Protectionrequired.com ads (fake) - Free Guide
Protectionrequired.com ads Removal Guide
What is Protectionrequired.com ads?
Protectionrequired.com is a fake website that shows misleading messages

Considering how steeply the growth of the internet began since its discovery, it is not surprising that various malicious actors came to the conclusion that it could serve as a perfect medium for scams. The Internet provides anonymity, hence consequences of malicious actions are rarer than in real life. Hence, it was quickly utilized as a measure to scam users out of their money, as well as infect their systems with malware.
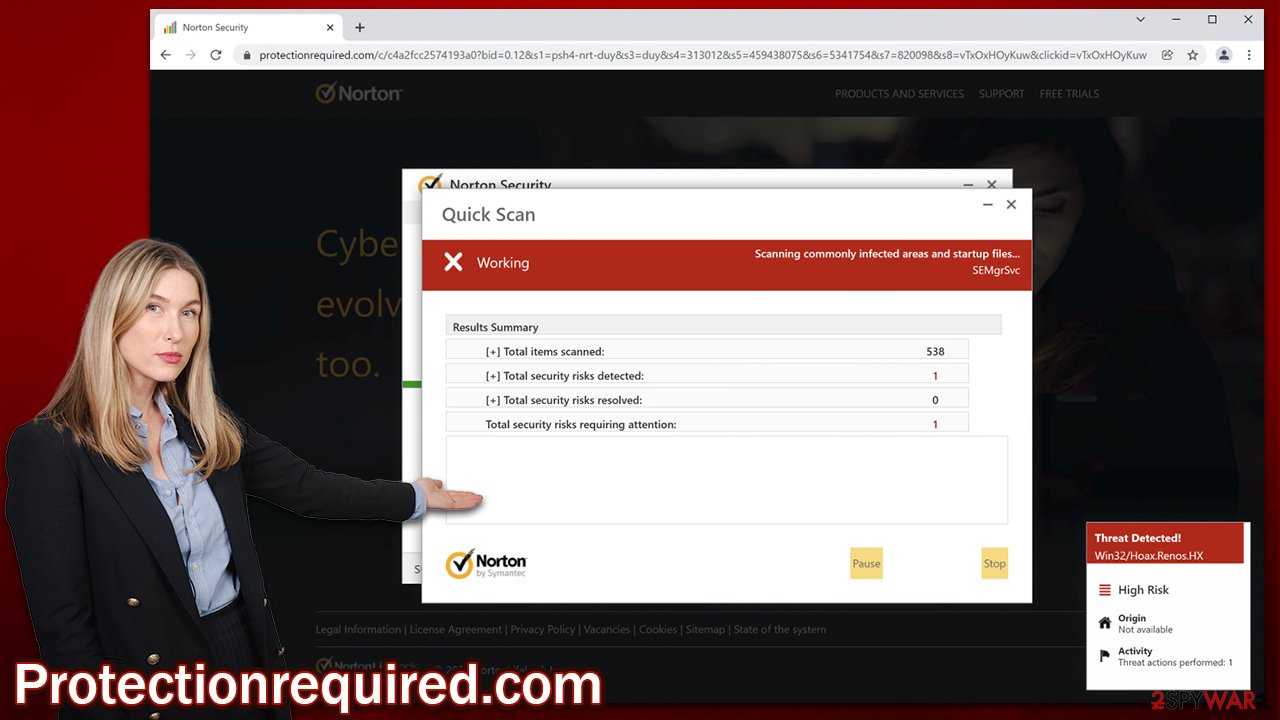
Protectionrequired.com is one of the websites that was created for monetization purposes. It uses various social engineering[1] techniques to mislead users into believing that their systems are infected with dangerous viruses and that the only way to get rid of them is to download software from Norton or McAfee. While these are perfectly legitimate security software vendors, you should not rely on websites that spread them via misleading messages.
The scam starts as soon as users are redirected to Protectionrequired.com – they are immediately exposed to a warning and told that they have visited a malicious website, which then quickly follows by what looks like an antivirus scan. In a few seconds, when the bar fills up, users are shown the following information:
Your PC is infected with 5 viruses!
ACTION REQUIRED
Your McAfee Subscription Has Expired!
Renew now to keep your PC protected.
If your PC is unprotected, it is at risk for viruses and other malware.
The scan presented by the website is entirely fake, and so are the “detected” viruses. Crooks simply use the name of popular security companies (logos can be easily faked) and imitate a scan of legitimate security tools. When dealing with these fake messages, keep in mind that no website can diagnose your PC by you simply entering it – only software installed on your system can do that.
Another tip is to always check the URL of the website you have doubts about; it becomes clear rather quickly that Protectionrequired.com has nothing to do with Norton or any other legitimate security software provider. To make it brief: never believe pop-ups or messages that claim that your computer is infected, blocked, or compromised, as these are used as means to make you spend money on useless software or install malware on your system.
| Name | Protectionrequired.com |
|---|---|
| Type | Scam, redirect, adware |
| Distribution | Software bundles, third-party websites, ads |
| Symptoms | Redirects to suspicious websites that accommodate commercial or scam content; fake messages that offer to download malicious software; ads plague every visited website; unknown extension or program installed on the system |
| Dangers | Installation of other potentially unwanted software or malware, personal information disclosure to cybercriminals, financial losses due to scams, etc. |
| Elimination | You should not interact with the contents shown by a scam website and instead, check your system for adware or malware infections with SpyHunter 5Combo Cleaner security software |
| Further tips | Third-parties can employ cookies to continue tracking your online activities, so we recommended clearing browser caches and other leftover PUP files with FortectIntego |
There is no doubt that all users would not like their systems being infected, hence they tend to avoid websites of high risk. Nonetheless, there are people who think that they could never be infected as long as they are careful enough. While being aware of dangers might diminish this probability, those who visit websites of dubious content are still much more likely to be a victim of an online scam or a malware attack, as there are so many techniques nowadays used by crooks in order to trick people into doing things they otherwise wouldn't.
Thus, the first rule is to avoid websites that are considered high-risk, for example, adult-oriented, illegal video streaming, software cracks, and similar. These types of sites are often poorly protected, as their operators mainly seek to gain some type of benefit from visitors, such as ad revenue. Unfortunately, ad space can often be rented to anyone, even malicious actors who can imbue these websites with malicious code that would infect some users with malware automatically.
Another rule for better security is adequate security tools such as anti-virus software, ad-blockers, firewalls,[2] web shields, etc. Remember, the software is as useful as you listen to its warnings – never assume that warnings are wrong and always investigate if you suspect there might be some type of mistake.
Check your system for adware
Adware is a type of potentially unwanted application that easily falls into the gray area – it is not entirely malicious, although not innocent enough to be ignored as a security threat. Nonetheless, it is important to note that there is an adware that can perform a variety of malicious actions which would result in a system security compromise.
For example, Lenovo was fined millions of dollars[3] for selling users laptops which included Superfish adware, which was able to make user PCs vulnerable to cyberattacks. Another great example of malicious adware is Wajam – it has been called out by various security researchers to be called for what it is – malware.
In most cases, adware is there to deliver ads, and the operators do not always have malicious intentions. However, since they often employ advertising networks that are not considered entirely secure, users who have their software installed are sometimes exposed to misleading, deceptive, and even dangerous ads or websites. Windowsdetector.com is just one of many sites you might encounter when having a PUP installed on your system, so it is recommended you immediately find and remove it from your machine.
Adware usually manifests as a browser extension, although it can also be installed as a program that you never suspected. Thus, you should open your web browser and check for extensions that you don't recognize. If you are not sure – simply remove them all and see if that stops the intrusive activities.
You should check whether there are programs installed on the system level as follows:
Windows
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

Mac
While moving apps into Trash is how you delete most normal applications, adware tends to create additional files for persistence. Thus, you should look for .plist and other files that could be related to the virus. If you are not sure, skip this step entirely.
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
Finally, you should perform a full system scan with anti-malware software such as SpyHunter 5Combo Cleaner or Malwarebytes, as manual elimination is not always successful. Malware can hide itself by using various obfuscation techniques and stay on the system for a very long time if not removed. Note that you should bring the security app to the latest version to ensure that the newest virus databases are used and only then scan your device.
Clean your web browsers and get rid of push notifications
After you eliminate adware and malware from your system, you should also take your time to clean or reset your web browsers. Cookies are known to collect various user data and can sometimes be used for session hijacking, which can be very dangerous. You can either use FortectIntego for this process (which would also fix any system issues caused by the virus) or proceed with the following steps:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Keep in mind that, if you have accepted the notifications from Protectionrequired.com, you might start seeing annoying and intrusive pop-ups on a regular basis – these would also expose you to various scams and misleading messages. Please do not click on any links shown by the site, as it could end badly. Instead, follow the instructions below to stop the ads from being shown to you once and for all.
Google Chrome
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Safari:
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

Note: IN these settings, you can enable the “Use quieter notifications” option, which would make the annoying notification prompt never show up on all websites. You can still view it by clicking a small prompt button on the left side of the address bar and then accepting notifications from the website.
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Social engineering (security). Wikipedia. The free encyclopedia.
- ^ What Is a Firewall?. Cisco. Security company.
- ^ Russell Brandom. Lenovo pays $3.5 million for preinstalling Superfish adware. The Verge. Technology news website.
