzyl that belongs to the Snatch ransomware family:
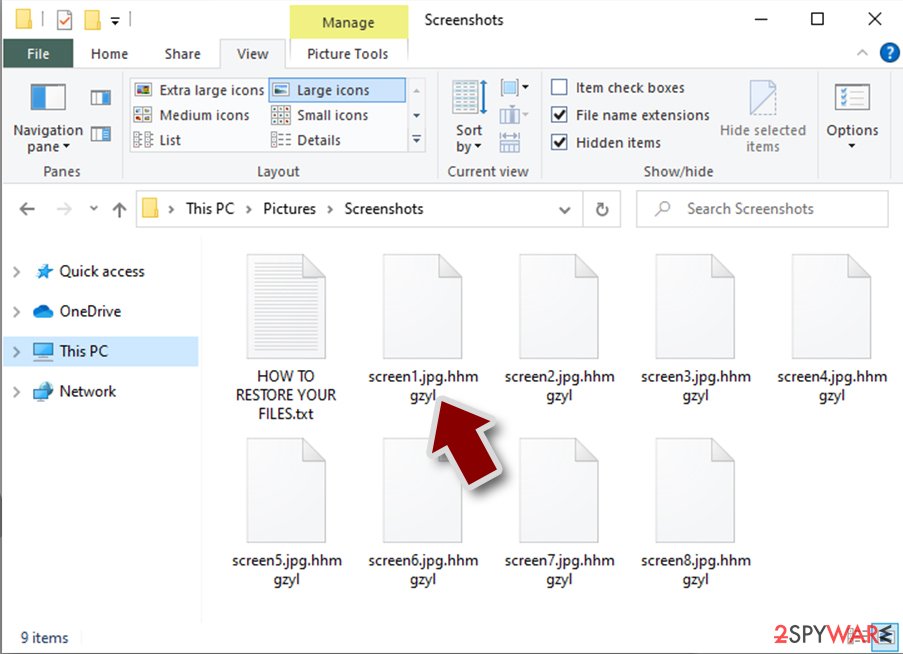
If your files are appended with .exe, .locked, .encrypted, or other broadly-used extensions that are difficult to identify, proceed with the next step.
Ransom note
Ransomware family might sometimes be identified by the ransom note it uses. In most cases, cybercriminals create a simple .txt file and place it on users' desktops or other places that are easily reachable (typically, where the encrypted data is located). Other times, a pop-up window can also be used, which is launched as soon as the encryption is complete. In some cases, threat actors name the ransomware within this note:
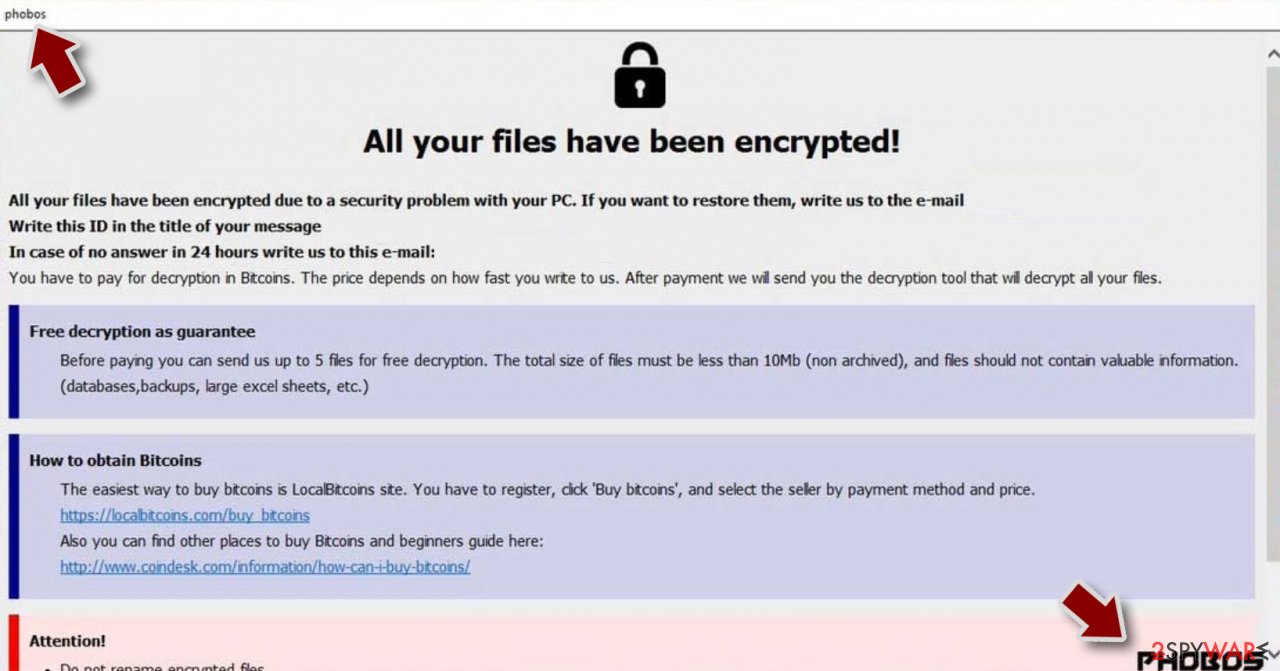
In some cases, it is possible to identify ransomware by its ransom note name, but they are typically very generic (e.g., FILES ENCRYPTED.txt, _readme.txt) and used by different cybercriminals groups.
Free ID Ransomware service
ID Ransomware is a free service that can easily let users identify the precise malware they are dealing with. All you have to do is upload the ransom note that can be found on the desktop and within folders where encrypted files are located and the sample of an encrypted file.
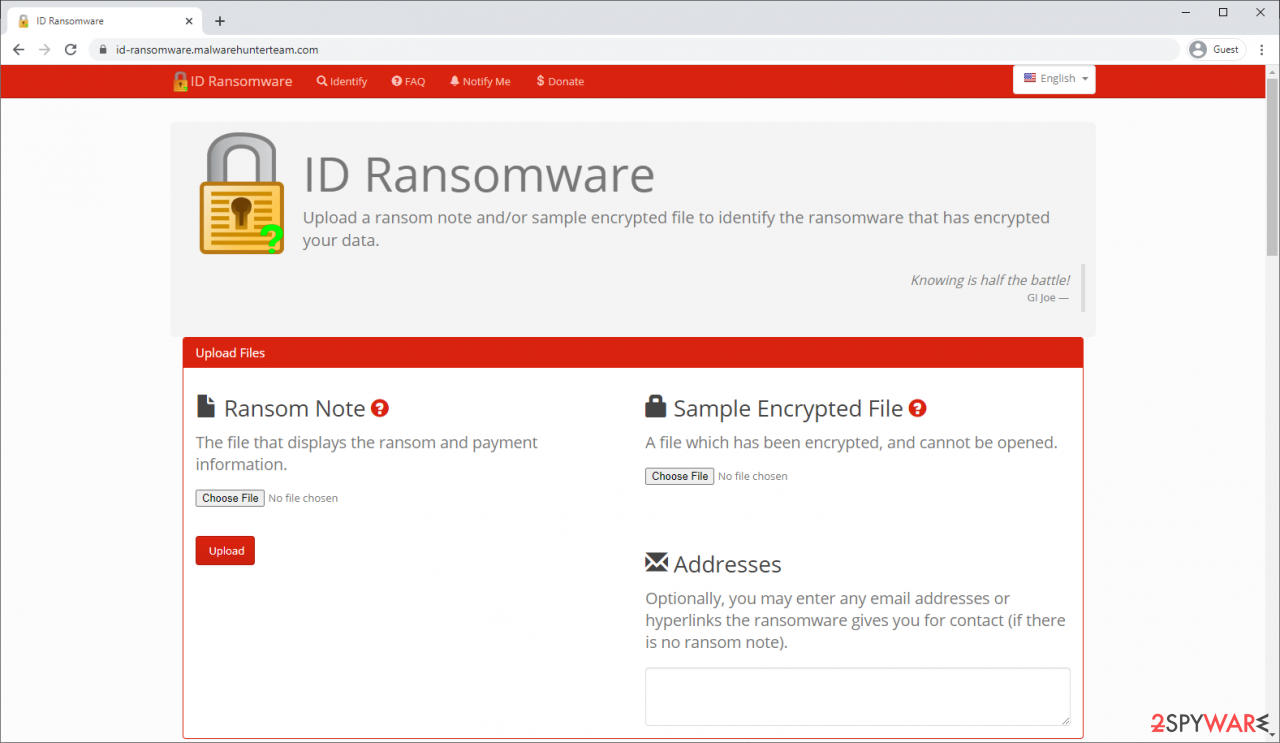
Soon after uploading the required files, you will be provided with all the relevant information, including what family ransomware belongs to and whether or not it is possible to decrypt files.
If none of the above helped you to identify which ransomware you are dealing with, you should use keywords (extension, contact email, ransom note contents, crypto-wallet address, etc.) to find the information on the internet.
Scan your system with anti-malware
If you are a victim of ransomware, you should employ anti-malware software for its removal. Some ransomware can self-destruct after the file encryption process is finished. Even in such cases, malware might leave various data-stealing modules or could operate in conjunction with other malicious programs on your device.
SpyHunter 5Combo Cleaner or Malwarebytes can detect and eliminate all ransomware-related files, additional modules, along with other viruses that could be hiding on your system. The security software is really easy to use and does not require any prior IT knowledge to succeed in the malware removal process.
Restore files using data recovery software
Since many users do not prepare proper data backups prior to being attacked by ransomware, they might often lose access to their files permanently. Paying criminals is also very risky, as they might not fulfill the promises and never send back the required decryption tool.
While this might sound terrible, not all is lost – data recovery software might be able to help you in some situations (it highly depends on the encryption algorithm used, whether ransomware managed to complete the programmed tasks, etc.). Since there are thousands of different ransomware strains, it is immediately impossible to tell whether third-party software will work for you.
Therefore, we suggest trying regardless of which ransomware attacked your computer. Before you begin, several pointers are important while dealing with this situation:
- Since the encrypted data on your computer might permanently be damaged by security or data recovery software, you should first make backups of it – use a USB flash drive or another storage.
- Only attempt to recover your files using this method after you perform a scan with anti-malware software.
Install data recovery software
- Download Data Recovery Pro.
- Double-click the installer to launch it.

- Follow on-screen instructions to install the software.

- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.

- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.

- Press Scan and wait till it is complete.

- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.

Find a working decryptor for your files
File encryption is a process that is similar to applying a password to a particular file or folder. However, from a technical point of view, encryption is fundamentally different due to its complexity. By using encryption, threat actors use a unique set of alphanumeric characters as a password that can not easily be deciphered if the process is performed correctly.
There are several algorithms that can be used to lock data (whether for good or bad reasons); for example, AES uses the symmetric method of encryption, meaning that the key used to lock and unlock files is the same. Unfortunately, it is only accessible to the attackers who hold it on a remote server – they ask for a payment in exchange for it. This simple principle is what allows ransomware authors to prosper in this illegal business.
While many high-profile ransomware strains such as Djvu or Dharma use immaculate encryption methods, there are plenty of failures that can be observed within the code of some novice malware developers. For example, the keys could be stored locally, which would allow users to regain access to their files without paying. In some cases, ransomware does not even encrypt files due to bugs, although victims might believe the opposite due to the ransom note that shows up right after the infection and data encryption is completed.
Therefore, regardless of which crypto-malware affects your files, you should try to find the relevant decryptor if such exists. Security researchers are in a constant battle against cybercriminals. In some cases, they manage to create a working decryption tool that would allow victims to recover files for free.
Once you have identified which ransomware you are affected by, you should check the following links for a decryptor:
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

If you can't find a decryptor that works for you, you should try the alternative methods we list below. Additionally, it is worth mentioning that it sometimes takes years for a working decryption tool to be developed, so there are always hopes for the future.
Create data backups to avoid file loss in the future
One of the many countermeasures for home users against ransomware is data backups. Even if your Windows get corrupted, you can reinstall everything from scratch and retrieve files from backups with minimal losses overall. Most importantly, you would not have to pay cybercriminals and risk your money as well.
Therefore, if you have already dealt with a ransomware attack, we strongly advise you to prepare backups for future use. There are two options available to you:
- Backup on a physical external drive, such as a USB flash drive or external HDD.
- Use cloud storage services.
The first method is not that convenient, however, as backups need to constantly be updated manually – although it is very reliable. Therefore, we highly advise choosing cloud storage instead – it is easy to set up and efficient to sustain. The problem with it is that storage space is limited unless you want to pay for the subscription.
Using Microsoft OneDrive
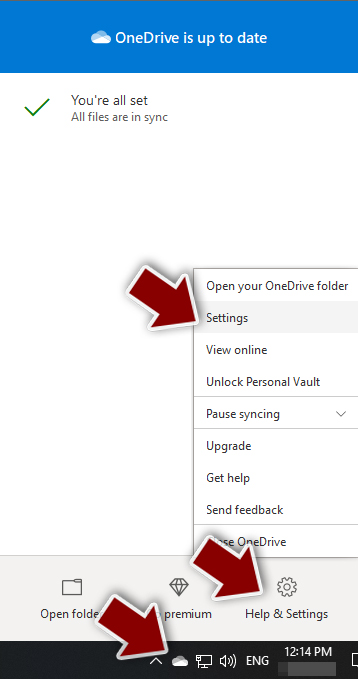
OneDrive is a built-in tool that comes with every modern Windows version. By default, you get 5 GB of storage that you can use for free. You can increase that storage space, but for a price. Here's how to setup backups for OneDrive:
- Click on the OneDrive icon within your system tray.
- Select Help & Settings > Settings.
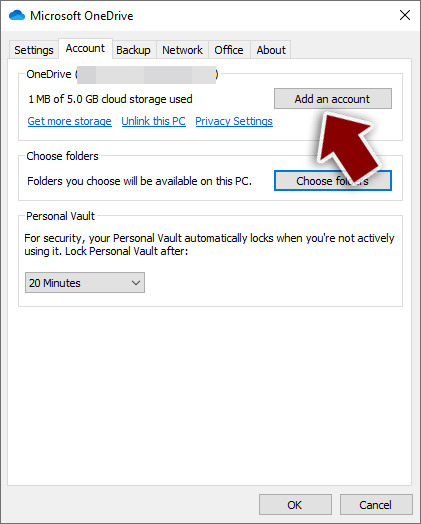
- If you don't see your email under the Account tab, you should click Add an account and proceed with the on-screen instructions to set yourself up.
- Once done, move to the Backup tab and click Manage backup.
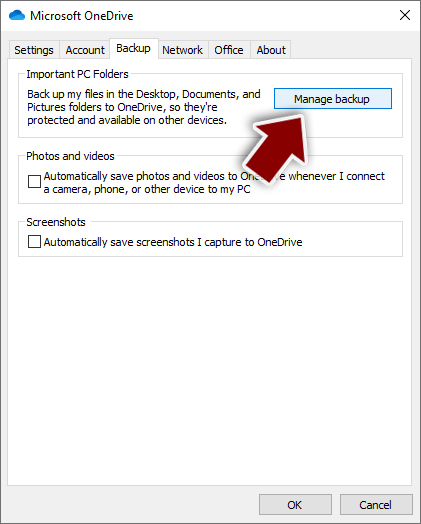
- Select Desktop, Documents, and Pictures, or a combination of whichever folders you want to backup.
- Press Start backup.
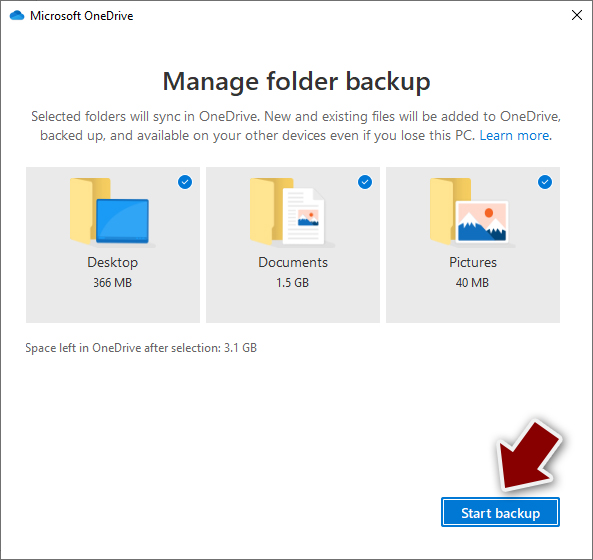
After this, all the files that are imported into the above-mentioned folders will be automatically backed for you. If you want to add other folders or files, you have to do that manually. For that, open File Explorer by pressing Win + E on your keyboard, and then click on the OneDrive icon. You should drag and drop folders you want to backup (or you can use Copy/Paste as well).
Using Google Drive
Google Drive is another great solution for free backups. The good news is that you get as much as 15GB for free by choosing this storage. There are also paid versions available, with significantly more storage to choose from.
You can access Google Drive via the web browser or use a desktop app you can download on the official website. If you want your files to be synced automatically, you will have to download the app, however.
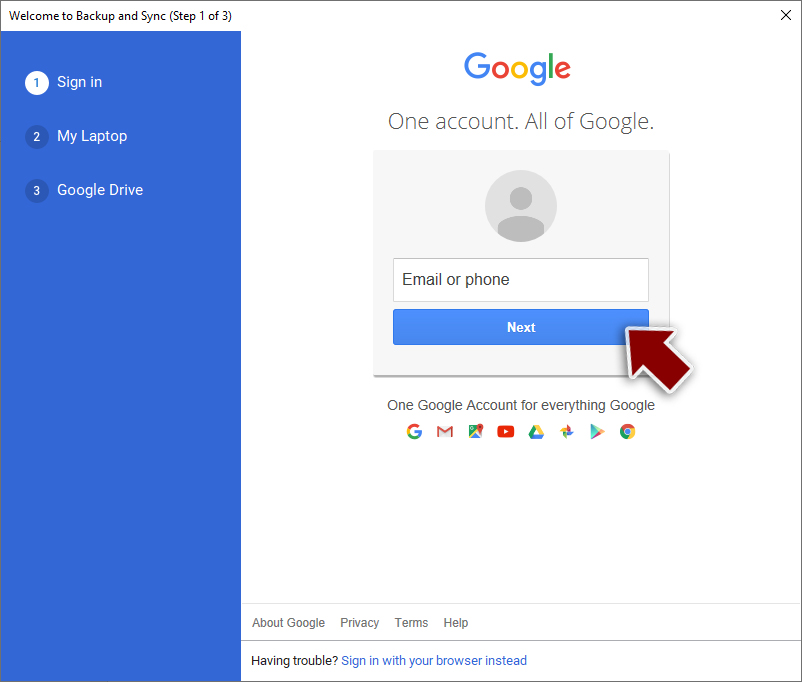
- Download the Google Drive app installer and click on it.

- Wait a few seconds for it to be installed.
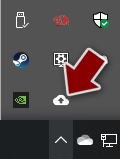
- Now click the arrow within your system tray – you should see Google Drive icon there, click it once.
- Click Get Started.
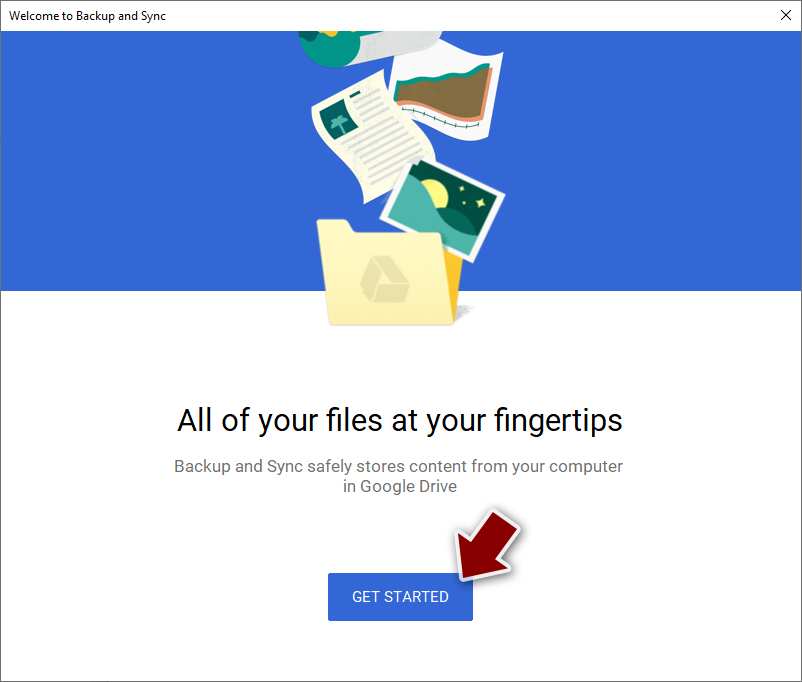
- Enter all the required information – your email/phone, and password.
- Now pick what you want to sync and backup. You can click on Choose Folder to add additional folders to the list.
- Once done, pick Next.
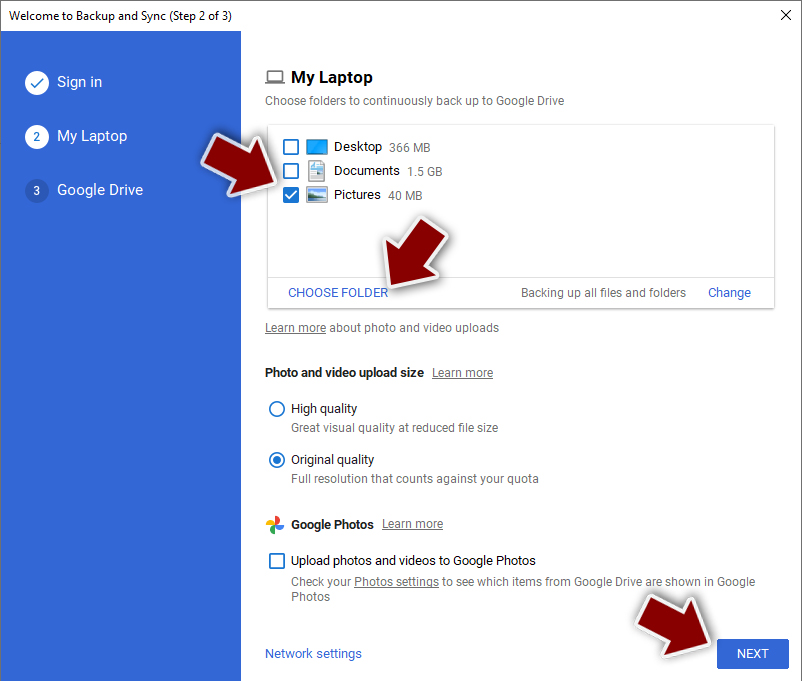
- Now you can select to sync items to be visible on your computer.
- Finally, press Start and wait till the sync is complete. Your files are now being backed up.
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Ovo and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ VirusTotal. Virustotal. Suspicious file analysis.
- ^ Catalin Cimpanu. Most malspam contains a malicious URL these days, not file attachments. Zdnet. Technology news, analysis and comments.
- ^ Steve Morgan. Global Ransomware Damage Costs Predicted To Reach $20 Billion (USD) By 2021. Cybersecurityventures. Cybercrime magazine.
- ^ ZonderVirus. Zondecvirus. Spyware and security news.
