Phoenix ransomware / virus (Simple Removal Guide)
Phoenix virus Removal Guide
What is Phoenix ransomware virus?
Current state of Phoenix virus: can your files be decrypted?
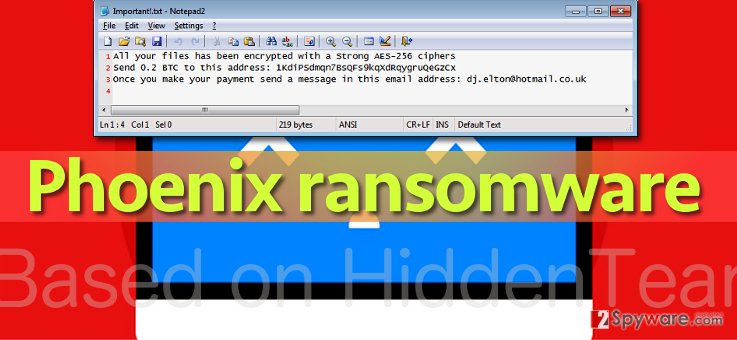
In-development ransomware dubbed Phoenix virus has been discovered, and reportedly it hasn’t reached a large number of computer users yet. The virus is buggy and currently not very dangerous, but it is likely to be improved anytime soon and distributed to a larger number of computer users. At the moment, Phoenix malware doesn’t encrypt files stored on all system folders but only those who are saved on the desktop. The virus is based on HiddenTear ransomware[1], uses AES-256 cipher to encrypt files, so anyone infected with the virus can decrypt their files for free. It is not the first virus that has been created using the educational open-source ransomware code; sadly, many versions of HiddenTear are used for malicious purposes[2], and Phoenix is yet another one. To recognize the virus, we suggest looking at the extensions of encrypted files – Phoenix malware appends .R.i.P file extensions to them.
Later on, this software crafts a ransom note text, saves it into Important!.txt file and saves it on victim’s desktop. The ransom note suggests writing to dj.elton@hotmail.co.uk to get file recovery software. Of course, this software cannot be obtained charge-free. Virus’ authors want 0.2 BTC for it, which is more or less 152 USD. The virus wants to receive the ransom payment in Bitcoins via the wallet address that is provided in the ransom note. We do not advise you to do so, because this virus is not worth a single penny that you’ve earned in your life. Just use HiddenTear decryptor to restore your files (full instructions on how to do it are given below Phoenix removal tutorial). You should remove Phoenix virus before taking any data recovery measures. As long as the virus stays in the computer system, you’re not safe, so uninstall it as quickly as you can. You can use tools like FortectIntego for that.
How to recognize malicious content online and protect your PC from it?
Malware is mainly spread using techniques that allow to mask it and present it to the victim as a safe-looking file, program, or browser extension.[3] Some malware examples do not drop executive files directly – they might redirect you to a malicious website and ask you to install a hideous browser extension, which is meant to connect to malicious server online and download ransomware from there; the same can happen with infectious Word files, too. Ransomware also hides in JavaScript files and even .vbs files, besides, future malware distribution predictions promise even more[4]. However, these techniques require additional effort, so we believe that Phoenix virus’ authors do not use them. Most likely this virus is distributed via email in a .exe file, so we suggest you avoid emails sent by unknown people. Just resist the urge to explore contents of interesting-looking links or attachments, and you will be fine. For extra protection, install anti-malware software to your computer.
How can you free your PC of Phoenix virus?
In case you have been accidentally hit by Phoenix ransomware virus, do not be scared. Consider this accident a good lesson, and never make same mistake again. However, since there are loads of more dangerous ransomware viruses that damage the computer so badly that files and settings cannot be restored[5]. You should definitely take actions to avoid such dangers.
To remove Phoenix virus, use anti-malware program, because despite the fact that this virus is not the most dangerous one, it still poses a big threat to the computer system and leaving one or two components of it can lead to sad consequences later on. If you’re ready to start the Phoenix removal, read instructions provided below.
Getting rid of Phoenix virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Phoenix using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Phoenix. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Phoenix from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Phoenix, you can use several methods to restore them:
Decrypt with HiddenTear decryptor
1. Download HiddenTear bruteforcer, which will find your decryption key. Extract the .zip file and run the bruteforcer. Choose mode (ransomware name). Select a sample file (encrypted one) and run the bruteforcer. Wait.
2. Once you have the decryption key, use it to decrypt your files. Download this HiddenTear decryptor for that and follow what it tells you to do.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Phoenix and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Jornt van der Wiel. Hidden tear and its spin offs. Securelist. Information about Viruses, Hackers and Spam.
- ^ Hidden Tear Project: Forbidden Fruit Is the Sweetest. TripWire. IT Compliance and Advanced Threat Protection.
- ^ Justin Ferris. How to spot disguised malicious files before they infect your computer. Komando. Source for the latest news on everything digital including security threats, scams, tips and tricks.
- ^ 2017 IT Security Predictions. Information Security Buzz. An independent resource that provides the best blogs, opinions and news for the information security community.
- ^ Ian Paul. Vicious new ransomware takes your money and still deletes your files. PCWorld. News, tips and reviews from the experts on PCs, Windows, and more.







