Qbaa ransomware (Decryption Steps Included)
Qbaa virus Removal Guide
What is Qbaa ransomware?
Qbaa ransomware comes from the family with 400 different versions
Qbaa ransomware collects various files and makes them useless by locking the piece. This is a virus that attacks Windows computers by using various infiltration methods. The infiltration is quick and cannot be stopped once it starts. Users are mainly responsible for this because if the email file attachments that needed to be downloaded and opened or pirating software gets installed willingly and leads to infiltration of the infection like this.
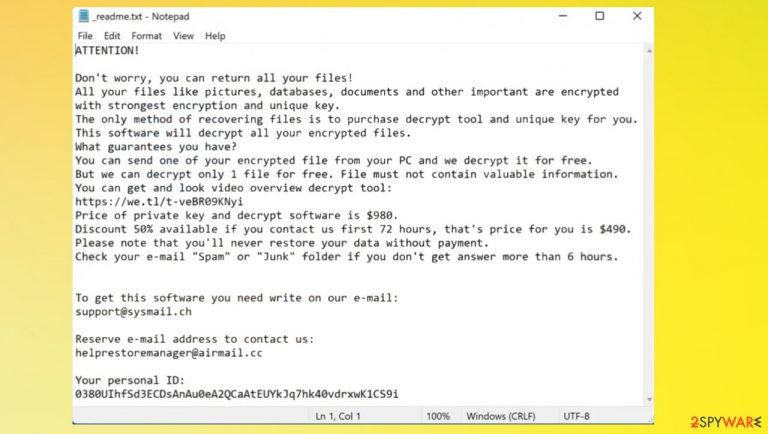
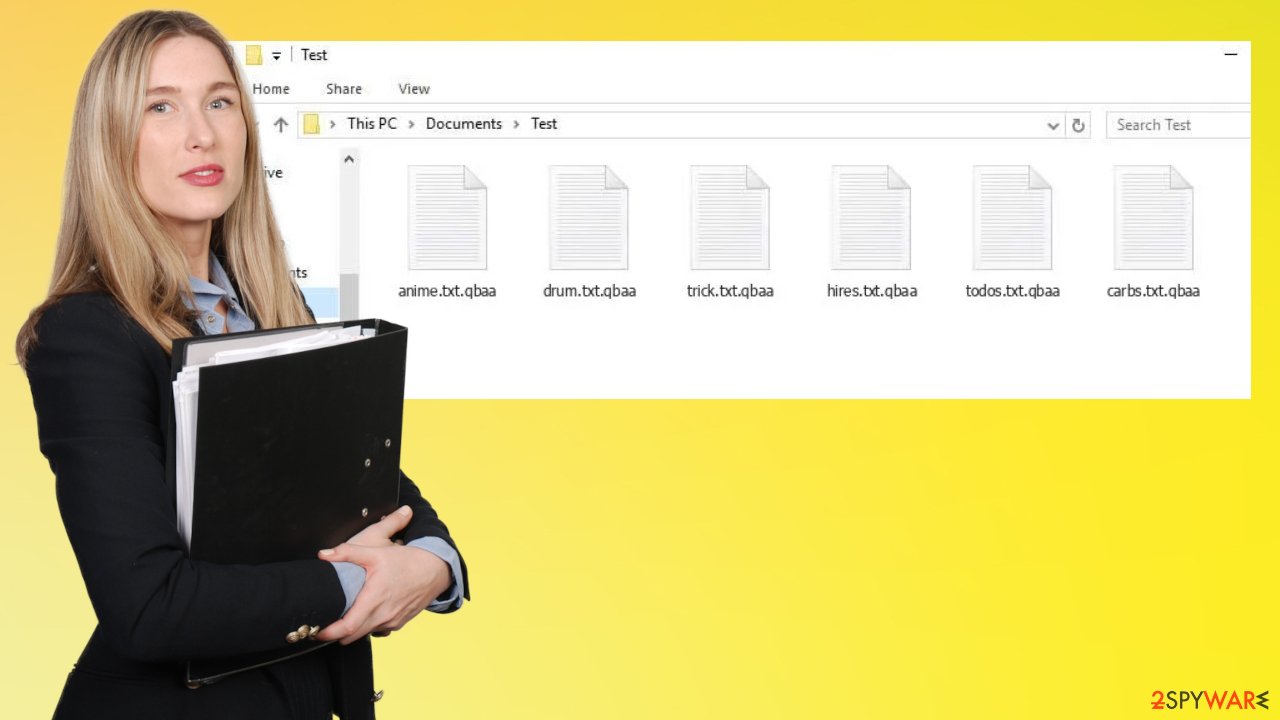
It uses an encryption algorithm[1] to lock up all documents, archives, videos, music, and other files, adding .qbaa extension to them. After that, ransomware delivers a ransom note _readme.txt text file, which includes instructions on how to recover the encrypted data. These are designed to scare people into paying the demanded sum of $980 in the form of Bitcoin.
According to Qbaa virus authors, victims need to contact them via support@sysmail.ch, helprestoremanager@airmail.cc email, and provide their personal ID that gets listed in the ransom demand message. Once that is done, users should receive further instructions to proceed with the payment and receive the decryption tool in exchange. Nonetheless, we do not recommend even contacting the attackers. Check out the alternative methods we provide below instead.
What is ransomware?
Qbaa ransomware – a computer infection that encrypts all personal files changing the original code and leading to a locking of the data that is later receiving the a .qbaa extension. Malware then drops a ransom note which claims that the only way to securely return data is by paying a ransom. The discount even is offered to encourage people to pay the ransom, but that is never a guarantee for data decryption.
This virus derives from a well-known family Djvu ransomware, which was first spotted in 2019. Since then, released multiple variants, including Vyia, Iiof, Sdjm, Fgnh. These versions are coming out weekly and are no longer decryptable since in the summer of 2019, criminals made advanced improvements to the threat code.
In this article, we will provide alternative methods for file recovery and safe ways of deleting the infection from a Windows computer. It is crucial to remove the program before any file repair steps because the second round of encryption results in permanent damage to files.
| Name | Qbaa file virus |
|---|---|
| Type | Ransomware, crypto-virus, file locking virus |
| Malware family | STOP virus/ Djvu ransomware |
| Extension | Files appended with .qbaa extension, e.g., “picture.jpg” is turned into “picture.jpg.qbaa” |
| Ransom note | _readme.txt |
| Contact emails | support@sysmail.ch, helprestoremanager@airmail.cc |
| Distribution | Files with the malware payload can be delivered via torrent sites with pirating software packages and included in files attached to various spam emails |
| File recovery | If no backups are available, recovering data is almost impossible. Nonetheless, we suggest you try the alternative methods that could help you in some cases – we list them below |
| Removal | Perform a full system scan with powerful security software and rely on anti-malware tools since those can detect[2] and treat any malicious files |
| System fix | Malware can seriously tamper with Windows systems, causing errors, crashes, lag, and other stability issues after it is terminated. To remediate the OS and avoid its reinstallation, we recommend scanning it with the FortectIntego repair tool |
The encryption process happens immediately after infection, so you might not even notice any other symptoms besides seeing weird messages on your screen every now again or the pop-up with Windows update indication. This particular message is appearing to take users' attention from the speed issue that is created by the file encryption procedure.
The danger of Qbaa ransomware is not just to your personal files but also any sensitive information that may be stored on the same device. It can quickly spread because it infects devices by releasing various files with a malware payload. The infection starts off when someone clicks on an infected link or opens a malicious email attachment that downloads this particular type of ransomware onto your device.
These threats should not be ignored because if left unchecked Qbaa ransomware virus infection could lead straight into major issues like losing data or even having files ruined permanently, which would get your money stolen in exchange for nothing. There are additional threats that control the persistence and security of the PC, so removing the infection quickly is crucial.
Removing the threat quickly and properly
Qbaa file virus is a malicious program that can damage your valuable files, so you would likely pay the ransom. There is a serious infection on your system that needs to be removed immediately. This threat will execute file corruption as well- not just during the encryption process but with the help of additional programs.
There are many ways to remove the file virus, and your device's built-in antivirus app can take care of it. There is no need to pay anything if you have an AV installed on your device because this type of software should be updated frequently. If you need an alternate option and the AV engine you use is not helping, try SpyHunter 5Combo Cleaner or Malwarebytes and scan the machine fully.
There is no need for prior IT knowledge when using these simple applications that can remove the Qbaa file virus and any damaging infections. Get back up to a normal state quickly with only one process. However, note that this is not the same as file recovery or decryption. You still need to restore the machine yourself.
Restore the performance
Once a computer is infected with malware, its system is changed to operate differently. For example, an infection can alter the Windows registry database, damage vital bootup, and other sections, delete or corrupt DLL files, etc. Once a system file is damaged by malware, antivirus software is not capable of doing anything about it, leaving it just the way it is. Consequently, users might experience performance, stability, and usability issues, to the point where a full Windows reinstallation is required.
Therefore, we highly recommend using a one-of-a-kind, patented technology of FortectIntego repair. Not only can it fix virus damage after the infection, but it is also capable of removing malware that has already broken into the system thanks to several engines used by the program. Besides, the application is also capable of fixing various Windows-related issues that are not caused by malware infections, for example, Blue Screen errors, freezes, registry errors, damaged DLLs, etc.
- Download the application by clicking on the link above
- Click on the ReimageRepair.exe

- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process

- The analysis of your machine will begin immediately

- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.

The encryption algorithm used by this Qbaa virus makes it so you cannot open these documents anymore, or even read what's inside of them. But do not panic and stay away from paying the ransom since there are major losses for those who pay. The family is known for a while now, and experts[3] do not recommend trusting these criminals.
Decryption for some of the versions
The ransomware can run in the background for hours, and you're never safe because of its ability to spread quickly with various methods. The idea that the only way around this problem is by paying them off might seem tempting, but before doing anything else think about all those risks first. Once the threat is eliminated, you can think about Qbaa file decryption.
However, that is strongly affected by the recent changes to encryption and the usage of offline ids vs. online ids. When you get hit with Qbaa ransomware, not only are all of your valuable pictures locked away from editing, but even accessing them could trigger deletion or secondary encryption.
The threat family now depends on unique online id forming methods mainly, so decryption is impossible. In case of a failed connection to the C&C servers, offline ID's can be used. These file recovery options may still work, and you should try running the application that was previously helping people with other Djvu versions.
However, it is important for users to know this tool will not always work because data could have been locked using the more common ways and advanced options. Trying to restore those Qbaa ransomware files can be helpful. If the tool shows results positive for the decryption – you are lucky. If not, go to the end of the article for additional tips.
If your computer got infected with one of the Djvu variants, you should try using Emsisoft decryptor for Djvu/STOP. It is important to mention that this tool will not work for everyone – it only works if data was locked with an offline ID due to malware failing to communicate with its remote servers.
Even if your case meets this condition, somebody from the victims has to pay criminals, retrieve an offline key, and then share it with security researchers at Emsisoft. As a result, you might not be able to restore the encrypted files immediately. Thus, if the decryptor says your data was locked with an offline ID but cannot be recovered currently, you should try later. You also need to upload a set of files – one encrypted and a healthy one to the company's servers before you proceed.
- Download the app from the official Emsisoft website.

- After pressing Download button, a small pop-up at the bottom, titled decrypt_STOPDjvu.exe should show up – click it.
- If User Account Control (UAC) message shows up, press Yes.
- Agree to License Terms by pressing Yes.

- After Disclaimer shows up, press OK.
- The tool should automatically populate the affected folders, although you can also do it by pressing Add folder at the bottom.
- Press Decrypt.

From here, there are three available outcomes:
- “Decrypted!” will be shown under files that were decrypted successfully – they are now usable again.
- “Error: Unable to decrypt file with ID:” means that the keys for this version of the virus have not yet been retrieved, so you should try later.
- “This ID appears to be an online ID, decryption is impossible” – you are unable to decrypt files with this tool.
Getting rid of Qbaa virus. Follow these steps
Important steps to take before you begin malware removal
File encryption and ransomware infection are two independent processes (although the latter would not be possible without the former). However, it is important to understand that malware performs various changes within a Windows operating system, fundamentally changing the way it works.
IMPORTANT for those without backups! →
If you attempt to use security or recovery software immediately, you might permanently damage your files, and even a working decryptor then would not be able to save them.
Before you proceed with the removal instructions below, you should copy the encrypted files onto a separate medium, such as USB flash drive or SSD, and then disconnect them from your computer. Encrypted data does not hold any malicious code, so it is safe to transfer to other devices.
The instructions below might initially seem overwhelming and complicated, but they are not difficult to understand as long as you follow each step in the appropriate order. This comprehensive free guide will help you to handle the malware removal and data recovery process correctly.
If you have any questions, comments, or are having troubles with following the instructions, please do not hesitate to contact us via the Ask Us section.
IMPORTANT! →
It is vital to eliminate malware infection from the computer fully before starting the data recovery process, otherwise ransomware might re-encrypt retrieved files from backups repeatedly.
Restore Windows "hosts" file to its original state
Some ransomware might modify Windows hosts file in order to prevent users from accessing certain websites online. For example, Djvu ransomware variants add dozens of entries containing URLs of security-related websites, such as 2-spyware.com. Each of the entries means that users will not be able to access the listed web addresses and will receive an error instead.
Here's an example of “hosts” file entries that were injected by ransomware:
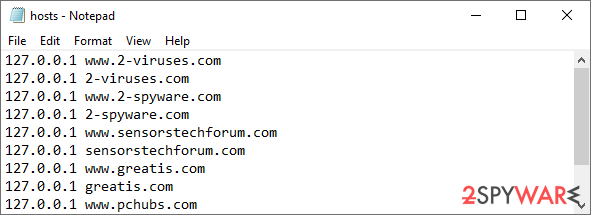
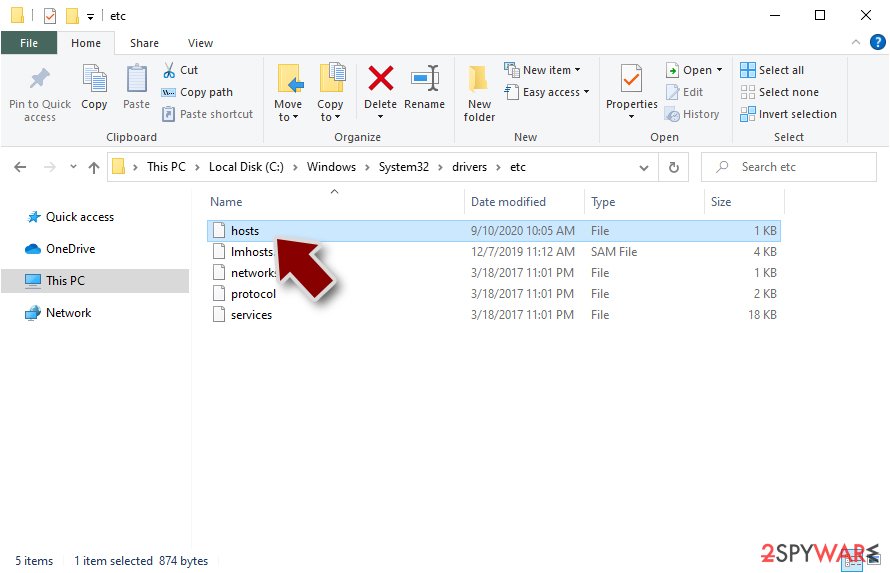
In order to restore your ability to access all websites without restrictions, you should either delete the file (Windows will automatically recreate it) or remove all the malware-created entries. If you have never touched the “hosts” file before, you should simply delete it by marking it and pressing Shift + Del on your keyboard. For that, navigate to the following location:
C:\\Windows\\System32\\drivers\\etc\\
Restore files using data recovery software
Since many users do not prepare proper data backups prior to being attacked by ransomware, they might often lose access to their files permanently. Paying criminals is also very risky, as they might not fulfill the promises and never send back the required decryption tool.
While this might sound terrible, not all is lost – data recovery software might be able to help you in some situations (it highly depends on the encryption algorithm used, whether ransomware managed to complete the programmed tasks, etc.). Since there are thousands of different ransomware strains, it is immediately impossible to tell whether third-party software will work for you.
Therefore, we suggest trying regardless of which ransomware attacked your computer. Before you begin, several pointers are important while dealing with this situation:
- Since the encrypted data on your computer might permanently be damaged by security or data recovery software, you should first make backups of it – use a USB flash drive or another storage.
- Only attempt to recover your files using this method after you perform a scan with anti-malware software.
Install data recovery software
- Download Data Recovery Pro.
- Double-click the installer to launch it.

- Follow on-screen instructions to install the software.

- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.

- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.

- Press Scan and wait till it is complete.

- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.

Create data backups to avoid file loss in the future
One of the many countermeasures for home users against ransomware is data backups. Even if your Windows get corrupted, you can reinstall everything from scratch and retrieve files from backups with minimal losses overall. Most importantly, you would not have to pay cybercriminals and risk your money as well.
Therefore, if you have already dealt with a ransomware attack, we strongly advise you to prepare backups for future use. There are two options available to you:
- Backup on a physical external drive, such as a USB flash drive or external HDD.
- Use cloud storage services.
The first method is not that convenient, however, as backups need to constantly be updated manually – although it is very reliable. Therefore, we highly advise choosing cloud storage instead – it is easy to set up and efficient to sustain. The problem with it is that storage space is limited unless you want to pay for the subscription.
Using Microsoft OneDrive
OneDrive is a built-in tool that comes with every modern Windows version. By default, you get 5 GB of storage that you can use for free. You can increase that storage space, but for a price. Here's how to setup backups for OneDrive:
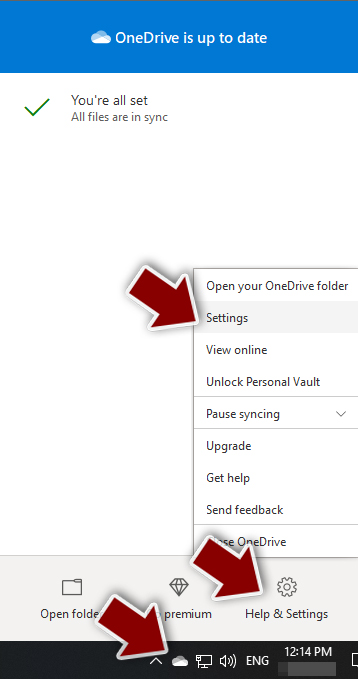
- Click on the OneDrive icon within your system tray.
- Select Help & Settings > Settings.
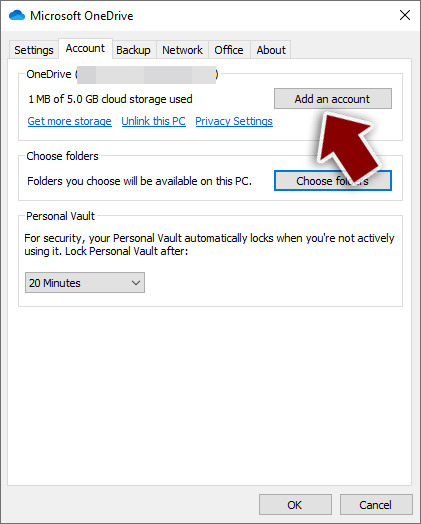
- If you don't see your email under the Account tab, you should click Add an account and proceed with the on-screen instructions to set yourself up.
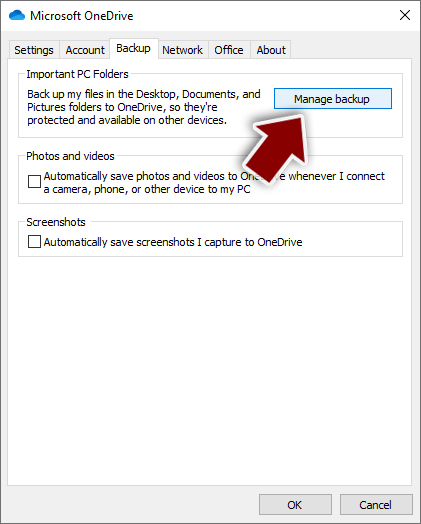
- Once done, move to the Backup tab and click Manage backup.
- Select Desktop, Documents, and Pictures, or a combination of whichever folders you want to backup.
- Press Start backup.
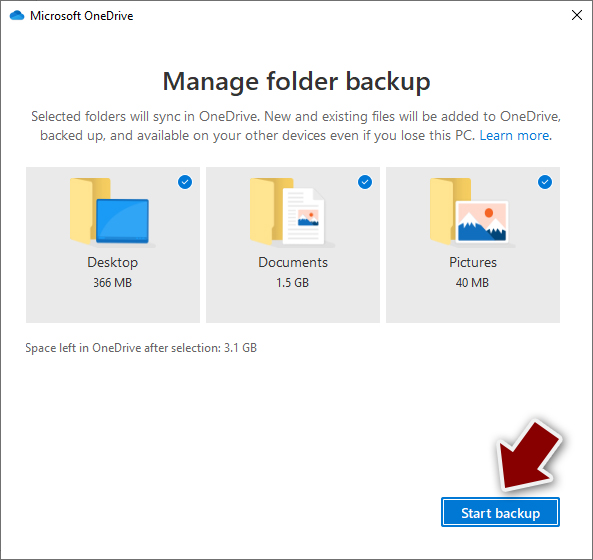
After this, all the files that are imported into the above-mentioned folders will be automatically backed for you. If you want to add other folders or files, you have to do that manually. For that, open File Explorer by pressing Win + E on your keyboard, and then click on the OneDrive icon. You should drag and drop folders you want to backup (or you can use Copy/Paste as well).
Using Google Drive
Google Drive is another great solution for free backups. The good news is that you get as much as 15GB for free by choosing this storage. There are also paid versions available, with significantly more storage to choose from.
You can access Google Drive via the web browser or use a desktop app you can download on the official website. If you want your files to be synced automatically, you will have to download the app, however.
- Download the Google Drive app installer and click on it.

- Wait a few seconds for it to be installed.
- Now click the arrow within your system tray – you should see Google Drive icon there, click it once.
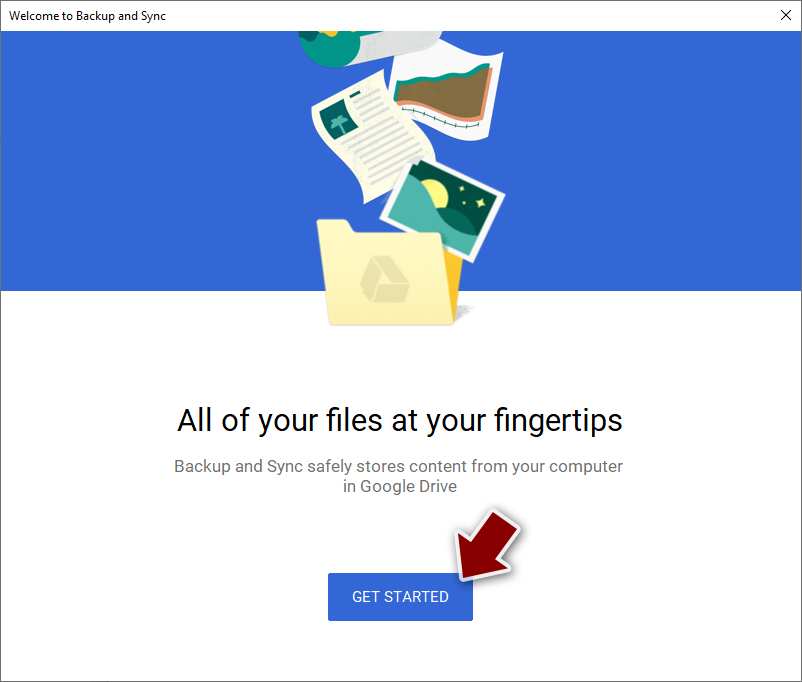
- Click Get Started.
- Enter all the required information – your email/phone, and password.
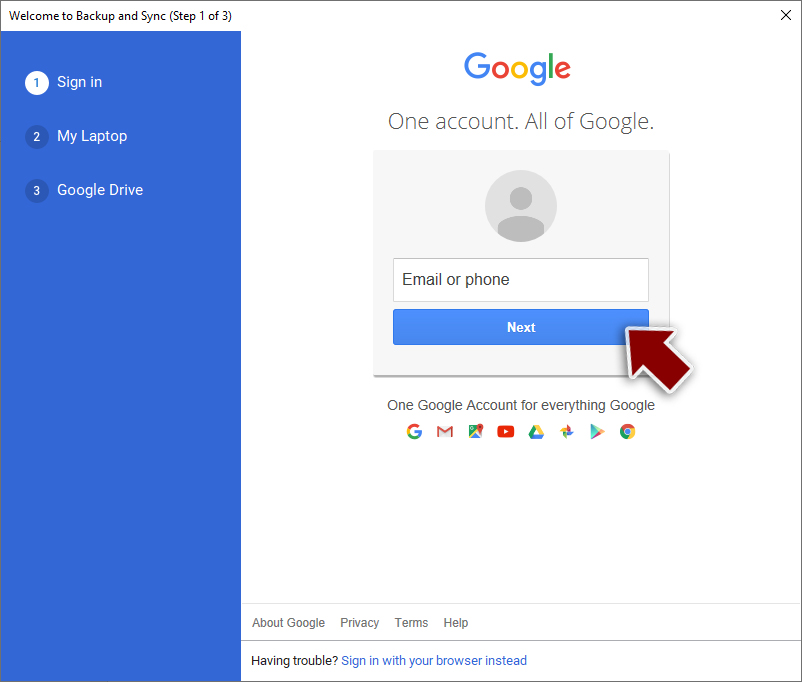
- Now pick what you want to sync and backup. You can click on Choose Folder to add additional folders to the list.
- Once done, pick Next.
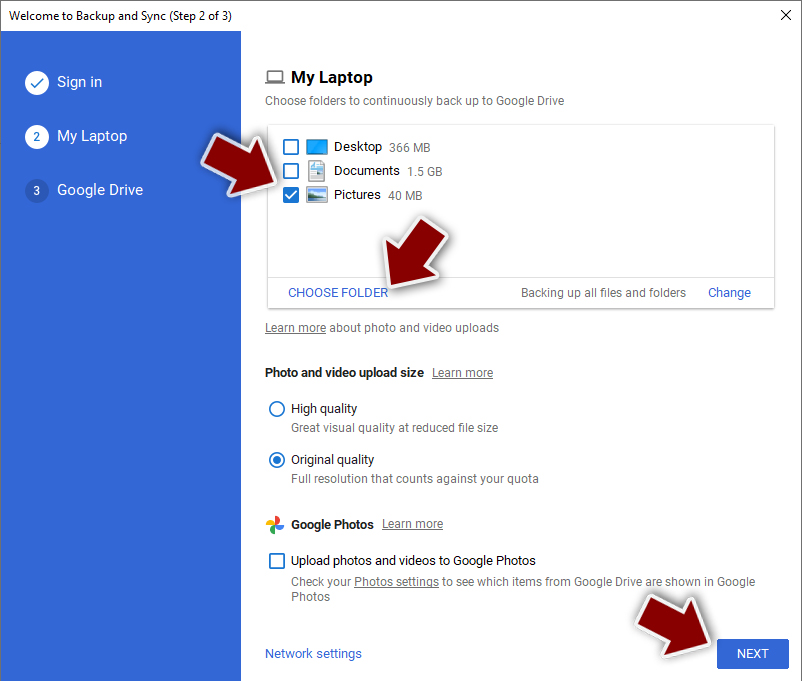
- Now you can select to sync items to be visible on your computer.
- Finally, press Start and wait till the sync is complete. Your files are now being backed up.
Report the incident to your local authorities
Ransomware is a huge business that is highly illegal, and authorities are very involved in catching malware operators. To have increased chances of identifying the culprits, the agencies need information. Therefore, by reporting the crime, you could help with stopping the cybercriminal activities and catching the threat actors. Make sure you include all the possible details, including how did you notice the attack, when it happened, etc. Additionally, providing documents such as ransom notes, examples of encrypted files, or malware executables would also be beneficial.
Law enforcement agencies typically deal with online fraud and cybercrime, although it depends on where you live. Here is the list of local authority groups that handle incidents like ransomware attacks, sorted by country:
- USA – Internet Crime Complaint Center IC3
- United Kingdom – ActionFraud
- Canada – Canadian Anti-Fraud Centre
- Australia – ScamWatch
- New Zealand – ConsumerProtection
- Germany – Polizei
- France – Ministère de l'Intérieur

If your country is not listed above, you should contact the local police department or communications center.
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Qbaa and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Encryption. Wikipedia. Free encyclopedia.
- ^ Virus detection. VirusTotal. Online malware scanner.
- ^ Virusler. Virusler. Spyware news.
