Repp ransomware (Feb 2020 update) - Removal Guide
Repp virus Removal Guide
What is Repp ransomware?
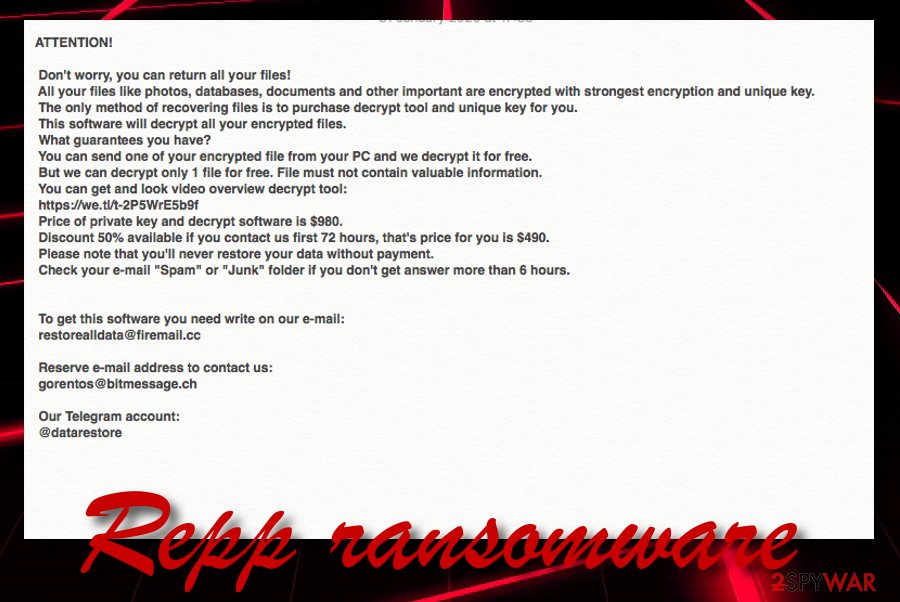
Repp ransomware – the 203rd version of Djvu ransomware that is currently undecryptable
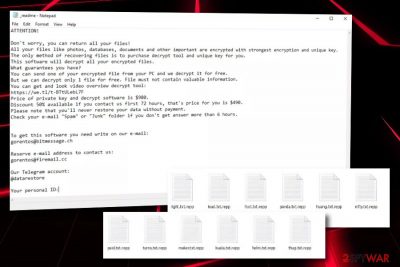
Repp ransomware, discovered by Michael Gillespie,[1] appears to be one of the newest Djvu ransomware versions that have emerged at the start of 2020. This malicious variant acts exactly the same as its other siblings and aims to target English-speaking people who are using Windows computers. The extension that the ransomware virus appends is .repp and is added to each file's name after the AES-256 cipher[2] performs its encryption task. Furthermore, Repp ransomware drops the _readme.txt message in a Notepad blank that is placed on the desktop and in each folder that holds encrypted documents and files.
Repp ransomware developers claim that they are the only ones who are capable of recovering encrypted files. These people provide ransom demands that vary from $490 to $980. The first price is the starter amount that needs to be paid in a 72 hour period. If the ransom is not transferred during that time, the money amount will double to $980. The criminals provide the gorentos@bitmessage.ch, gorentos@firemail.cc email addresses, and @datarestore telegram account as a way to initiate contact with them.
| Name | Repp ransomware |
|---|---|
| Type | Ransomware/malware |
| Family | Djvu virus |
| Appearance | This cyber threat has emerged at the start of 2020, in January |
| Target | Regarding the language in which the ransom note is written, the ransomware infection points its target at English people and English-speaking users |
| Danger level | This infection carries the danger level of “high”. Besides encrypting valuable files and demanding a big ransom price, it also can plant other malware onto the Windows computer |
| Appendix | When files are locked with the AES-256 encryption cipher, all of the filenames receive the .repp appendix |
| Ransom note | The cybercriminals provide all of the ransom demands and required payment conditions in the _readme.txt ransom note that is the same for all Djvu ransomware variants |
| Ransom price | At first, the crooks urge for $490 as a 50% discount from $980. If the payment is not transferred in 72 hours, the hackers will double the price again to $980 |
| Crooks' contacts | The ransom message provides gorentos@bitmessage.ch, gorentos@firemail.cc email addresses, and @datarestore telegram account |
| Removal | If you have been dealing with this ransomware virus lately, you should remove the malware ASAP. For this task, employ only reliable antimalware software that is capable of detecting and eliminating such dangerous cyber threats |
| Fix software | If you have discovered any type of damage on your Windows computer, you can try repairing the corrupted areas with the help of a repair tool such as FortectIntego |
Repp virus is a dangerous infection that does not get installed intentionally but still requires the user's interaction. Most of the time, users lose carefulness while opening email spam attachments, visiting third-party websites, or clicking on various ads and this way they create the perfect conditions for a ransomware attack to emerge.
Ransomware infections such as Repp ransomware are developed to target Windows operating systems. Mostly, these cyber threats target English-speaking users as the biggest variety of people is speaking this language and the criminals can infect as many users as possible.
Furthermore, the ransomware developers are likely to urge for cryptocurrency such as Bitcoin as such transfers allow the process to stay untracked and completely anonymous. The same also goes for Repp ransomware spreaders. These people are interested in receiving a fine amount of income, according to the ransom note:
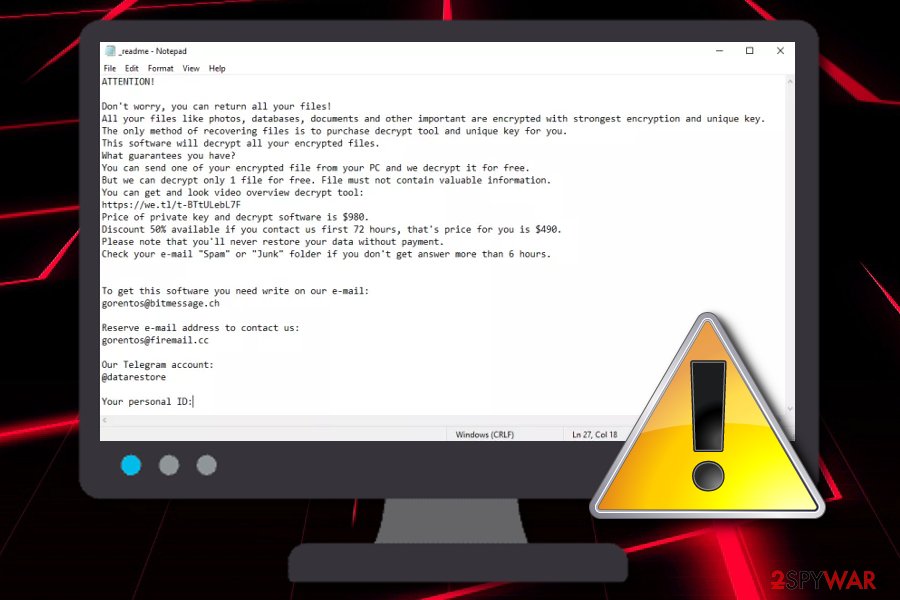
ATTENTION!
Don't worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-2P5WrE5b9f
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
restorealldata@firemail.ccReserve e-mail address to contact us:
gorentos@bitmessage.chOur Telegram account:
@datarestore
Repp ransomware is a malicious parasite that can include malware-laden components all over the system, including the desktop, User's folder, AppData folder, Task Manager, and Windows Registry. The malware can camouflage itself as a well-known process and run undetected in the Task Manager for a while.
Furthermore, Repp ransomware can aim to delete the Shadow Volume Copies of encrypted files to harden the decryption process for the users. Nevertheless, the virus permanently damages the Windows hosts file in order to prevent the users from accessing security-related websites where they could receive valuable information on the virus removal and data recovery processes.
Keep in mind that once you are completing the Repp ransomware removal process, you should delete the hosts file too, otherwise, the access to security websites will remain blocked. Besides all the mentioned activities, this malware can distribute the AZORult Trojan virus as it is also related to the STOP ransomware family which spreads this current threat.
If Repp ransomware brings you a trojan infection, it can get hidden anywhere on your computer system and start monitoring malicious processes in the background. For example, the malware will likely start overusing your CPU's power, recording personal, information, swindling money, mining cryptocurrency, or injecting other more advanced threats.
You should remove Repp ransomware from your Windows computer system before it is too late and the damage is too big to recover from. Employing a trustworthy antivirus product should help you to deal with the entire process. Also, if you have already found some alterings on your computer system, try repairing them with FortectIntego.
When you uninstall Repp ransomware, you can start thinking about data recovery possibilities. Note that it is not worth to pay the cybercriminals as they can easily scam you by taking your money and just running off without giving you any key. Even though the Djvu Emsisoft decrypter is available for versions that have been released before August 2019,[3] there are other alternatives that you could try for file restoring.
If you are looking for something that would help you to recover the files that have been touched by Repp ransomware, we have provided some software solutions at the end of this article. Also, you can try using DrWeb's Rescue pack for $150 that includes decryption software and 2 years of system protection.[4]
The most common distribution tactics of ransomware payload
Cybersecurity experts from LosVirus.es[5] claim that ransomware infections are most commonly spread through email spam. The crooks often pretend to be from reliable companies such as FedEx and DHL and deliver legitimate-looking attachments that come in forms of executables, word documents, and other formats.
Once the user opens the infected file, he/she receives the malicious payload straight on the Windows operating system. you should be aware of email messages that fall in the Spam section and avoid opening any emails that look questionable to you. Always identify the sender, check the letter's text for grammar mistakes and do not open any attachments that look suspicious to you. If you have already downloaded the file, scan it with an antivirus product.
Furthermore, file-encrypting cyber threats are delivered through cracked software that is included in peer-to-peer networks such as The Pirate Bay, eMule, and BitTorrent. You should use only original downloading sources for your wanted products and services. P2P sites and other untrusted websites should be avoided as they lack the required security and can easily be misused by malware developers for their own malicious purposes.
However, this is still not all that you should know about ransomware spreading. These cyber threats can also be brought to the computer system through malvertising ads that appear on third-party websites, infected hyperlinks, exploit kits, and fake software updates that offer to upgrade your Flash Player or JavaScript. Always employ reliable antimalware software that will protect you from unexpected infections and alert if something suspicious is waiting for you ahead.
Removal steps for Repp ransomware from Windows OS
If you have been dealing with Repp ransomware lately, you should eliminate the malware with no hesitation. The process requires employing trustworthy malware removal software that is capable of deleting all the malicious components that were brought by the ransomware virus to the Windows computer system.
Do not try to remove Repp ransomware on your own, especially if you are an inexperienced computer user as you can make some mistakes that might bring permanent damage to the system. Also, if you think that your machine might have been corrupted in one way or another, you can check such speculation with SpyHunter 5Combo Cleaner or Malwarebytes. If this software shows any damaged areas, you might have a chance of repairing them with FortectIntego.
After Repp ransomware removal and damage fix, you can start thinking about data recovery strategies. Remember that rushing to pay the cybercriminals is not the best thing to do as you can get easily scammed. Alternatively, travel to the end of this web page where you will find some data recovery methods.
Getting rid of Repp virus. Follow these steps
Manual removal using Safe Mode
To deactivate the ransomware virus on your Windows computer and diminish all malicious settings, you should apply the following steps to set the Safe Mode with Networking feature on your device.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Repp using System Restore
To diminish all malware-laden changes and reverse your computer system back to its previous state, you should follow the below-provided guidelines and opt for System Restore.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Repp. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Repp from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Repp, you can use several methods to restore them:
Use Data Recovery Pro to recover at least some of your files.
Try using this software if the ransomware virus has encrypted your files and documents. Complete all of the steps as required in order to reach the best results possible.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Repp ransomware;
- Restore them.
Using Windows Previous Versions feature might allow you to restore some data.
If the ransomware virus has affected your valuable files, you can try restoring some of them with the help of this software. However, make sure that you have enabled the System Restore feature before.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Shadow Explorer might be a handy tool for data recovery.
If the ransomware virus did not permanently damage or delete the Shadow Volume Copies of your encrypted files, you have a chance of restoring some of your individual documents.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Currently, the cybersecurity experts are working on the official decryption tool.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Repp and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Michael Gillespie. #STOP #Djvu #Ransomware. Twitter. Social platform.
- ^ Advanced Encryption Standard. Wikipedia. The free encyclopedia.
- ^ Emsisoft Decryptor for STOP Djvu. Emsisoft. Decryption tools.
- ^ Dr.Web Rescue Pack. Dr Web products.
- ^ LosVirus.es. LosVirus. Security and spyware news.





















