Precomp.exe (Removal Guide) - Free Instructions
Precomp.exe Removal Guide
What is Precomp.exe?
Precomp.exe – a Windows background process that might indicate malware infection
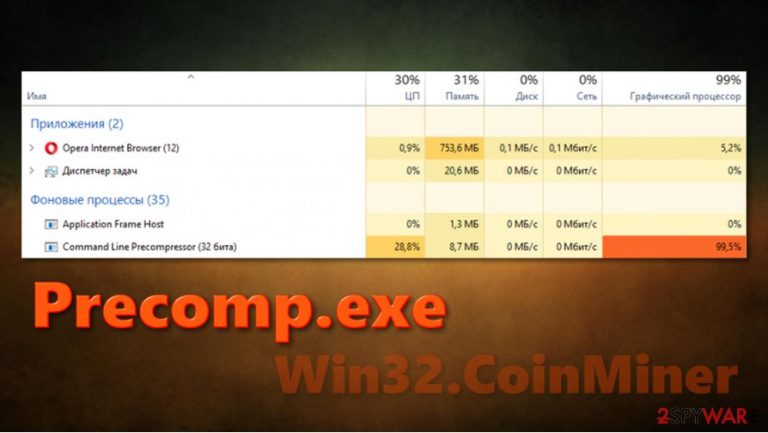
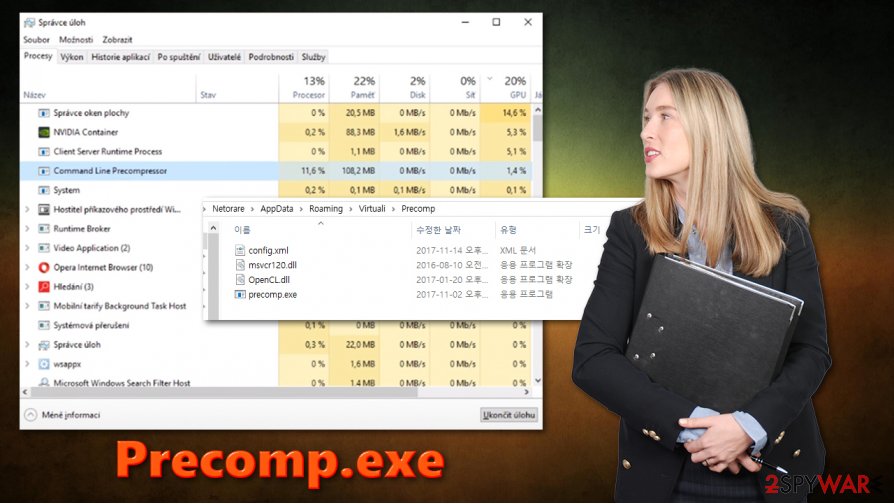
Precomp.exe is a process that users might find running on their Task Manager under the name of Command Line Precompressor, which can be used by many different programs, including WinRar, uTorrent, and others. The process runs in the background, and its location is usually located in the “User” folder, although it can also be found in Program Files, System32, or other folders.
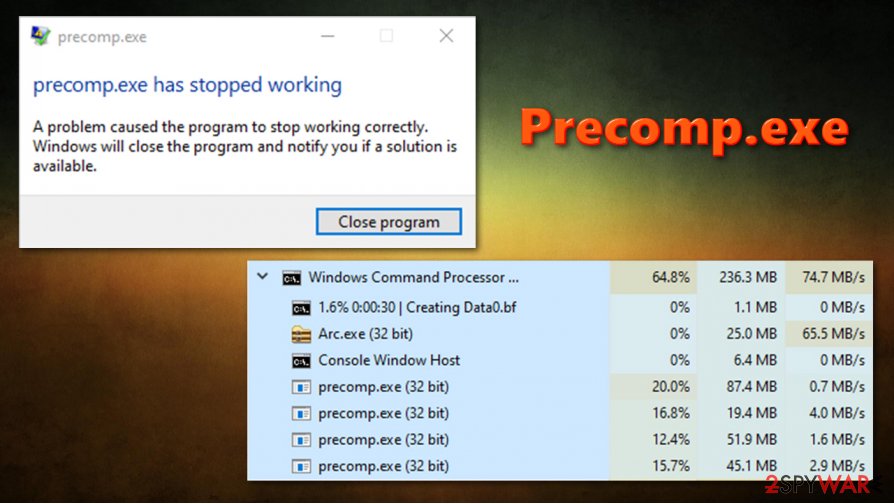
However, many users have complained that Precomp.exe is running at high CPU in the background, greatly disrupting the computer work and causing lag, crashes, and errors. While, in some cases, issues may lie within corrupted program files or similar, the high resource usage is one of the main indicators for the Win32.CoinMiner malware infection. Thus virus specializes in secretly mining digital currency by using Windows CPU or/and GPU – the funds are transferred directly to cybercriminals' crypto-wallets. Without a doubt, you should not tolerate the appearance of the Precomp.exe virus, as it might seriously compromise your computer performance and personal safety.
| Name | Precomp.exe |
|---|---|
| Type | Cryptojacking malware, Trojan |
| Process name | Command Line Precompressor |
| Symptoms | High CPU usage, Internet speed reduction, crashes, freezes, unresponsive apps, etc. |
| Related malware | Win32.CoinMiner |
| Risks | Increased electricity bills, installation of other malware, personal information disclosure, monetary loss, etc. |
| Elimination | If the executable is not related to malware infection and is a part of |
| System Recovery | Malware might seriously damage several Windows processes or even corrupt some system files, especially if it has been running for a while. Upon successful elimination, we highly advise using FortectIntego repair program in order to fix underlying issues after malware infection |
Cryptominers are well-known in the cybersecurity world and have been one of the most prevalent threats during the time when Bitcoin price skyrocketed. While the popularity of cryptojackers[1] decreased, users can still infect their computers with this type of malware, and it's something that nobody would like to deal with.
Cybercriminals behind Precomp.exe Trojan might use several different distribution techniques, including:
- fake updates
- spam emails
- malicious cracks/pirated installers
- software vulnerabilities[2]
- malicious JavaScript, etc.
As evident, there are several ways how you could get infected with coin-mining malware. Nonetheless, this precise infection is known to be spread via pirated program installers for video games or cracked software. As evident, if you downloaded such a file from a torrent or a similar site, you should remove Precomp.exe virus with a powerful security app, such as SpyHunter 5Combo Cleaner or Malwarebytes. After that, you should tune-up and fix Windows system files and settings with FortectIntego if required.
While the impact of crypto-mining malware might not be taken seriously by some, it is important to realize that as long as a virus is installed on a computer, it is considered to be compromised. It can prevent users from performing high-resource required tasks, such as watching high-res video recordings, editing video, using graphical applications, or playing video games. In other words, Precomp.exe Miner Trojan might make the infected computer almost impossible to operate, as CPU/GPU will rack up 90% 100% of usage at any given time, and the fans will spit at their full capacity.
However, regular computer usage disruption is just one of the worries – the main risks include data theft as well as a computer security compromise. Malware can inject a variety of malicious files into the system, some of which might spawn tasks only later. Thus, Precomp.exe can download additional malware later and, as a result, infect the computer with other Trojans, backdoors, rootkits, ransomware, or other malicious software.
We would also like to point out that Precomp.exe can be a part of a legitimate program, even though it is causing high CPU usage. So how should you know whether you are infected? The truth is that each case is very individual, and there is no universal answer. You need to perform some checks in order to find out.
The first thing you should do is scanning your device with security software. However, keep in mind that not all security programs can detect all variants of the virus, hence Precomp.exe removal might be a bit more complicated. The solution to this is to scan your machine with a few different security programs or upload the file in question to Virus Total or similar analysis services.
Another hint is whether or not the Precomp.exe process appeared after you installed a program yourself or if it showed up seemingly out of nowhere. If you downloaded a pirated game or an app, it is highly likely that you are infected. However, if the process belongs to WinRar or another legitimate app and causes you problems, you should simply uninstall them via the Control Panel. We provide the instructions below.
Avoid being infected with malware
As previously mentioned, crypto-mining malware is just one of many security threats that are spreading around the internet. Ransomware, Remote Access Trojans (RATs), backdoors, rootkits, worms, and other types of malicious programs are designed for various tasks, and none of them are positive, at least for the end-user. Unfortunately, many malware is programmed to stay invisible on the system for as long as possible, and, if no security solutions are implemented, it can run for weeks or even months before it is spotted.
Thus, as a first security measure, you should always ensure that your computer is protected with an up-to-date anti-malware solution. Make sure your automatic updates are set in place and run regular, on-demand scans as required. Unfortunately, there is no security program that would be able to detect all malware, as it is constantly shifting – criminals find new ways to bypass security measures. Thus, experts[3] advise being cautious and conscious about online threats.
You should not open email attachments (and allowing documents to run macro function) or click on the embedded links, and avoid visiting websites that spread pirated programs/software cracks. Also, use strong passwords and never repeat them.
Use security software to get rid of Precomp.exe virus
As previously mentioned, Precomp.exe removal might not be necessary if the process related to it comes from a legitimate program. If that is the case, we advise you to employ FortectIntego and attempt to fix issues you might be having with a Windows computer performance. If nothing helps and you are still having problems with high CPU usage, you should simply uninstall the related program, as we explain below.
To remove Precomp.exe virus, you should employ an anti-malware solution. While manual elimination is indeed possible, it is not recommended for regular computer users, as it requires deep understanding within the IT field and cybersecurity. To ensure that no such infections happen in the future, make sure you employ a real-time protection feature on your security program.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Precomp.exe. Follow these steps
Uninstall from Windows
If some application is causing you troubles, uninstall it via the Control Panel as explained below:
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Crypto-mining malware might inject components into Google Chrome and continue to operate via the web browser. Thus, we recommend you reset the browser to ensure its integrity:
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Precomp.exe registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting trojans
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Michael Nadeau. What is cryptojacking? How to prevent, detect, and recover from it. CSO Online. Business continuity and data protection.
- ^ Vulnerability (computing). Wikipedia. The free encyclopedia.
- ^ Semvirus. Semvirus. Cybersecurity advice and malware insights.
