Program:Win32/Wacapew.B!ml (Removal Guide) - Free Instructions
Program:Win32/Wacapew.B!ml Removal Guide
What is Program:Win32/Wacapew.B!ml?
Program:Win32/Wacapew.B!ml can be a false positive detection or refer to an SDBbot Remote Access Trojan
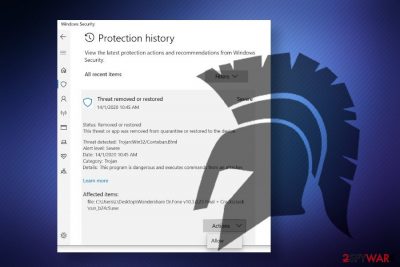
Program:Win32/Wacapew.B!ml is a generic detection name delivered to Windows users by Windows Defender antivirus program. Typically, people encounter a pop-up flagging malicious behavior on the machine after installing a piece of software, especially keygens, cracks of software for hack tools for the Windows license key. This issue has been extremely prevalent in 2019 as there were many reports on Microsoft forums.
Nevertheless, people keep asking how to remove Program:Win32/Wacapew.B!ml trojan up till now. If you keep getting a report from Windows Defender reporting this infection, the culprit may be wrong virus definitions of the in-built Windows security software. However, ignoring this detection may be a huge mistake because the detection may refer to the malicious mswinload0.dll file, which is one of the core processes run by Get2 downloader[1] and SDBbot RAT.
| Name | Program:Win32/Wacapew.B!ml |
| Associated AV | Windows Defender |
| Classification | It's a generic virus detection name that can either be a false positive or flag a malicious banking Trojan infection |
| Possibly related virus | Get2 downloader and SDBbot RAT |
| Symptoms | The main symptom – Windows Defender keeps launching warning popups reporting the malicious behavior of the Program:Win32/Wacapew.B!ml virus. Apart from warnings, the Windows machine may become sluggish, CPU consumption may jump from low to high, etc. |
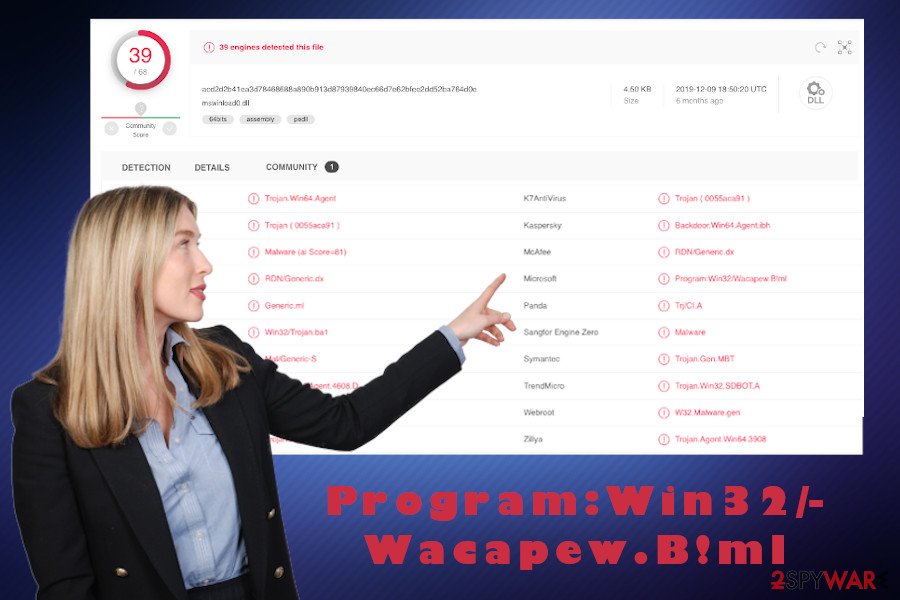
| Other detections | Win64:Trojan-gen (Avast), Malware@#15ko81j88dnzv (Comodo), Trojan.TR/Agent.gyhwl (F-Secure), Mal/Generic-S (Sophos AV), Win64:Trojan-gen (AVG), Trojan.GenericKD.42040575 (BitDefender), Trojan.GenericKD.42040575 (B) (Emsisoft), etc. (VirusTotal) |
| Removal | If any AV engine reports a malicious application, reboot the system into Safe Mode and perform a thorough system scan. Quarantine and remove all dangerous entries using an automatic tool |
| Malicious Trojans and spyware are capable of corrupting Windows registries and startup programs. Thus, the repair is required upon virus removal. For that, take advantage of the FortectIntego repair tool | |
Program:Win32/Wacapew.B!ml detection alert by Windows Defender Antivirus can be a false positive. According to user reports, this security tool has had some issues with virus definitions and tended to flag reliable software as malicious. Upon testing the issue, Microsoft[2] has initiated comprehensive log changes for security intelligence update version 1.293.1036.0 and added renewed threat detections.
Upon the update, the issue regarding false positive detection of the Program:Win32/Wacapew.B!ml virus seems to have stopped. However, people are still having this same detection warning brought by Windows Defender Antivirus, while scanning the machine with alternative AV engines report the following detections:
- Trojan.GenericKD.42040575
- TR/Agent.gyhwl
- Malware@#15ko81j88dnzv
- W64/Agent.SE!tr
- RDN/Generic.dx
- Win32/Trojan.ba1
- Trojan.Win32.SDBOT.A
- Backdoor.Win64.Agent.ibh, etc.[3]
In this case, the Program:Win32/Wacapew.B!ml detection can be related to a highly dangerous SDBbot Remote Access Trojan and Get2 Downloader. According to Proofpoint researchers who detected this threat in spring 2019, this malicious RAT allows hackers to take full control over the host machine and subsequently sends commands to download and run files, monitor the activities, harvest information, log keystrokes, take screenshots, capture Webcam shoots, and similar.
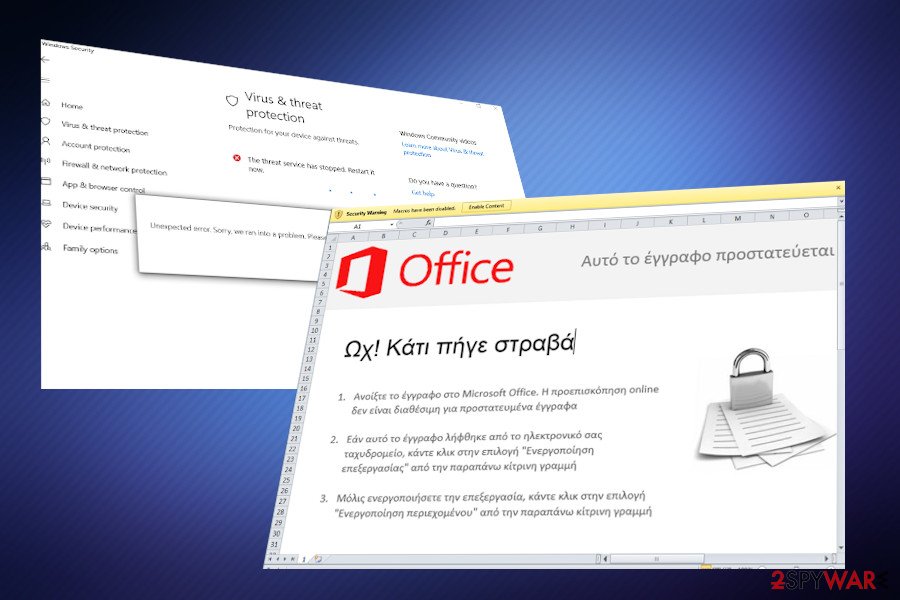
Program:Win32/Wacapew.B!ml virus is typically downloaded by a Get2 trojan. The latter can get into the system silently via spam email attachments (hpe_s_hp-inv_02[.]xls, dc123456[.]xls, business cloud invoice no142 09-09-2019[.]xls, etc.), roots into the system without manifesting its presence, thus ensuring persistence.
After that, the Get2 Trojan runs a pack of malicious processes and downloads the FlawedGrace, FlawedAmmyy, Snatch, and SDBbot RAT as secondary payloads. According to cybersecurity experts, Windows Defender and other AV security tools recognize the malicious performance of the mswinload0.dll file.
In the registry-based persistence mechanisms, a separate loader DLL is used to execute the RAT payload. In the analyzed sample, the loader was named “RegCodeLoader[.]dll” and saved to disk as “mswinload[.]dll” or “mswinload0[.]dll”. The application shimming-based persistence doesn’t use a separate DLL, but the code it patches into services[.]exe is similar in functionality. In both cases the random registry key and value name is patched into the loader code.
Anyway, if your security suite keeps warning you about a highly dangerous Trojan, evaluate the situation adequately, and take needed actions to remove Program:Win32/Wacapew.B!ml virus from the system completely. If the detection turns out to be related to the SDBbot RAT, it may lead to privacy violations, identity theft, or money loss.
If Program:Win32/Wacapew.B!ml Windows Defender Antivirus detection is bound to this particular security suite and none of the other AV engines detect issues on your device, it's possible that it's a false positive detection and you should report this issue to the Microsoft support.
Otherwise, take action to protect yourself from hackers by initiating a thorough Program:Win32/Wacapew.B!ml removal. Malicious Trojans usually enable commands to disable AV software. Therefore, we recommend you to restart the machine into Safe Mode with Networking. You can rely on tools like SpyHunter 5Combo Cleaner, Malwarebytes, or another robust anti-malware.
Post Trojan state of the Windows machine can not be pleasant. Malicious viruses tend to alter Windows registry entries, startup programs, core processes, some system files, etc. that eventually can cause errors and BSODs. Therefore, right after you remove Program:Win32/Wacapew.B!ml virus detection, try optimizing the system with FortectIntego repair suite.
Spam emails and pirated software can deliver Trojans and other viruses
Malicious payloads can get into the system via malicious spam email attachments or pirated software like keygens and cracks. Beware that suchlike malicious files do not disclose their presence. Instead, they remain in disguise with legitimate Windows system files, such as mswinload0.dll, Svchost.exe, or Winrmsrv.exe.
Payloads are responsible for downloading cyber threats, such as Trojans, spyware, malware, RATs, and more. Beware that they are developed in an extremely sophisticated manner to bypass antivirus programs without being noticed. Thus, you should evaluate online risks to prevent launching malicious files related to viruses.
In most of the cases, such viruses are being disseminated via malicious spam email attachments. Hackers can release tens of thousands of email that contain Microsoft Excel attachments under names like
- Subject – HPE INV-02 – Invoice and documents. Attachment hpe_s_hp-inv_02[.]xls.
- Subject – Need to Apply. Attachment dc123456[.]xls
- Subject – Document. Attachment business cloud invoice no142 09-09-2019[.]xls
- Subject – EXECUTIVE SUMMARY. Attachment προτιμολογιο[.]xls
Such attachments require to enable macros, which is a catch used by hackers to make users download malicious virus payload. Thus, if you received a questionable email message that you were not waiting for, it's better to send it to spam inbox or completely remove it.
Another perfect perfect medium for viruses to spread is pirated software. As pointed out by NoVirus.uk team[4], hackers can fill keygens and software cracks with malicious virus payloads quite easily. Thus, instead of downloading a “help” to hack some paid software, you can get your machine hacked.
Terminate Program:Win32/Wacapew.B!ml trojan to protect yourself from identity theft
When the Program:Win32/Wacapew.B!ml virus gets onto the machine, it can decrease its performance, increase vulnerability, and download other malicious entries to the system. Although it may be difficult to detect this entry manually, you can suspect the presence of a Trojan if the system keeps restarting all of a sudden, CPU usage gets high, AV engine keeps flagging malicious behavior, etc.
Keep in mind that severe computer viruses are exceptionally persistent and can hide malicious files over the system, disable AV tools, quarantine legitimate software, remove Windows registry entries, etc. Therefore, you should go to the Safe Mode and then focus on Program:Win32/Wacapew.B!ml removal.
To remove Program:Win32/Wacapew.B!ml virus completely, try using reputable anti-malware tools, such as Malwarebytes. Robust security tool ensures elimination of malicious files, clean PUPs, and other viruses. Nevertheless, AV tools are not programmed to repair the Registries and other Windows locations. Thus, we recommend scanning the system with FortectIntego tool that may increase the system's performance.
Getting rid of Program:Win32/Wacapew.B!ml. Follow these steps
Manual removal using Safe Mode
If you are dealing with the Program:Win32/Wacapew.B!ml trojan virus on your machine, try restarting it to Safe Mode with Networking and launch the security tool. Set it to scan the system thoroughly. Note that a full scan can take some time, so be patient.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Program:Win32/Wacapew.B!ml using System Restore
If Safe Mode does not work, try to quarantine Program:Win32/Wacapew.B!ml malware using System Restore feature.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Program:Win32/Wacapew.B!ml. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Program:Win32/Wacapew.B!ml and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Denis Swartz. TA505 Distributes New SDBbot Remote Access Trojan with Get2 Downloader. ProofPoint. Cybersecurity solutions.
- ^ Change logs for security intelligence update version 1.293.1036.0. Microsoft. The official support website.
- ^ mswinload0.dll. VirusTotal. Free file and URL scanner.
- ^ SECURITY AND SPYWARE NEWS. NoVirus. Virus and spyware news.





















