22btc ransomware (Virus Removal Guide) - Improved Instructions
22btc virus Removal Guide
What is 22btc ransomware?
22btc ransomware – a cryptovirus that leaves FILES ENCRYPTED.txt ransom note after encrypting victim' files
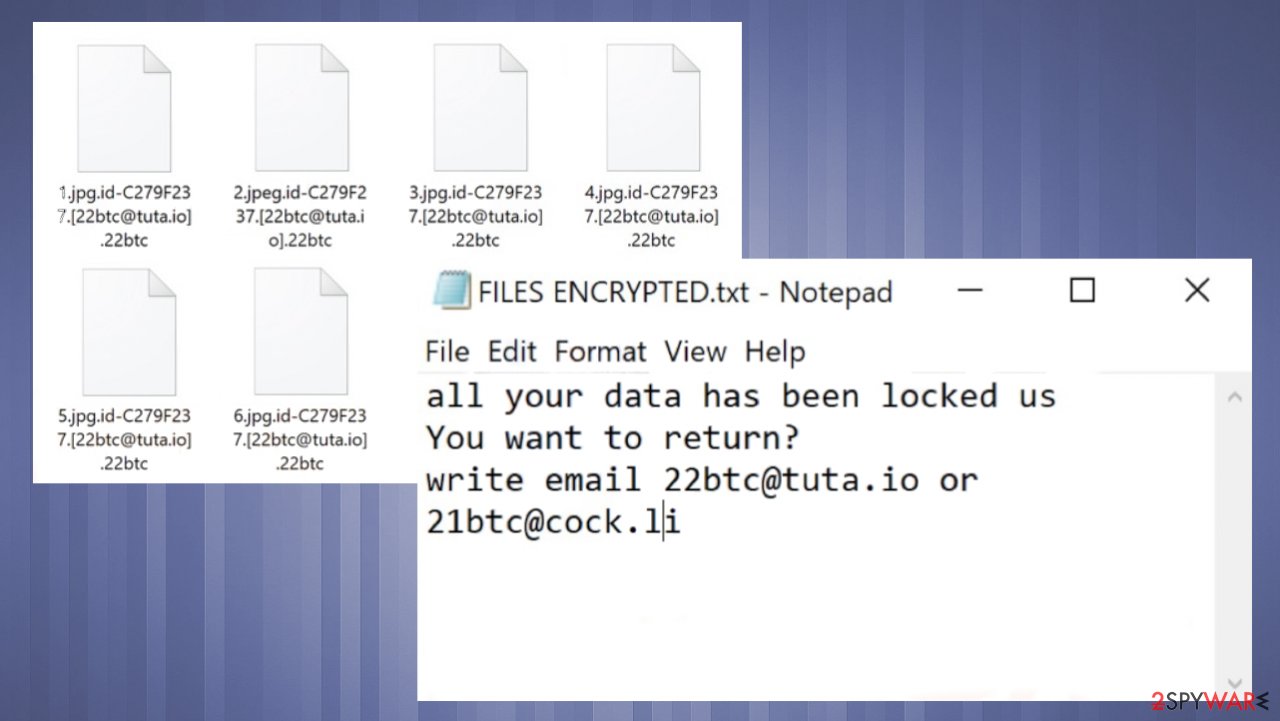
22btc ransomware is a computer infection that demands to purchase a decryption tool after it encodes all personal data on a contaminated computer. The file-locker also renames all files by appending a unique user ID, criminals' email address, and .22btc extension to all original filenames. If you had a file named a.pdf, it would now appear as a.pdf.id-XXXXXXXX.[22btc@tuta.io].22btc.
Locked data contents aren't changed, but users can't access them until a specific decryption key or tool is used. Usually, only threat actors behind the attack can unlock the files. But in no way does that mean that victims should give in to their demands. There are other options, and you came to the right place to find out how to eliminate this cyber infection and learn more about it.
When files are encrypted and renamed, 22btc ransomware virus generates two ransom notes, a pop-up window, and a FILES ENCRYPTED.txt text file. Such notes' main purpose is to convince victims that there are no other chances of regaining access to data apart from paying the criminals. This cryptovirus belongs to the Dharma ransomware family, which is constantly spewing new versions like the 14x virus, Hub virus, yoAD virus, and a myriad of others.
| name | 22btc ransomware |
|---|---|
| type | Cryptovirus, file-locking virus |
| Family | Dharma/CrySis ransomware |
| Appended file extension | .id-XXXXXXXX.[22btc@tuta.io].22btc extension is added to all non-system data |
| Ransom note | A pop-up window and a FILES ENCRYPTED.txt text file |
| Distribution | Deceptive ads, file-sharing platforms, malspam |
| Criminal contact details | 22btc@tuta.io and 21btc@cock.li |
| threat removal | All malware, including the culprit of this article, should be removed with a professional anti-malware tool to ensure a proper elimination |
| System health | Ransomware usually makes various alterations to system files that could cause abnormal behavior such as crashing, freezing, BSoD, and alike. Restore your system with the FortectIntego system repair tool |
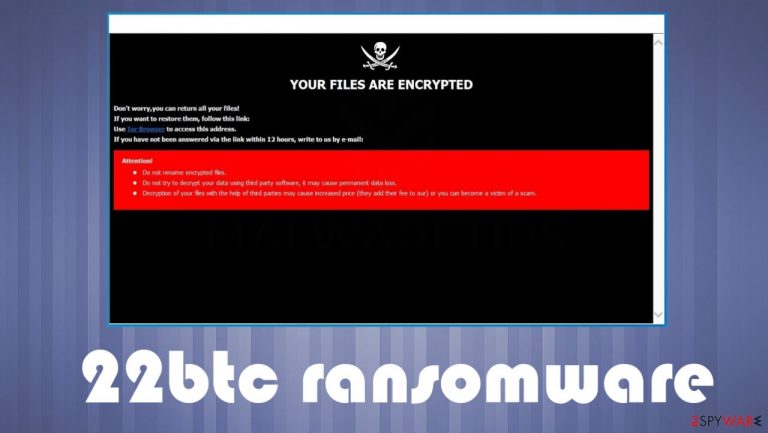
Apart from using similar coding algorithms for data encryption, Dharma family ransomware has one more indisputable similarity – their ransom notes. Text ones are always short and contain two email addresses for victims to get in touch with their assailants. Pop-up windows have a bit more info. Here's the message from the pop-up ransom note of 22btc virus:
YOUR FILES ARE ENCRYPTED
Don't worry,you can return all your files!
If you want to restore them, follow this link:email 22btc@tuta.io YOUR ID –
If you have not been answered via the link within 12 hours, write to us by e-mail:21btc@cock.liAttention!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
Text presented in the FILES ENCRYPTED.txt ransom note:
all your data has been locked us
You want to return?
write email 22btc@tuta.io or 21btc@cock.li
As you can see, developers of 22btc ransomware virus don't put much effort into the ransom notes. If victims would write a letter to any given email – 22btc@tuta.io or 21btc@cock.li, they could find out the price, preferred payment method, and other ransom details.
But please don't do that. Many cybersecurity experts agree[1] that the only way to stop ransomware from spreading is by stopping the cash flow, i.e., cease paying ransoms. So no matter how much you need your files back, how little the ransom sum might be, or whatever the case is – don't forward a dime to the cybercriminals.

Instead, remove 22btc ransomware from infected Windows devices. Best results are achieved when doing so with a trustworthy anti-malware tool like SpyHunter 5Combo Cleaner or Malwarebytes. According to reports from VirusTotal.com[2], 60 out of 69 AV engines caught the cryptovirus and prevented their systems from infection and encryption. Here are a few examples of its detection names:
- Ransom:Win32/Wadhrama!hoa
- Ransom.Crysis
- Win32:RansomX-gen [Ransom]
- Trojan.GenAsa!PU4zXkABPRE
- Trj/GdSda.A.
To finish 22btc ransomware removal, you will have to use one more tool – a system repair app. If you don't own one, we highly advise getting the powerful FortectIntego system tune-up app. It will refresh your Windows files, restore all corrupted registry entries, and take care of other system irregularities.
Precautions that could save time and money
Ransomware attacks have been around for decades, and they aren't going away anytime soon. And although tech giants try to make the web a safer place, it's really tough to keep up with cybercriminals. Therefore, home users have to take matters into their own hands and increase their cybersecurity level.
Our team has compiled a list of guidelines that would help do that. Please follow these directions so ransomware and other malware couldn't cause you any nightmares:
- Purchase a professional anti-malware service and update its virus database regularly.
- Acquire a powerful system tool that would keep your system files and settings in order and your device clean.
- Learn about file-sharing platforms, deceptive ads, spam emails, and other techniques used by cybercriminals to distribute their creations.
- Keep backups of all essential data on two separate devices, e.g., cloud, USB drive, offline HDD storage, etc.
- Install the latest updates to your operating system and other software.
Remove 22btc ransomware virus once and for all with reliable anti-malware tools
If you've spotted any of the symptoms that your device might be infected with 22btc ransomware virus, you have to take action immediately. First of all, copy all important files to an offline storage device. There's no decryptor available now, but it might be developed in the near future.
Then, if you had security software, but it failed you, get a trustworthy anti-malware tool. We recommend either SpyHunter 5Combo Cleaner or Malwarebytes. Either of these apps will automatically remove 22btc ransomware along with other questionable files. Keep virus databases of such apps updated to prevent cyberattacks in the future.
System repair tools are needed to finalize 22btc ransomware removal and restore your system to a pre-contamination phase. Cybersecurity experts from NoVirus.uk,[3] highly recommend downloading and using the FortectIntego system tune-up tool for this assignment.
Getting rid of 22btc virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove 22btc using System Restore
System Restore might be capable of removing infections
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of 22btc. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove 22btc from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by 22btc, you can use several methods to restore them:
Retrieve lost files with Data Recovery Pro
This app might help to recover 22btc files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by 22btc ransomware;
- Restore them.
Restore individual files with Windows Previous Version feature
With this feature, users might be able to restore .22btc extension files one at a time.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Using Shadow Explorer for data recovery
This open-source app might recover old copies of files from Shadow Volume Copies if they weren't removed during the encryption.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryption tool is currently available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from 22btc and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Aaron Holmes. Ransomware attacks are increasing at an unprecedented rate — and the US is now begging people not to pay ransoms. Insider. American financial and business news website.
- ^ VirusTotal. Virustotal. Suspicious file analysis.
- ^ NoVirus. Novirus. Spyware and security news.







