Qarallax (Virus Removal Guide) - Free Instructions
Qarallax Removal Guide
What is Qarallax?
Qarallax is a remote access tool which helps to steal private information
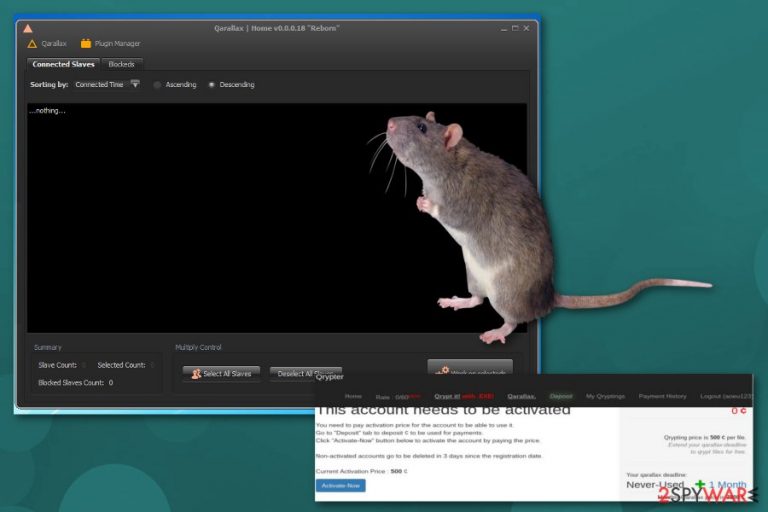
Qarallax is a malware which uses malicious scripts to gather information. This program can be called as an info-stealer virus because of its RAT[1] capabilities. This malware is associated with the group of BlackHat[2] hackers called Quaverse that used this program several attacks on business company servers. This activity was discovered back in 2016 and in December 2017 it was spotted again with an updated version.
| Name | Qarallax |
|---|---|
| Type | Malware |
| Sub-type | Remote Access Tool (RAT) |
| Associated with | Quaverse hacker team |
| Firstly spotted | June 2016 |
| Main dangers | Monitors and launches programs, allows other attackers to access the system remotely |
| Distribution | Spam email attachments |
| Elimination | Do not attempt uninstall Qarallax manually. Use FortectIntego instead. |
Qarallax virus is capable of various malicious activities. This program runs as a Java app on the computer and supports Command and Control (C&C) servers. This RAT is designed to place virus-filled VBS files to system folder under AppData directory.
Qarallax RAT can be known for various attacks on big companies. Malware payloads usually spread via spam emails and various fake files. Images or text files that have .jar extension might be the potential carriers of this malicious program. It is known that it is associated to the following file names:
- HEUR:Trojan.Java.Agent.gen;
- JAVA.S.Agent.546304;
- Java.Trojan.Agent.Adkp;
- Java.Trojan.Agent.Wrqi;
- Java.Trojan.GenericGB.20241;
- Java.Trojan.GenericGB.20247;
- Java:Malware-gen [Trj];
- Trojan.Gen.NPE.2;
Qarallax can make multiple changes in your PC system and give remote control to attackers or misuse your personal data. RAT programs commonly has these features:
- Can connect to your desktop remotely and input commands via keyboard and mouse;
- Can turn your webcam on and off, record input;
- Can remotely connect to Windows and download files;
- Allow threat actors to access your system and manage your files;
- Monitor programs. Can launch and terminate them.
Computer security researchers at Zondervirus.nl[3] note that Qarallax malware might disguise as a legitimate software and be offered to download via promotions, discounts, and surveys for free. Unfortunately, this is merely a deceptive technique which helps criminals to access your system remotely.
You should remove Qarallax because it can allow threat developers to get on your system and plant other dangerous malware infections. Keep in mind that this virus may have numerous undiscovered and hazardous features which could damage your PC permanently.
Qarallax removal should not be treated as an easy process. So do not attempt to get rid of the malicious program manually. Rely on anti-malware tools that can access your system and run a full system scan in order to delete all possible threats. This a sophisticated cyber threat, so use a reputable tool, like FortectIntego. 
Spam email attachments can contain various fake files with malware
RATs are usually downloaded and installed unknowingly as most of the malicious programs. The most common distribution method is spreading the malware via spam emails. Cyber attackers hide the executable files in email attachments rarely look suspicious and this is the reason why this is one of the most beloved distribution technique employed by hackers.
Once this file is downloaded and when a user runs it, RAT silently installs itself to system memory and the attacker can use this program in the background without notifying the computer user. Also, it is possible that malware like this enter targeted computer through game applications or freeware if not paying enough attention. Use your anti-spyware tools and update them if you want to avoid various infections.
Qarallax removal requires certified tools
To remove Qarallax you should use professional tools and do not think twice about this. Manual malware elimination is not going to give positive results. It is barely possible to delete RAT by yourself. Anti-malware tools like FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes can help in this case because running a full system scan can detect all intruders and infections.
Furthermore, Qarallax removal is difficult and important. This program might be doing multiple damaging processes behind your back and you need to take control in your hands. Proper elimination can only be done using trustful programs. This method terminates every little piece that affects your PC's performance.
How to prevent from getting malware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Margaret Rouse. RAT. Tech target. Search security education.
- ^ Black hat hackers. Wikipedia. The free encyclopedia.
- ^ Zondervirus. Zondervirus.
