PizzaCrypts ransomware / virus (Removal Guide)
PizzaCrypts virus Removal Guide
What is PizzaCrypts ransomware virus?
The essential information about PizzaCrypts virus
Summer is speeding up its pace so do the hackers – recently PizzaCrypts virus joined the gang of ransomware. This file-encoding virus emerged in early July. Like other recent newbies – CryptoFinancial, and BitStak viruses, it also tends to change the formats of corrupted files. It seems that hackers enjoy their misdeeds and occasionally laugh at their victims either by making up amusing titles or demanding laughable ransoms. Nevertheless, users whose computers have been infected with this threat the least are willing to giggle. If you happen to fall into the victim list, then, find out how you can remove PizzaCrypts. One of the ways to do that is to employ FortectIntego.
Taking a look at recent ransomware emergence trend, generating a file-decoding malware seems to be the new wave. While such ransomware titans as CryptoWall and TeslaCrypt blew over, more free space appeared for other viruses. Moreover, specialists deduct that different hackers publish ransomware. While some are ridiculously easy to decode, others, e.g., Cerber, presents a real puzzle for the virus researchers. PizzaCrypts malware has been named in such manner for its distinctive feature to change the extensions of the encoded files into .id-[victim_id]-maestro@pizzacrypts.info. Moreover, the virus does not lag behind other threats since it also employs an asymmetric encoding technique. The latter consists of two mathematically intertwined sets of code. Thus, the biggest probability to decode the information is to obtain the unique private key.
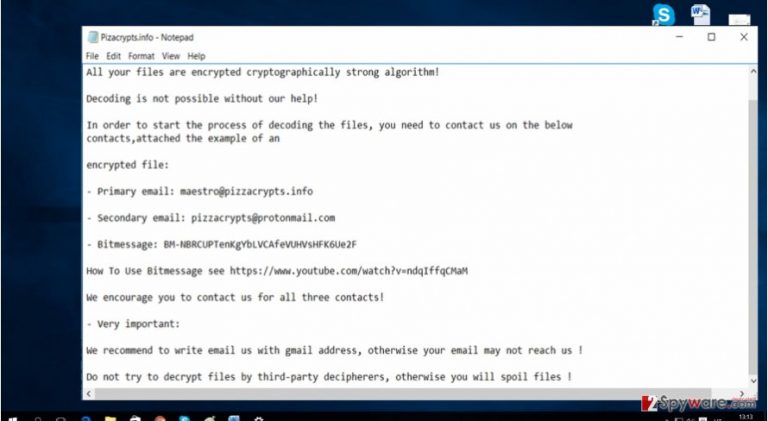
Misusing this quality, hackers try to convince the victims that there is no other choice retrieving the information except by paying the demanded amount of money. Regarding the latter, it is not known how much the virus asks in exchange since it does not present the sum directly in the message. It is speculated that PizzaCrypts ransomware might require from one Bitcoin to three (600 – 2000 USD). In any case, do not consider making the transaction because few ransomware hackers keep their word of returning the files. Consequently, concentrate on PizzaCrypts removal option.
How does the virus invade operating systems?
This particular ransomware is not picky when it comes to attacking the computer. Both, Windows, Mac OS users should stay alert because the ransomware might break into their systems at any time. Luckily, it has been revealed that the virus prefers spreading via Neutrino exploit kit. In other words, it is a trojan which is capable of disguising itself as a legitimate file. Like in the legend of a Trojan horse, the file can sneak into the system without getting spotted, though it contains ominous content within – PizzaCrypts. In this case, it is of utmost importance to improve the PC security. You can do it by updating or downloading powerful and trustworthy anti-virus and anti-spyware programs. This combination will ensure that no trojan or similar malware sneaks into the computer. Certainly, for the programs to ensure the maximum protection, they must be updated daily.
PizzaCrypts removal method
When it comes to ransomware, we recommend installing a security program to do the elimination. Because the virus uses an elaborate encryption method, locating its source files might turn out to be a tiresome activity. The software will remove PizzaCrypts within a couple of minutes. In addition, it will run an additional system scan to check for other threats. After your computer returns to status quo, you can concentrate on either recovering your files or backing them up. You can do it either by using the OS function or online websites. We suggest keeping the data in several places to decrease the risk of its loss.
Getting rid of PizzaCrypts virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove PizzaCrypts using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of PizzaCrypts. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from PizzaCrypts and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.







