Panda Banker (Removal Guide) - Free Instructions
Panda Banker Removal Guide
What is Panda Banker?
Panda Banker Trojan switches its target to Japanese institutions

Panda Banker is a Trojan horse, which has been released in 2016. It's based on the Zeus Trojan, which has been treated as one of the most hazardous infections since 2007. Following the leak of its source code,[1] hackers started developing new strains of Zeus, and Panda Banker is one of them. It targets financial institutions in Italy, Canada, Australia, Germany, the United States, the United Kingdom, Japan, and Latin America. The 78%[2] of institutions targeted are US and Canada banks, cryptocurrency websites, global social media providers, payroll, and tech providers. Disguised under malicious Microsoft Word attachments, Panda Banker injects a code that performs region-specific man-in-the-browser attacks and starts acquiring the most sensitive data.
| Name | Panda Banker |
|---|---|
| Also known as | Zeus Panda, BandaBot |
| Classification | Banking Trojan |
| Relation | It's a strain of Zeus Trojan |
| Countries targeted | Italy, Canada, Australia, Germany, the United States, the United Kingdom, Japan, and Latin America |
| Distribution | Spam email attachments, exploit kits (Rig, Seamless), CVE-2014-1761 and CVE-2012-0158 vulnerabilities, phishing websites, etc. |
| Removal | There's no other way to get rid of a Trojan as to scan the system with a powerful anti-virus. In this case, we recommend using FortectIntego. |
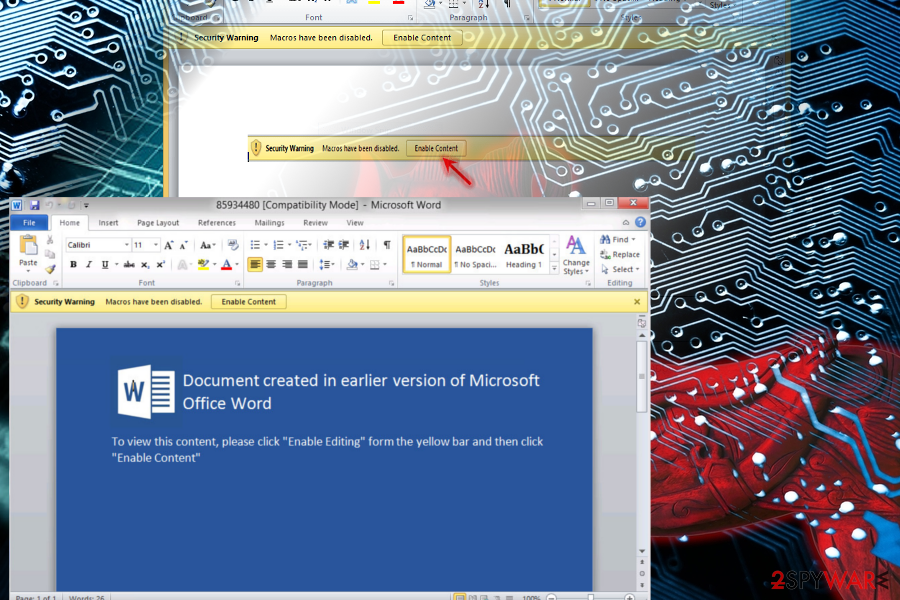
Panda and Zeus are practically identical. The only difference between the two is that Panda mainly targets banks in UK and Australia. Other traits are more or less similar. Usually, Panda Banker spreads through malicious Word documents which come attached to the spam emails and becomes activated with the Word Macros function. The researchers report that the highest risk of being infected with this virus is attributed to the Microsoft Windows operating system.
Specifically, Panda Banker virus exploits the CVE-2014-1761 and CVE-2012-0158[3] vulnerabilities to activate itself. Also, it is not uncommon for the virus to use deceptive social engineering techniques to trick people into enabling Word Macros support themselves.
Once the virus infiltrates the computer it starts tracking the user’s data. Its initial interests are the computer owner’s username, installed antivirus and firewall software information, OS platform, computer name, local time and similar characteristics. The gathered data is then transferred to the C&C (command and control) server where a unique client is created helping to distinguish infected device from other computer bots. At this point, it is practically impossible to spot that the virus has already infiltrated the system. However, a sophisticated antivirus software, such as FortectIntego should be able to detect and remove the virus from your computer, as long as you keep it updated to its latest version.
While the infected computer owners continue using their computers as usual, the Panda Banker trojan starts inserting malicious code into the banking websites. You should be careful if you have any accounts in the Bank of Scotland, Halifax UK, Lloyds Bank, Santander Bank or TSB. Once the code is injected, the trojan is then able to collect the user’s banking credentials and, eventually, breaking into the user’s accounts. If you notice any suspicious processes running on your computer or, worse, considerable sums of money disappearing from your bank account, you should immediately scan your system with antivirus software and ensure a complete Panda Banker removal.
The activity of Panda Banking Trojan
Initially detected in 2016, Panda Banker has been delivered by three different exploits known as Angler, Nuclear, and Neutrino. According to Proofpoint researchers, these exploits were necessary for criminals to find out target users in Australia and the United Kingdom.[4] The virus used to target banks in particular.
In 2017, experts noticed a shift from banking institutions to holiday shoppers. To harvest banking credentials, Panda Banker injects code into region-specific banking sites, including payment sites, casinos, travel sites, video-streaming sites, retailers, and similar. In 2017, the virus hit thousands of people in the period, which included Thanksgiving, Black Friday, Cyber Monday, and Christmas.
The injects of Zeus Panda found in 2017 were configured to steal a variety of information, including credit card number, address, phone number, DOB, SSN, and security question-related information.
Most of the victims were tricked by a fake email attachment called resume.doc, with the subject line “Application submitted from Gumtree Jobs by [First Last Names] for Field Sales Consultant – Status: Emailed.” This malicious email refers to a job application, which is popular in UK, Australia, New Zealand, and South Africa.
The latest strain of Panda Banker, known as version 2.6.6, has been observed at the end of March 2018.[5] According to experts, the Trojan has switched its target from Canada and the United States to Japan. It's the first time in Zeus Panda, also dubbed as PandaBot, to be targeting Japanese financial institutions.
Although the virus itself hasn't been modified remarkably, it has no ICO overlap with the previous PandaBanker attacks, and the target moved to Japan. These two facts make it stand out from the earlier attacks. The latest attack is closely related to hillaryzell[.]xyz address, which is registered to a Petrom Vladim using an email yalapinziw@mail.ru.

Based on the analysis initiated by Netscout, the C2 server returned 27 injects, 17 of which were embedded into Japanese banking websites. The current version is mainly distributed via Rig, Seamless, and Vokut Exploit Kits.
Banking Trojans are distributed via EK and spam email attachments
As already has been pointed out in this article, this particular version of Zeus is typically distributed via infected spam email attachments. According to experts, the Trojan takes advantage of the CVE-2014-1761 and CVE-2012-0158 vulnerabilities or renders Rig, Seamless or Vokut Exploit Kits (EK)[6] to infect targeted PCs or servers.
Most of the victims were infected with this Trojan right after opening an infected email attachment. The most widely spread Panda payload is known as resume.doc file, which spreads attached to emails with the subject line “Application submitted from Gumtree Jobs by [First Last Names] for Field Sales Consultant – Status: Emailed.”
Alternatively, it may be disguised under Gert.exe executable file atached to spam email messages. If the potential victim executes the file, the trojan is downloaded from 78.128.92[.]31/gert.exe.
Having in mind the activity of such and similar trojans, both home users and institutions should reconsider system's protection. One of the prerequisites when trying to stay safe from banking trojans is a reputable anti-virus program. It's important to keep it up-to-date and check if Real-Time protection feature is enabled. Besides, you should always update the OS. Outdated OS is more vulnerable to cyber attacks initiated via exploit kits.[7]
Tips on Panda Banker virus removal
For less experienced computer users, even the thought of having to deal with malicious, money-stealing viruses on their own is highly intimidating. Luckily, there's a multiplicity of anti-virus vendors worldwide offering advanced security tools that are not only capable of protecting the system from infections and removal of the existing ones. Most of them now has a PC's optimization feature, which is extremely useful after a cyber attack.
Therefore, NoVirus.uk[8] cybersecurity team stresses the importance of obtaining a reliable antivirus suite is the best option to remove Panda Banker trojan from the infected computer. We recommend such acknowledged virus-fighting utilities as FortectIntego or Malwarebytes.
As this trojan runs in the system unnoticed, it is advisable to run regular scans with the obtained antivirus utility. If any trouble arises when removing the virus automatically, or the trojan tries to terminate the system scan, you can try disconnecting your computer from the network, which should diminish the virus functionalities on your computer.
Getting rid of Panda Banker. Follow these steps
Manual removal using Safe Mode
If you cannot perform Panda Banker removal because your anti-virus gets blocked each time you try to launch it, follow these steps to restart the system into Safe Mode with Networking. One there, update your anti-virus and run a full system scan:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Panda Banker using System Restore
If the previous method did not help to get rid of a trojan, here's what you may try:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Panda Banker. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Panda Banker and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Asavin Wattanajantra. Complete Zeus Trojan source code gets leaked. The Inquirer. The Incisive Media.
- ^ Ionut Arghire. Panda Banker Campaign Hits U.S. Banks. Security Week. Internet and Enterprise security news.
- ^ Alex Macdonnell. CVE-2014-1761, Oh did you mean CVE-2012-2539?. Talos Intelligence Blog.
- ^ Zeus Panda Banking Trojan Targets Online Holiday Shoppers. Proofpoint. Protects your people, data and brand against advanced threats and compliance risks.
- ^ Dennis Schwarz. Panda Banker Zeros in on Japanese Targets. NetScout. Unique threat analysis.
- ^ Distribution of Zeus Panda illustrated. Twitter. Cybersecurity researcher's blog.
- ^ Rig EK via Malvertising drops Panda Banker. Zero Phage Malware. A blog on Exploit Kits and the malware they drop.
- ^ Novirus. Novirus. Cyber security news and insights oriented to UK Internet community.







