Queryexplorer.com virus (Removal Guide) - Chrome, Firefox, IE, Edge
Queryexplorer.com virus Removal Guide
What is Queryexplorer.com virus?
Reasons why Queryexplorer.com does not deserve a place on your PC
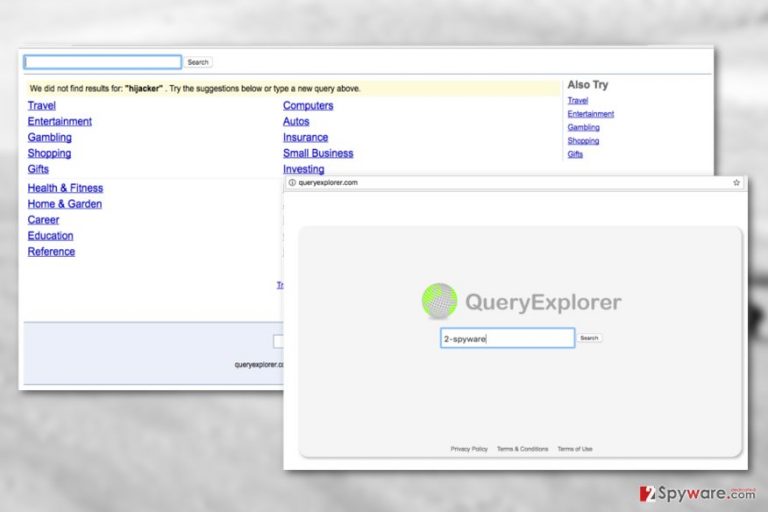
Queryexplorer.com is a suspicious website which shows up on the web browsers uninvited and introduces unauthorized changes to their settings. Unlike what its New York-based creators claim, Query Explorer is not some innovative search provider which can outmatch the web giants such as Google or Yahoo. In fact, looking at its functionalities, it would not even make it to the list of trusted search engines in the first place. The only description it does fit is of a full-blown browser hijacker [1]. The first aspect that allows such categorization is the fact that this malware uses deceptive techniques, such as software bundling, to reach computers. Bundling is not a malicious software distribution technique by its nature, but it can be used to deploy content on the computers without asking direct permissions from the users. Secondly, the http://queryexplorer.com/ domain replaces the previously assigned search engines or homepages which is another typical sign of a browser hijack. Finally, the search service this website provides is useless and mainly focused on promoting irrelevant services or products. Besides, with the arrival of this hijacker, you may also notice other suspicious programs such as QueryExplorer Search Desktop app or unfamiliar toolbars show up on your computer without you actually installing them. In order to stop unwanted programs making their way on your computer, you should start by performing Queryexplorer.com removal first. Rooting this hijacker out of your system will close gateways for malicious program to enter your PC. To make sure all of the virus components are adequately eliminated from the system, use reputable software such as FortectIntego.
Another important thing we’ve found out while looking through the Terms and Conditions page on Queryexplorer.com was that this website monitors user’s behavior and tracks all sorts of non-personally identifiable information [2] such as the computer’s IP address, software ID, search queries and phrases. Not only do the search providers collect this data but they also share it with their partners among which are indicated Yahoo!, AskJeeves.com and Miva. Rare of us would consciously agree to such management of our personal information. Luckily, you can stop this immediately by simply dedicating a few minutes to remove Queryexplorer.com from your computer.

Install software carefully — there might be a hijacker hidden inside the software package
As we’ve indicated before, Queryexplorer.com is a type of software which primarily spreads around together with other programs. Typically, hijacker creators pick popular freeware or shareware applications to bundle this malware with, ensuring a better chance that the users will download them. When such software package is downloaded, Queryexplorer.com installs along with the program the user originally intended to obtain. Luckily, it is not too difficult to check whether the downloaded software package contains unwanted components or not. You simply have to opt for the Advanced or Custom installation mode once the installation wizard opens.
Suggestions to remove Queryexplorer.com from your PC
Basically, there are two ways to remove Queryexplorer.com virus from the PC: manual and the automatic one. If you choose the first method, you have to be prepared to closely follow the guidelines at the end of the article. Nevertheless, if you are less experienced in computing, you should better stick to the automatic elimination method instead. Queryexplorer.com removal will be more successful if you update the security tool to the latest version. This way, the virus database will be renewed with all the latest virus versions, ensuring that the malware will be detected and banished from the PC.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Queryexplorer.com virus. Follow these steps
Uninstall from Windows
If you need a manual solution to Queryexplorer.com removal, please follow the step-by-step elimination guide below.
-
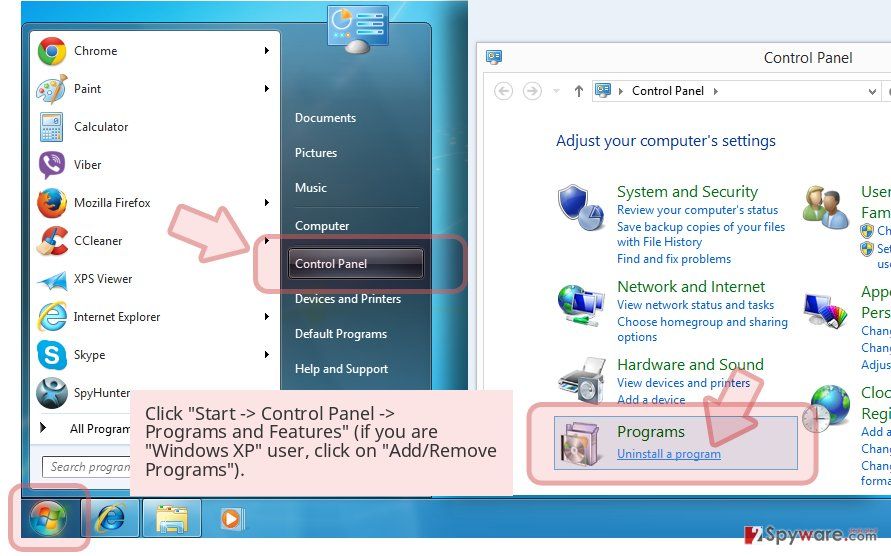
Click Start → Control Panel → Programs and Features (if you are Windows XP user, click on Add/Remove Programs).

-
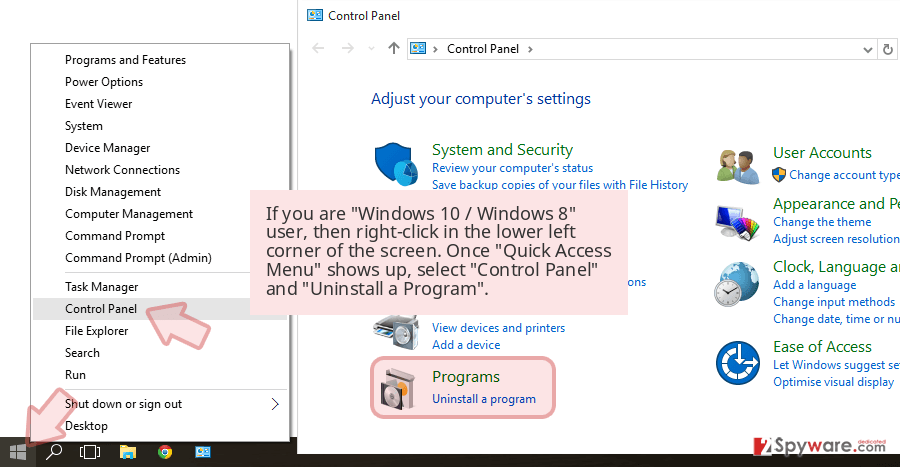
If you are Windows 10 / Windows 8 user, then right-click in the lower left corner of the screen. Once Quick Access Menu shows up, select Control Panel and Uninstall a Program.

-
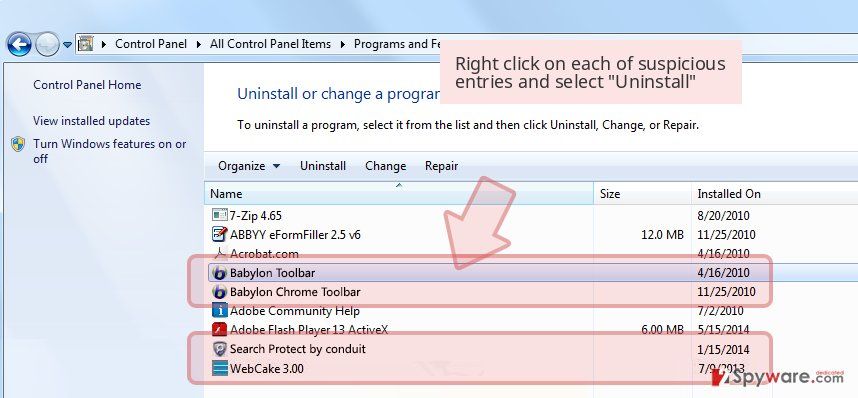
Uninstall Queryexplorer.com and related programs
Here, look for Queryexplorer.com or any other recently installed suspicious programs. -
Uninstall them and click OK to save these changes.

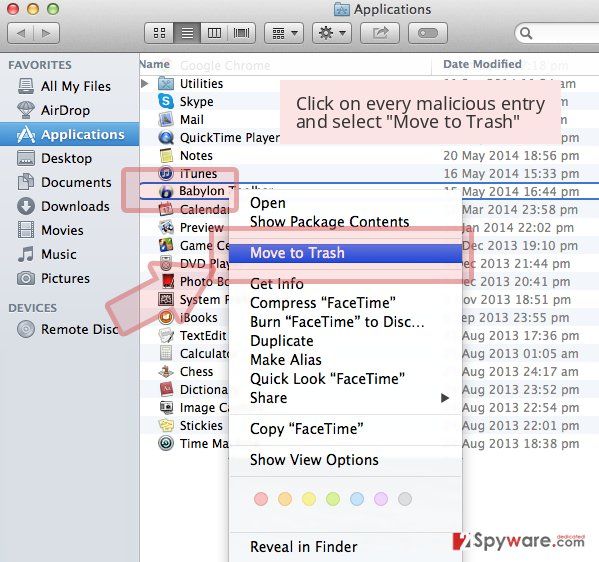
Delete from macOS
-
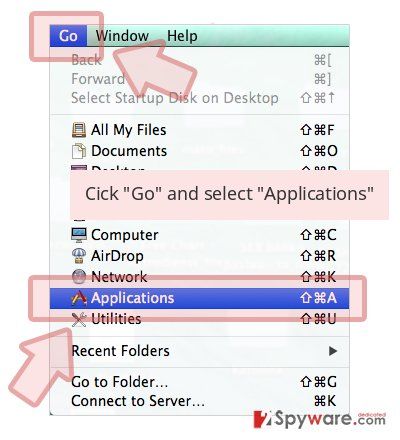
If you are using OS X, click Go button at the top left of the screen and select Applications.

-
Wait until you see Applications folder and look for Queryexplorer.com or any other suspicious programs on it. Now right click on every of such entries and select Move to Trash.

Remove from Microsoft Edge
You may remove Queryexplorer.com from your PC manually, but to roll back the changes made to your browser settings you will have to reset Microsoft Edge manually. If you have never performed a browser reset — don’t worry, we explain how it’s done right here:
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click Remove.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Settings > Privacy, search, and services..
- Under Clear browsing data, pick Choose what to clear.
- Select Cookies and other site data and Cached images and files. (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Remove next to any suspicious startup page.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.
- This will disable extensions and reset startup pages but will not delete bookmarks, saved passwords, or browsing history.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select the unwanted extension and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Settings.
- Under Home, set your preferred homepage and new tab settings.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data and Temporary cached files and pages, then click Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
If you find that your Google Chrome is infected with the hijacker, don’t panic and follow the guidelines below the article. This way, you’ll reset your browser and roll back the regular settings.
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all suspicious extensions related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

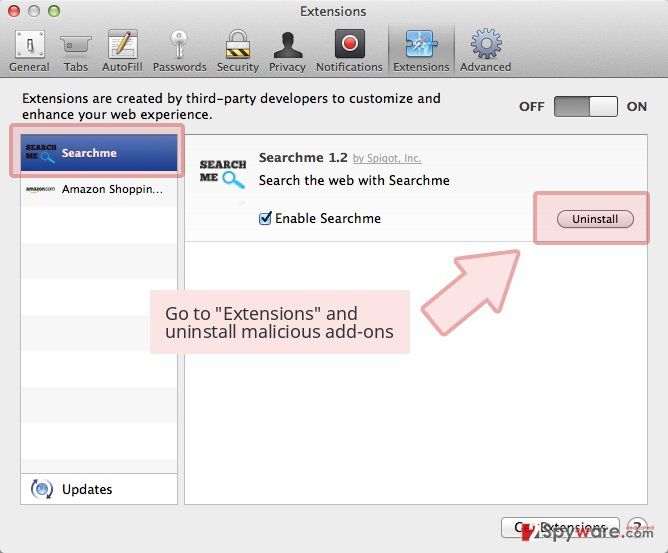
Delete from Safari
-
Remove dangerous extensions
Open Safari web browser and click on Safari in menu at the top left of the screen. Once you do this, select Preferences.
-
Here, select Extensions and look for Queryexplorer.com or other suspicious entries. Click on the Uninstall button to get rid each of them.

-
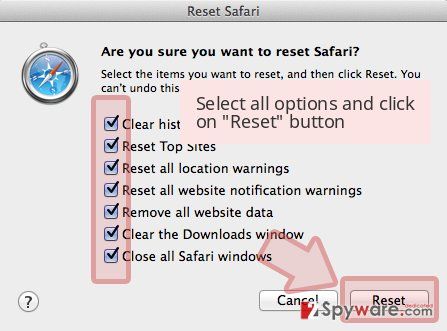
Reset Safari
Open Safari browser and click on Safari in menu section at the top left of the screen. Here, select Reset Safari....
-
Now you will see a detailed dialog window filled with reset options. All of those options are usually checked, but you can specify which of them you want to reset. Click the Reset button to complete Queryexplorer.com removal process.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Queryexplorer.com registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting stealing programs
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Browser hijacking: How to help avoid it and undo damage. Web Archive. Internet Archive Wayback Machine.
- ^ Michael Sweeney. What is PII, non-PII, and Personal Data?. 7suite. Data Management Platform.