Page Links Loader adware (virus) - Free Guide
Page Links Loader adware Removal Guide
What is Page Links Loader adware?
Page Links Loader extension can cause unwanted pop-up ads, redirects, or browser settings
Page Links Loader is advertised as a tool for quickly accessing all links on a web page, but it also displays ads. These ads, which are symptoms of adware,[1] can lead to dangerous websites such as technical support scam pages, phishing sites, and sites offering potentially unwanted apps.[2]
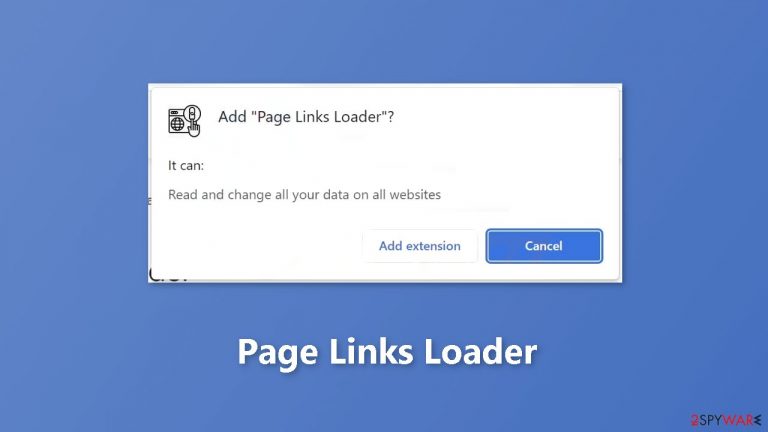
The app attaches itself as a browser extension, which gives it permission to collect and use personal information from users, which may be sold or used for marketing. This is why it is not recommended to use or keep Page Links Loader on your device. You can keep reading our guide to learn how to remove it.
| NAME | Page Links Loader |
| TYPE | Adware |
| SYMPTOMS | Annoying pop-ups and other types of advertisements start appearing on the screen |
| DISTRIBUTION | Shady websites, deceptive ads, freeware installations |
| DANGERS | Links embedded in the ads might lead to dangerous websites |
| ELIMINATION | Eliminate the extension through your browser settings; scanning the machine with anti-malware tools is recommended |
| FURTHER STEPS | Use FortectIntego to get rid of any remaining damage and optimize the machine |
Distribution methods
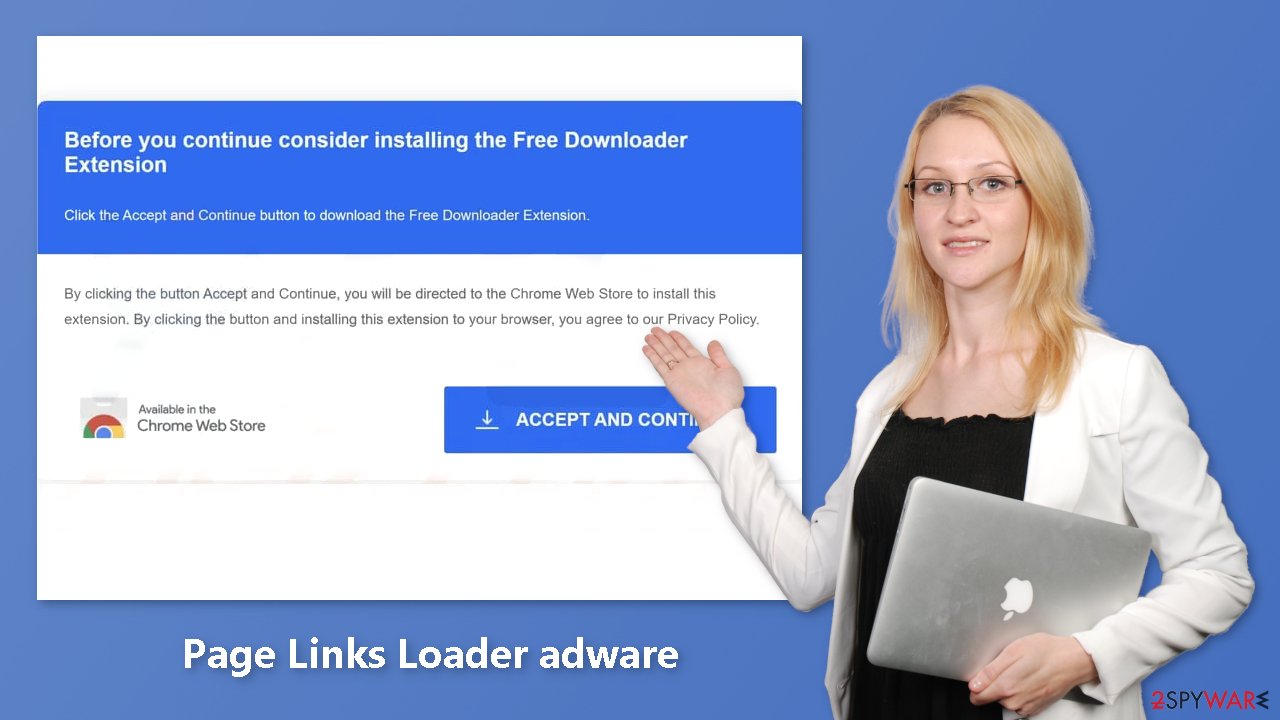
Page Links Loader was found on a suspicious website, where visitors were instructed to click “ACCEPT AND CONTINUE” to download the browser extension. Page Links Loader is added to a web browser after following the provided steps. Once installed, the app is able to display ads on the web pages visited by the user.
Another common tactic used to trick users into installing adware is by bundling it with other software. This additional software can often be found by choosing the “Advanced,” “Custom,” or similar settings during the installation process. If users do not change these settings, they may inadvertently install adware and other unwanted apps. This can cause the user's device to slow down, display unwanted pop-ups, or even infect the device with malware.
Additionally, ads on sketchy websites and notifications from these sites can also result in unwanted downloads and installations of adware. This can be especially dangerous for users who may not be aware of the risks associated with these types of apps. Because of these risks, users should be cautious when downloading or installing any apps or browser extensions from untrusted sources.
Social engineering tactics
Social engineering is a tactic used by cybercriminals to trick people into giving away personal information, installing malware, or performing other actions that benefit the attacker. Online, social engineering can take many forms, including phishing emails, fake software update prompts, and malicious ads.
One popular form of social engineering online is the use of fake software update prompts. These prompts may appear to be from legitimate software companies and may instruct the user to download and install an update to fix a security vulnerability. However, the update is actually malware in disguise. Once installed, it can give the attacker access to the user's personal information, login credentials, and other sensitive data.
Remove Page Links Loader adware
Page Links Loader adware can be removed by going to the browser settings and looking at the extension list. We recommend removing plugins one by one to see if you notice any changes.
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Adware. Malwarebytes. Cybersecurity Basics.
- ^ Potentially unwanted program. Wikipedia, the free encyclopedia.
- ^ Dusan Vasic. What Are Cookies? The Good and the Bad of Browser Cookies. Dataprot. Security Solutions.










