Racareewitu.xyz ads (scam) - Free Instructions
Racareewitu.xyz ads Removal Guide
What is Racareewitu.xyz ads?
Racareewitu.xyz ads might show you links to insecure websites
Are you encountering strange Racareewitu.xyz pop-ups that show up at random times on your screen without seemingly being triggered by anything? You shouldn't worry because hundreds of people are affected by the same issue, regardless of whether they are using Google Chrome, Mozilla Firefox, MS Edge, or Safari.
These push notifications are sent by the website randomly, all while people are browsing the web or having the browser running in the background. However, the activity is not triggered by anything in particular that users do – the push notifications simply appear at the top of all the other running apps.
Within these prompts, there could be plenty of content that users rather not see. While some of the prompts might simply advertise some type of service or items, phishing messages might also appear on the screen regularly. For example, users might be told that they have won an expensive gift or that they can earn a lot of money quickly. In exchange, people are asked to provide their personal information or pay fees that go directly into crooks' hands. Thus, do not interact with any content that is promoted by the site.
While removing Racareewitu.xyz push notifications is not difficult at all, you also be aware that redirects to suspicious websites might commonly point to adware[1] infection. Therefore, multiple aspects of this phenomenon should be checked, and we explain everything you need to know below.
| Name | Racareewitu.xyz |
|---|---|
| Type | Push notifications, ads, pop-ups, scam |
| Distribution | Intrusive pop-ups can start showing up at some point after the “Allow” button is pressed within the notification prompt |
| Symptoms | Intrusive pop-ups show up directly on the screen, covering all the other opened apps or websites |
| Risks | Ads and links to sites displayed by the website might be dangerous: users might suffer from monetary losses, install malware or potentially unwanted programs on their systems, or disclose their sensitive data to cybercrooks |
| Elimination | You can disable notifications via browser settings; in case you experience more ads and redirects to suspicious sites, you should check your system with software like SpyHunter 5Combo Cleaner for adware infection |
| Further steps | You should delete web browser caches and other data from your browsers to protect your privacy and prevent information leaks. You can do that quicker with FortectIntego |
We have previously discussed many websites and scams related to push notifications, such as Usfinf.net, News-cuvasi.cc, or Lukchit.com. These websites have a lot in common, even though the naming of domains might not be similar at all. The truth is that there are thousands of fake websites created by malicious actors every day and, while some of them are being shut down by appropriate bodies, new ones come up regularly. This article will tackle the distribution, operation, and removal of the Racareewitu.xyz ads.
How push notification scams operate
Initially, the push notification feature was dedicated to the better usability of the device. For example, users can receive a message when they get an email in their mailbox, which makes them immediately pay attention to what happened. This simple principle was first used by Apple as early as 2009,[2] and it soon became apparent that the feature could be expanded on.
In 2015, it had finally reached desktop browsers, when more and more websites began using it. Currently, most of the sites ask whether or not you want to enable push notifications, even though the pop-ups have received a lot of negative reception due to it being another step users need to take before being able to access the website's content.
Once subscribed, users can receive relevant information from that particular website which would come in the form of notifications – these are not triggered by anything that users do but rather the website that is sending them. This operation principle soon became a very attractive opportunity for all sorts of fraudsters, and that's when the influx of fake websites began. To this day, there are thousands of new websites created for this malicious purpose alone.
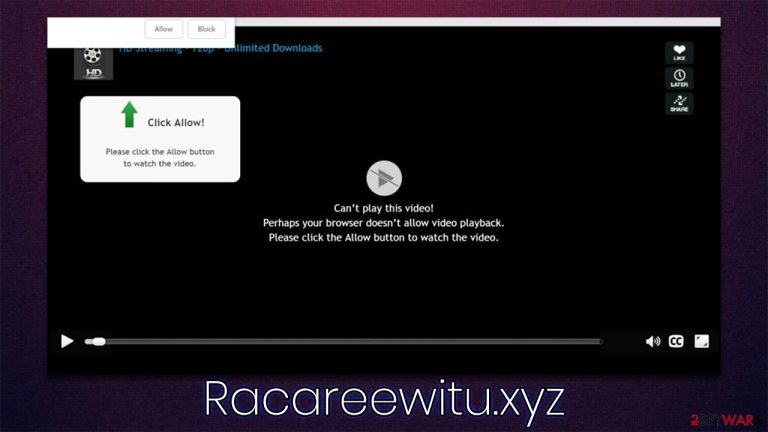
In most cases, users are shown misleading information about what the “Allow” button actually does. It is claimed that they need to use it to provide proof they are not bots or that there's 18+ content ahead. In other words, it often seems like some type of content is locked behind the action of a button press.
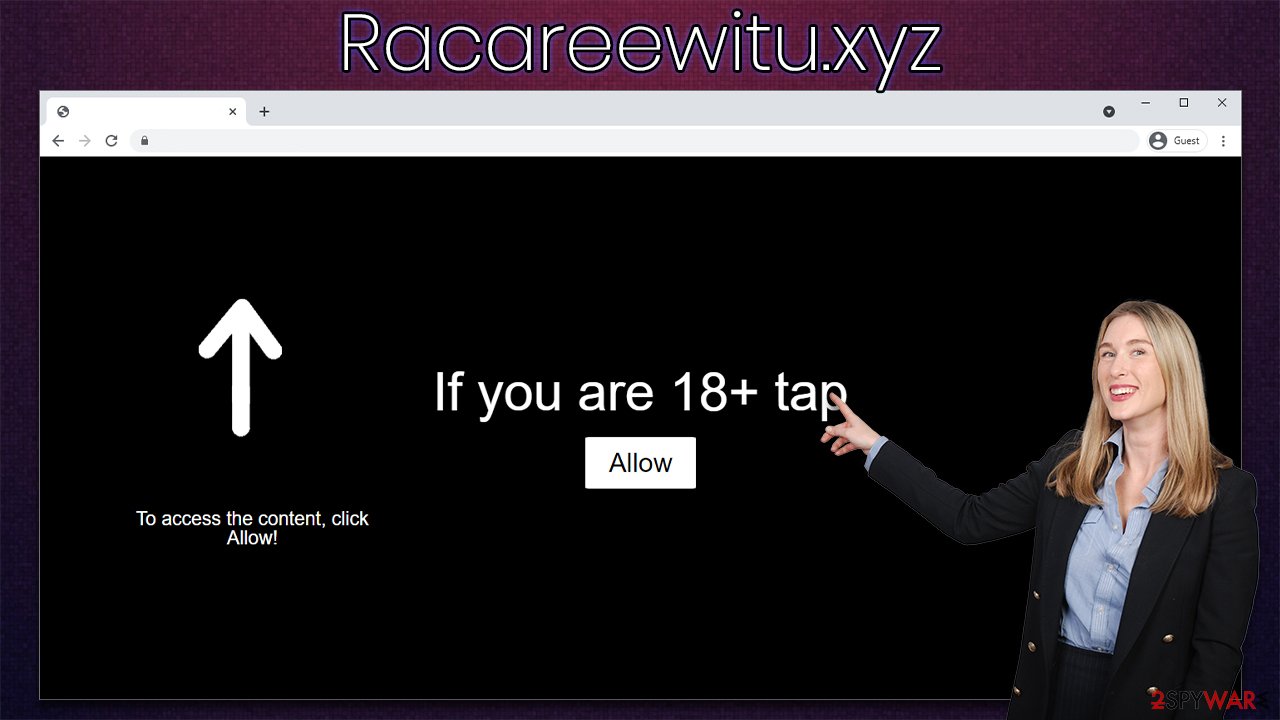
To avoid being scammed in the future, simply remember that no reputable website will ask you to enable notifications in order to reveal its contents. Likewise, there is no other purpose for that “Allow” button you see after entering a website, regardless of what the background message/picture claims.
Before you proceed: make important system checks
While some users might enter dangerous websites on purpose (for example, torrent sites are known to host malicious ads and spread malware via software cracks), most people don't endanger their safety and computer security on purpose. Crooks behind the Racareewitu.xyz scam are well aware of that, so they need to come up with some type of plan.
The plan is relatively simple: they either rely on links that are placed on various insecure websites or adware that users are not even aware of being installed on the system. The first method is relatively easy to avoid – security experts have long been warning about software cracks and similar illegal websites, as they are often used to spread malware such as Moia ransomware. Likewise, employing security software and ad-blockers can significantly decrease the possibility of redirects to scam, phishing,[3] and malware-laden websites.
However, when it comes to adware, the issues are rather persistent and can't be avoided unless the malicious software is removed from the system. You can try looking at the list of the installed programs within your Control Panel in Windows or Applications in Mac locations:
Windows
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

Mac
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Also, don't forget that potentially unwanted applications can be installed on the browser environment as extensions, so it is vital you check those areas as well. However, when it comes to adware and malware, sometimes things are a little bit more complicated than they may seem. For example, the app might not have a visible window and simply run as a background process or might not provide the entry within the uninstall section.
In such a case, we strongly recommend you rely on powerful security software, such as SpyHunter 5Combo Cleaner or Malwarebytes, to resolve the situation. Anti-malware can quickly and easily check your device for dangerous components and remove them at once. In some cases, computer infections can negatively impact the performance of the device due to system file corruption, resulting in program crashes, errors, and BSODs.
To resolve this, you can rely on FortectIntego PC repair solution that can find and replace damaged sectors within just a few minutes. Additionally, the app can also remove all the tracking cookies and other components from your browsers automatically.
Remove the intrusive pop-ups
After you check your system for malware and adware and ensure that it is safe, you can then proceed with the removal of the annoying pop-ups that come up on your screen on a regular basis. For that, you have to access the settings section of your browser.
Google Chrome (desktop):
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).

Mozilla Firefox:
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

MS Edge (legacy):
- Open Microsoft Edge, and click the Settings and more button (three horizontal dots) at the top-right of the window.
- Select Settings and then go to Advanced.
- Under Website permissions, pick Manage permissions and select the URL in question.
- Toggle the switch to the left to turn notifications off on Microsoft Edge.

Safari:
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
